NIST SPECIAL PUBLICATION 1800-9C
Access Rights Management for the Financial Services Sector¶
Volume C:
How-to Guides
James Banoczi
National Cybersecurity Center of Excellence
Information Technology Laboratory
Sallie Edwards
Nedu Irrechukwu
Josh Klosterman
Harry Perper
Susan Prince
Susan Symington
Devin Wynne
The MITRE Corporation
McLean, VA
August 2017
DRAFT
DISCLAIMER
Certain commercial entities, equipment, products, or materials may be identified in this document in order to describe an experimental procedure or concept adequately. Such identification is not intended to imply recommendation or endorsement by NIST or NCCoE, nor is it intended to imply that the entities, equipment, products, or materials are necessarily the best available for the purpose.
National Institute of Standards and Technology Special Publication 1800-9C Natl. Inst. Stand. Technol. Spec. Publ. 1800-9C, 276 pages, August 2017 CODEN: NSPUE2
FEEDBACK
You can improve this guide by contributing feedback. As you review and adopt this solution for your own organization, we ask you and your colleagues to share your experience and advice with us.
Comments on this publication may be submitted to: financial_nccoe@nist.gov
Public comment period: August 31, 2017 through October 31, 2017
All comments are subject to release under the Freedom of Information Act (FOIA).
NATIONAL CYBERSECURITY CENTER OF EXCELLENCE
The National Cybersecurity Center of Excellence (NCCoE), a part of the National Institute of Standards and Technology (NIST), is a collaborative hub where industry organizations, government agencies, and academic institutions work together to address businesses’ most pressing cybersecurity issues. This public-private partnership enables the creation of practical cybersecurity solutions for specific industries, as well as for broad, cross-sector technology challenges. Through consortia under Cooperative Research and Development Agreements (CRADAs), including technology partners—from Fortune 50 market leaders to smaller companies specializing in IT security—the NCCoE applies standards and best practices to develop modular, easily adaptable example cybersecurity solutions using commercially available technology. The NCCoE documents these example solutions in the NIST Special Publication 1800 series, which maps capabilities to the NIST Cyber Security Framework and details the steps needed for another entity to recreate the example solution. The NCCoE was established in 2012 by NIST in partnership with the State of Maryland and Montgomery County, Md.
To learn more about the NCCoE, visit https://nccoe.nist.gov. To learn more about NIST, visit https://www.nist.gov.
NIST CYBERSECURITY PRACTICE GUIDES
NIST Cybersecurity Practice Guides (Special Publication Series 1800) target specific cybersecurity challenges in the public and private sectors. They are practical, user-friendly guides that facilitate the adoption of standards-based approaches to cybersecurity. They show members of the information security community how to implement example solutions that help them align more easily with relevant standards and best practices and provide users with the materials lists, configuration files, and other information they need to implement a similar approach.
The documents in this series describe example implementations of cybersecurity practices that businesses and other organizations may voluntarily adopt. These documents do not describe regulations or mandatory practices, nor do they carry statutory authority.
ABSTRACT
Managing access to resources (data) is complicated because internal systems multiply and acquisitions add to the complexity of an organization’s IT infrastructure. Identity and access management (IdAM) is the set of technology, policies, and processes that are used to manage access to resources. Access rights management (ARM) is the subset of those technologies, policies, and processes that manage the rights of individuals and systems to access resources (data). In other words, an ARM system enables a company to give the right person the right access to the right resources at the right time. The goal of this project is to demonstrate an ARM solution that is a standards-based technical approach to coordinating and automating updates to and improving the security of the repositories (directories) that maintain the user access information across an organization. The coordination improves cybersecurity by ensuring that user access information is updated accurately (according to access policies), including disabling accounts or revoking access privileges as user resource access needs change. Cybersecurity is also improved through better monitoring for unauthorized changes (e.g., privilege escalation). The system executes user access changes across the enterprise according to corporate access policies quickly, simultaneously, and consistently. The ARM reference design and example implementation are described in this NIST Cybersecurity “Access Rights Management” practice guide. This project resulted from discussions among NCCoE staff and members of the financial services sector.
This NIST Cybersecurity Practice Guide also describes our collaborative efforts with technology providers and financial services stakeholders to address the security challenges of ARM. It provides a modular, open, end-to-end example implementation that can be tailored to financial services companies of varying sizes and sophistication. The use case scenario that provides the underlying impetus for the functionality presented in the guide is based on normal day-to-day business operations. Though the reference solution was demonstrated with a certain suite of products, the guide does not endorse these specific products. Instead, it presents the NIST Cybersecurity Framework (CSF) core functions and subcategories, as well as financial industry guidelines, that a company’s security personnel can use to identify similar standards-based products that can be integrated quickly and cost-effectively with a company’s existing tools and infrastructure. Planning for deployment of the design gives an organization the opportunity to review and audit the access control information in their directories and get a more global, correlated, disambiguated view of the user access roles and attributes that are currently in effect.
KEYWORDS
Access; authentication; authorization; cybersecurity; directory; provisioning.
ACKNOWLEDGMENTS
We are grateful to the following individuals for their generous contributions of expertise and time.
| Name | Institution |
|---|---|
| Jagdeep Srinivas | AlertEnterprise |
| Hemma Prafullchandra | HyTrust |
| Roger Wigenstam | NextLabs |
| Don Graham | Radiant Logic |
| Adam Cohen | Splunk |
| Clyde Poole | TDi Technologies |
| Dustin Hayes | Vanguard Integrity Professionals |
The Technology Partners/Collaborators who participated in this build submitted their capabilities in response to a notice in the Federal Register. Respondents with relevant capabilities or product components were invited to sign a Cooperative Research and Development Agreement (CRADA) with NIST, allowing them to participate in a consortium to build this example solution. We worked with:
| Product Vendor | Component Name | Function |
|---|---|---|
| AlertEnterprise | Enterprise Guardian | Access policy management, administration and account provisioning system |
| HyTrust | Cloud Control | Privileged user access controller, monitor, and logging system for VSphere |
| NextLabs | NextLabs | Attribute based access control interface for SharePoint |
| Radiant Logic | RadiantOne | Virtual directory system |
| Splunk | Enterprise | Log aggregation and analytics system |
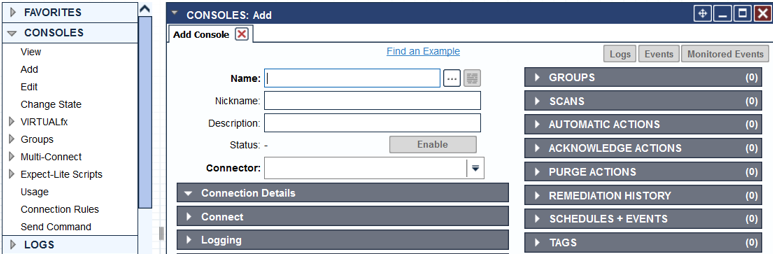
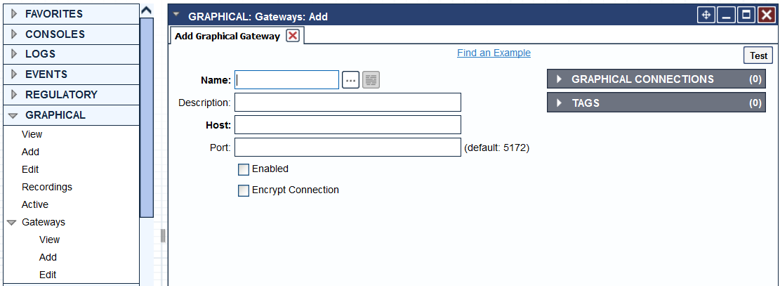
| TDi Technologies | ConsoleWorks | Application and operating system privileged user access controller, monitor, and logging system |
| Vanguard Integrity Professionals | Vanguard | Mainframe RACF to LDAP interface system |
List of Figures
Figure 1‑1 Logical Access Rights Management Lab Build Architecture
Figure 1‑2 Logical Security Log Collection and Monitoring Lab Build Architecture
Figure 1‑3 NCCoE Lab Networking Diagram
Figure 1‑4 NCCoE Lab Networking Diagram
List of Tables
Table 1‑1 NCCoE Lab Network and System IP Addresses
1. Introduction¶
The NIST Cybersecurity Practice Guide shows IT professionals and security engineers how we implemented this example solution. In Volume C we cover all the products employed in the reference design. We do not re-create the product manufacturers’ documentation, which is presumed to be widely available. Rather, these guides show how we incorporated the products together in our environment.
Note: These are not comprehensive tutorials. There are many possible service and security configurations for these products that are out of scope for this example implementation.
1.1. Practice Guide Structure¶
This NIST Cybersecurity Practice Guide demonstrates a standards-based reference design and provides users with the information they need to replicate this access rights management (ARM) approach. The reference design is modular and can be deployed in whole or in parts.
The guide contains three volumes:
- NIST SP 1800-9a: Executive Summary — High-level overview
- NIST SP 1800-9b: Approach, Architecture, and Security Characteristics—What we built and why
- NIST SP 1800-9c: How-To Guides —Instructions for building the example implementation (you are here)
Depending on your role in your organization, you might use this guide in different ways:
Business decision makers, including chief security and technology officers will be interested in the Executive Summary (NIST SP 1800-9a), which describes the:
- challenges identified by financial services companies
- operational benefits of adopting the solution
- high-level solution description
Technology or security program managers who are concerned with how to identify, understand, assess, and mitigate risk will be interested in the Approach, Architecture, and Security Characteristics (NIST SP 1800-9b) part of the guide, which describes what we did and why. The following sections will be of interest:
- Section 3.4.1, Assessing Risk Posture, describes the risk analysis we performed.
- Section 3.4.2, Security Control Map, maps the security functions and control of this example implementation to cybersecurity standards and best practices.
IT professionals who want to implement an approach like this will find the whole Practice Guide useful. The guide’s information will provide insight into the resources and skills needed to implement an ARM solution. You can use the How-To portion of the guide, NIST SP 1800-9c (which is this document), to replicate all or parts of the example implementation created in our lab. NIST SP 1800-9c provides specific product installation, configuration, and integration instructions for implementing the example implementation. We do not re-create the product manufacturers’ documentation, which is generally widely available. Rather, we show how we incorporated the products in our environment to create an example implementation.
The guide assumes that IT professionals have experience implementing security products within the enterprise. Though we have used a suite of commercial products to address the challenge, this guide does not endorse these particular products. Your organization can adopt this solution or one that adheres to these guidelines in whole, or you can use this guide as a starting point for tailoring and implementing parts of the solution. Your organization’s security experts should identify the products that will best integrate with your existing tools and IT system infrastructure. We hope you will seek products that are congruent with applicable standards and best practices.
A NIST Cybersecurity Practice Guide does not describe “the” solution, but a possible solution. This is a draft guide. We seek feedback on its contents and welcome your input. Comments, suggestions, and success stories will improve subsequent versions of this guide. Please contribute your thoughts to financial_nccoe@nist.gov
1.2. Build Overview¶
The build is an example implementation of an access rights management system. The main components of the system include policy management, policy administration, access information provisioning, and security monitoring. In addition to these components, we have included privileged access management to secure the administration of the main components.
Security of the implementation is provided through logging changes to account/access information within the directories, a virtual directory, the policy administration system, and the privileged access management systems. The virtual directory is used to cache (mirror) the contents of the directories by checking for changes every 60 sec. All changes are reported to the security monitoring system immediately. Analytics within the security monitoring system (log collection and monitoring) correlates incoming logs. Security analysts are alerted when the analytics identify potential security events caused by inconsistent logs. Furthermore, the security analysts can drill down and investigate the cause of any alert. The available information within the security monitoring system enables them fully analyze the logs causing the alert and determine a course of action to effectively mitigate the cybersecurity incident. In addition, the directory monitoring provides another tool to monitor for malicious insider activity.
1.3. Typographical Conventions¶
The following table presents typographic conventions used in this volume.
| Typeface/Symbol | Meaning | Example | |
|---|---|---|---|
| Italics | filenames and pathnames references to documents that are not hyperlinks, new terms, and placeholders |
For detailed definitions of terms, see the NCCoE Glossary. | |
| Bold | names of menus, options, command buttons and fields | Choose File > Edit. | |
Monospace
|
command-line input, on-screen computer output, sample code examples, status codes | mkdir
|
|
Monospace Bold
|
command-line user input contrasted with computer output | service sshd start
|
|
| blue text | link to other parts of the document, a web URL, or an email address | All publications from NIST’s National Cybersecurity Center of Excellence are available at https://nccoe.nist.gov. | |
1.4. Logical Architecture Summary¶
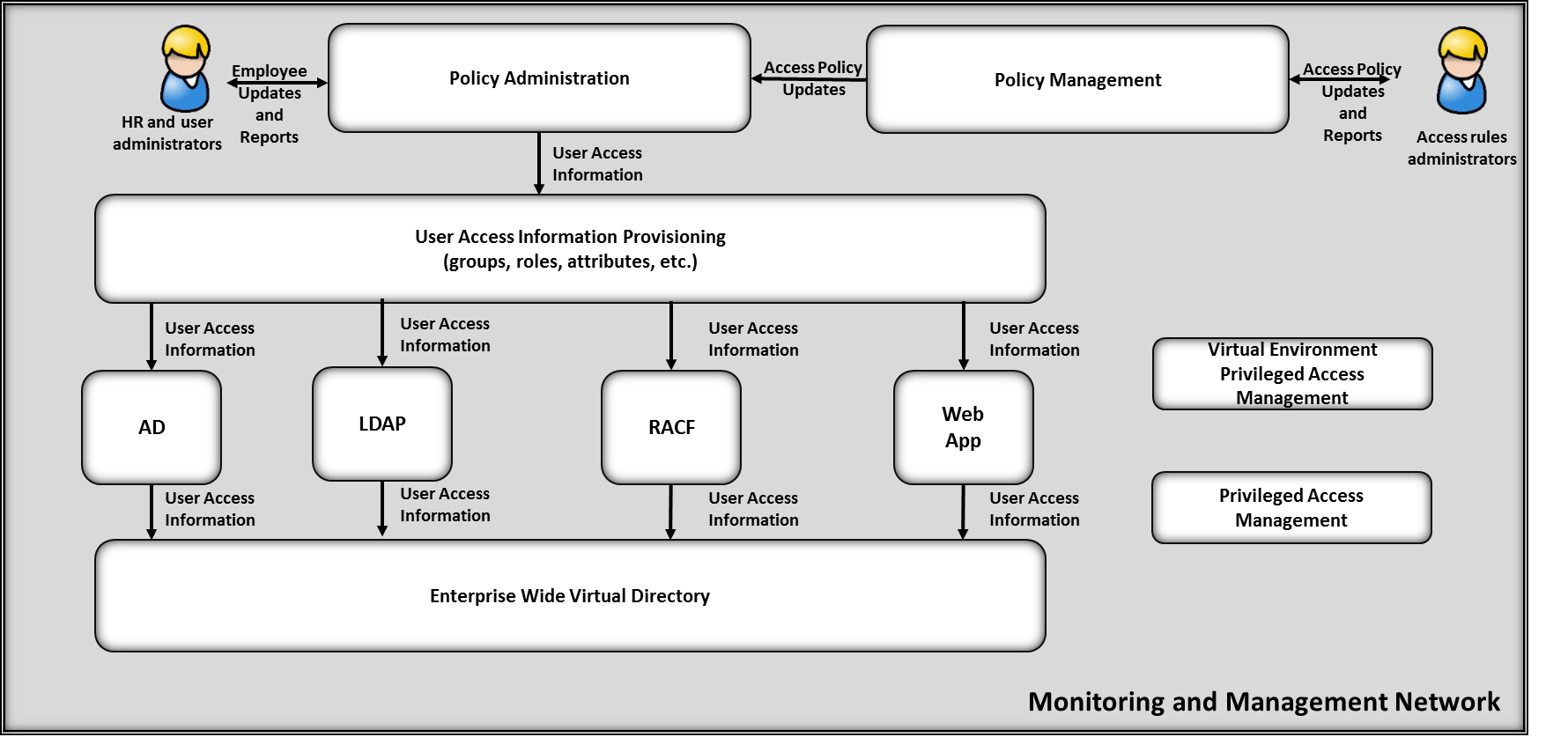
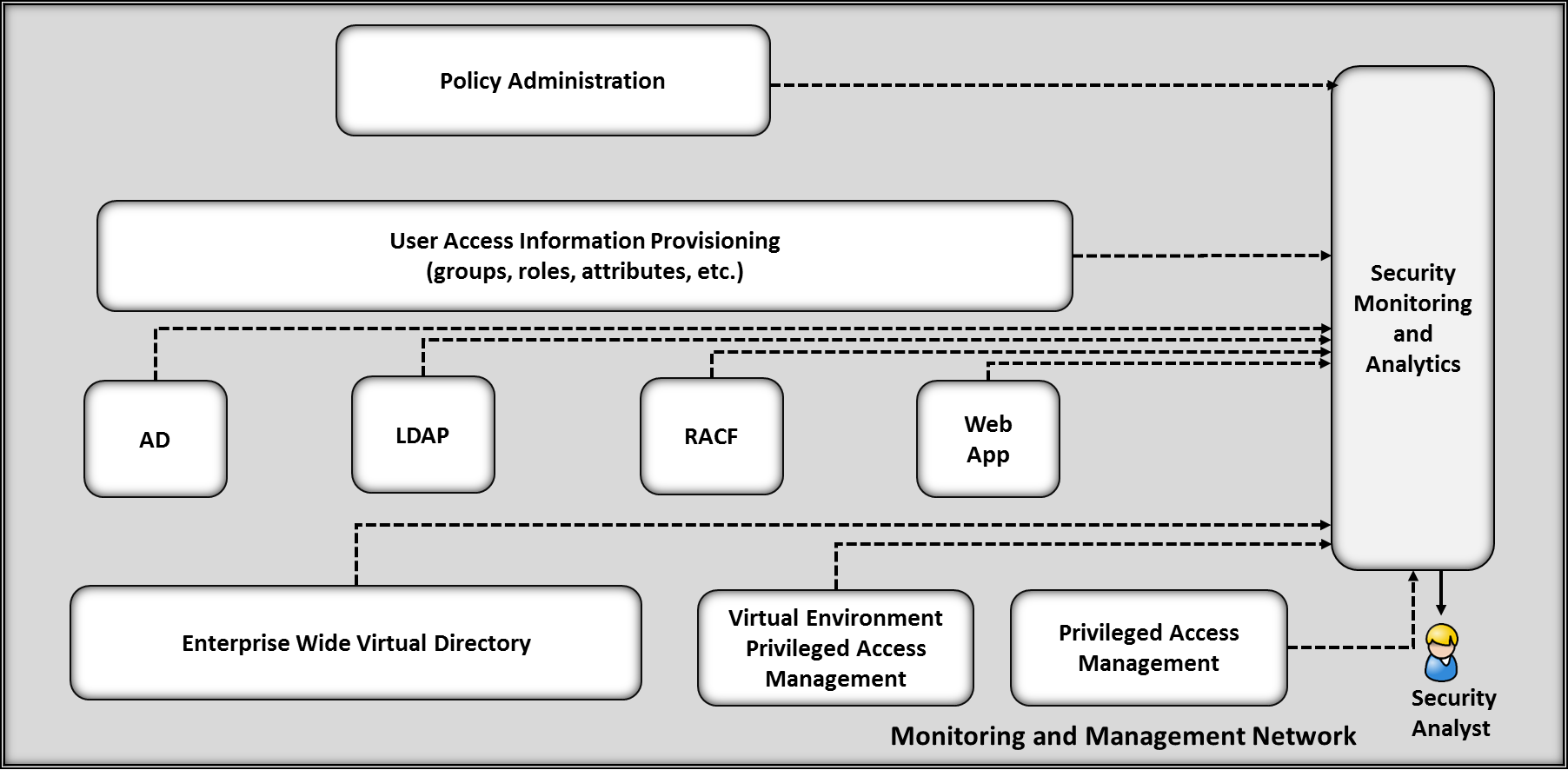
NIST Special Publication 1800-9b (SP1800-9b) describes an example implementation consisting of user access management (including provisioning) and security monitoring / data collection. SP1800-9b includes a much more detailed description of the architecture for building an instance of the example implementation using commercial products. That architecture is depicted in Figure 1-1 and Figure 1-2.
Figure 1‑1 Logical Access Rights Management Lab Build Architecture
Figure 1‑2 Logical Security Log Collection and Monitoring Lab Build Architecture
This volume of the practice guide provides detailed instructions on installing, configuring, and integrating the products used to build an instance of the example solution. The role of each product in the example implementation is described in SP1800-9b, Section 4, Architecture.
1.5. Network Diagrams¶
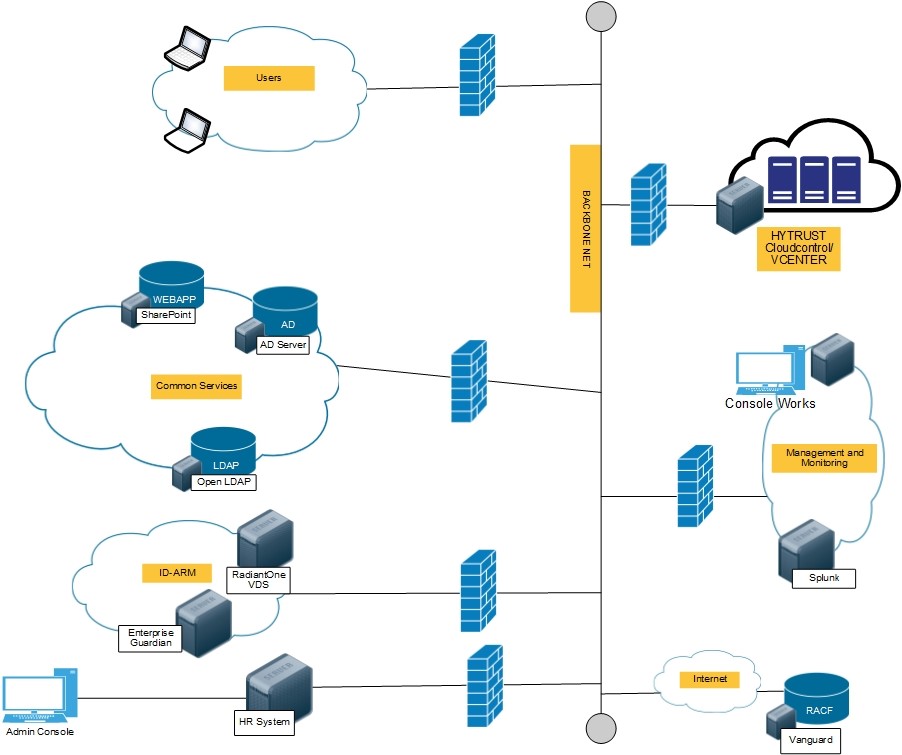
The architecture diagrams in the previous section present the logical connections needed among the products used to build an instance of the example implementation. This section describes the virtual environment lab implementation depicting the connectivity among the products.
1.6. NCCoE Lab¶
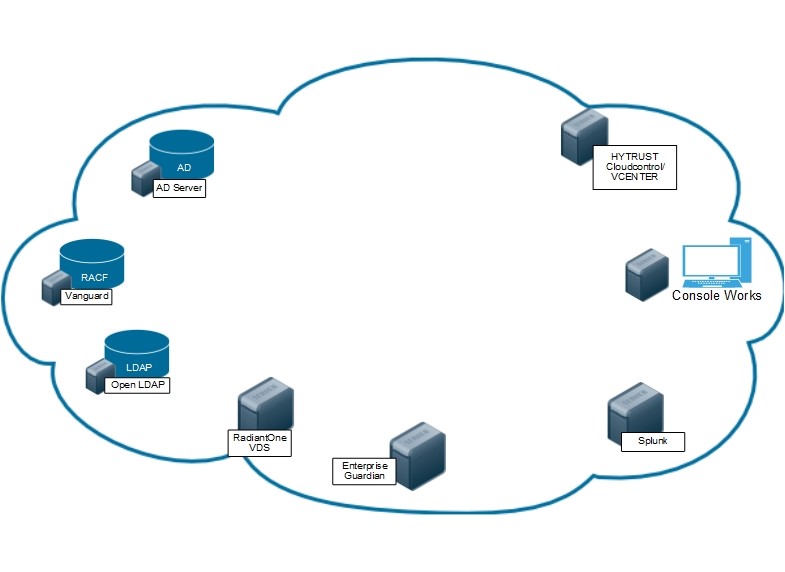
Figures 1-3 and 1-4 show the network configurations used in the example implementation.
Figure 1‑3 NCCoE Lab Networking Diagram
Figure 1‑4 NCCoE Lab Management and Monitoring Networking Diagram
The following table includes the IP addresses for each of the networks depicted in Figure 1-3 and Figure 1-4.
Table 1‑1 NCCoE Lab Network and System IP Addresses
| Network | System | IP Address |
|---|---|---|
| Logging Network: 192.168.17.0/24 | Splunk | 192.168.17.10 |
| Vendor Network: 10.33.50.0/16 | ConsoleWorks | 10.33.50.164 |
| Common Services Network : 192.168.19.0/24 | ActiveDirectory | 192.168.19.10 |
| OpenLDAP | 192.168.19.11 | |
| ID-ARM: 192.168.14.0/24 | AlertEnterprise | 192.168.14.113 |
| RadiantOne VDS | 192.168.14.111 | |
| Vanguard: 172.17.212.0/24 | VanguardMainframe | 172.17.212.10 |
| HyTrust: 192.168.20.0/24 | CloudControl | 192.168.20.11 |
| ESXiServer | 192.168.20.12 | |
| Users: 192.168.15.0/24 | User 1 | 192.168.15.110 |
| User 2 | 192.168.15.111 | |
| HR1 | 192.168.15.112 |
2. Product Installation Guides¶
This section of the practice guide contains detailed instructions for installing and configuring all the products used to build an instance of the example implementation Product installation information is organized alphabetically by vendor, with one section for each instance of the product.
2.1. AlertEnterprise¶
AlertEnterprise Enterprise Guardian is an identity and access management system that provides end to end automated account provisioning, account change management, policy enforcement, and account administration across multiple diverse account directory systems.
2.1.1. How It’s Used¶
AlertEnterprise Enterprise Guardian is used in the example implementation to provide access policy management, account change logging/reporting, account administration and account provisioning. Provisioining accounts includes creating new accounts and changes to existing accounts, including disabling accounts within multiple directories simultaneously.
2.1.2. Virtual Machine Configuration¶
The AlertEnterprise virtual machine consists of a Windows Server 2012 R2 configured as follows:
- Windows Server 2012 R2
- 1 CPU
- 2 NICs
- 32GB Mem
- 190GB Storage
Network Configuration (Interface 1)
Network Configuration (Interface 2)
2.1.3. Prerequisites¶
Before starting the installation of the Enterprise Guardian Application, you must install the prerequisite software, which consist of a compatible version of JRE, Apache Activemq, and a SQL database. You will also need a supported internet browser and zip extracting software. See the AlertEnterprise System Requirement Specifications Guide (provided by vendor) for a full list of supported prerequisite software.
Prerequisite software used in this build:
- JRE 1.6 Update 22
- Apache Tomcat 6.0.26
- Oracle SQL Database 12c
- Google Chrome 55.0.2883.87
- 7-zip 16.04
2.1.4. Java¶
Download and install Java from the Oracle web site.
Make sure that JAVA_HOME variable is set to the folder where Java is installed and
%JAVA_HOME%/binis in the system’s path.Open the Command Prompt in Administrator Mode (right-click > Run as Administrator) and issue:
Set JAVA_HOME=<PATH OF JDK/JRE>Where <> is the path where Java is installed, for example,
C:\\Program Files\\Java\\JRE6Setting Path:
PATH= C:\\Program Files\\Java\\JDK1.6.0-21\\bin;%PATH%Checking JAVA_HOME and PATH:
Echo %JAVA_HOME%Echo %PATH%
2.1.5. Apache Activemq¶
- Install the Activemq server according to documentation found on the Apache website.
- Run ActiveMQ as a Windows service.
- Ensure the server is installed correctly and running by connecting to
the admin console on port 8161. For example:
URL: <IP address of the server where Active MQ is 2130 installed>:8161/admin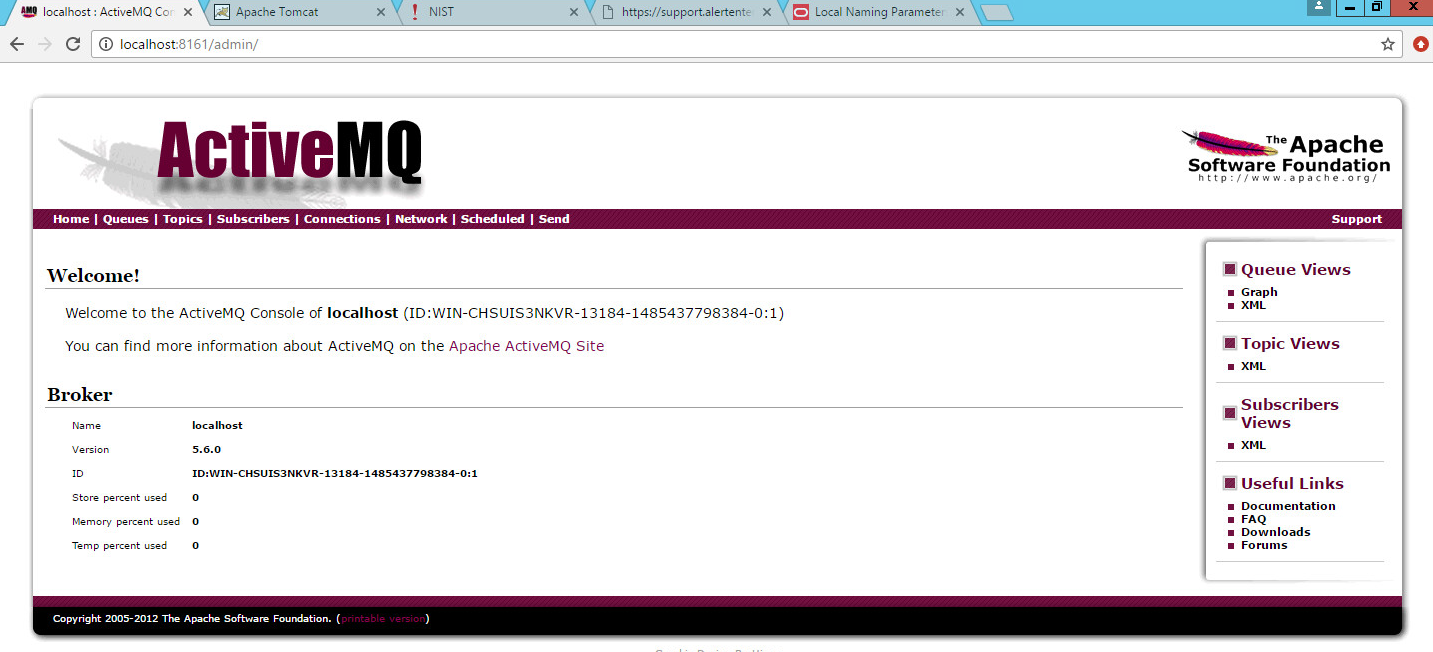
2.1.6. Oracle DB¶
Install the Oracle SQL database according to documentation found on the Oracle website.
Ensure the pdborcl pluggable database service name is added correctly in the tnsnames.ora file per the Oracle documentation.
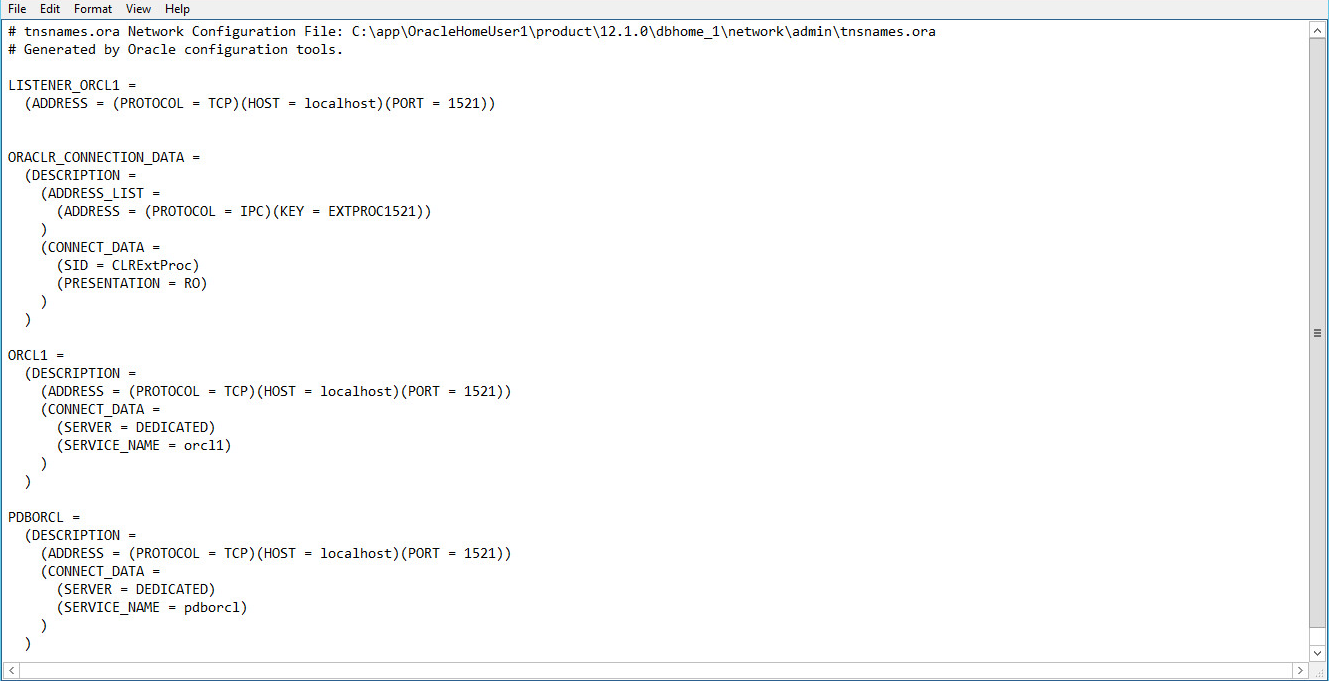
Open a command prompt and test by connecting with this command:
sqlplus sys/<password>@pborcl as sysdba.
2.1.7. 7-Zip¶
- Download and install 7-Zip from www.7-zip.org.
2.1.8. Installation¶
You can install the AlertEnterprise Enterprise Guardian Application in three steps. This information is also found within the AlertEnterprise Installation Guide.
- Install and Configure the Apache Tomcat Server.
- Configure the database server.
- Deploy the application.
2.1.9. Install and Configure Tomcat¶
Install the Apache Tomcat Server per the documentation found on the Apache website. Details can also be found within the AlertEnterprise Enterprise Guardian Install Guide.
- During the installation, specify the destination folder as C:\AlertEnterprise\Tomcat.
When installation is complete, navigate to Start>Programs>Configure Tomcat and select the Java tab.
- Add the following lines to the end of Java Options, ensuring there are no spaces:
-XX:PermSize=1024 -Xms2048m -Xmx2048m -Dcom.alnt.fabric.loadInitData=force " "--Dalert.db.update=update
Click Apply and OK to close the dialog box.
2.1.10. Configure the Database Server¶
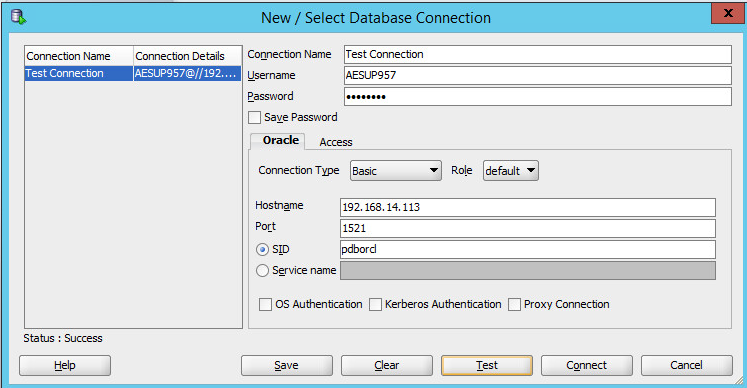
The NCCoE build supports Oracle SQL Database 12c. See the administrator’s guide for the full installation and configuration guide. Open a command prompt with administrator privileges and connect:
sqlplus sys/<password>@pborcl as sysdba
1. Create a new schema/SID per your naming convention:
create user<user/schema name> identified by <password>, you may have to
unlock the schema: alter user <user/schema name> identified by <password>unlock
Use
grant <attribute> to <user/schema name>;to grant the new user all of the following attributes:connect; resource; create synonym; create session; create sequence; create view; unlimited tablespace; create procedure; create trigger; create table
You can use Oracle SQL Developer to test the connection using the username and password created in Step 2. When this connection is successful, you can proceed.
2.1.11. Deploying the Application¶
After you have successfully configured the database, proceed to deploy the AlertEnterprise product on your web application server. The following deployment steps are required for the Tomcat 6.0 version:
Note: For steps required to use the SAP system connector or MySQL database, see the vendor documentation.
Stop the Tomcat server from the Windows services if it is already running. Click Start > Run and type
services.mscthen click OK. Select the Apache Tomcat and click the Stop Service icon to stop the service.Copy the
AlertEnterprise.war,AccessMap.war(if you possess AlertInsight license),AlertEnterpriseHelp.war, andjasperserver-pro.warfiles to the<Tomcat installation folder>\webapps\path.If you have a license for the Password Management application, you need to copy the password management war file (
AIPM.war) to<Tomcat installation folder>/webapps.Create new folders
AlertCommonLibandAlertExternalLibunder the<Tomcat Installation Folder>.Extract
AlertCommonLib.zipunder theAlertCommonLibfolder. You will see many new files in this folder.Edit
<Tomcat Installation Folder>\conf\catalina.propertiesusing any editor and addcommon.loaderas described below:common.loader=${catalina.base}/lib,${catalina.base}/lib/*.jar,${catalina.home}/lib,${catalina.home}/lib/*.jar,${catalina.home}/AlertCommonLib/*.jar,${catalina.home}/AlertExternalLib/*.jarSave the file and close the editor.
- Add Database Connection. Add a new resource entry as below with
name
jdbc/alntdbin<Tomcat installation folder>\conf\context.xml. Replace the code in <> with relevant information.
For ORACLE:
<Resource description="DB Connection" name="jdbc/alntdb" auth="Container" type="com.mchange.v2.c3p0.ComboPooledDataSource" factory="org.apache.naming.factory.BeanFactory" user=<"Schema User"> password=<"Schema User Password"> jdbcUrl="jdbc:oracle:thin:@<db host name>:<db port>:<schema name>/SID" driverClass="oracle.jdbc.driver.OracleDriver" maxPoolSize="100" minPoolSize="5" acquireIncrement="5" numHelperThreads="20" maxIdleTime="600" maxIdleTimeExcessConnections="300" debugUnreturnedConnectionStackTraces="true" unreturnedConnectionTimeout="900" />
To add more <resource> entries, see the AlertEnterprise Enterprise Guardian Installation Guide.
2.1.12. Start the Server¶
Make sure that Active MQ is up and running and then start the Tomcat server.
Start the AlertEnterprise application using the address of the form
http://<Server IP Address>:8080/AlertEnterprise.Note: 8080 is the default port on local host. If you want to change it, change it in the server.xml.
Log on to the application using username admin and password: System@123. You should be able to view the Home screen of the application.
2.1.13. Provisioning Configuration¶
For this build, the AlertEnterprise support team pre-configured AlertEnterprise Enterprise Guardian for provisioning. Configuring the provisioning functionality involves several steps to ensure that each connector is properly provisioning attributes. All steps for configuring provisioning are documented and delivered with the application in the Help tab. The parameters used during the configuration of different components are found here.
2.1.14. Creating System Connectors¶
Navigate to Setup > Manual Configuration > Systems > System.
Click New to create a new system.
Enter the following Definition:
- System Type –
Active Directory - Connector Name –
AD - Connector Description –
AD - Connector Long Description –
AD - Connector Type –
LDAP(default)
- System Type –
Click Next.
Enter the following Parameters:
- HostName –
192.168.19.10 - Port Number –
636(use389if SSL is not configured yet) - Service user Dn –
CN=AlertServiceAccount,CN=Users,DC=Acmefinancial,DC=com - Password –
Fsarm@nccoe1 - Use SSL –
true(use false if SSL is not configured yet) - User Base DN –
OU=Operations,DC=Acmefinancial,DC=com - Group Base DN –
DC=Acmefinancial,DC=com - Object Class –
user - Is Primary –
Yes - LastModified Column role –
whenChanged - Last Modified User Column –
whenChanged
- HostName –
Click Next.
Enter the following parameters:
- Application –
AlertAccess - Check the following boxes –
Provisioning, Role Management, Offline System, Allow Modify Role - Category –
production - Time Zone –
Eastern Standard Time
- Application –
Click Next.
Click Save.
Repeat Steps 1–9 to add the OpenLDAP and RACF connectors with the following parameters:
OpenLDAP:
- System Type –
OpenLDAP Server - Connector Name –
OPENLDAP - Connector Description –
OpenLDAP - Connector Type –
OpenLDAP - HostName –
192.168.19.11 - Port Number –
636(use389if SSL is not configured yet) - Service user Dn –
CN=Admin,DC=Acmefinancial,DC=com - Password –
Fsarm@nccoe1 - Use SSL –
true(use false if SSL is not configured yet) - User Base
DN – OU=Operations,DC=Acmefinancial,DC=com - Group Base
DN – OU=Operations,DC=Acmefinancial,DC=com - Object Class –
inetOrgPerson - Group Object Class Name –
groupOfUniqueNames - Primay Connection –
Yes - LastModified Column role –
whenChanged - Last Modified User Column –
whenChanged - Member Attribute Name for Group -
uniqueMember - LDAP DnName –
cn - LDAP Account Control Column Name –
cn - User Password attributed –
default - Encode Password Required? –
default - LDAP Group Search Attributed -
cn - userIdColumnName (Optional Parameter) -
cn - Application –
AlertAccess - Check the following boxes –
Provisioning, Role Management, Offline System, Allow Modify Role - Category –
production
aa. Time Zone –
Eastern Standard TimeRACF:
- System Type –
OpenLDAP Server - Connector Name –
ACF_OPENLDAP - Connector Description –
RACF_OpenLDAP - Connector Type –
OpenLDAP - HostName –
172.17.212.10 - Port Number –
636(use ``389``if SSL is not configured yet) - Service user Dn –
racfid=TSNI00,profiletype=user,sysplex=sysplex1 - Password –
Fsarm@nccoe1 - Use SSL –
true(use false if SSL is not configured yet) - User Base DN –
profiletype=user,sysplex=sysplex1 - Group Base DN –
profiletype=user,sysplex=sysplex1 - Object Class –
racfUser - Primay Connection –
Yes - LDAP DnName –
racfId - LDAP UserID Column Name –
racfId - User Password attributed –
default - Encode Password Required? –
default - Ignore user check –
Yes - isObjectClassExist –
No - userIdColumnName (Optional Parameter) –
racfid - isCnAttrExists (Optional Parameter) –
No - Application –
AlertAccess - Check the following boxes –
Provisioning, Role Management, Offline System, Allow Modify Role - Time Zone –
Eastern Standard Time
File Connector
- System Type –
File Connector - Connector Name –
FILE CONNECTOR - Connector Type –
FileConnector - User Folder Path –
C:\Program Files\User - Role Folder Path –
C:\Program Files\Role - User role Folder Path –
C:\Program Files\UserRole - Column Header for User ID –
UserId - Skip Provisioning –
Yes - Application –
AlertAccess - Check the following boxes –
Provisioning, Role Management - Category –
Production - Time Zone –
Eastern Standard Time
Identity Store
- System Type –
Database (JDBC J2EE) - Connector Name –
IDENTITYSTORE - Connector Type –
Database (JDBC J2EE) - User Name –
admin - Password –
System@123 - JNDI Name –
java:comp/env/jdbc/alntdb - Application –
Alert Access - Check the following boxes –
Provisioning, Role Manangement, Offline System, Identity Provider - Category –
Production - Time Zone –
Eastern Standard Time
- System Type –
2.1.15. User Data Source¶
- Navigate to Setup>Manual Configuration>User Data>User Data Source.
- Click New. Create the following User Data Source:
| System Type | Connector | Unique Key | Sequence | Mapping |
|---|---|---|---|---|
| Database (JDBC J2EE) | IDENTITYSTORE | UserId | 1 |
|
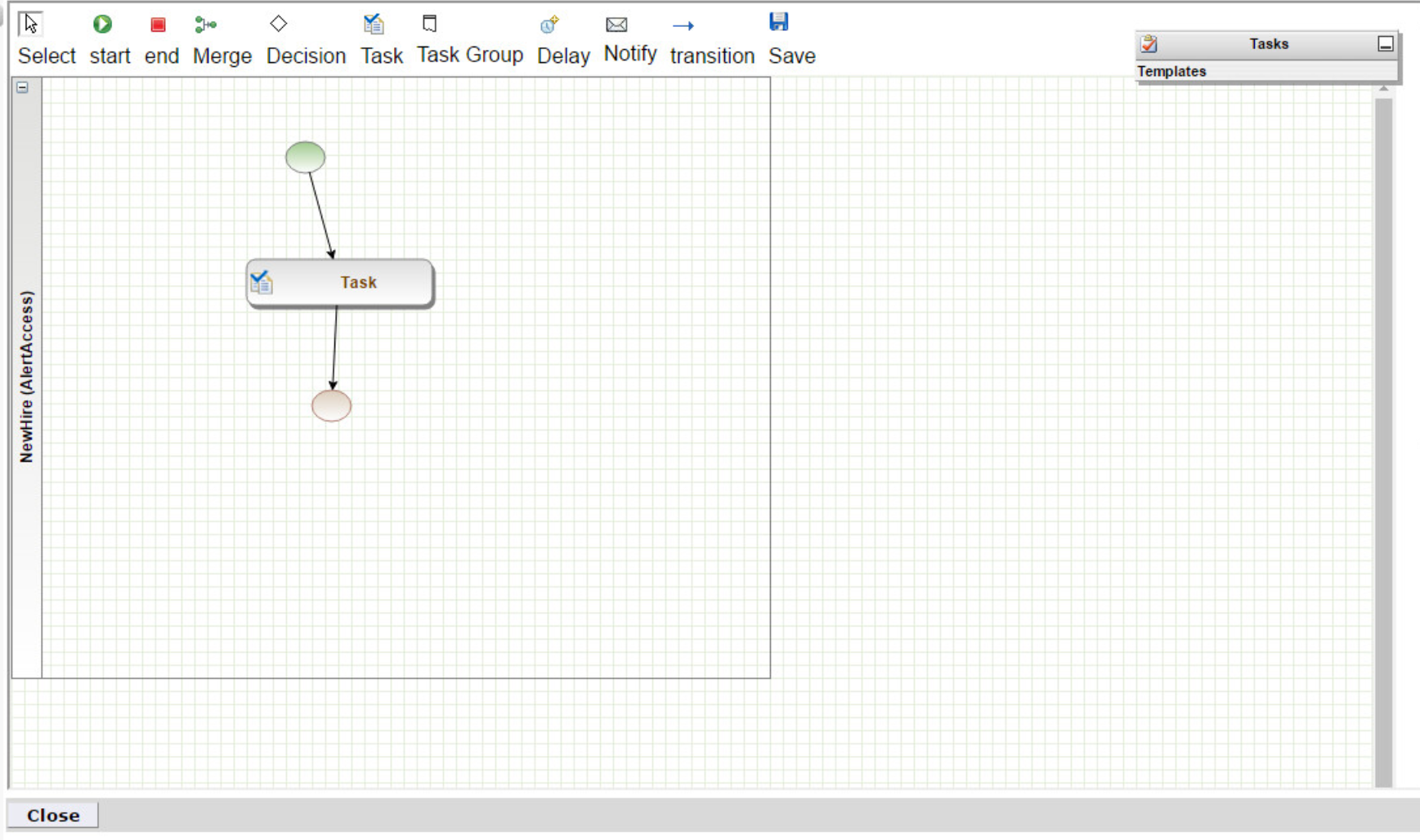
2.1.16. Process Designer¶
2.1.17. Policies¶
- Navigate to Setup>Manual Configuration>Policy Engine>Policies.
- Click New. Create the following policies:
| Policy Name | Rule Name | Priority | Active | Attribute Name | Value |
|---|---|---|---|---|---|
| OpenLDAP prov Action | OpenLDAP prov Action | 0 | Yes | System ProvAction | Change_Roles |
| Termination-shell update | Termination-shell update | 0 | Yes | loginShell | disable |
2.1.18. Rules¶
- Navigate to Setup>Manual Configuration>Policy Engine>Rules.
- Click New. Create the following rules:
| Rule Name | Entity Type | Rule Type | Description | Applicable To | Attributes | Condition |
|---|---|---|---|---|---|---|
| Survey Rule | Workflow | Survey | Survey Rule | Initiator | AND | |
| NewHire | Workflow | AlertAccess | NewHire | Initiator | AND Request Category | = Change Access |
| NewHireSuggestDefault | Workflow | AlertAccess | NewHireDefault | Suggest/Default | AND Request Category |
|
| Role Assignement | Workflow | AlertAccess | Role Assign | Policy | AND Role:Alias | Any Value |
| OpenLDAP prov Action | Workflow | AlertAccess | OpenLDAP provisioning action | Policy | AND Request Category; System Multi Select |
|
| Termination-shell update | Workflow | AlertAccess | Terminate shell update | Policy | AND Request Category | =Termination |
2.1.18.1. Suggest/Default Access¶
- Navigate to Setup>Manual Configuration>Policy Engine>Suggest/Default Access.
- Click New. Create the following criteria:
| Name | Type | Condition | Search By | Resources | Attributes |
|---|---|---|---|---|---|
| NewHire | Default | NewHireSuggestDefault | Systems | OpenLDAP, AD, RACF_OPENLDAP | |
| DefaultRoleAssignment | Default | NewHireSuggestDefault | Role Attributes | Alias | |
| 123 | Defaul | NewHireSuggestDefault | Role Attributes | RoleDescription |
2.1.19. Policy Designer¶
- Navigate to Setup>Manual Configuration>Policy Engine>Policy Designer.
- Click New.
- Enter RoleRecon as the Name and
Alert Accessas the Rule Type. - Create the following policy:
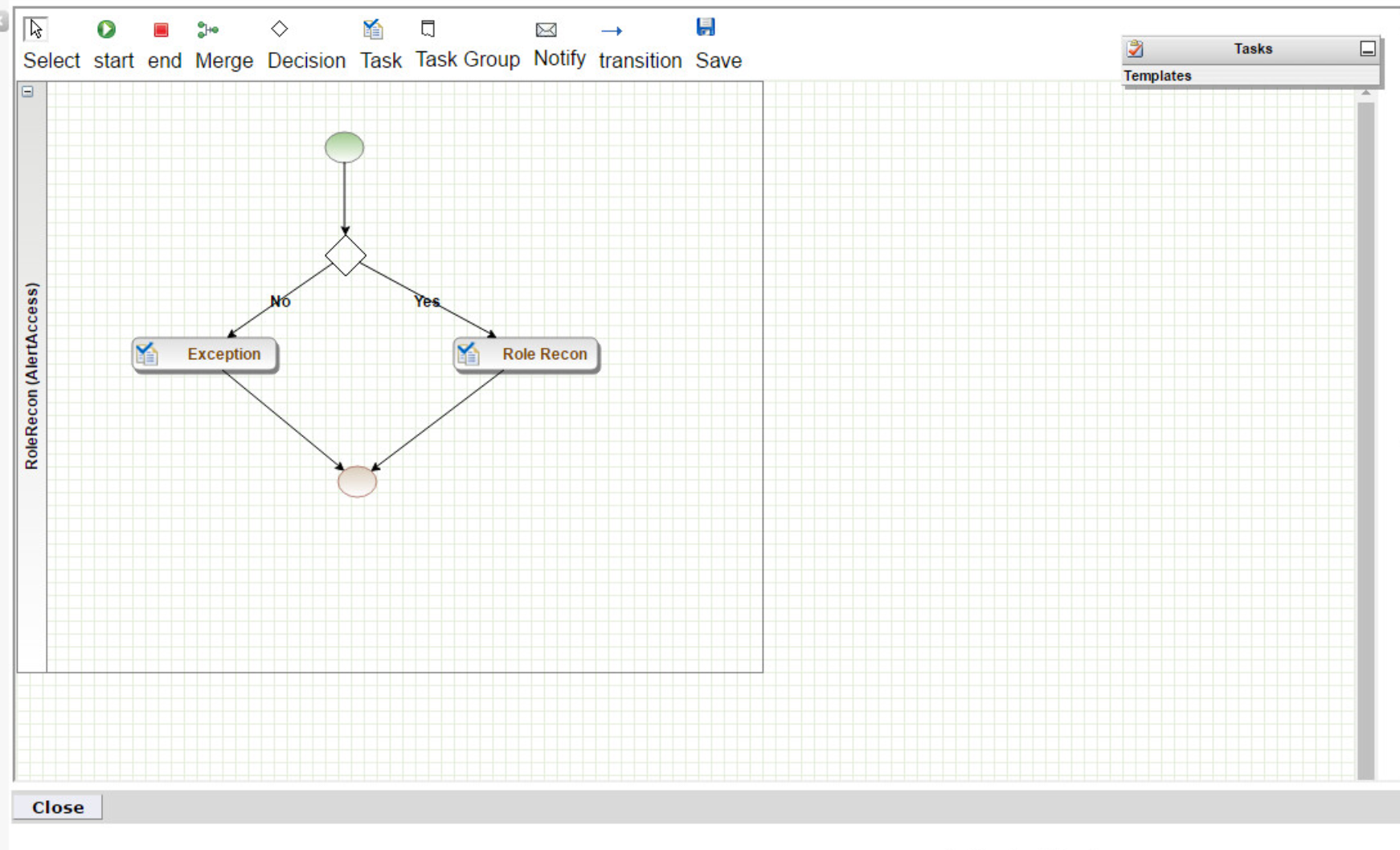
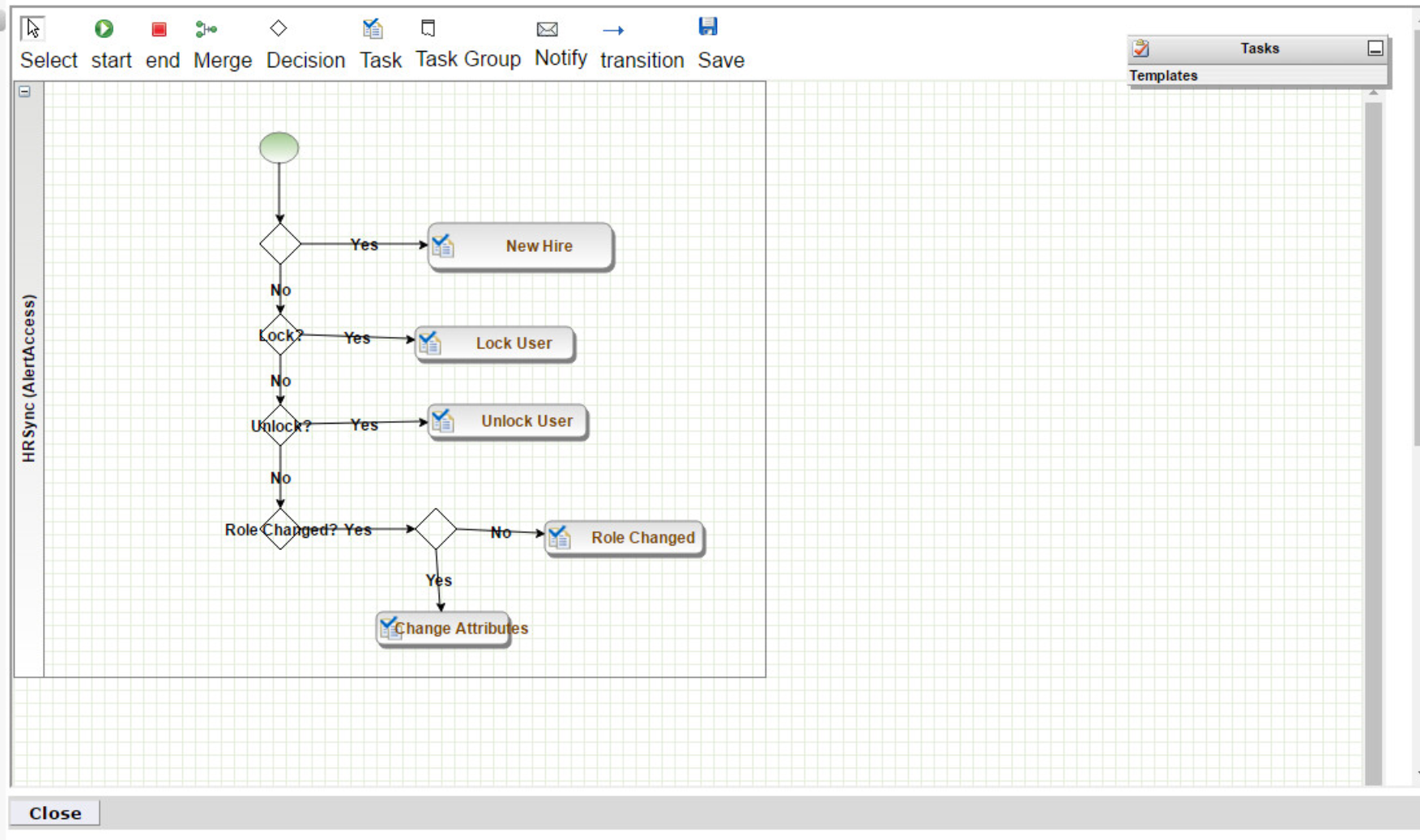
- Repeat Steps 1-4 for with HRSync as the Name and the following
policy:
2.1.19.1. Rule Action Handlers¶
- Navigate to Setup>Manual Configuration>Policy Engine>Rule Action Handler.
- Click Create. Create the following action handlers:
| Action Handler Name | Workflow | Task Type | Value | Priority | Update Identity Info | Evaluate Enterprises Role |
|---|---|---|---|---|---|---|
| Termination | AlertAccess | Recon Create Request | Termination | 0 | Yes | No |
| Recon Exception | AlertRecon | Recon Exception Record | 0 | |||
| NewHire | AlertAccess | Recon Create Request | NewHire | 0 | Yes | No |
| Rehire | AlertAccess | Recon Create Request | Rehire | 0 | Yes | No |
| UpdateRepo | AlertAccess | Update Identity Info | Yes | 0 | Yes | No |
| Role recon | AlertRecon | Recon Create role in Repo | 0 | |||
| ChangeAccess | AlertAccess | Recon Create Request | ChangeAccess | 0 | Yes | No |
| ChangeUser | AlertAccess | Recon Create Request | ChangeUser | 0 | Yes | No |
| Attribute Change | AlertAccess | Recon Create Request | Attribute Change | 0 | Yes | No |
2.1.19.2. Job Triggers¶
- Navigate to Setup>Manual Configuration>Job Scheduler>Triggers.
- Click Create. Create the following trigger:
| Name | HRSync |
| Description | HRSync |
| Type | Reconciliation |
| Batch Size | 100 |
| Number of Attempts | 3 |
| Policy Designer for Users | HRSync |
| Policy Designer for roles | RoleRecon |
| System:Reconciliation From | FILE CONNECTOR |
| Reconciliation System: | FILE CONNECTOR |
| Field Mapping Group | HR Sync |
| Process Deleted Option for Full Reconciliation | User Role |
| Process Deleted Option for Incremental Reconciliation | User Role |
2.1.20. Triggers Field Map¶
- Navigate to Setup>Manual Configuration>Job Scheduler>Triggers Field Map.
- Click Create. Create the following field map group:
| Group Name | Type |
| HR Sync | Reconciliation |
2.1.21. Form Customization¶
- Navigate to Setup>Manual Configuration>Form Customization>Attributes.
- Click Create. Create the following attributes:
| Name/Label | Attribute Type | Visible | Mandatory | Data Type | Field Type | Check Boxes |
|---|---|---|---|---|---|---|
| ADUserId | Custom | No | No | String | Textbox | Provisioning |
| LDAPUserId | Custom | No | No | String | Textbox | Provisioning |
| ADuserName | Custom | No | No | String | Textbox | Provisioning |
| LDAPuserName | Custom | No | No | String | Textbox | Provisioning |
| FirstName | Standard | Yes | Yes | String | Textbox | Provisioning |
| EmployeeNo | Custom | No | No | String | Textbox | Provisioning |
| BaseDN | Custom | No | No | String | Textbox | Provisioning |
| L | Custom | No | No | String | Textbox | Provisioning |
| Pager | Standard | Yes | Yes | String | Textbox | Provisioning |
| Initials | Standard | Yes | No | String | Textbox | Provisioning |
| Racfid | Custom | No | No | String | Textbox | Provisioning |
| Racfprogrammername | Custom | No | No | String | Textbox | Provisioning |
| Racfworkattrusername | Custom | No | No | String | Textbox | Provisioning |
| Racfaddressline1 | Custom | No | No | String | Textbox | Provisioning |
| Racfaddressline4 | Custom | No | No | String | Texbox | Provisioning |
Note: This list is not exhaustive. The application is deployed with several attributes preconfigured.
2.1.22. User Field Mapping¶
- Navigate to Setup>Manual Configuration>Identity & Access>User Field Mapping.
- Select Identity from the drop-down menu. Click Go.
- Click Create New.
- Create the following field mappings:
| Custom Field | Visible in List | isSearchable | Column Location |
|---|---|---|---|
| UserId | Yes | Yes | 1 |
| ValidFrom | No | No | 2 |
| ValidTo | No | No | 3 |
| FirstName | Yes | Yes | 4 |
| LastName | Yes | Yes | 5 |
| Alias | No | No | 6 |
| No | No | 7 | |
| ManagerId | No | No | 8 |
| Department | No | No | 9 |
| JobTitle | No | No | 10 |
| CompanyName | No | No | 11 |
| ManagerName | No | No | 12 |
| FullName | No | No | 13 |
| Mobile | No | No | 14 |
| User Base Dn | No | No | 15 |
| ADUserId | No | No | 16 |
| LDAPUserId | No | No | 17 |
| ADuserName | No | No | 18 |
| LDAPuserName | No | No | 19 |
| EmployeeNo | No | No | 20 |
| Initials | No | No | 21 |
| Pager | No | No | 22 |
| L | No | No | 23 |
| Racfid | No | No | 24 |
| Racfprogrammername | No | No | 25 |
| Racfworkattrusername | No | No | 26 |
| Racfaddressline1 | No | No | 27 |
| Racfaddressline4 | No | No | 28 |
2.1.23. Provisioning Mapping¶
- Navigate to Setup>Manual Configuration>Identity & Access>Provisioning>Provisioning Mapping.
- Select the connector and click Configure for the following connectors:
IDENTITYSTORE
| Database Attribute Name | Mandatory | AlertEnterprise Attribute Name | Default Value | Editable | Visible | Validation Flag | isUser-Id attribute |
|---|---|---|---|---|---|---|---|
| FullName | No | FullName | $<FirstName> $<LastName> | No | No | No | No |
OPENLDAP
| Database Attribute Name | Mandatory | AlertEnterprise Attribute Name | Default Value | Editable | Visible | Validation Flag | isUser-Id attribute |
|---|---|---|---|---|---|---|---|
| Cn | No | LDAPUserId | Yes | Yes | No | Yes | |
| Sn | No | LastName | Yes | Yes | No | No | |
| givenName | No | FirstName | Yes | Yes | No | No | |
| UserBaseDn | No | BaseDn | Yes | Yes | No | No | |
| uidNumber | No | uidNumber | 1 | Yes | Yes | No | No |
| gidNumber | No | gidNumber | 1 | Yes | Yes | No | No |
| homeDirectory | No | Homedirectory | Yes | Yes | No | No | |
| objectClass | No | UserObjectClass | inetOrgPerson| organizationalPerson| Person|Top| PosixAccount | No | No | ||
| No | Yes | Yes | No | No | |||
| userPassword | No | Password | Yes | Yes | No | No | |
| employeeNumber | No | EmployeeNo | Yes | Yes | No | No | |
| Mobile | No | Mobile | No | No | No | No | |
| DepartmentNumber | No | Department | No | No | No | No | |
| Title | No | JobTitle | No | No | No | No | |
| O | No | CompanyName | No | No | No | No | |
| loginShell | No | loginShell | No | No | No | No | |
| Uid | No | LDAPUserId | Yes | Yes | No | Yes | |
| L | No | L | No | No | No | no |
AD
| Directory Attribute Name | Mandatory | AlertEnterprise Attribute Name | Default Value | Editable | Visible | Validation Flag | isUser-Id attribute |
|---|---|---|---|---|---|---|---|
| sAMAccountName | No | ADUserId | Yes | Yes | No | Yes | |
| Sn | No | LastName | Yes | Yes | No | No | |
| givenName | No | FirstName | Yes | Yes | No | No | |
| accountExpires | No | ValidTo | Yes | Yes | No | No | |
| UserBaseDn | No | User Base Dn | Yes | Yes | No | No | |
| unicodePwd | No | Password | System@123 | Yes | Yes | No | No |
| displayName | No | DispalyName | $<LastName>, $<FirstName> | Yes | Yes | No | No |
| No | Yes | Yes | No | No | |||
| employeeNumber | No | EmployeeNo | No | No | No | No | |
| Mobile | No | Mobile | No | No | No | No | |
| Department | No | Department | No | No | No | No | |
| userPrincipalName | No | NISTEmptyDN | $<UserID>@AcmeFinancial.com | No | No | No | No |
| Title | No | JobTitle | No | No | No | No | |
| Company | No | CompanyName | No | No | No | No | |
| userAccountControl | No | UserAccountControl | 512 | No | No | No | No |
| **Pager ** | No | Pager | No | No | No | No | |
| Initials | No | Initials | No | No | No | no |
RACF_OPENLDAP
| Directory Attribute Name | Mandatory | AlertEnterprise Attribute Name | Default Value | Editable | Visible | Validation Flag | isUser-Id attribute |
|---|---|---|---|---|---|---|---|
| Racfid | Yes | Racfid | No | No | No | Yes | |
| Racfworkattrusername | No | Racfworkattrusername | No | No | No | No | |
| UserBaseDn | Yes | homeDirectory | profiletype=user, sysplex=sysplex1 | No | No | No | No |
| objectClass | No | UserObjectClass | racfUser | No | No | No | No |
| Racfprogrammername | No | Racfprogrammername | No | No | No | No | |
| Racfaddressline1 | No | Racfaddressline1 | No | No | No | No | |
| Racfaddressline4 | No | Racfaddressline4 | No | No | No | No |
2.1.24. External Provisioning Attributes¶
- Navigate to Setup>Manual Configuration>Identity & Access>Provisioning>External Provisioning Attributes.
- Select the connector and click Configure for the following connectors:
OPENLDAP
| Name | Description |
|---|---|
| loginShell | loginShell |
RACF_OPENLDAP
| Name | Description |
|---|---|
| Racfid | Racfid |
| Racfworkattrusername | Racfworkattrusername |
| UserBaseDn | UserBaseDn |
| objectClass | objectClass |
| Racfprogrammername | Racfprogrammername |
| Racfaddressline1 | Racfaddressline1 |
| Racfaddressline4 | Racfaddressline4 |
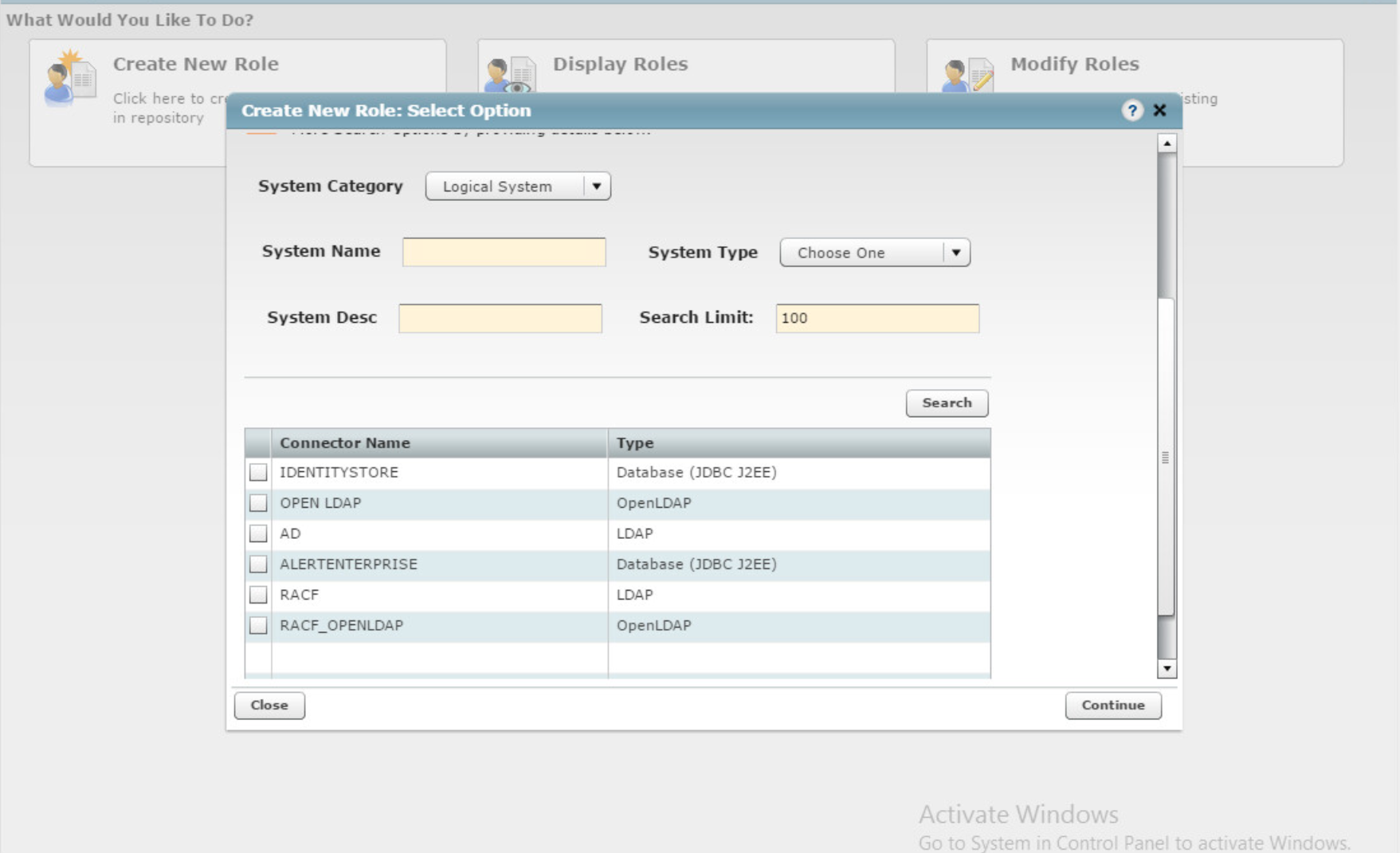
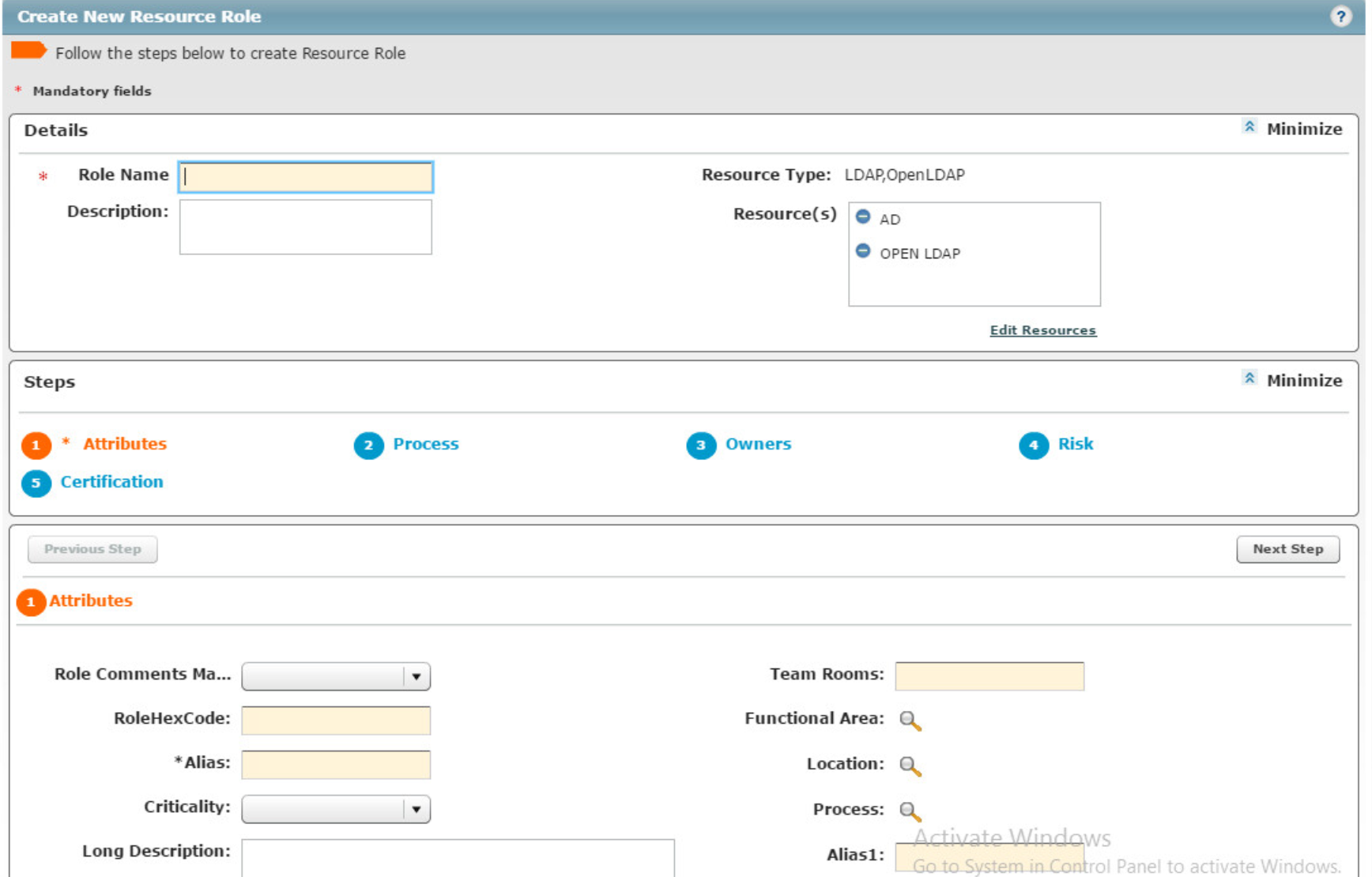
2.1.25. Role Repository¶
Navigate to Setup>Manual Configuration>Role Repository.
Click Create New Role to begin.
Select Create New Role from Start.
Click Search to load the connector names. Select the OpenLDAP and AD connectors.
Click Continue.
Select Yes for Active for Provisioning and Provisioning Assigned.
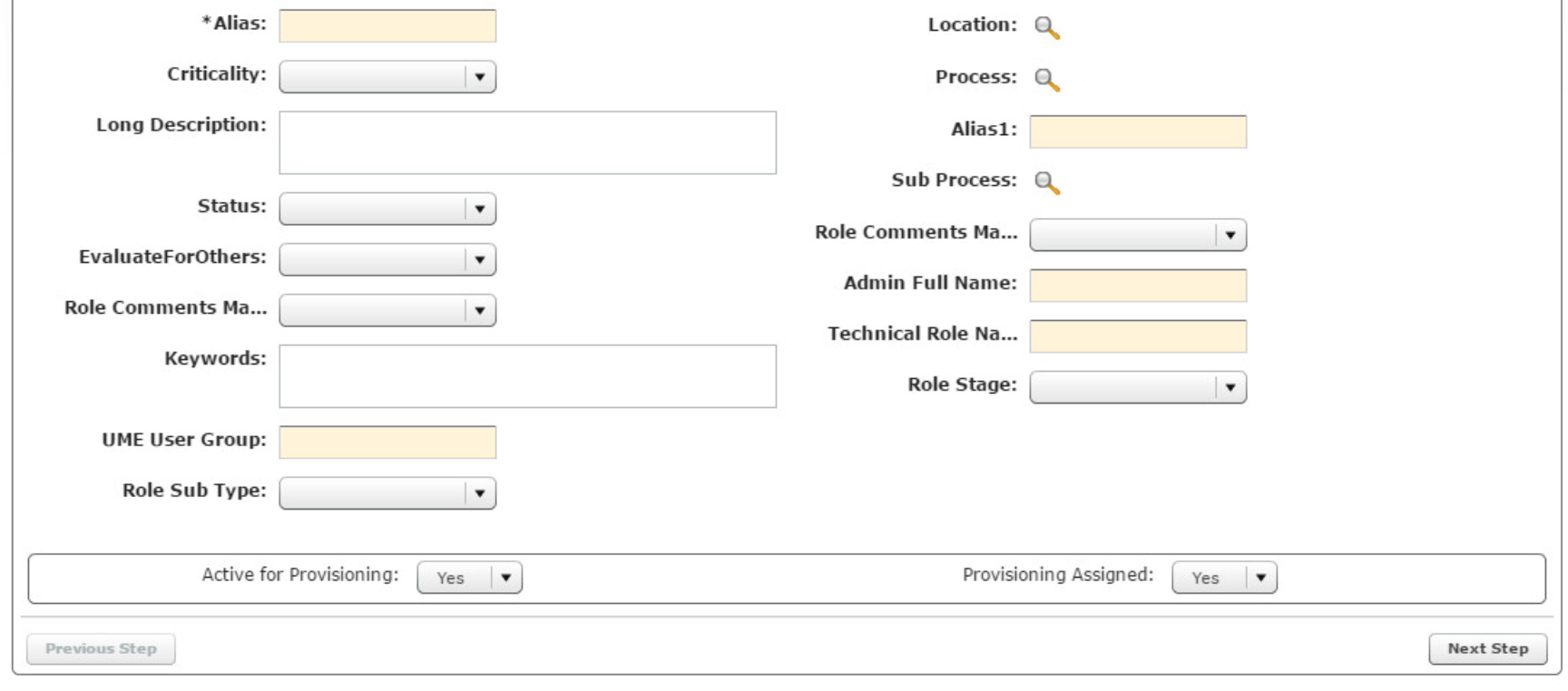
Create the following roles in the repository:
| Role Name | Resource(s) |
|---|---|
| Accounting Manager | AD, OpenLDAP |
| Branch Manager | AD, OpenLDAP |
| Financial Analyst | AD, OpenLDAP |
| Financial Manager | AD, OpenLDAP |
| Loan Officer | AD, OpenLDAP |
| Operations Manager | AD, OpenLDAP |
| Security Analyst | AD, OpenLDAP |
| Systems Admin | AD, OpenLDAP |
| Teller | AD, OpenLDAP |
| VM Admin | AD, OpenLDAP |
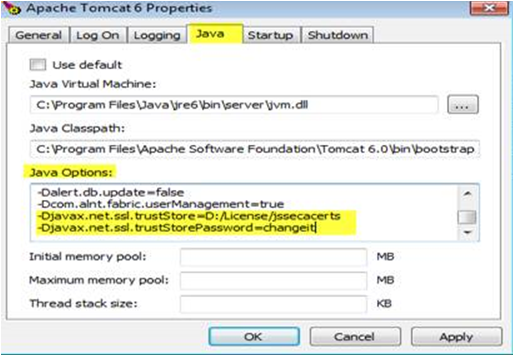
2.1.26. Enabling SSL¶
To better secure LDAP communications between AlertEnterprise Enterprise Guardian and the directory servers, we have configured such communications to use SSL encryption. Specifically, the LDAPS protocol has been configured. The steps to configure LDAPS for each connection to a directory server are as follows:
Create a D:\cert\folder on your system.
Place certificate jar file inside that folder.
Open the command prompt in administrator mode and perform the command:
cd D:\cert\Download certificate from directory server using the following command:
java -cp ALNTADCertUtil.jar com.alnt.ADCertInstaller <IP_Address_Of_Directory_Server>:636
This creates the jssecacerts file in D:\cert\ folder.
Add the following D parameters in <Tomcat Installation Folder>/bin/Tomact6w .. rst-class:: bold
-Djavax.net.ssl.trustStore=D:/License/jssecacerts -Djavax.net.ssl.trustStorePassword=changeit
Copy jssecacerts to D:/License (create this folder if it does not exist) and restart Tomcat.
Switch connection back to 636 port and set SSL as true from false.
2.2. HyTrust Cloud Control¶
HyTrust CloudControl provides a variety of security and policy enhancements to the virtual infrastructure without impacting the GUI tha vSphere, NSX and ESXi admins already know and use. HyTrust CloudControl mediates the actions taken by virtual infrastructure administrators using familiar interfaces. Approved actions are allowed, disapproved actions are blocked and additional approval workflow is enabled.
2.2.1. How Its Used¶
HyTrust CloudControl (HTCC) is used as a centralized point of control for access management within the virtual infrastructure of this example implementation.
2.2.2. Virtual Machine Configuration¶
HTCC uses one ESXi host and two virtual machines for its infrastructure. One virtual machine is the HTCC appliance. This virtual machine is delivered as an .OVF file from the HyTrust support site. The other virtual machine is a VCenter server, which is installed as a virtual machine within the ESXi host.
Note: The ESX host and HTCC Virtual Machine requirements depend on the specific load of a protected virtual environment. See the HTCC installation guide for a complete list of system requirements.
VCenter Server:
- Windows Server 2012 R2
- 2 CPU core
- 16GB of RAM (memory)
- 1 NIC
- 60GB of storage
HTCC:
- CentOS 4/5/6/7 (64-bit)
- 4 CPU core
- 16GB of RAM (memory)
- 1 NIC
- 70GB of storage
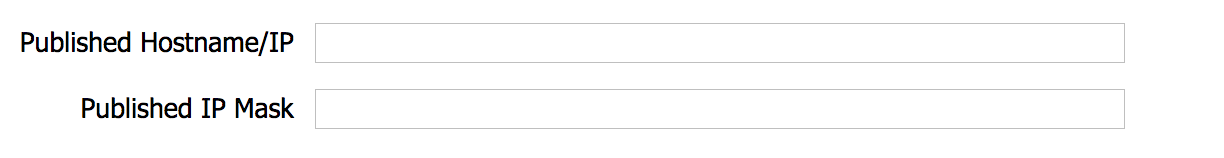
Network Configuration (VCenter Server)
Network Configuration (HTCC)
2.2.3. Installing Vcenter Server¶
Install Vcenter Sever 6.0 according to the VMware documentation found here.
2.2.4. Configuring Vcenter Server¶
Vcenter server is configured with 1 host and 1 data center.
ESXi Host:
- VMware ESXi, 6.0.0
- Dell PowerEdge R620
- 20 CPUs x 2.8 GHz
- 23,478 mb / 262,098 mb
- 8 Physical Adapters
2.2.5. Deploying HTCC¶
Before installing the HTCC appliance, the following conditions should be in place:
- Virtual infrastructure, consisting of installed vCenter Servers and, optionally, ESX hosts.
- Network connectivity and access to the HTCC host machine.
- The HTCC installation requires an ESX host with at least one dedicated network interface (using VLANs).
- For Directory Service mode authentication, setup of Microsoft Active Directory (AD) with an AD Service Account and the recommended HyTrust security groups, as described in the HyTrust CloudControl Administration Guide.
- Services used by virtual infrastructure clients should be routable from the appropriate interface.
See the HTCC installation guide for a step-by-step guide on deploying the HTCC appliance. The installation guide is available on request.
2.2.6. Configuring HTCC¶
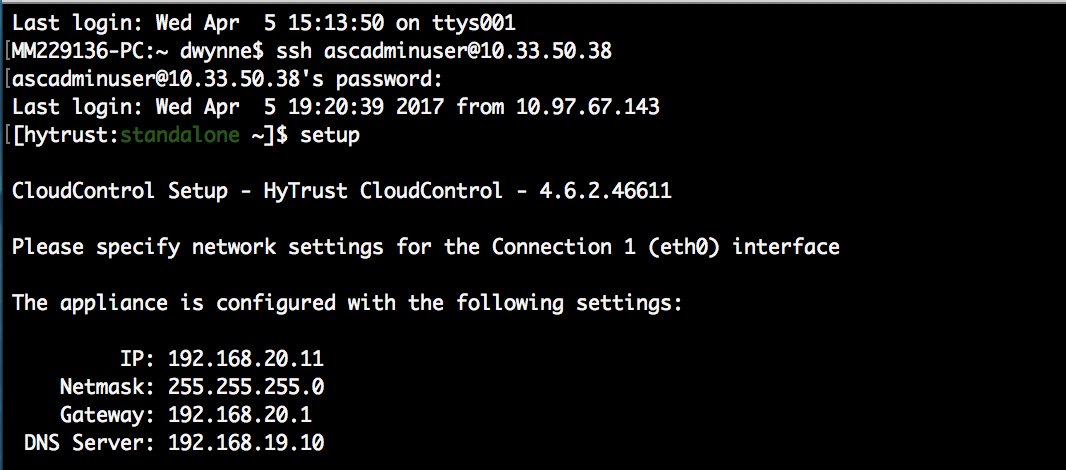
The HTCC Management network interface (eth0) must be manually configured before you can access the HTCC Management Console.
Configure the HTCC Management network interface:
At the vSphere Client console window, log in as the user ascadminuser with the password Pa$$w0rd123!.
You are prompted to assign a new password to the local HTCC administrator account (ascadminuser). Be sure to keep your new password in a safe and secure place.
Start the setup procedure. At the prompt, type: setup
Manually assign a static IP address to the management network interface (eth0) and set the subnet mask, gateway, and DNS server addresses.
Save by typing:
yLog out after network settings have been saved. This build is configured with the following settings:
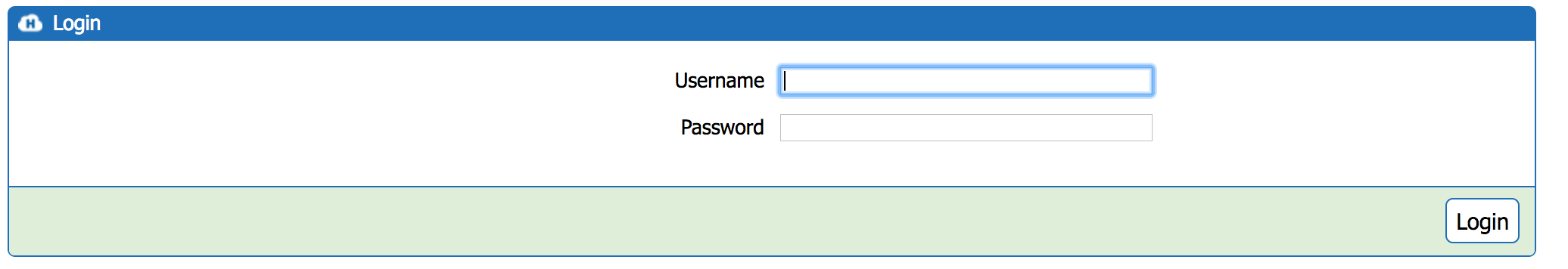
The HTCC web-based management console is used to customize the HTCC
settings. When accessing HTCC for the first time, you must use the IP
address in the URL. For example: https://<ipaddress>/asc
- Enter the IP address of the HTCC Management network interface.
- Manually allow the security exception.
Once logged in, you can complete the initial setup and configuration. Here is an overview of the initial setup and configuration steps. The detailed steps can be found in the HTCC installation guide, which is available on request.
- Accept the end-user license agreement.
- If applicable, install a license.
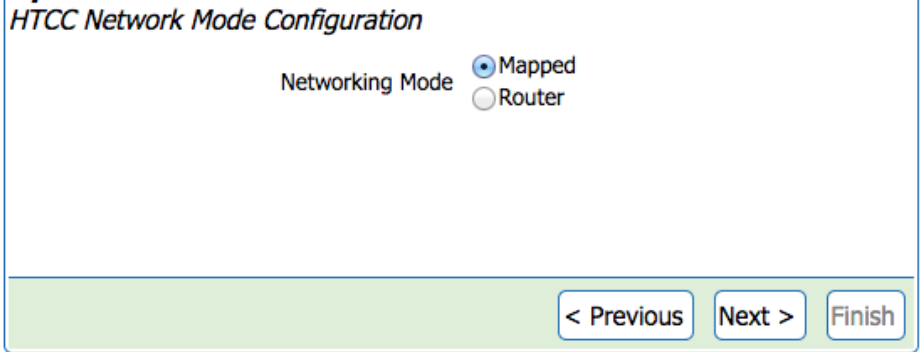
- Complete the HTCC Installation Wizard based on your selected networking mode.
- Perform post-installation setup.
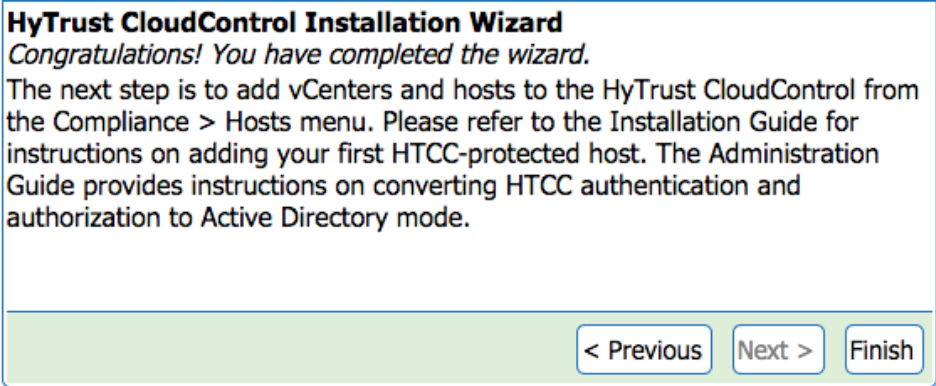
HTCC Installation Wizard:
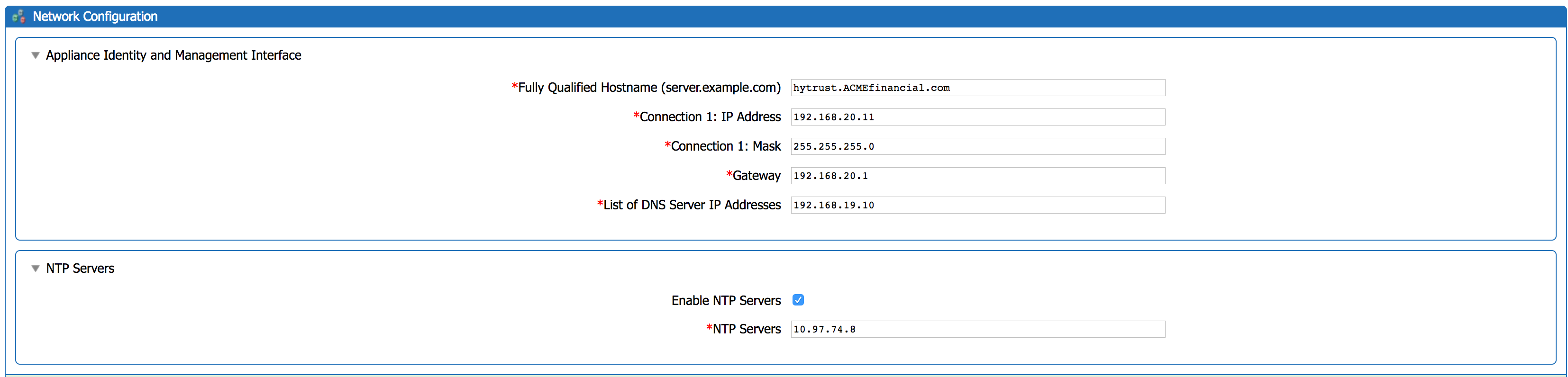
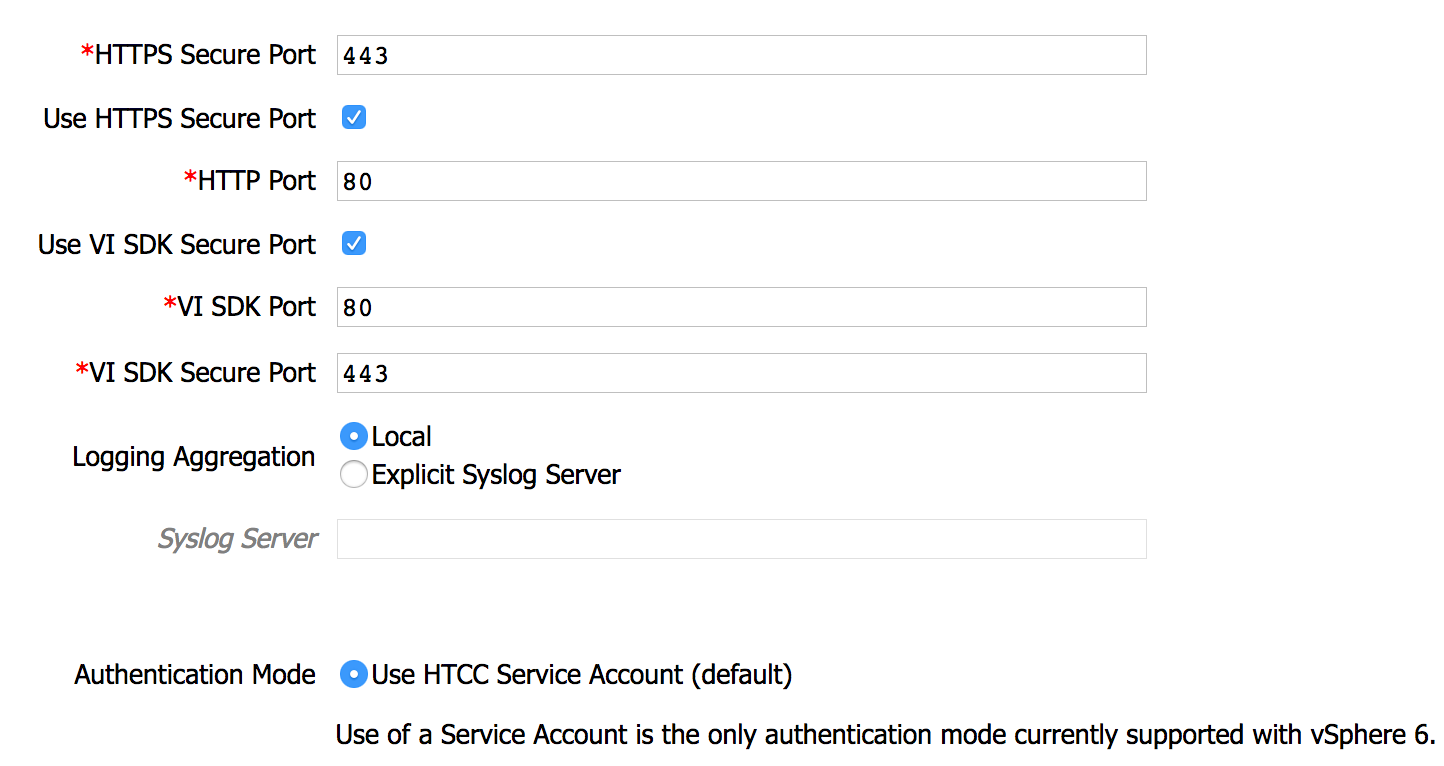
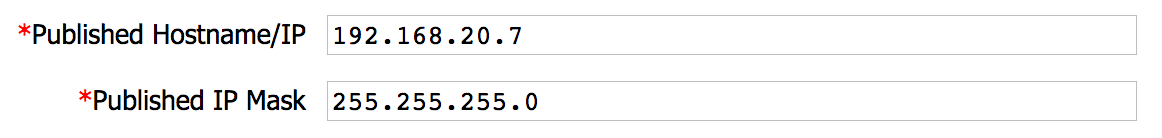
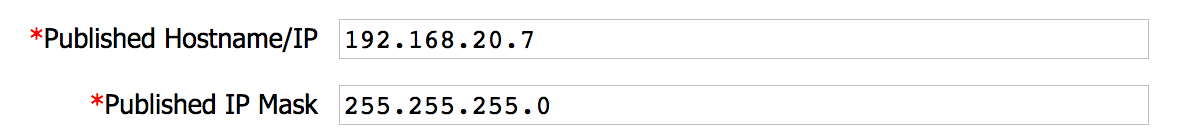
Specify the network information on the Network Configuration page. This build is configured as follows:
Add VCenter and Hosts to the HTCC:
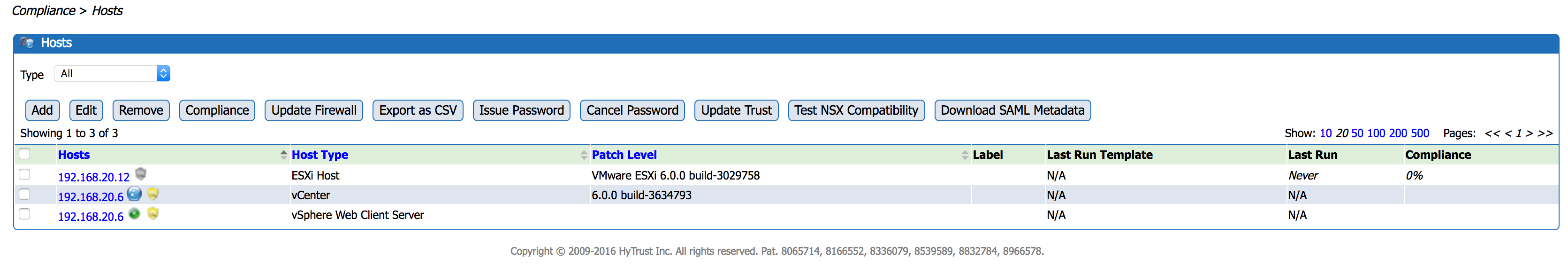
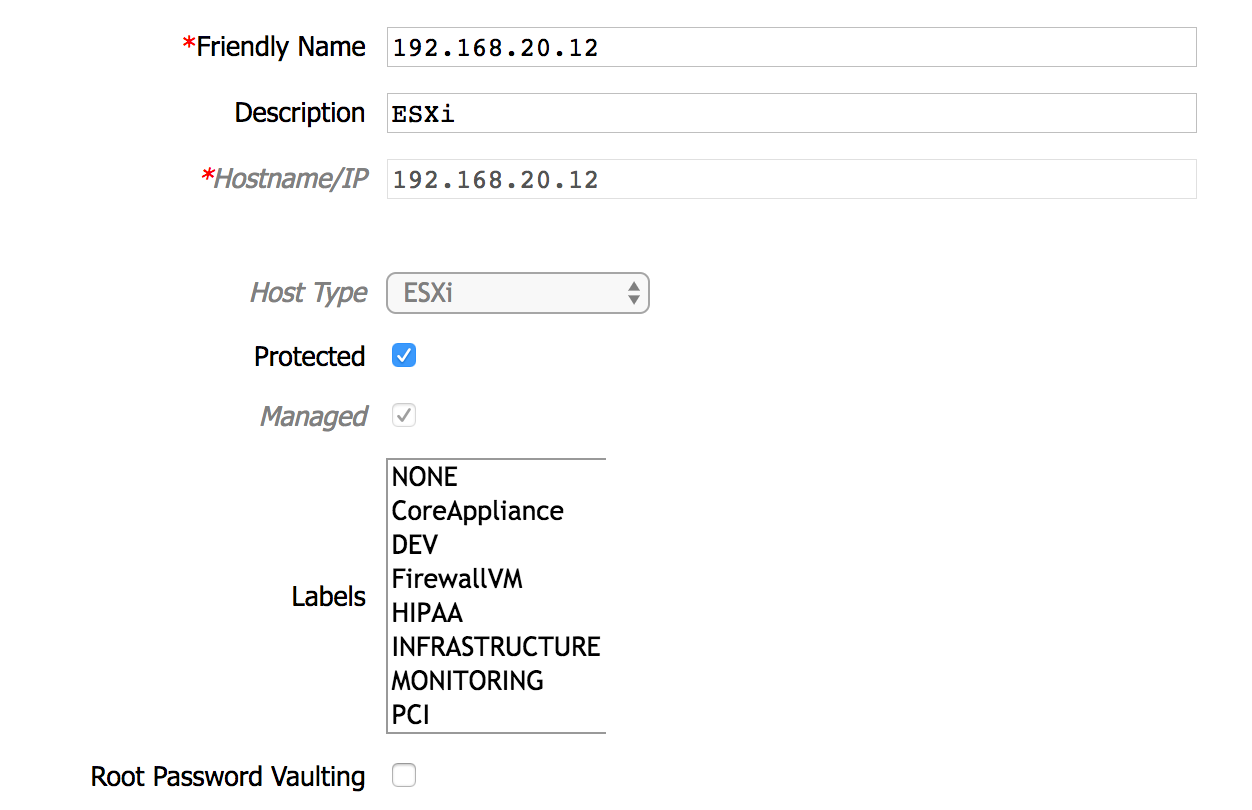
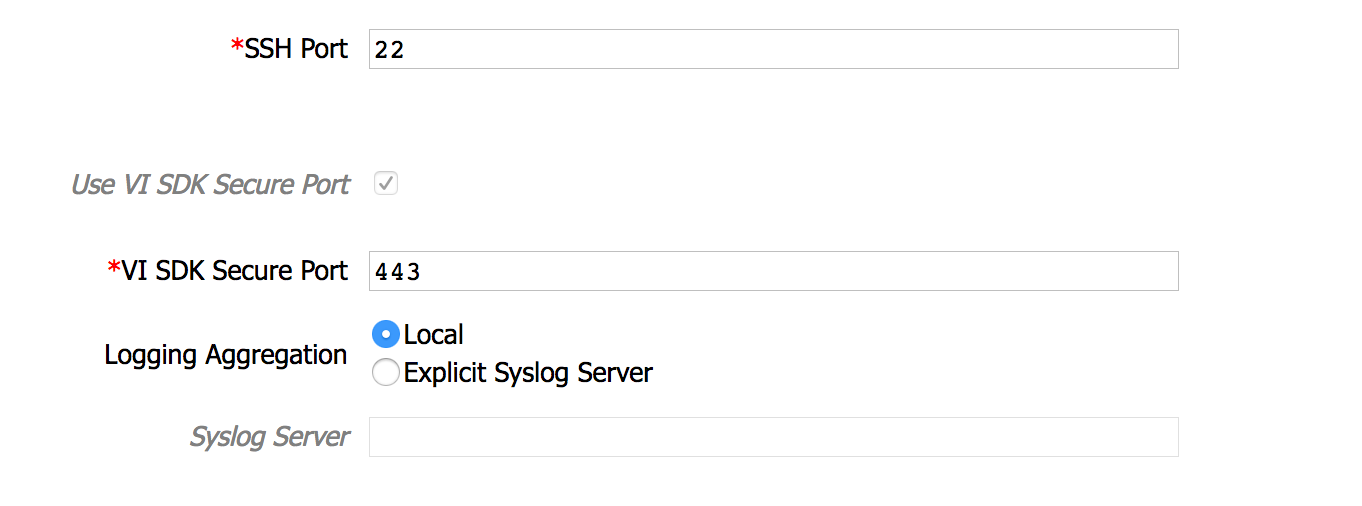
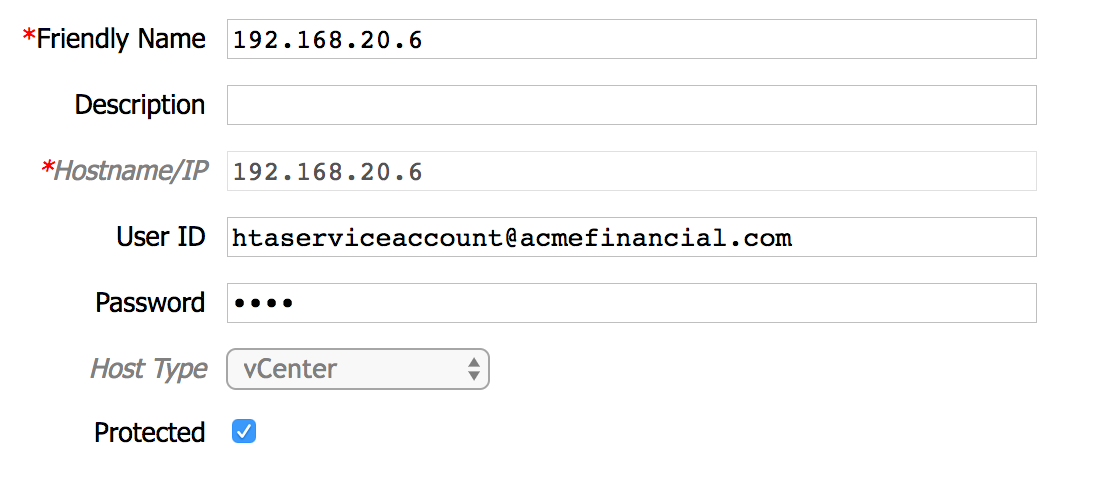
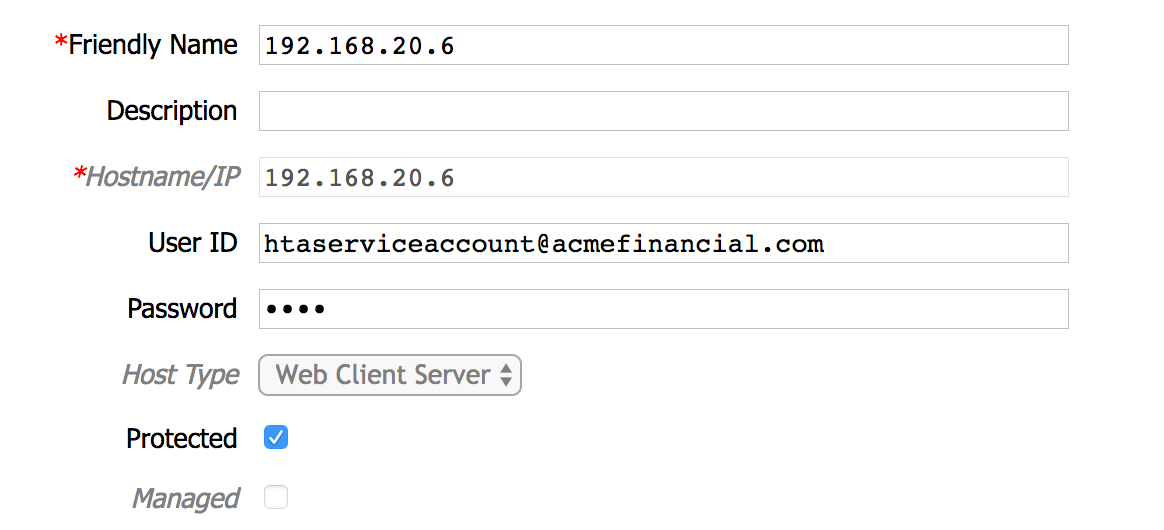
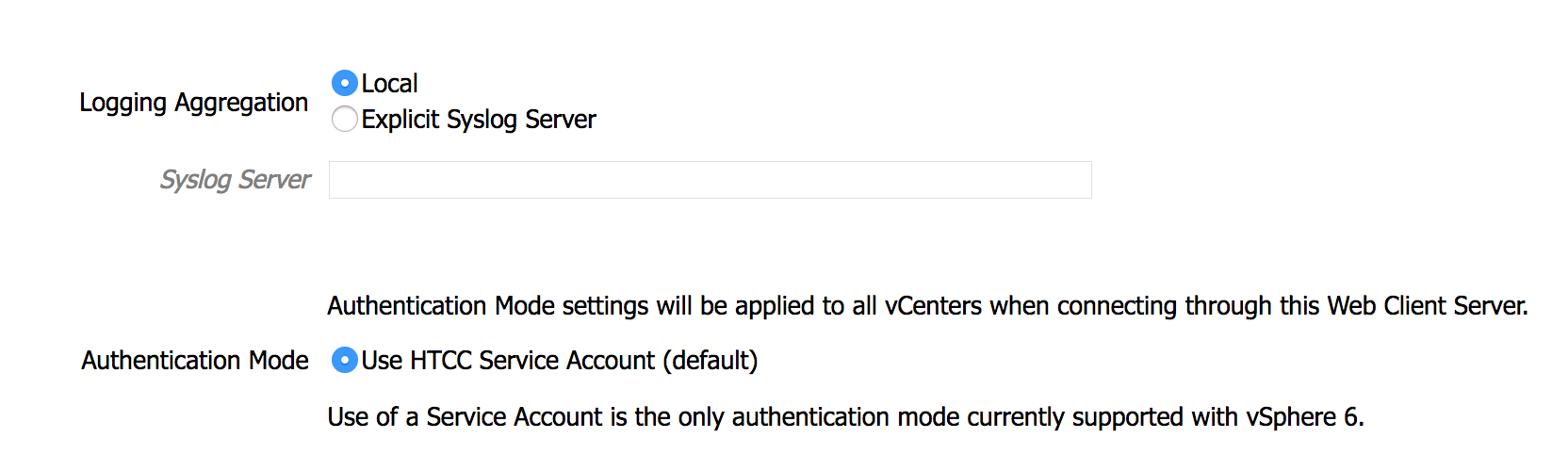
In this build, three managed hosts are added. The three hosts are ESXi, Vcenter, and Vcenter Web Client Server. For the full list of options for the host and detailed steps of adding a host, see the HTCC installation guide. The configurations of each added host are as follows:
ESXi:
Note: Ensure that each host is protected.
vCenter:
Note: The htaserviceaccount must be created in Active Directory first. See Integrating with Active Directory.
vSphere Web Client Server:
2.2.7. Integrating With Active Directory¶
In this build, HTCC is integrated with Active Directory. Users who have access to the virtual environment have accounts in AD and are a part of the ‘hytrust users’ group.
First, you must create a service account in Active Directory with the following permissions. In this build, the htaserviceaccount is created.
- Domain object: Read memberOf
- User object: attributes memberOf and distinguishedName
- Group object: attributes member, memberOf, and distinguishedName
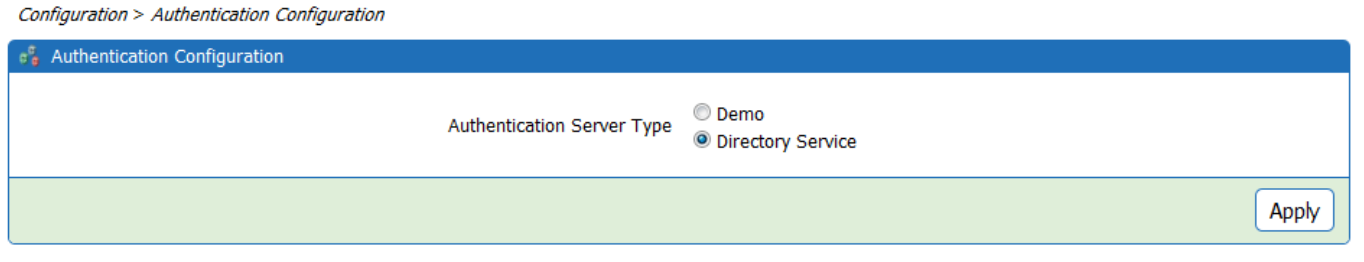
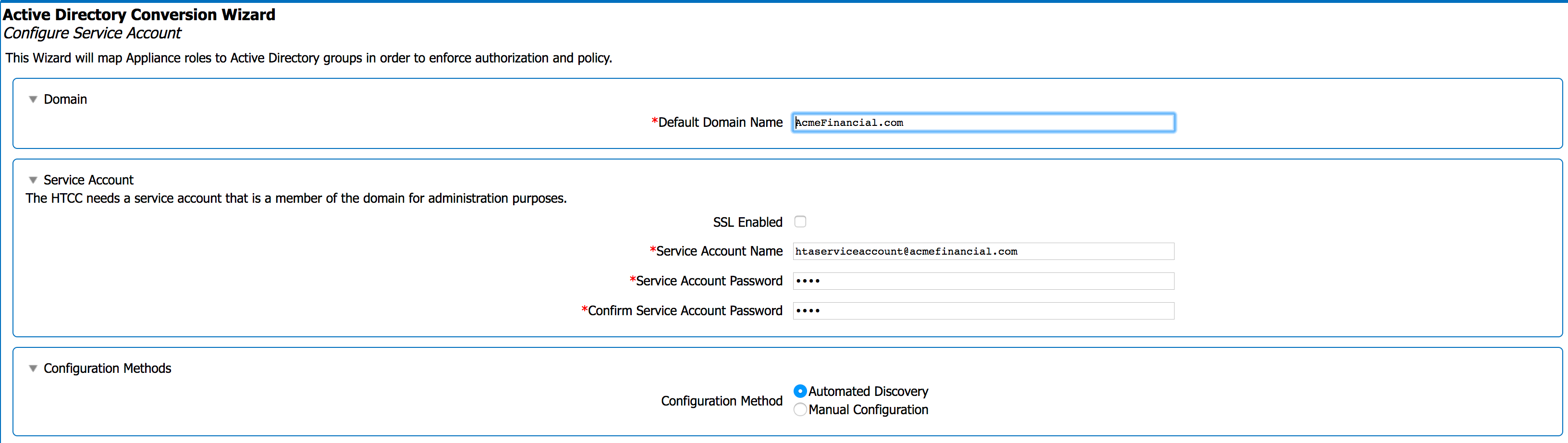
To convert HTCC to Directory Service mode:
Open the Authentication Configuration page (Configuration > Authentication).
Select the Directory Service radio button and click Apply.
The Active Directory Conversion Wizard opens, which guides you through the steps to connect HTCC to your directory service.
Use the Service Account panel to specify the AD HTCC service account information. Select Automated Discovery. Click Next.
Check View Active Directory Advanced Settings to view advanced settings. Otherwise, select Next.
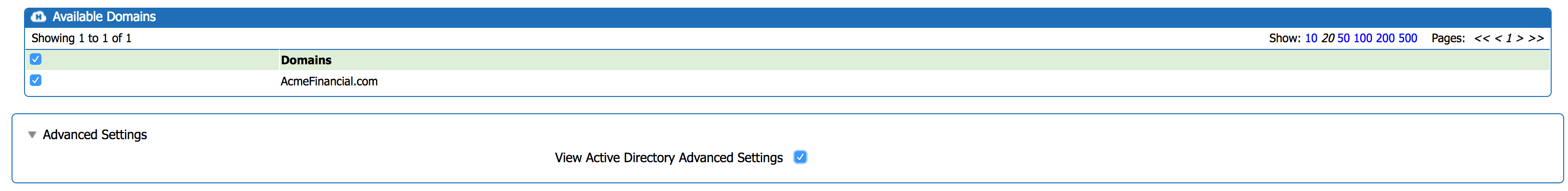
The Rule Conversion page appears where you can map HTCC roles to AD groups. For this build, we mapped the ASC_SuperAdmin role to the Enterprise Admins Group.
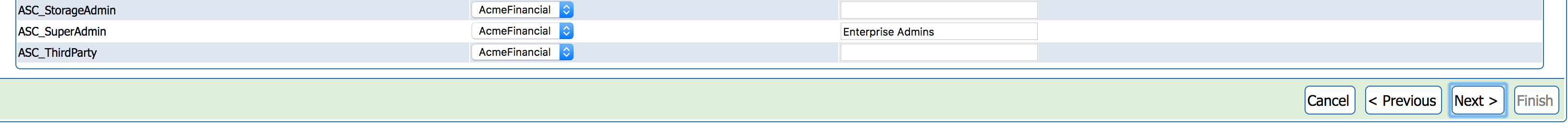
Note: At a minimum, one Active Directory security group (e.g., SuperAdmin) must be mapped to HTCC ASC_SuperAdmin role for AD conversion to be successful.
- Click Next.
A summary page appears confirming the AD settings. Review the information to make sure the Domain Controllers, Rule Conversion, and Service Account settings are accurate.
- Click Finish to convert HTCC to Directory Service mode.
Perform the following steps to create the HTCC security groups in AD:
- Create a security group for each HTCC you choose. For this build, two groups called ‘Hytrust Users’ and ‘Hytrust Users 2’ are created.
- For each group, assign the Group scope to Global and the Group type to Security.
For additional configuration options for integrating with Active Directory. see the HTCC Administration Guide, which is available on request.
2.2.8. Creating and Deploying Access Policies¶
Before creating and deploying access policies on a virtual infrastructure, confirm that HTCC is protecting the vCenter Server and all the imported hosts. See the HyTrust CloudControl Installation Guide for assistance in importing a vCenter Server, adding a host, or protecting these resources.
After importing a vCenter Server protected host, HTCC adds the vCenter Server object structure to a new draft policy and deploys it automatically.
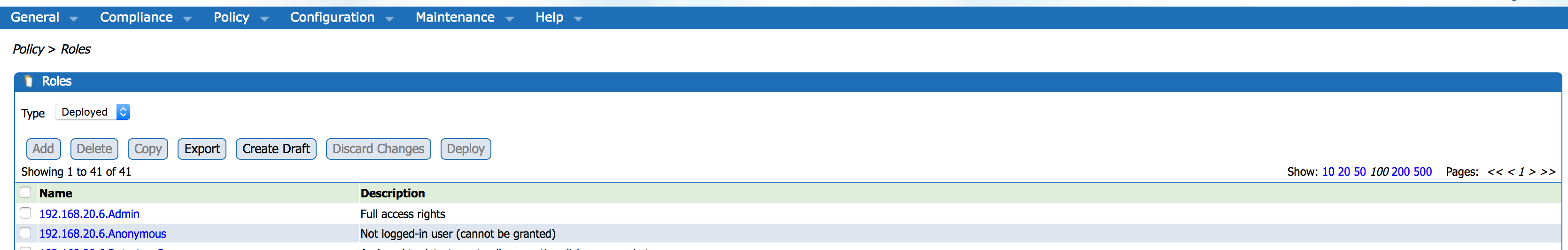
Any time a new virtual machine is created or a new host is added, the new object is automatically added to the HTCC policy and the deployed policy is enforced on the new object. To view the current policy, navigate to Policy>Resources. The Deployed policy is the policy that is currently in effect.
To make a change in the deployed policy, such as adding a new rule to a protected host, follow these steps:
- Open any Policy page.
- Click the Create Draft button. This copies the “Deployed” policy to a “Draft” policy.
- Make your desired changes to the Draft policy using the various policy pages.
- Click the Deploy button to replace the current Deployed policy with the Draft policy.
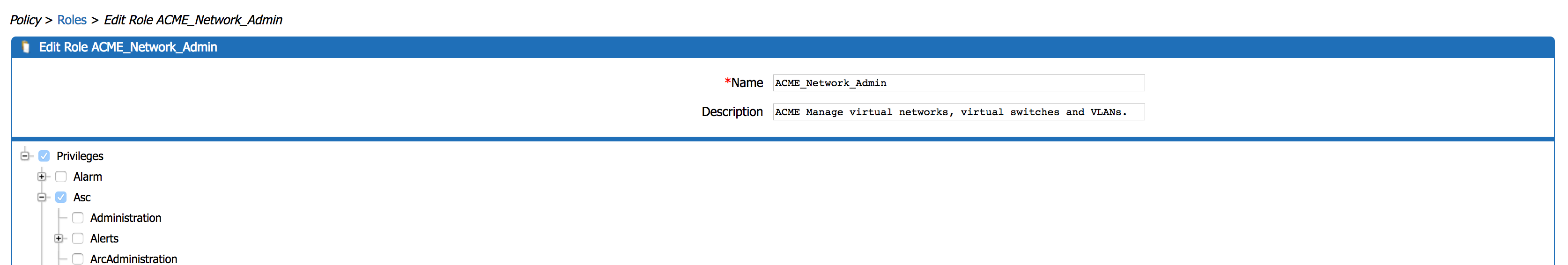
For this build, two roles are created called ACME_Network_Admin and ACME_Systems_Admin. To create the rules and roles used to demonstrate the access rights management capability, follow these steps:
Navigate to Policy>Roles.
Select Add. First, create the network admin role. Then, name the role and provide a description.
Select all of the following permissions:
- Asc>NxOsConfig, NxOsShow, NxOsXmlApi,ssh,storage
- DVPortgroup>Entire List (Note: This configuration item is deprecated in versions 5.1 and above of the product.)
- DVSwitch>Entire List
- DataCenter>IpPoolConfig,IpPoolQueryAllocations,IpPoolReleaseIp
- Global>CancelTask,LogEvent
- Host>Config>AdvancedConfig,NetService,Network,PciPassthru
- Network>Assign,Delete,Router
- Resource>Delete
- System>Entire List
- Task>Entire List
- VirtualMachine>Config>ManagedBy,MultiActions
Press OK.
Press Deploy.
Repeat Steps 2–6 to create the system admin role, but with the following permissions selected:
- Global>CancelTask,LogEvent
- System>Entire List
- Task>Entire List
- VApp>Entire List
- VirtualMachine>Entire List
Next, you must create the rules that will apply the roles to the host. First, create the rule for the system admins role, assigning it to the ‘HyTrust Users’ AD group.
- Navigate to Policy>Rules.
- Select Create Draft.
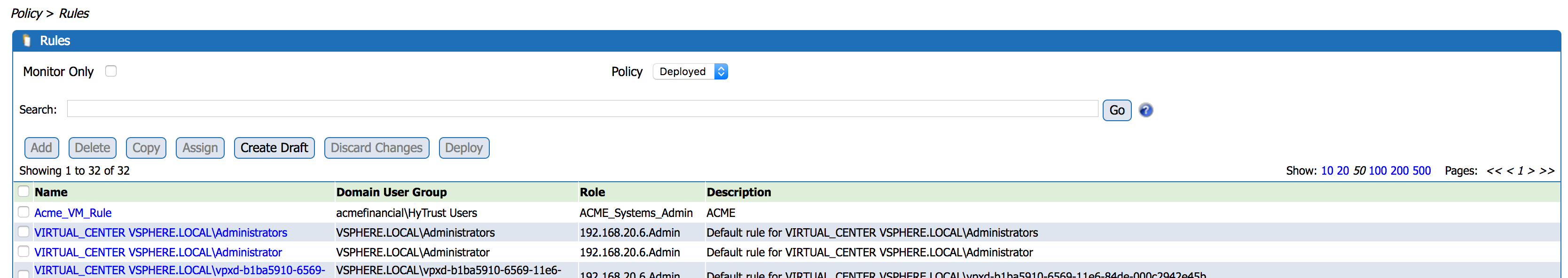
- Select Add. Name the rule and type in the user group created in
Active Directory.
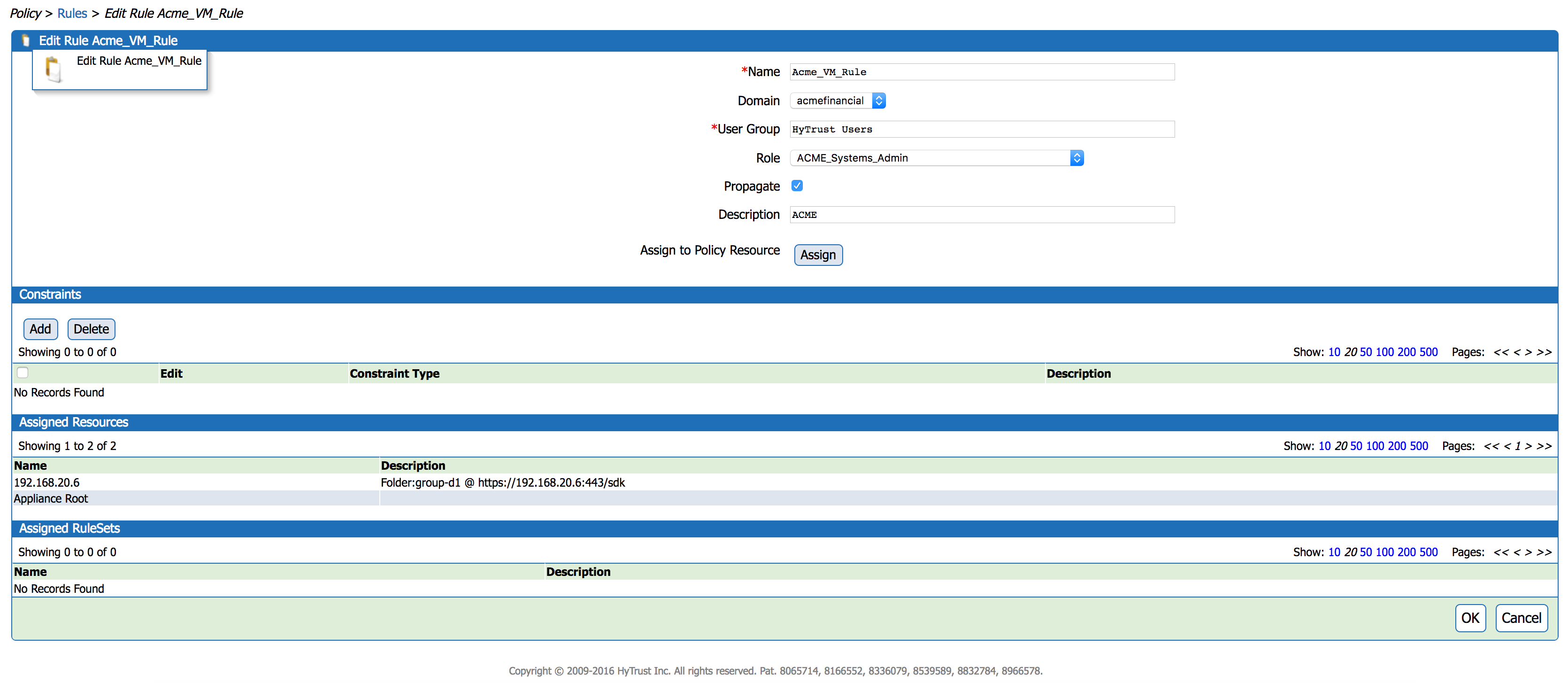
- Select Assign.
- Check the HyTrust CloudControl Appliance Root radio
button.
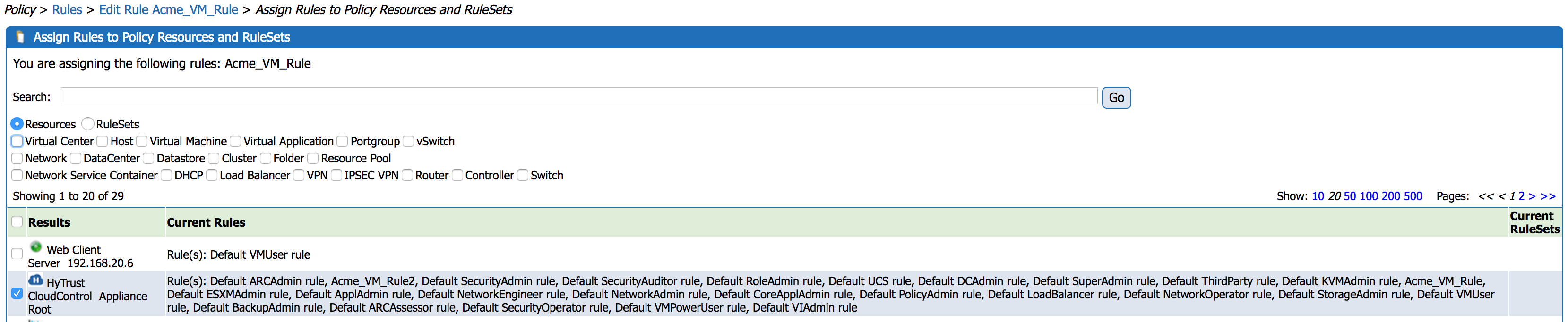
- Select OK.
- Select OK.
- Select Deploy.
- Repeat Steps 1–9 to create a rule for the network admins role, assigning it to the ‘Hytrust Users 2’ active directory group.
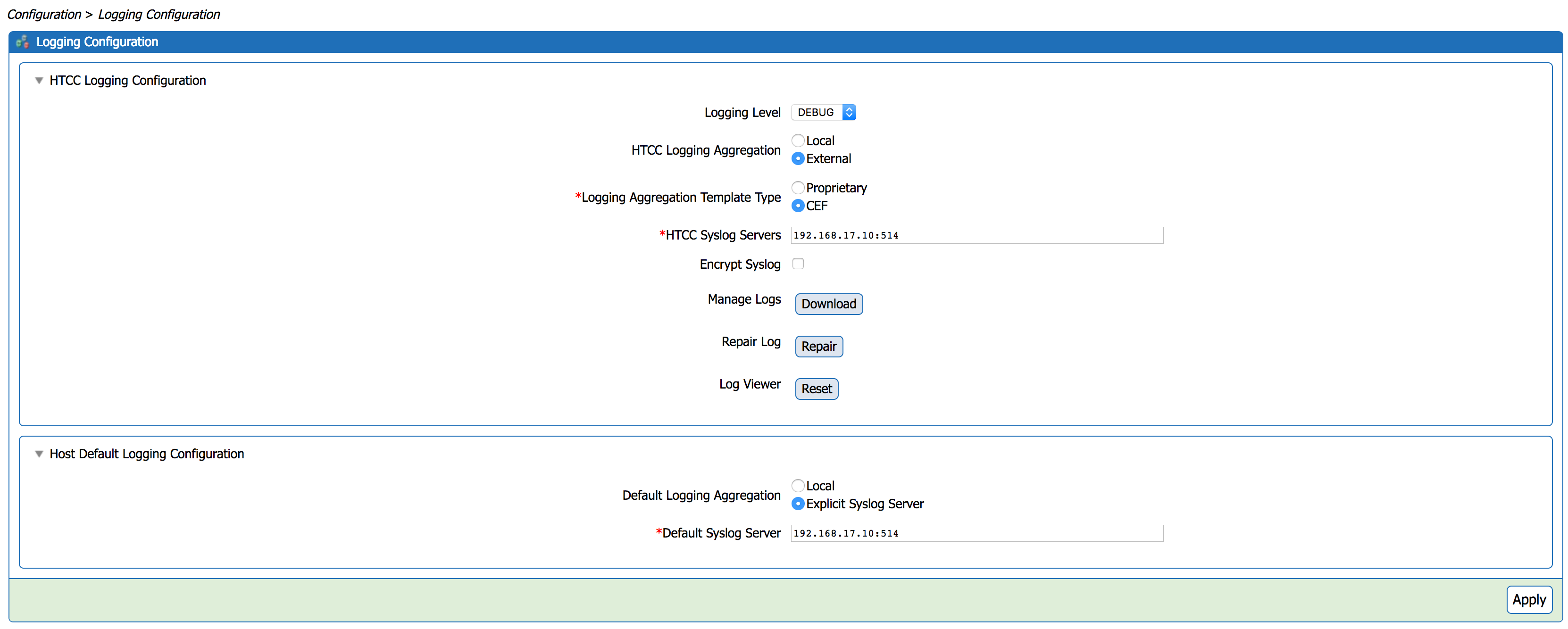
2.2.9. Configure Logging¶
2.3. Microsoft Active Directory¶
An LDAP directory service that stores user account and attribute information.
2.3.1. How It’s Used¶
Microsoft AD acts as one of the user identity management repositories in the example solution. AD can provision and de-provision user identities; the creation, modification, and deletion of subject attributes; and the provisioning and de-provisioning of subject attributes to specific user identities. Administration of user identity and attribute provisioning is controlled by AlertEnterprise Enterprise Guardian. AD is also used for its logging and auditing of user identity and attribute provisioning administration.
2.3.2. Virtual Machine Configuration¶
The AD virtual machine is configured as follows:
- 1 CPU Core
- 4GB RAM
- 84GB HDD
- 2 Network Adapters
Network Configuration (Interface 1)
2.3.3. Installing AD¶
Install a new Windows server 2012 R2 Active Directory Forest:
The name of the domain used for this build is AcmeFinancial.com.
2.3.4. DNS Configuration¶
- Create the following host records in the AcmeFinancial.com forward lookup zone:
| Name | FQDN | IP address |
|---|---|---|
| Activedirectory | Activedirectory.acmefinancial.com | 192.168.19.10 |
| ADBackup | ADBackup.acmefinancial.com | 192.168.19.12 |
| ConsoleWorks | Consoleworks.acmefinancial.com | 192.168.17.11 |
| Openldap | Openldap.acmefinancial.com | 192.168.19.11 |
| Racf | Racf.acmefinancial.com | 172.17.212.10 |
| RadiantOne VDS | RadiantOne VDS.acmefinancial.com | 192.168.14.111 |
| RadiantOne VDS | RadiantOne VDS.acmefinancial.com | 192.168.17.100 |
| Sharepoint2 | Sharepoint2.acmefinancial.com | 192.168.17.113 |
| Splunk | Splunk.acmefinancial.com | 192.168.17.10 |
| VcenterServer | Vcenterserver.acmefinancial.com | 192.168.20.6 |
- Create the following IPv4 reverse lookup zones:
| Name |
|---|
| 14.168.192.in-addr.arpa |
| 17.168.192.in-addr.arpa |
| 19.168.192.in-addr.arpa |
| 20.168.192.in-addr.arpa |
| 212.17.212.in-addr.arpa |
2.3.5. Installing Splunk Universal Forwarder¶
Note: You will need a Splunk account to download the Splunk Universal Forwarder. It is free and can be set up at: https://www.splunk.com/page/sign_up
Download the Splunk Universal Forwarder from: http://www.splunk.com/en_us/download/universal-forwarder.html
You want the latest version for OS version Windows (64-bit). Because this is installing on Windows, select the file that ends in .msi. An example is: spunkforwarder-6.4.2-00f5bb3fa822-x64-release.msi
2.3.6. Install Security Compliance Manager¶
Install Microsoft Security Compliance Manager: https://www.microsoft.com/en-us/download/details.aspx?id=53353
2.3.7. Group Policy Object (GPO) Configuration¶
Auditing is enforced using the Microsoft Group Policy feature. Group policy auditing is administered with Microsoft Security Compliance Manager (SCM). Details for downloading and installing SCM can be found here.
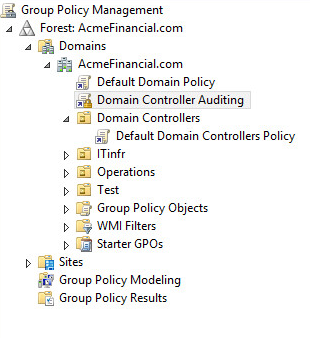
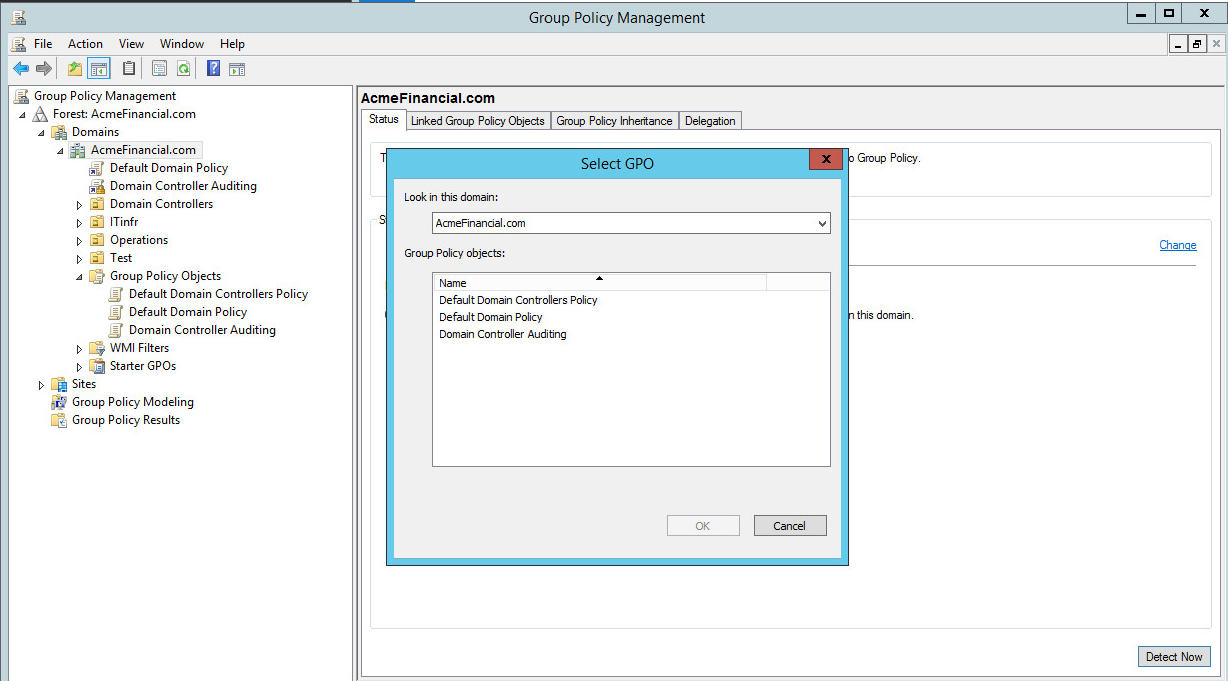
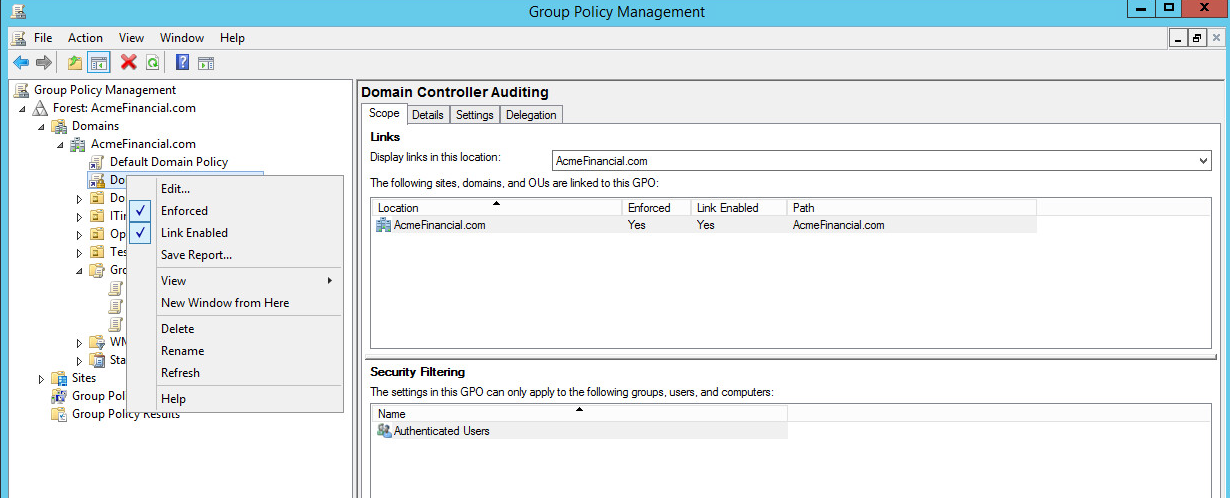
SCM consist of baseline configurations based on Microsoft security guide recommendations and industry best practices. In this build, the Domain Controller Security Policy is deployed using SCM to established a benchmark. The .CAB file is included in the SCM. In our build, we deployed this benchmark named as “Domain Controller Auditing.” For directions for deploying a benchmark,see the Microsoft documentation found here.
Group policy automatically applies the Default Domain Policy and Default Domain Controllers Policy when AD is installed, as shown here:
For this build, no changes are made to the Default Domain or Default Domain Controllers Policy. Both policies are “enabled” and “link enabled.”
Minor changes are made to the Domain Controller Auditing Policy to enable the ability to audit user account changes, attribute changes, and policy changes for this build.
Note: This example is built in a lab environment. Some security measures were dialed back or turned off for testing purposes.
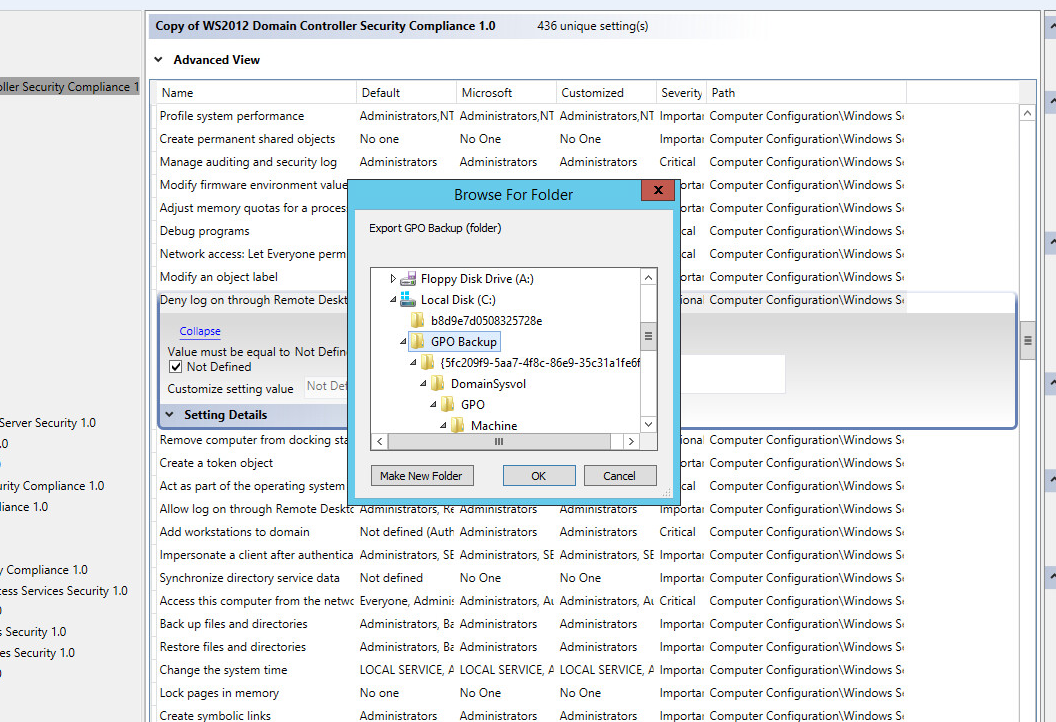
Create a duplicate of the “WS2012 Domain Controller Security Compliance 1.0” baseline. Name it what you would like and save. Domain Controller Auditing is the name for this build.
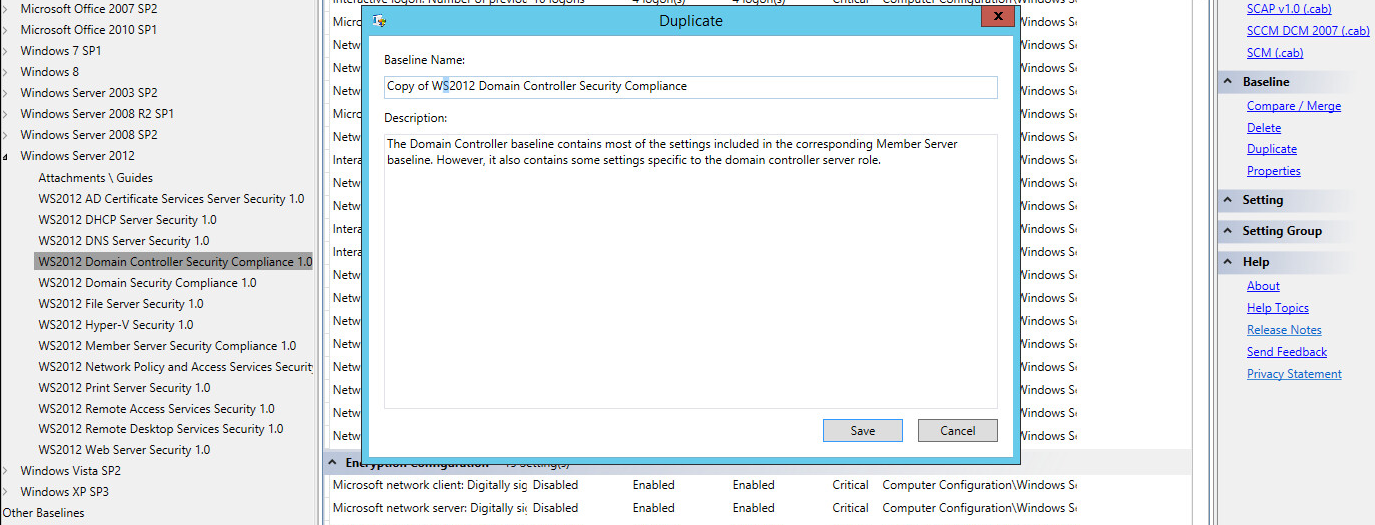
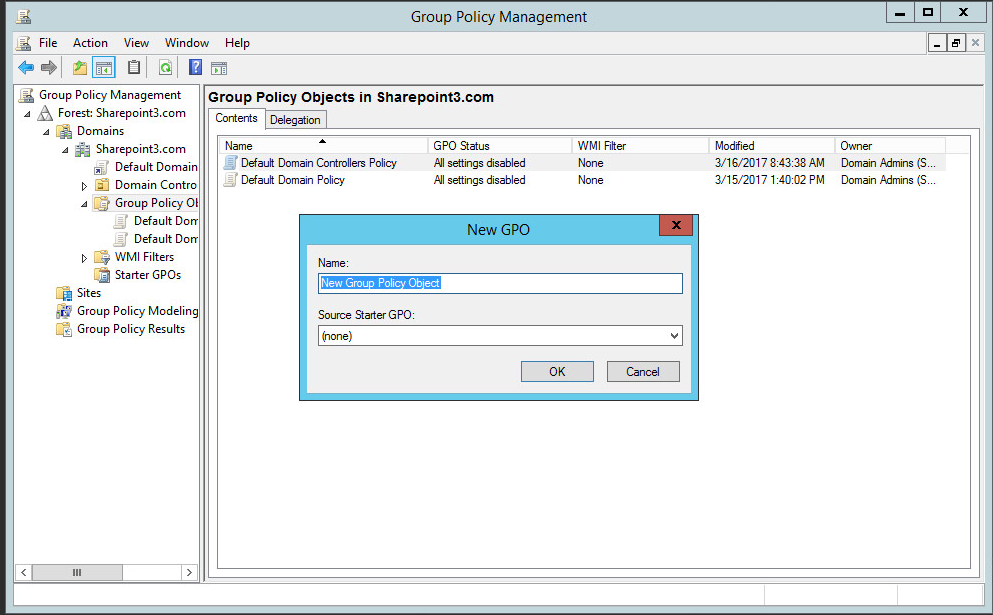
Open group policy management. Under the top level of the domain, right-click on Group Policy Object and select New. Name the GPO and click OK.
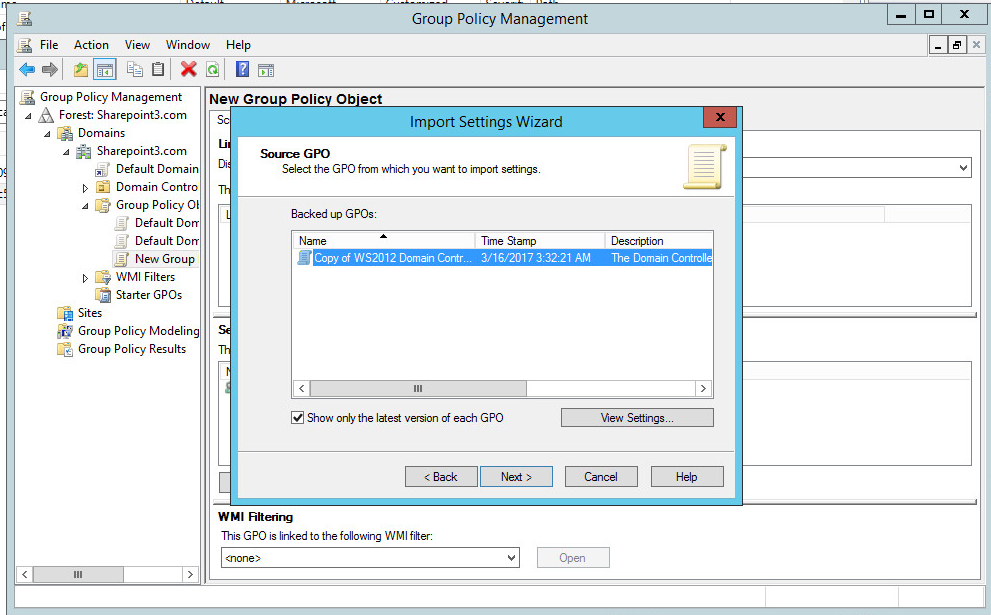
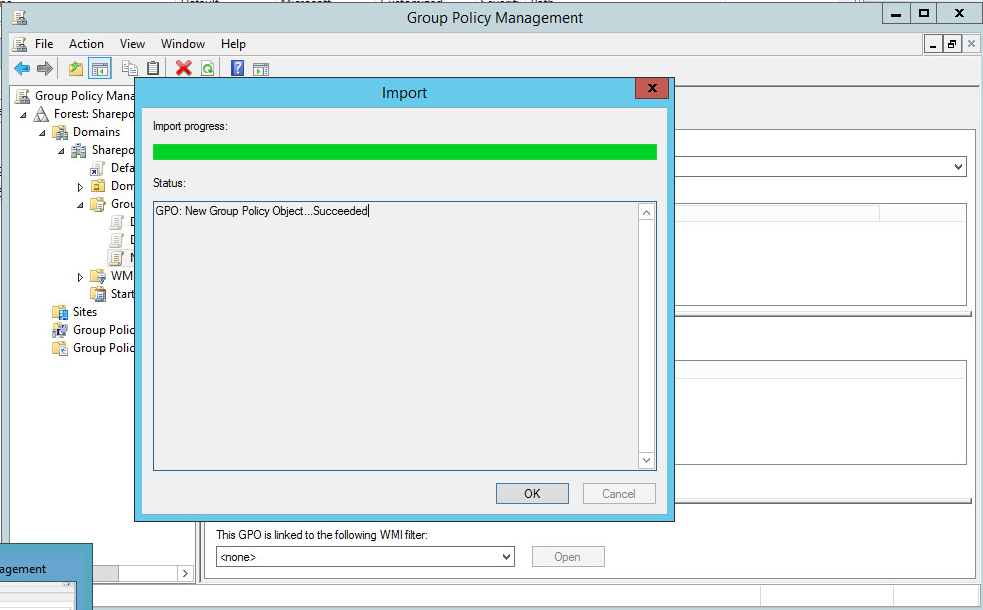
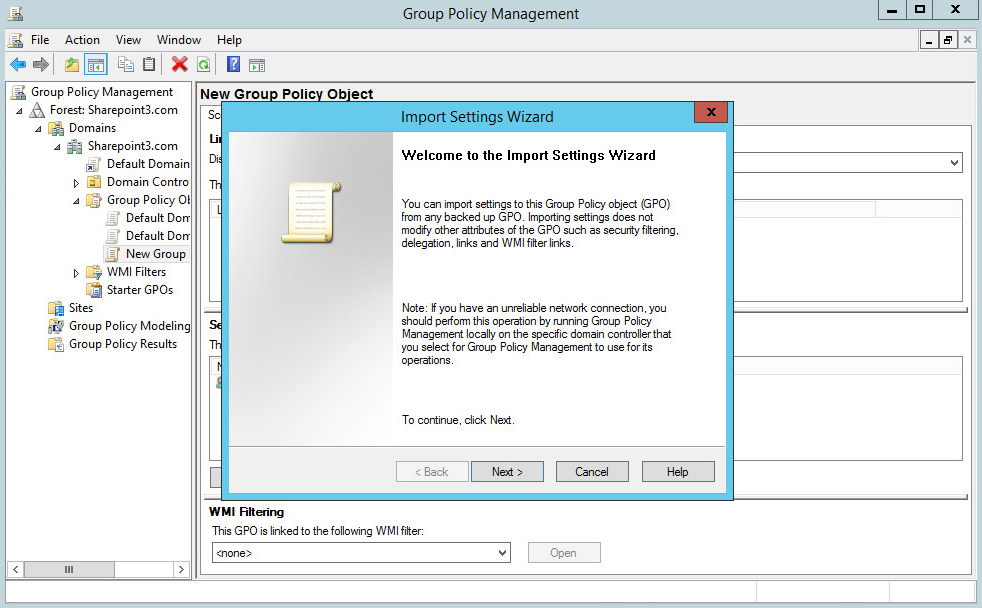
Right-click on the new policy and select Import Settings. Click Next.
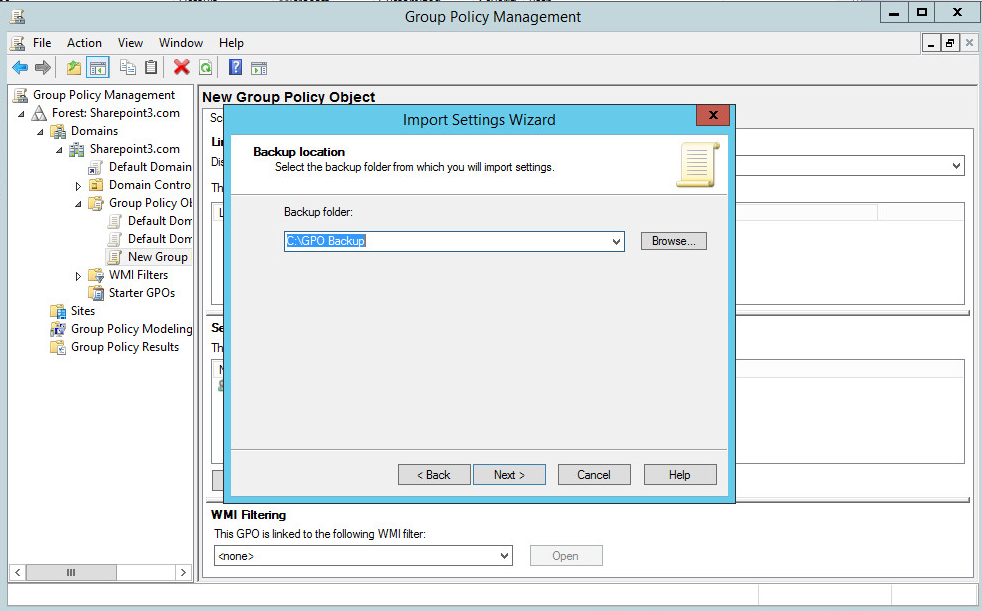
Select the folder location of the backup created in Step 2. Select Next.
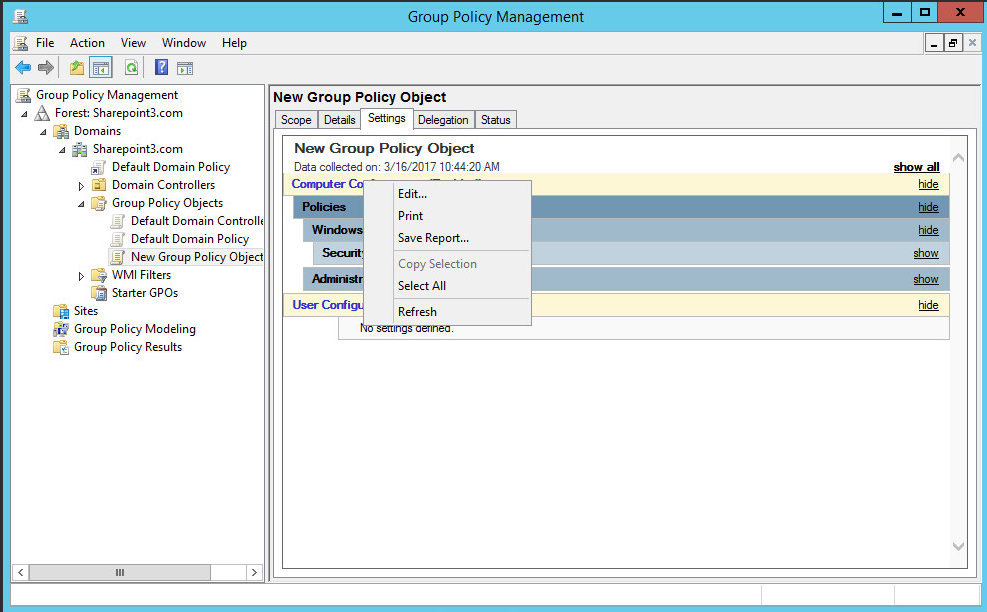
Select the new GPO, select the Settings tab, right-click anywhere, and select Edit.
Navigate to Computer Configuration>Policies>Windows Settings>Security Settings>Local Policies>Security Options. Change the value for “Audit: Force audit policy subcategory settings (Windows Vista or later) to override audit policy category settings” to “Enabled.” Change the value for “Domain controller: LDAP server signing requirements” to “require signing.”
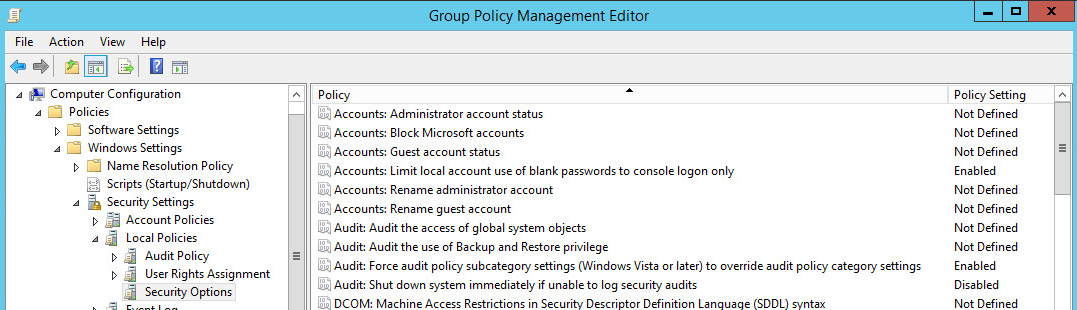
Navigate to Computer Configuration>Policies>Windows Settings>Security Settings>Advanced Audit Policy Configuration>Audit Policies. Make the following changes and save:
Account Logon Audit Credential Validation Success, Failure Account Management Audit Application Group Management Success, Failure Audit Distribution Group Management Success, Failure DS Access Audit Directory Service Access No Auditing Audit Directory Service Changes Success, Failure Object Access Audit Files Share Success Audit File System Success Policy Change Audit Audit Policy Change Success, Failure Audit Authentication Policy Change Success Audit Authorization Policy Change Success Audit MPSSVC Rule-Level Policy Change Success Right-click on the top level of the domain again, select Link an Existing GPO, and choose the created GPO.
Right-click on the new GPO linked directly under the top-level domain and select Enforced by checking it on the left.
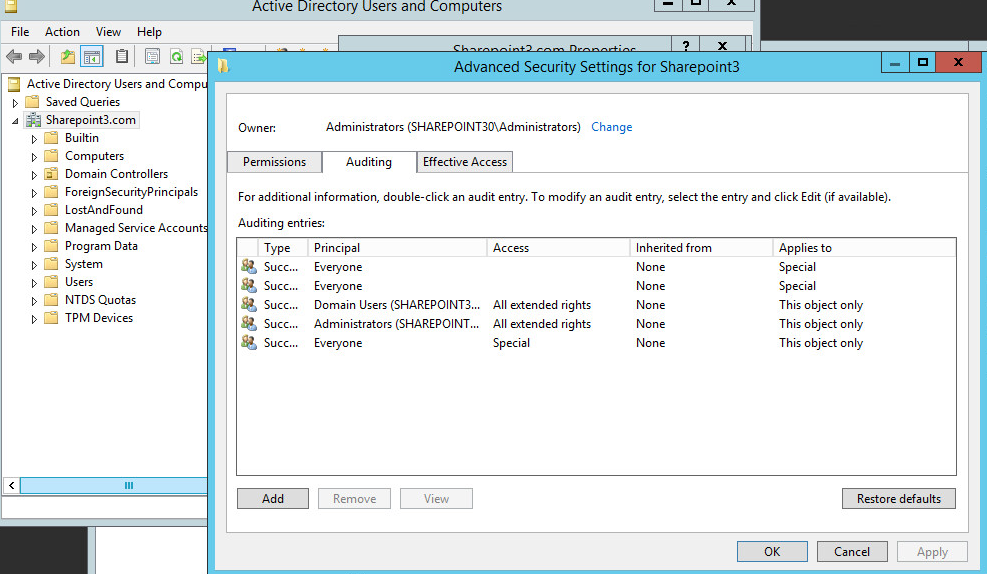
Open Active Directory Users and Computers, right-click on the top level of the domain, select Properties, and navigate to the Security tab.
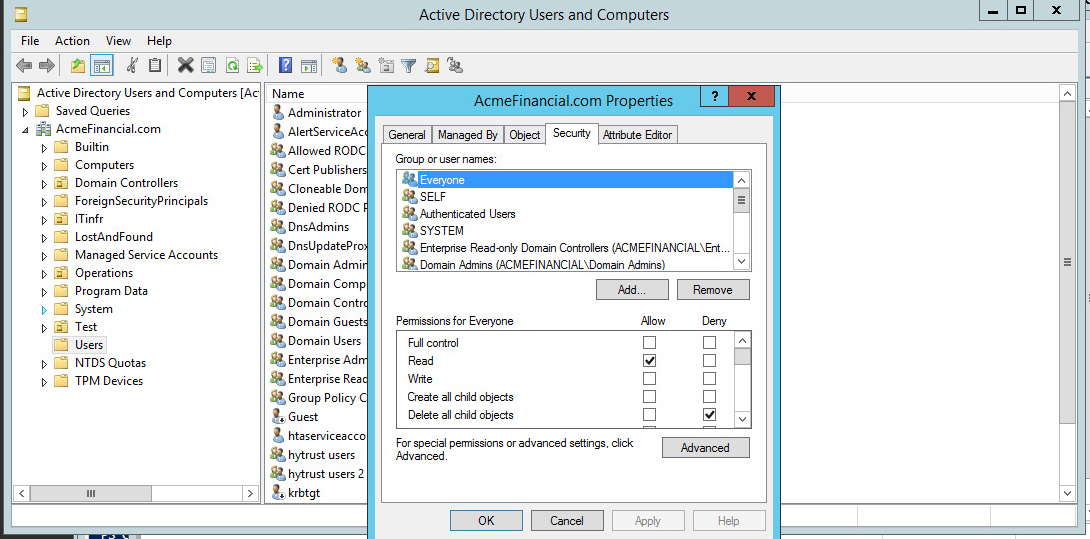
Add a new entry with the following parameters:
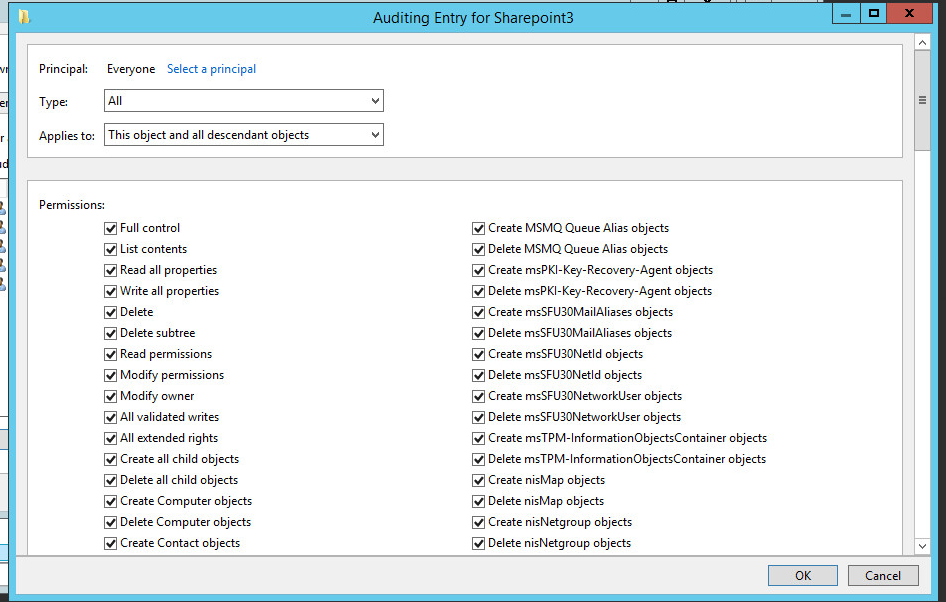 Type: All, Principal: Everyone, Applies to: This
object and all descendant objects. Select every checkbox under
“Permissions” and “Properties” to audit for each action. Click
OK and apply the changes.
Type: All, Principal: Everyone, Applies to: This
object and all descendant objects. Select every checkbox under
“Permissions” and “Properties” to audit for each action. Click
OK and apply the changes.
2.3.8. Script: AdDOnlineStatus.ps1¶
A powershell script is scheduled to run regularly on the active directory server that determines whether it is online or not and writes messages to a local file that Splunk consumes.
#This script determines if this server is online or offline
#If a gateway route exists, the script will
#output the current time, hostname, status and previous time (last
#time it wrote to output file)
#Check if gateway route exists
if (Get-Netroute 0.0.0.0/0)
{
#Store date in PrevTime variable
$PrevTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyyy"
#Check if prevtime-file.txt exists
if (ls C:\scripts\prevtime-file.txt)
{
#Place the contents of prevtime-file.txt in the PrevTime variable
$PrevTime=Get-Content C:\scripts\prevtime-file.txt
}
#Place the current date in CurrentTime
$CurrentTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy"
#Overwrite the contents of prevtime-file.txt with the current date
Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy" > C:\scripts\prevtime-file.txt
$HostVar = hostname
$Status = 'online'
#Add the contents of the variables CurrentTime, HostVar, Status, PrevTime to Radiant-Status-Output.csv
Add-Content C:\scripts\AD-Status-Output.csv $CurrentTime','$HostVar','$Status','$PrevTime
}
else
{
$PrevTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyyy"
if (ls C:\scripts\prevtime-file.txt)
{
$PrevTime=Get-Content C:\scripts\prevtime-file.txt
}
$CurrentTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy"
Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy" > C:\scripts\prevtime-file.txt
$HostVar = hostname
$Status = 'offline'
Add-Content C:\scripts\AD-Status-Output.csv $CurrentTime','$HostVar','$Status','$PrevTime
}
2.3.9. LDAPS Configuration¶
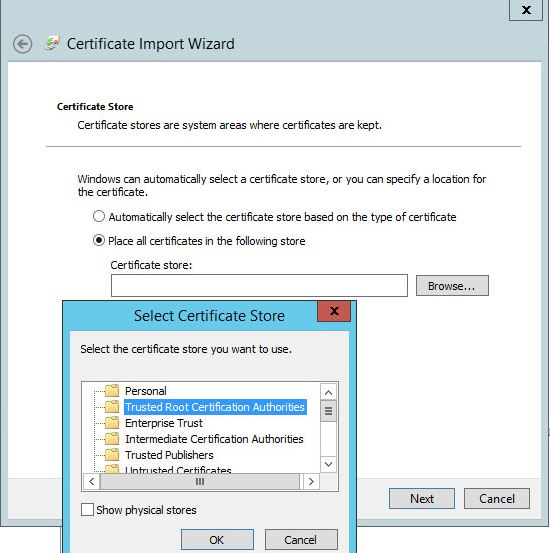
Once installed, the Active Directory service listens for both LDAP and LDAPS connections. To make LDAPS active, you will need to make sure that the certificates for the Active Directory domain controller and the certificate authority (CA) that signed the certificate are properly installed. Once these certificates are imported, LDAP clients will be able to use the LDAPS service.
Copy the CA and domain controller certificates over to the Active Directory domain controller.
Right-click on each certificate and choose Install Certificate.
Choose Local Machine.
Click Next
Choose the placement of the certificate:
- Choose to place the certificate in the Personal Store if it is the domain controller’s certificate.
- Choose to place the certificate in the Trusted Store if it is the CA certificate.
Click OK and then click Next.
LDAPS requests can be processed at this point.
2.4. NextLabs Entitlement Manager¶
NextLabs Entitlement Manager is a dynamic authorization system based on Attribute Based Access Control.
2.4.1. How It’s Used¶
NextLabs Entitlement Manager is used to authorize access to the web application, which is SharePoint in this build. Entitlement Manager requires three components for functionality: NextLabs Control Center, Policy Studio, and Entitlement Management for Microsoft SharePoint Server.
NextLabs Control Center is installed on its own server along with Policy Studio. Entitlement Management is installed on an instance of Microsoft SharePoint Server.
2.4.2. Virtual Machine Configuration¶
The NextLabs virtual machine is configured with:
- Windows Server 2012 R2
- 8 CPU cores
- 16GB of RAM
- 1 NIC
- 100GB of Storage
Network Configuration (Interface 1)
2.4.3. Prerequisites¶
NextLabs Control Center requires an Oracle or MS SQL Server. It is recommended that the database be given 500GB of free storage space. In this build, only 100GB of storage is used for development purposes.
Additionally, multiple deployment configurations are supported. The development deployment configuration is used in this build. For this deployment, the Control Center server is deployed on the same instance as the SQL Server. For a full list of supported software and deployment configurations, see the NextLabs Control Center Installation Guide found at the customer portal.
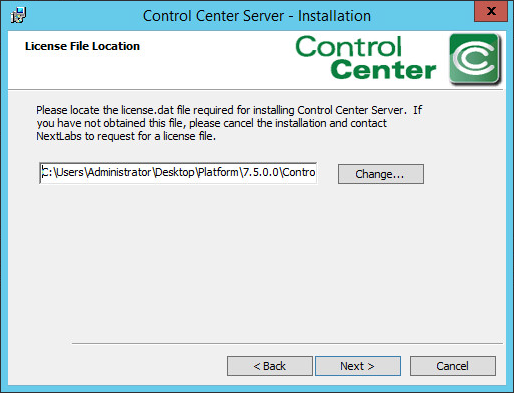
2.4.4. Installing NextLabs¶
Control Center 7.7
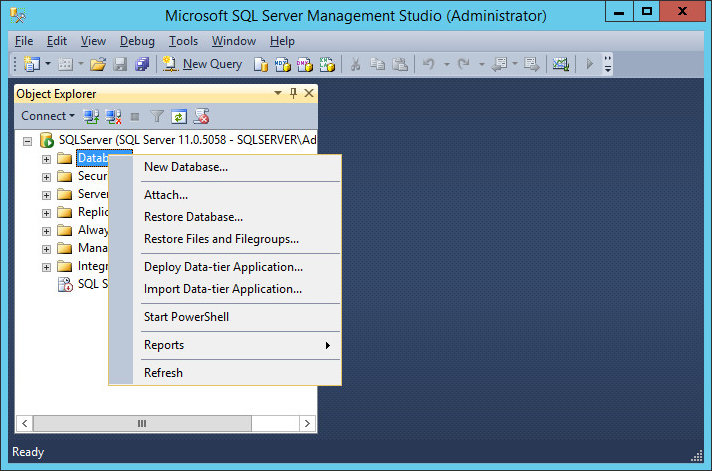
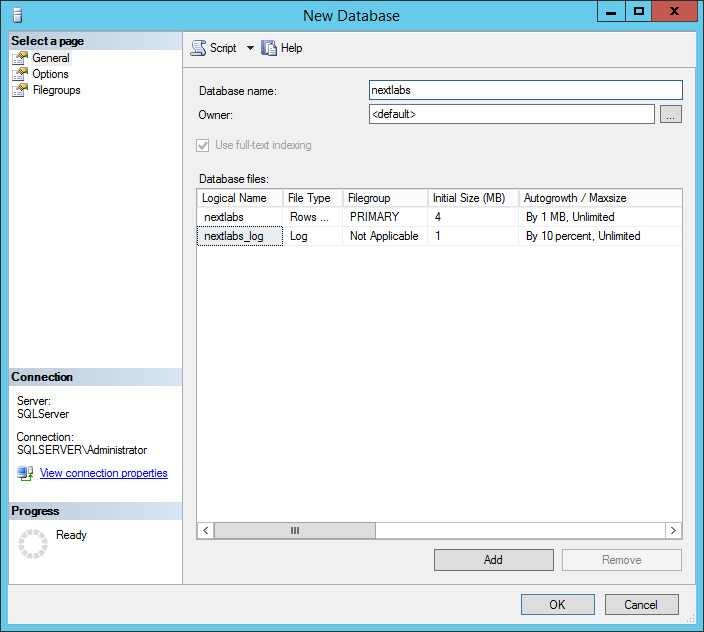
Install the Microsoft SQL Server 2012 according to instructions available online.
Open Microsoft SQL Server Management Studio and log in to the Microsoft SQL Server.
In the New Database window, specify a Database name that works for you. The application automatically copies this into the Logical Names of the Database files. Click OK. Example name from this build: nextlabs.
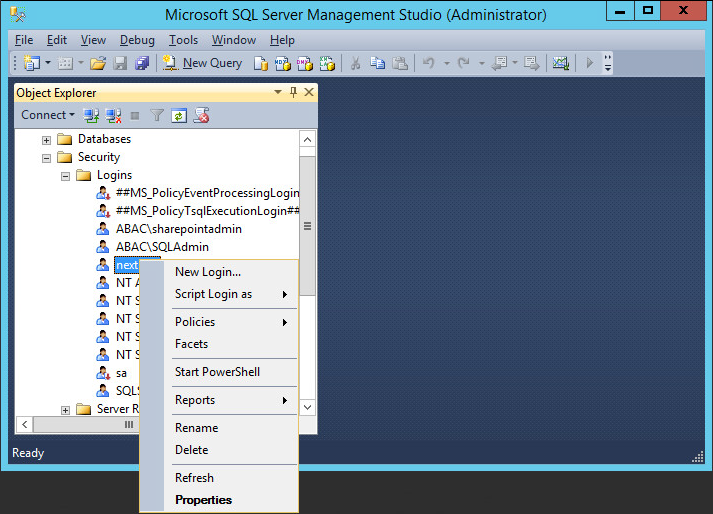
Click on the menu box next to Security to begin the process for creating a new login for the new NextLabs database’s administrator.
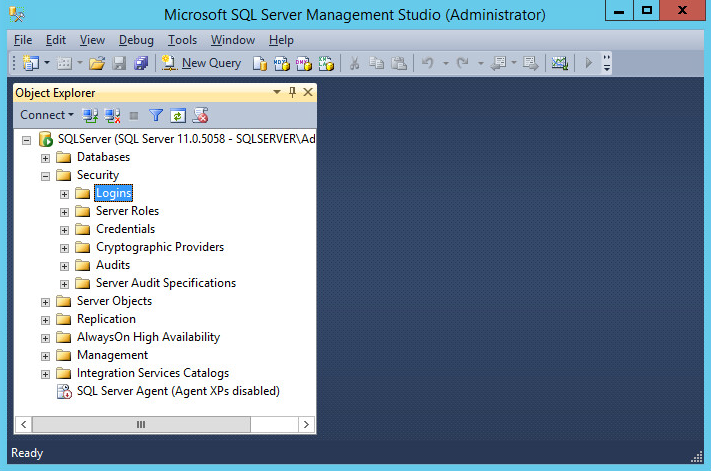
Right-click Logins. Left-click New Login.
Click on SQL Server authentication, and enter a new Login name and Password.
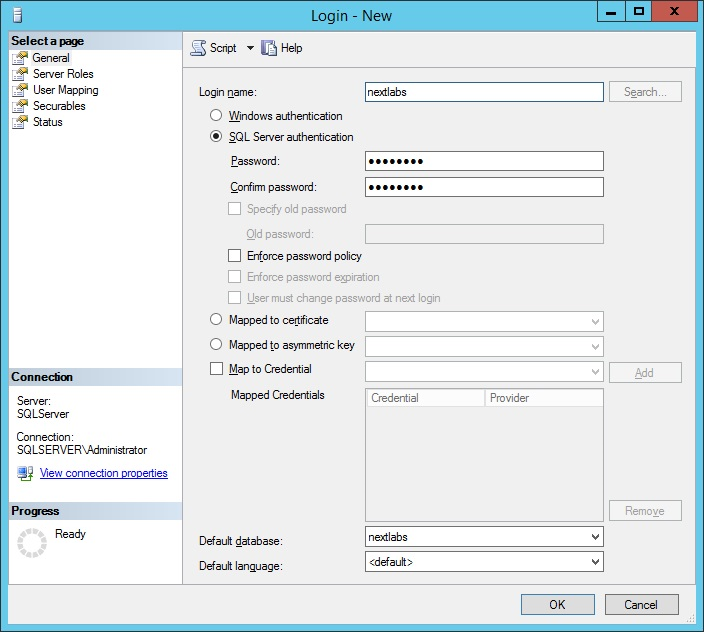
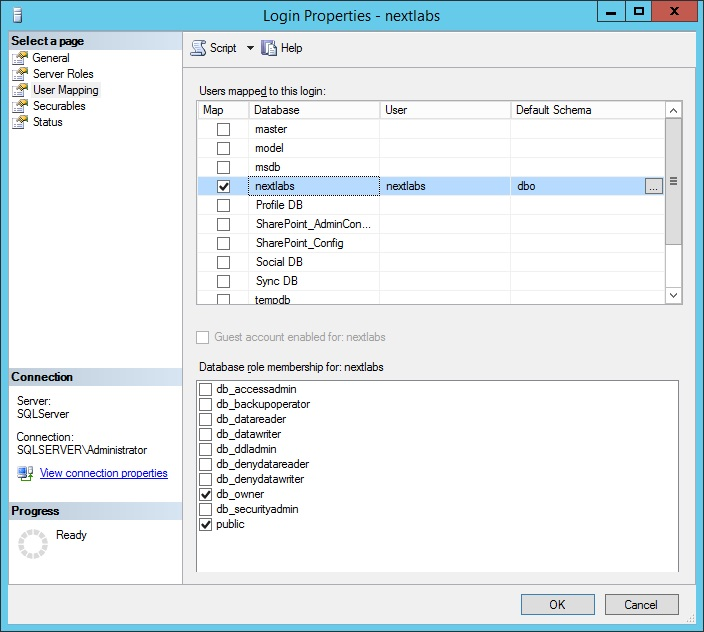
Click the menu box next to Logins. Right-click on the new user created in the previous step. Click Properties.
Click on User Mapping, then New Database. Under Database role membership for: [database_name], check the box next to db_owner.
Locate the installation zip file, provided by NextLabs support, and extract it.
Run the installer as follows:
- On a Windows server, launch Command Prompt as Administrator.
- In the command prompt, navigate to the folder that contains
install.bat. The following is an example of the cd command to type if the installation zip file is extracted inc:\build.cd build\ControlCenter-Windows-chef-- main\PolicyServer
From this directory, run the command:
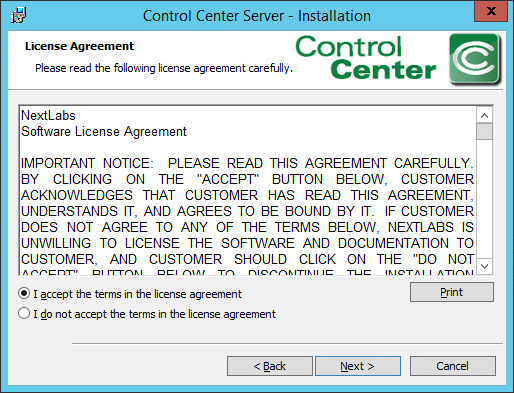
install.batClick Next.
Accept the license agreement, and click Next.
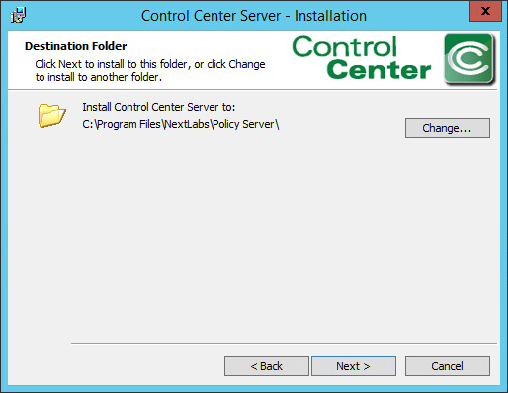
Click Next.
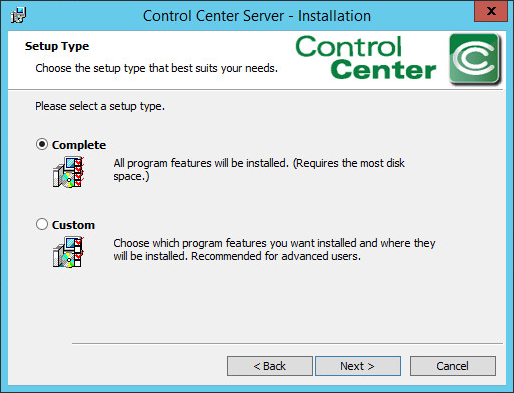
Select the Complete setup type. Click Next.
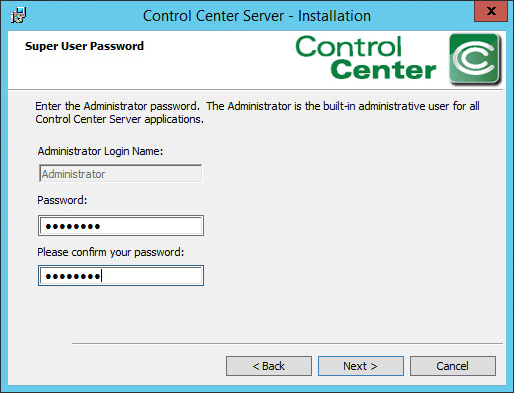
Enter a Password for the built-in administrative user for all Control Center Server applications. Click Next.
Enter a Password to access the SSL certificates for the Control Center Server. Click Next.
Enter a Password to access the Encryption Key Store for the Control Center Server. Click Next.
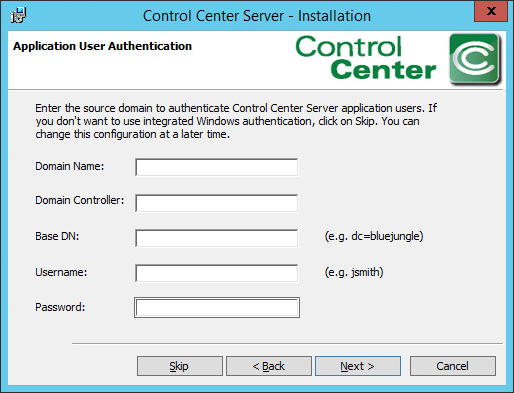
At the Application User Authentication screen, click Skip.
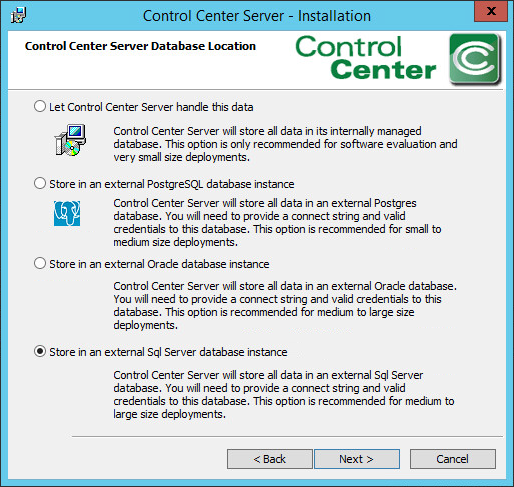
Select Store in an external Sql Server database instance. Click Next.
At the SQL Server settings screen, specify the Connect String, Username, and Password. Make sure the SQL Server is running. It may help to restart the SQL Server.
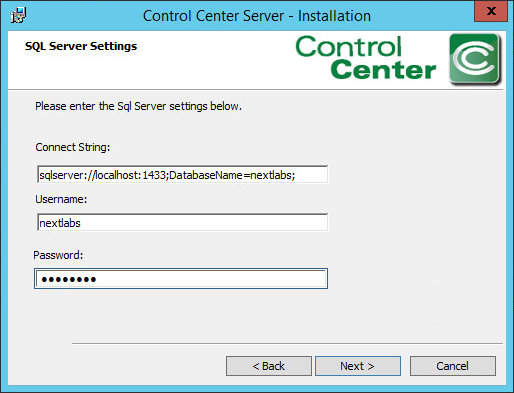
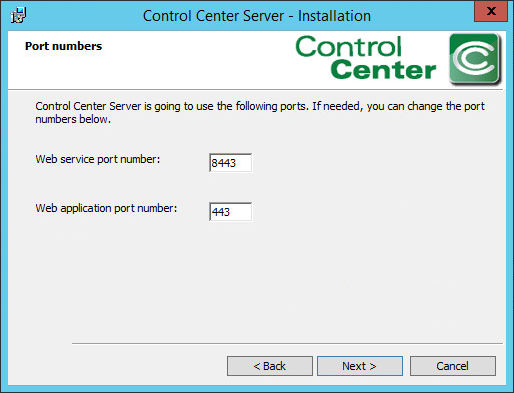
Use the default port numbers. Click Next.
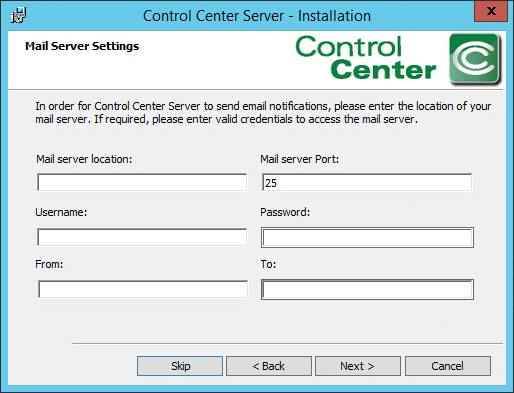
Click Skip.
Click Install.
Once completed, click Finish.
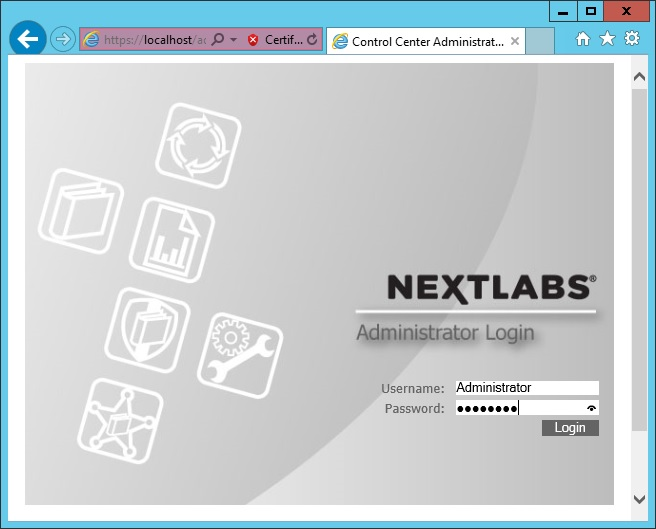
Open an Internet browser, navigate to https://localhost/administrator, and log in to the Control Center Administrator web application.
Once logged in to the Control Center Administrator web application in your browser, you can verify that the NextLabs Control Center is installed and configured correctly on the SQL Server.
Policy Studio 7.7
Complete the standard Policy Studio installation per NextLabs documentation available to customers using the following steps:
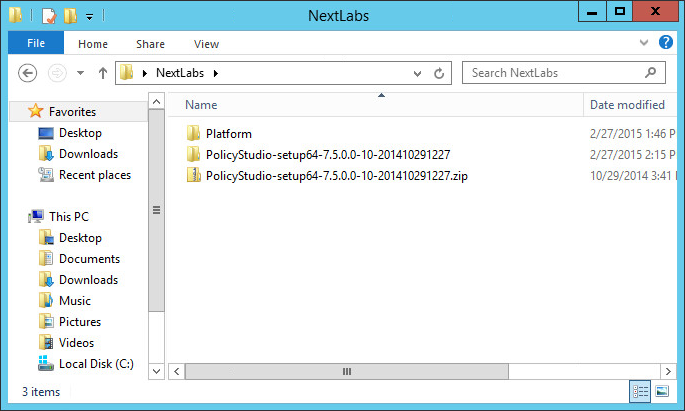
On the same server, go to your desktop or other known location where the required NextLabs Policy Studio installation files are stored.
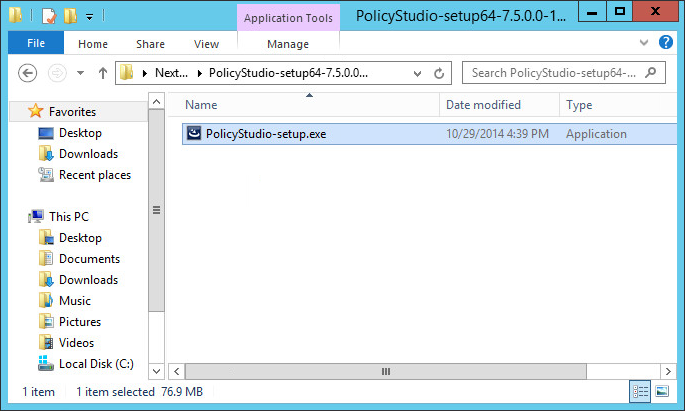
Right-click on PolicyStudio-setup64-7.5.0.0-10-201410291227.zip and select Extract All. Wait for files to be extracted.
Double-click to open the PolicyStudio-setup64-7.5.0.0-10-201410291227 folder.
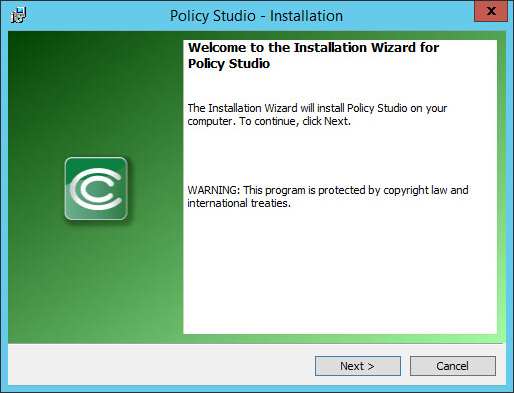
Right-click on PolicyStudio-setup.exe and select Run as Administrator.
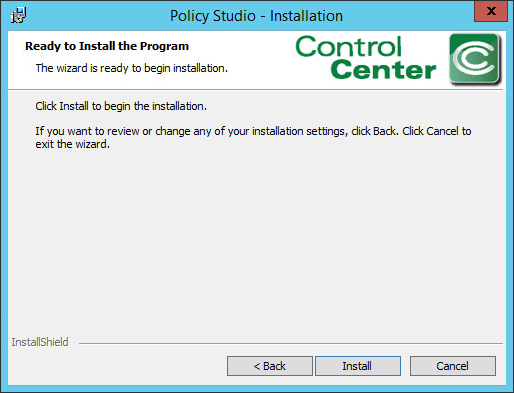
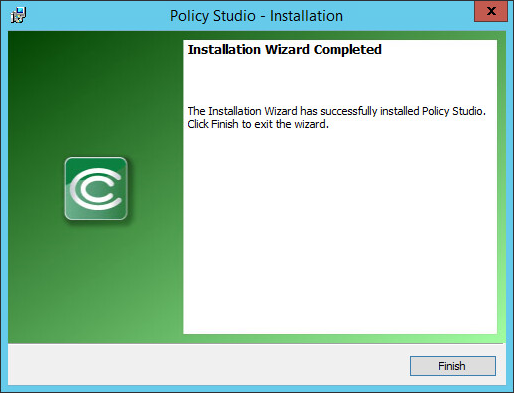
At the Welcome to the Installation Wizard for Policy Studio screen of the Policy Studio Installation Window, click Next.
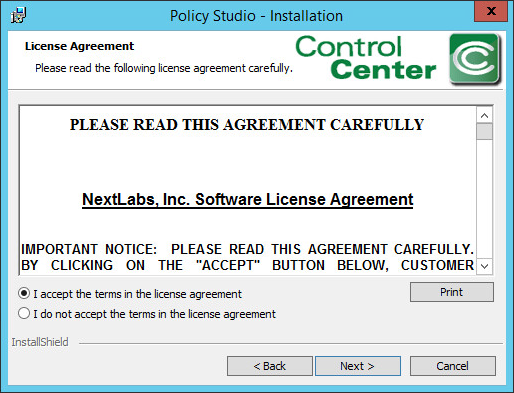
At the License Agreement screen, select I accept the terms in the license agreement, and click Next.
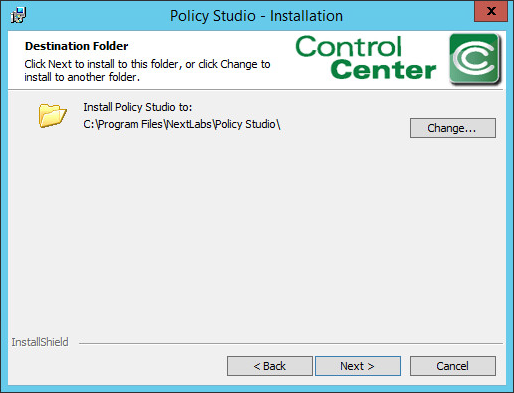
At the Destination Folder screen, click Next.
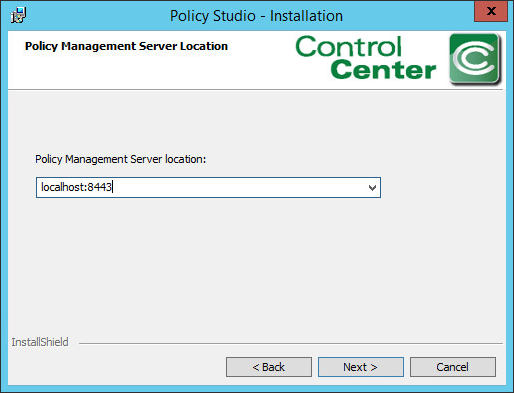
At the Policy Management Server Location screen, enter the default location localhost:8443.
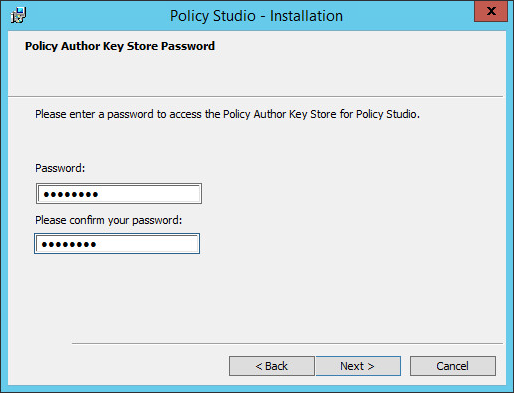
At the Policy Author Key Store Password screen, enter a Password and click Next.
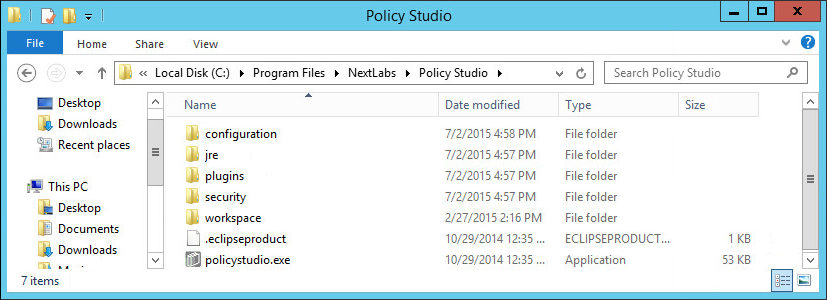
In Windows Explorer, find and open the policystudio.exe application file.
- Navigate to the C:/ drive>Program Files>NextLabs>Policy Studio.
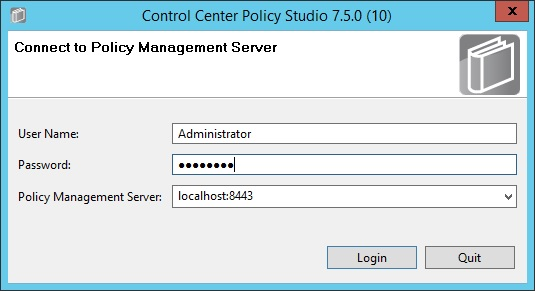
- Click policystudio.exe.
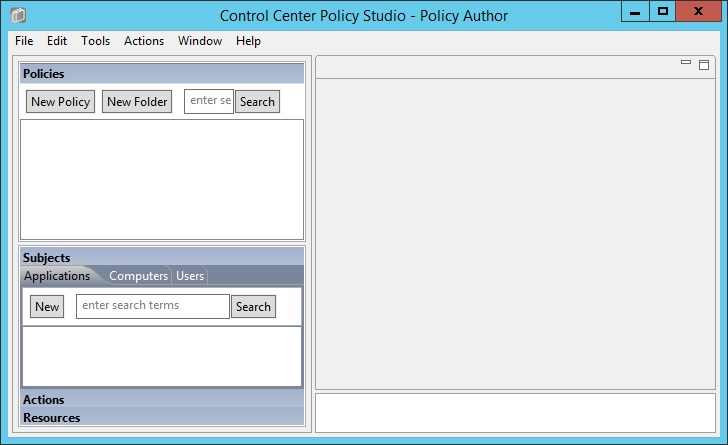
In the Control Center Policy Studio window, enter a User Name and Password to connect to the Policy Management Server.
If the connection is successful, the Control Center Policy Studio - Policy Author window will open. Policies are defined and deployed in this interface.
Policy Controller 7.7
The Policy Controller is installed on the SharePoint Server. To complete standard Policy Controller installation per NextLabs documentation available to customers, use the following steps:
On the SharePoint Server, go to your desktop or other known location where the required NextLabs Policy Controller installation files are stored.
Extract the files from the PolicyController-CE-64-<version>.zip file.
Open the PolicyController-CE-64-<version> folder.
Click CE-PolicyController-setup64.msi to begin installation.
At the Welcome to the InstallShield Wizard for NextLabs Policy Controller Installation screen, click Next.
At the License Agreement screen, select I accept the terms in the license agreement and click Next.
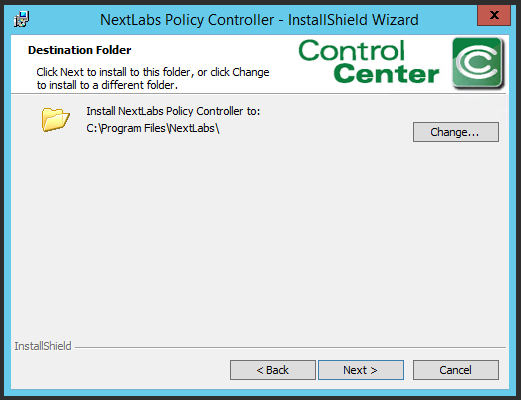
At the Destination Folder screen, click Next.
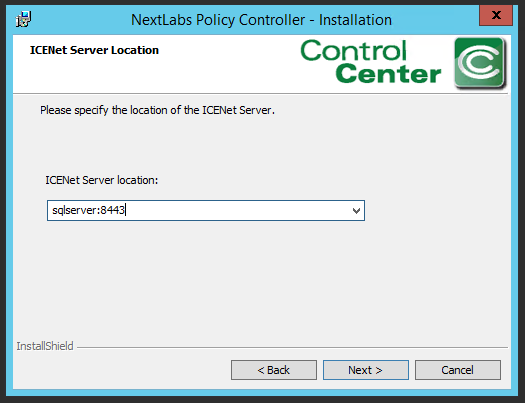
At the ICENet Server Location screen, enter the default ICENet Server Location: sqlserver:8443. Click Next.
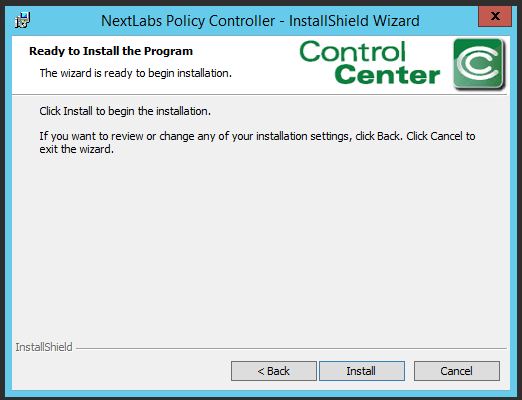
At the Ready to Install the Program screen, click Install.
At the InstallShield Wizard Completed screen, click Finish.
In the window that immediately opens, click Yes to restart the computer, or click No to wait and restart after installing Entitlement Manager.
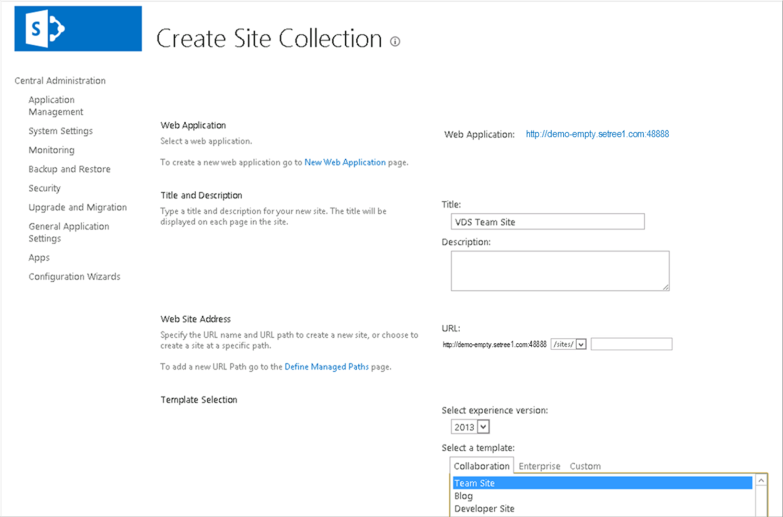
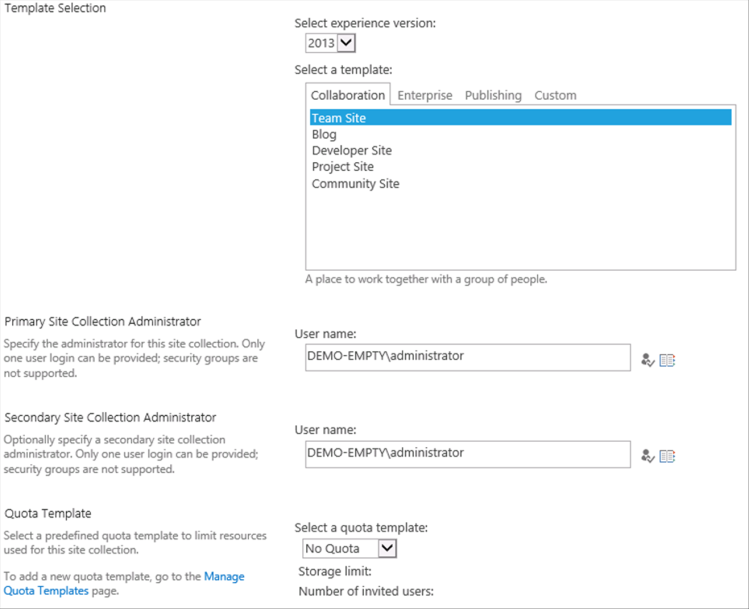
Entitlement Manager for Microsoft SharePoint 7.6
Entitlement Manager is installed once SharePoint and the Policy Controller have been installed. The web application site and site collection must already exist in SharePoint. See Section 2.7 for installing SharePoint and creating site collections. Complete the standard Entitlement Manager for SharePoint Server installation per NextLabs documentation available to customers using the following steps.
On the SharePoint Server, go to your desktop or other known location where the required NextLabs Policy Controller installation files are stored.
Extract the files from the SharePointEnforcer-2013-64-<version>.zip folder.
Open the SharePointEnforcer-2013-64-<version> folder.
Click on the SharePointEnforcer-2013-64-<version>.msi to begin the installation.
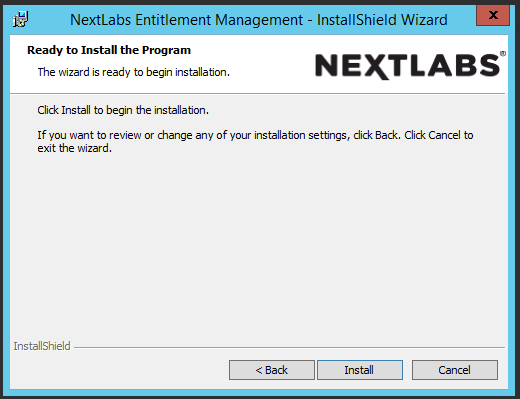
At the Welcome to the InstallShield Wizard for NextLabs Entitlement Manager for MicroSoft SharePoint screen, click Next.
At the License Agreement screen, select I accept the terms in the license agreement and click Next.
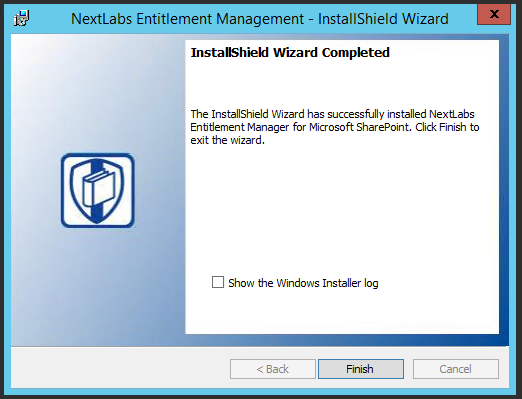
After installing, the IIS server must be reset:
- Click the Windows icon and begin typing the word PowerShell and open the windows PowerShell application.
- From within the Windows PowerShell window, type in this command and press Enter to reset Internet Information Services: iisreset.
On the SharePoint Server, click the Start icon to see the applications pinned to the Start menu.
Click the NextLabs Entitlement Manager for SharePoint Server Deployment icon.
This shortcut is automatically pinned during the initial installation. In case the shortcut is not created automatically, the application can be opened from File Explorer at the location: C:\Program Files\NextLabs\SharePoint Enforcer\bin\NextLabs.Entitlement.Wizard.exe
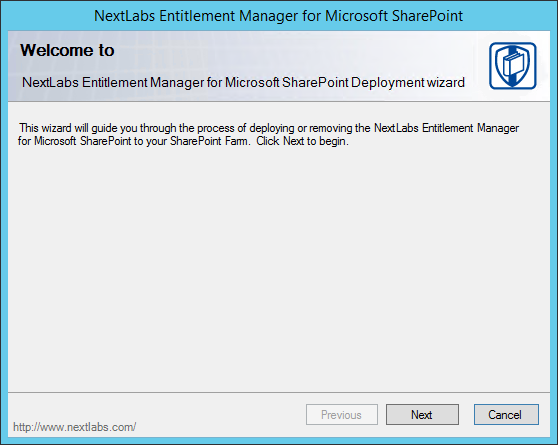
At the Welcome to NextLabs Entitlement Manager for Microsoft SharePoint Deployment wizard screen, click Next.
At the System Check screen, after the system check is complete, click Next.
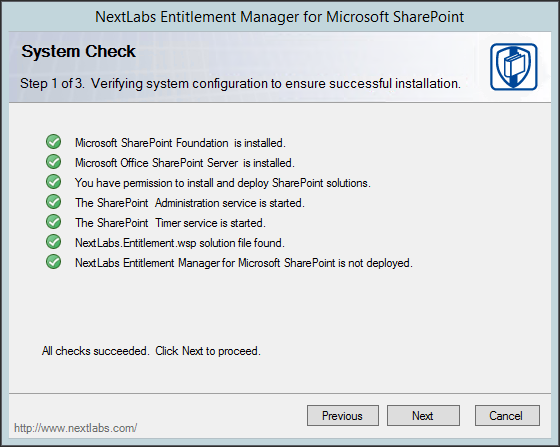
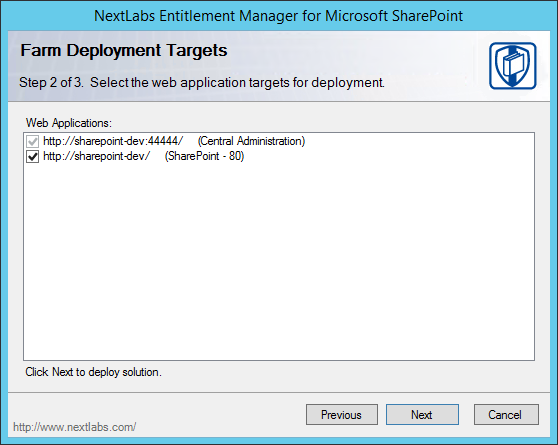
At the Farm Deployment Targets screen, select the applicable web application on which to deploy.
Note: If only one entry is listed, i.e., http://sharepoint:44444/Central Administration, no web applications have been created.
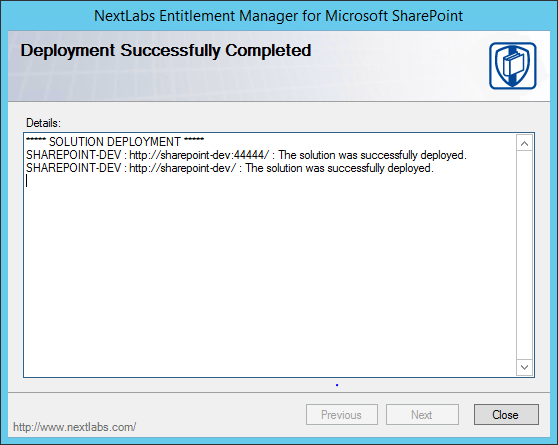
At the Deploying Step 3 of 3 screen, click Next.
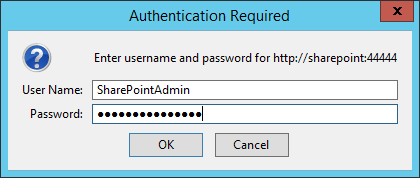
Open a browser and navigate to the SharePoint Central Administration Portal. Log in with the SharePoint Administrator account.
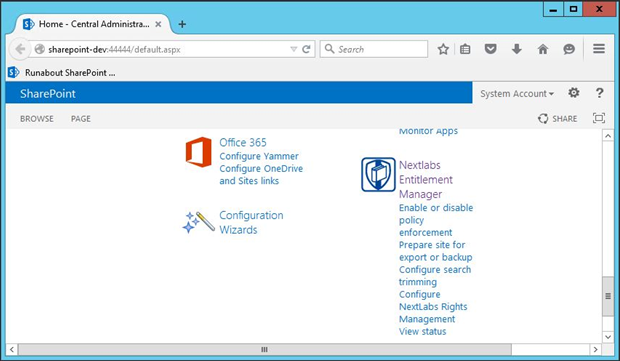
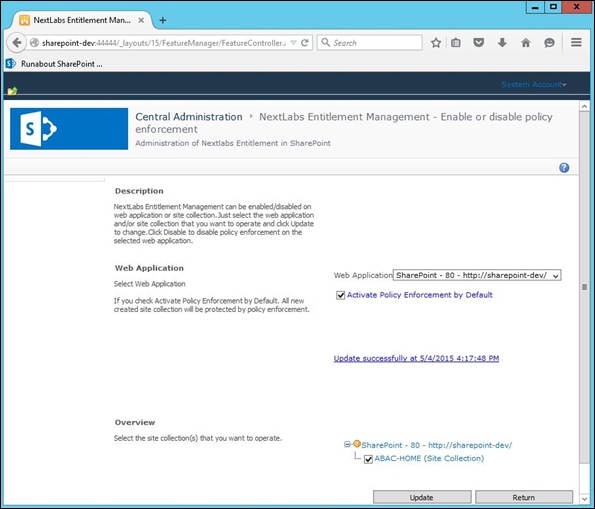
Click on the NextLabs Entitlement Manager icon.
In the page that opens, scroll down to verify that the correct Web Application is chosen and the service is Enabled.
2.5. OpenLDAP¶
OpenLDAP is an open source implementation of the Lightweight Directory Access Protocol. It stores user identity information along with various other attributes that are indicative of access rights, and it is able to provide the necessary information that requesting services need to make authorization decisions.
2.5.1. How It’s Used¶
OpenLDAP stores user information and associated attributes for users who need access to Unix/Linux based applications. Examples of such attributes are a user’s userid, group, organizational unit, job title and various other custom attributes. The OpenLDAP service listens and responds to requests from the virtual directory service that acts as the enterprise policy information point and has the responsibility for retrieving, organizing, and aggregating each user’s attribute set under a single view.
2.5.2. Virtual Machine Configuration¶
The OpenLDAP virtual machine is configured aas follows:
- Ubuntu Linux 16.04 LTS
- 1 CPU core
- 2GB of RAM
- 2 NICs
- 60GB of storage
- OpenLDAP server software
Network Configuration (Interface 1)
Network Configuration (Interface 2)
2.5.3. Firewall Configuration¶
Enter the following commands in sequence to allow traffic to LDAPS and SSH ports only.
ufw allow 636/tcp to allow
ufw allow 22/tcp to allow
ufw default deny incoming
2.5.4. Installation¶
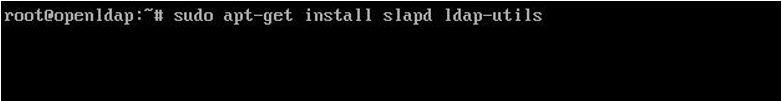
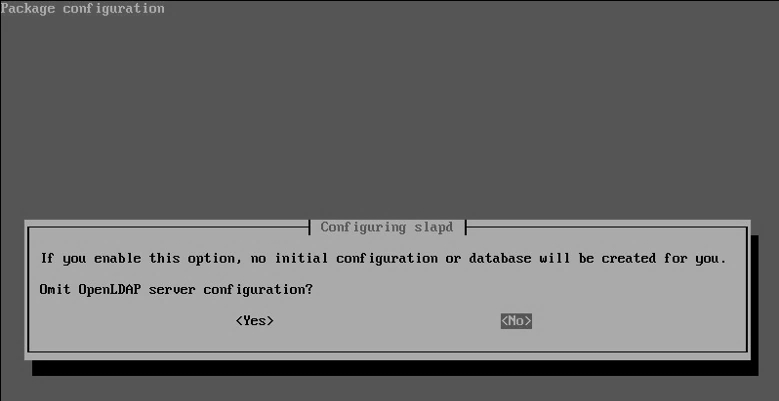
- Select No and press Enter.
- Enter the organizational Name on the following screen (for example, acmefinancial.com).
- Enter the administrator password for the BaseDN (BaseDN: acmefinancial.com).
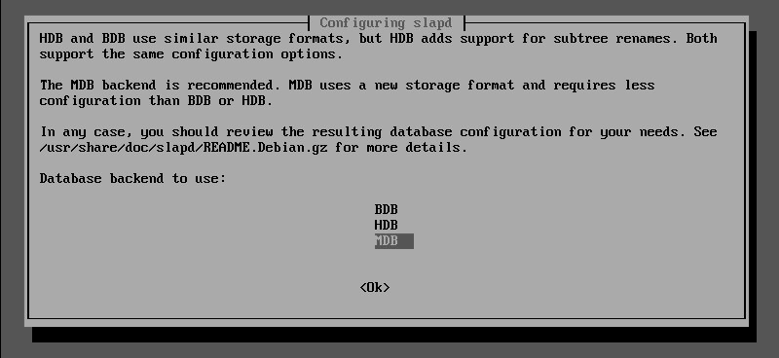
- Select MDB as the Backend database for OpenLDAP and press Enter.
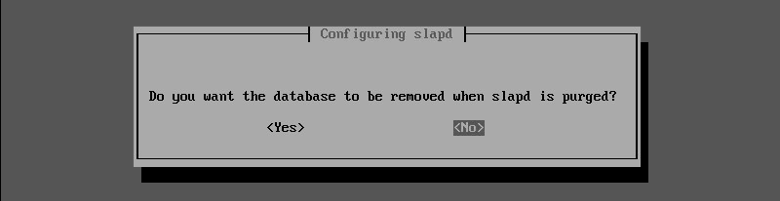
- Select No and press Enter.
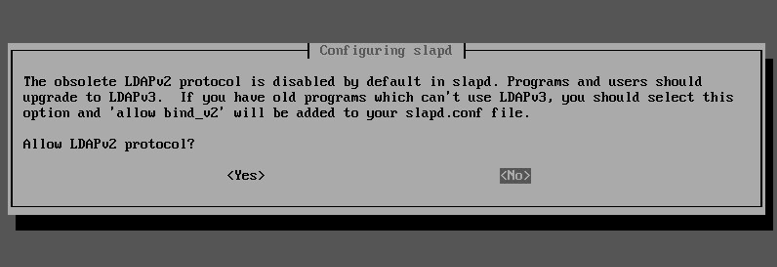
- Select No to disable LDAPv2.
2.5.5. Audit Configuration¶
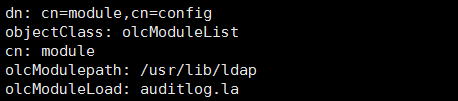
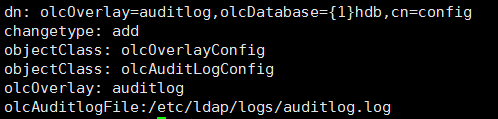
Enter
mkdir /etc/ldap/logsat a shell prompt to create a directory that is writable by the OpenLDAP service.Enter
chown openldap.openldap /etc/ldap/logsto make the logs subdirectory owned by the openldap service.Enter
touch create-cn-module.ldifto create a file that will be used to load a cn module. This will allow the AuditLogConfig object class to be added. The file contents should be as follows:Enter
ldapadd -Q -Y -EXTERNAL -H ldapi:/// -f create-cn-module.ldifto add the cn module.Enter
touch logging.ldif.The file contents should be as follows:Enter
chmod 775 /etc/ldap/logs.Enter
chmod 664 /etc/ldap/logs/auditlog.log.Enter
ldapadd -Q -Y -EXTERNAL -H ldapi:/// -f logging.ldif.Changes to user records should now appear in /etc/ldap/logs/auditlog.log.
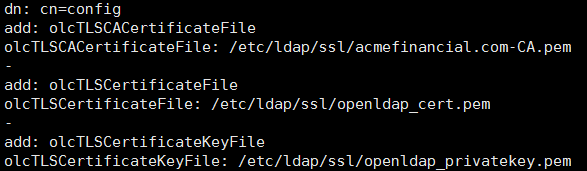
2.5.6. STARTTLS and LDAPS Configuration¶
On the OpenLDAP server, create an ssl directory /etc/ldap/ssl. Enter mkdir /etc/ldap/ssl.
Move the certificates created for the OpenLDAP server from the Certificate of Authority to the ssl subdirectory:
scp openldap_cert.pem user1@openldap.acmefinancial.com:\ldap\sslscp openldap_privatekey.pem user1@openldap.acmefinancial.com:\ldap\sslscp acmefinancial.com-CA.pem user1@openldap.acmefinancial.com:\ldap\ssl
Install the CA certificate so that local applications can use the certificate when necessary:
cp acmefinancial.com-CA.pem /usr/share/ca-certificates/acmefinancial.com-CA.crt- Add acmefinancial.com-CA.crt to the end of the /etc/ca-certificates.conf file.
- Enter
sudo update-ca-certificates.
Create a certificate information file called certinfo.ldif in /etc/ldap/ssl with the following contents:
Set permissions and ownership on the certificate files so that the openLDAP user can read the key file:
sudo adduser openldap ssl-certchgrp ssl-cert /etc/ldap/ssl/openldap_privatekey.pemchmod g+r /etc/ldap/ssl/openldap_privatekey.pemchmod o-r /etc/ssl/ldap/openldap_privatekey.pemchown root.ssl-cert /etc/ldap/ssl/openldap_privatekey.pemchown root.ssl-cert /etc/ldap/ssl/openldap_cert.pemchmod root.ssl-cert /etc/ldap/ssl
Reconfigure slapd by running the following command
ldapmodify -Y EXTERNAL -H ldapi:/// -f /etc/ldap/ssl/certinfo.ldif- Restart slapd by running
service slapd restart
StartTLS should now be enabled.
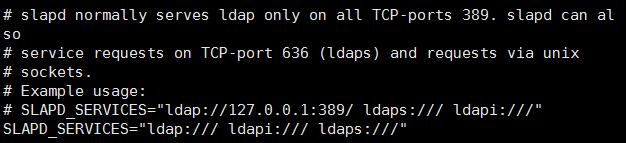
Enable LDAPS by adding ldaps:/// to the SLAPD_SERVICES line in the /etc/default/slapd file:
- Go to the SLAPD_SERVICES line and add ldaps:/// as shown above.
- Enter
service slapd restartto restart the OpenLDAP service.
Prepare the slapd client to use StartTLS:
- Create the /etc/ldap/ssl directory.
- Copy acmefinancial.com-CA.pem to /etc/ldap/ssl/ directory.
- Go to the client computer and edit /etc/ldap/ldap.conf.
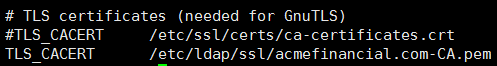
- Comment out the previous TLS_CACERT entry and add a new one pointing to the location of your CA certificate.
2.5.7. Formatting Audit Logs¶
The file /etc/ldap/logs/auditlog.log stores log entries destined for the Splunk indexer. Using the following scripts, the logs were formatted in such a way that enables the Splunk indexer to easily determine the start and end of each log event.
2.5.8. Script: /etc/ldap/logs/auditlogscript¶
#!/bin/bash
# Remove newlines, make file a single string and dump to auditlog.string
tr -s '\n' ' ' < /etc/ldap/logs/auditlog.log > /etc/ldap/logs/auditlog.string
# Change every occurrence of #0 to just 0
sed -i -e 's/#0/0/g' /etc/ldap/logs/auditlog.string
# Remove spaces between attributes and their values
sed -i -e 's/: /:/g' /etc/ldap/logs/auditlog.string
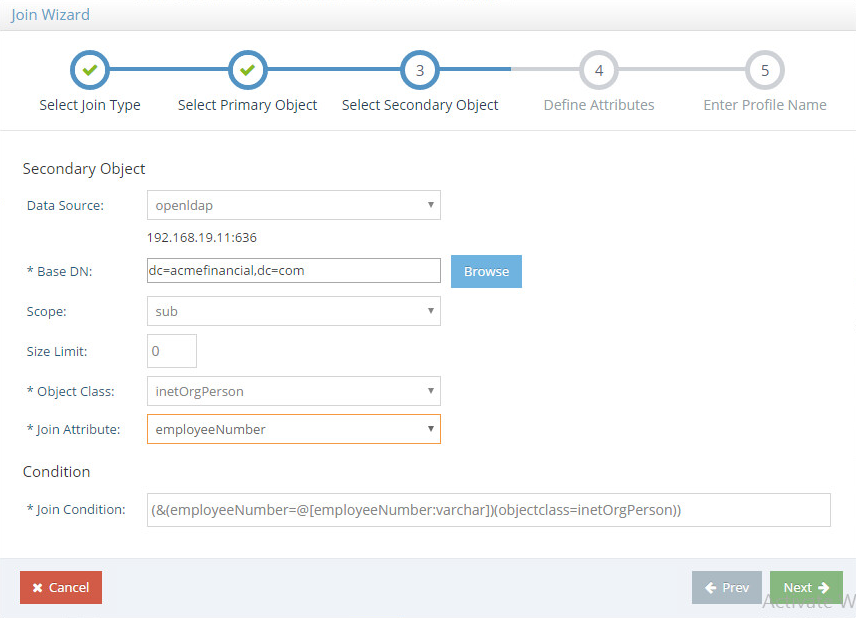
#Additional formatting helpful in showing field separation
sed -i -e 's/ /;;/g' /etc/ldap/logs/auditlog.string
# Change # to newline making each line a unique openldap event and dump
# to auditlog.lines
tr -s '#' '\n' </etc/ldap/logs/auditlog.string> /etc/ldap/logs/auditlog.lines
#Additional formatting in removing unneeded lines
sed -i '/;;end;;/d' /etc/ldap/logs/auditlog.lines
# Empty previous contents of outlog.log
# outlog.log is effectively overwritten when script runs
cp /dev/null /etc/ldap/logs/outlog.log
# Call add-timestamp.py to add readable timestamps and dump to outlog.log
/etc/ldap/logs/add-timestamp.py
2.5.9. Script: /etc/ldap/logs/add-timestamp.py¶
#!/usr/bin/python3
import datetime
start_index = 0
end_index = 0
timestamp = 123456789 #var to store datetime object; values are placeholders
localtime = "12345" #string var to store local time; values are placeholders
filename = "/etc/ldap/logs/auditlog.lines" #Each event in file is a line
#Open the file, parse each each line,identified char set in IF
#statement exposing the epoch_time without leading or trailing chars
with open(filename, 'r') as file_object:
for string in file_object:
if ";;dc" in string:
end_index = string.find(";;dc")
string = string.strip()
newstring = string[start_index:end_index]
newstring = newstring.lstrip(';')
newstring = newstring.lstrip('add')
newstring = newstring.lstrip('modify')
newstring = newstring.lstrip('delete')
newstring = newstring.lstrip('rdn')
newstring = newstring.lstrip(';')
epoch_time = int(newstring) #Store epoch_time as integer
#Convert epoch_time to datetime object and store in timestamp
timestamp = datetime.datetime.fromtimestamp(epoch_time)
#Convert value in timestamp to string and store in localtime
localtime = str(timestamp)
#If line is blank, do nothing, else prepend localtime to line
if string.isspace():
pass
else:
with open('/etc/ldap/logs/outlog.log','a') as outfile_object:
outfile_object.write(localtime + string + '\n')
2.5.10. Script: /etc/cron.daily/openldap-status¶
#!/bin/bash
#This script sends online status updates to splunk with enough information
#such that anlytics on Splunk can determine whether or not this host has
#failed to send updates in a given period.
if ls /var/log/oldstatustime # check if file exists
then
prevtime=$(cat /var/log/oldstatustime) #store date in file in variable prevtime
else
date >/var/log/oldstatustime #else write current date to file path
fi
#write time hostname previous run time and online keyword to file path
#in a single line separated by commas
((date && hostname && echo $prevtime && echo online)|tr -s '\n' ','|sed s'/online,/online/';echo "") >> /var/log/openldap-status-file.csv
date > /var/log/oldstatustime
2.6. Radiant Logic¶
Radiant Logic RadiantOne Virtual Directory Server (VDS) is a virtual directory that performs a federated identity service. (Note: Radiant Logic changed their product name from RadiantOne Virtual Directory Server (VDS) to RadiantOne Federated Identity Service (FID)).
2.6.1. How Its Used¶
The RadiantOne VDS (VD) is used in two capacities in this example implementation. First, the VD acts as a federated identity service, correlating users from each directory into a single view. Second, the VD acts as a monitoring service, where the created view is cached, and changes made to the cache are logged and sent to Splunk.
2.6.2. Virtual Machine Configuration¶
The Radiant Logic virtual machine is configured as follows:
- Ubuntu Linux 16.04 LTS
- 4 CPU cores
- 24GB of RAM
- 2 NICs
- 100GB of storage
Network Configuration (Interface 1)
Network Configuration (Interface 2)
2.6.3. Installing the Virtual Directory¶
To install the VD, see the documentation provided with the software. The VD installation guide can also be found on the Radiant Logic support website here.
2.6.4. Configuring VD¶
Steps for configuring the VD are as follows:
- Add server backends.
- Create proxy backend.
- Configure caching and system connectors.
- Create SharePoint view.
- Log Settings.
To add the server backends in the VD, complete the following steps:
While logged in as the Directory Manager, navigate to Settings>Server Backend>LDAP Data Sources,
Name the data source and enter the parameters. For AD, the parameters used are shown in the following screenshot. Click Save.
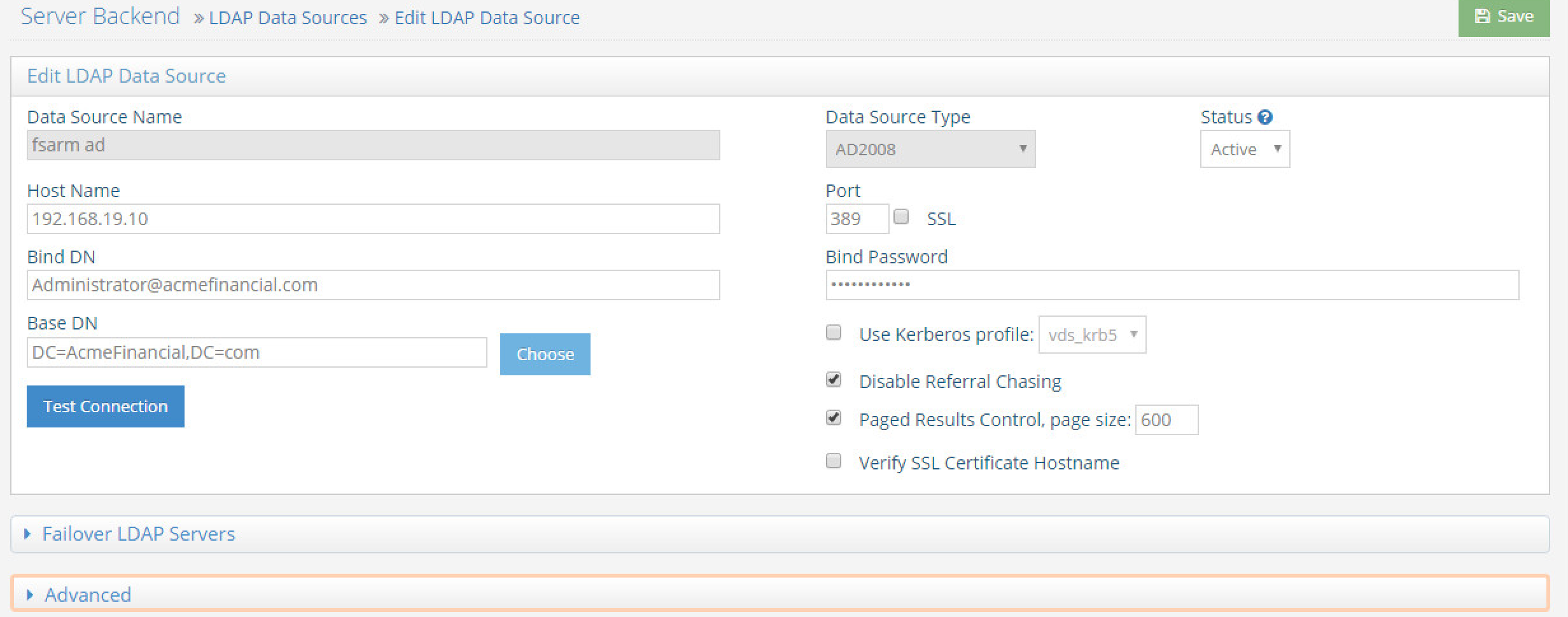
Note: Be sure to select Disable Referral Chasing for AD.
Repeat Steps 2 and 3 for the OpenLDAP and RACF directories. Use LDAP as the data source type. Details for each are shown in the following screenshots:
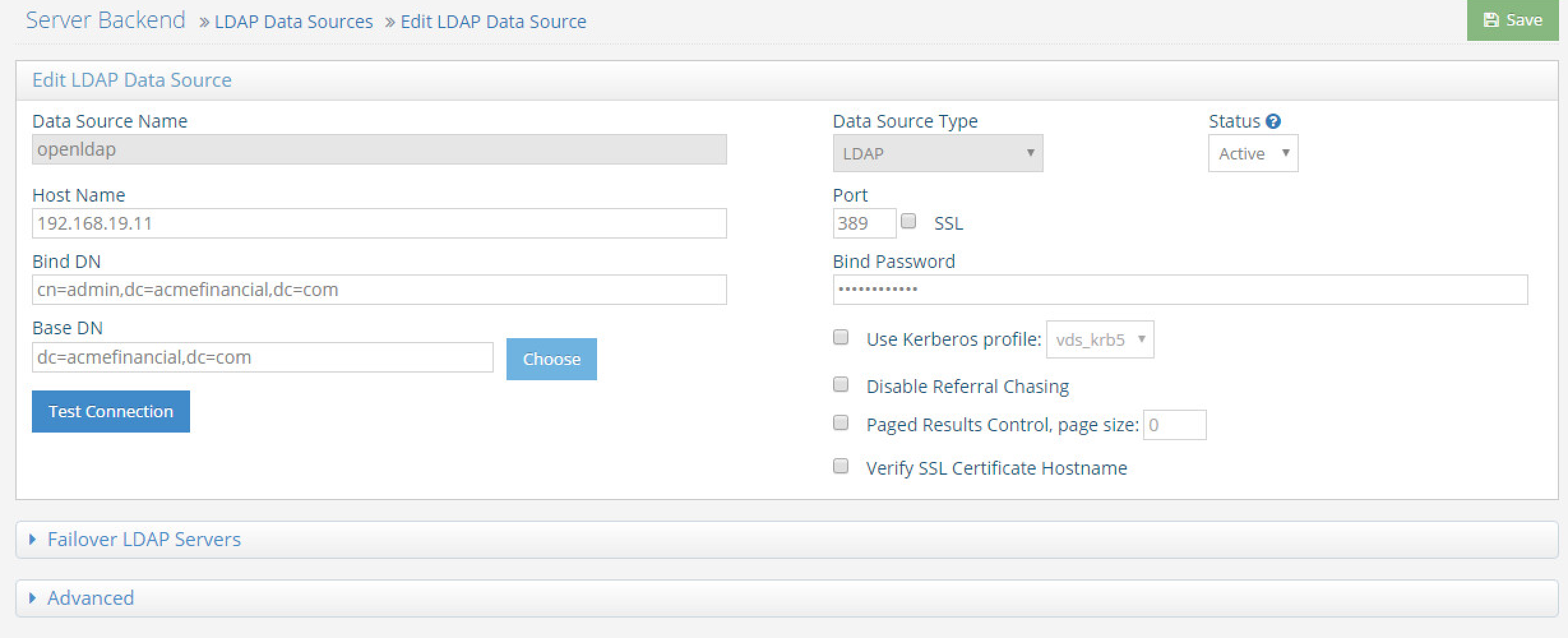
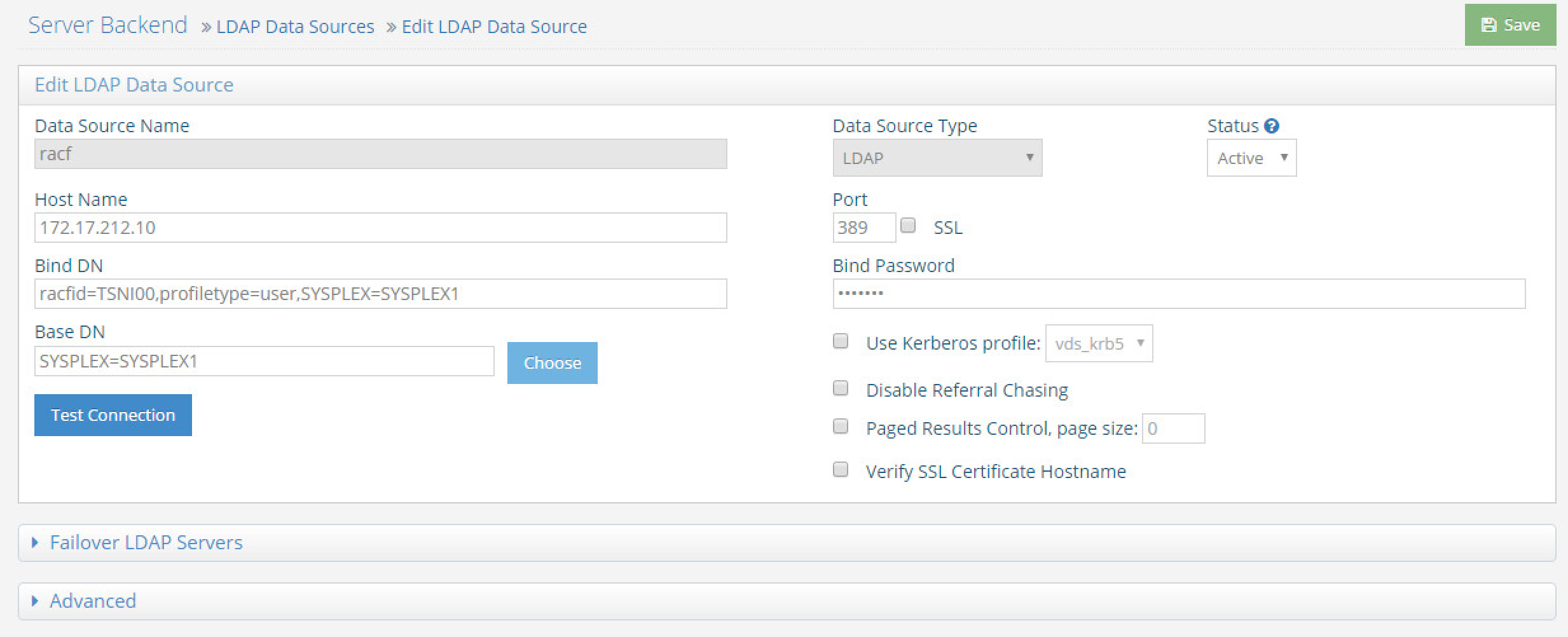
To create a proxy view to the backend directories, complete the following steps:
On the Directory Namespace tab, select New Naming Context (the plus sign) at the top left of the screen.
Select the LDAP Backend radio button and enter a naming context such as o=directoryProxy. Select Next.
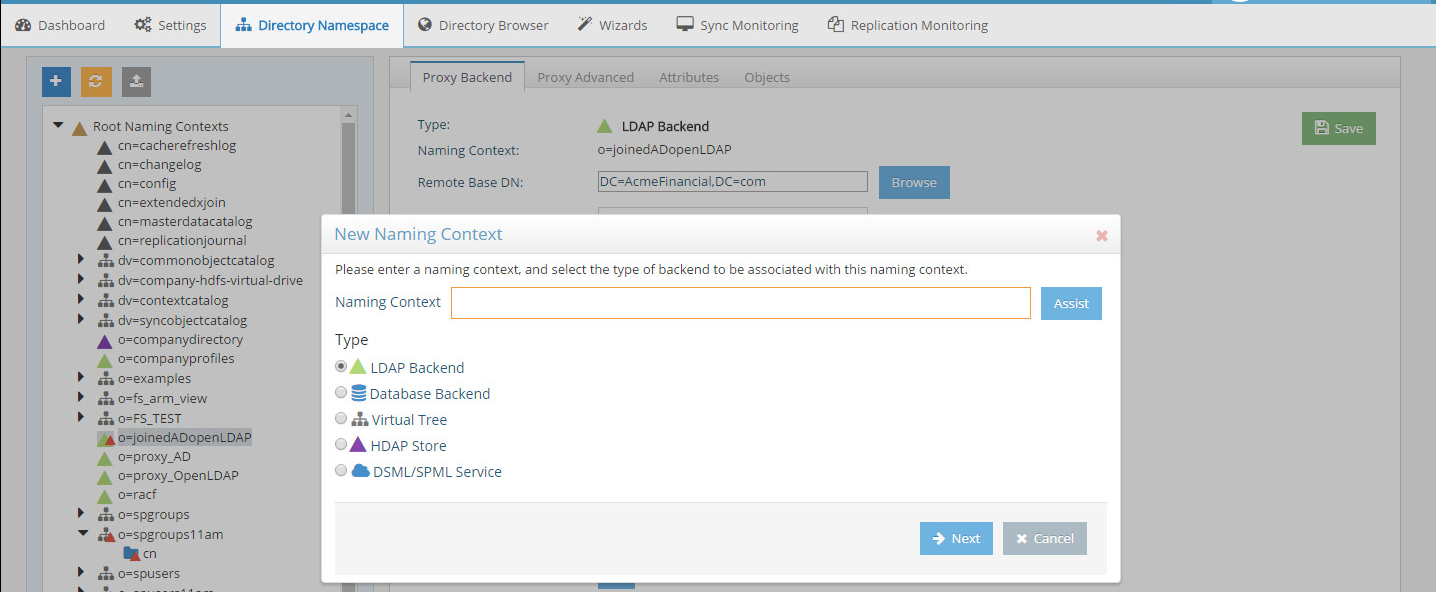
Select the name of the AD backend created earlier as the Data Source. Select the Remote Base DN of the domain. Select OK.
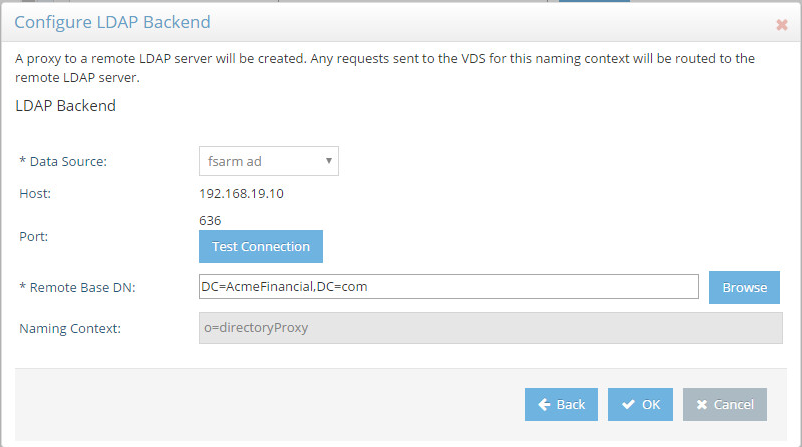
When the LDAP proxy is created, select the root naming context created in the left window pane.
Choose Regular. Click Next.
Select employeeNumber as the Join Attribute. Click Next. Note: The employee number must be unique for each user. For example, if an employee has an account in AD and OpenLDAP, the employeeNumber attribute should be the same in both sources for that employee.
Select openLDAP as the Data Source and enter dc=acmefinancial,dc=com as the Base DN. Specify sub as the Scope, inetOrgPerson as the Object Class, and employeeNumber as the Join Attribute. Leave Size Limit as default. Click Next.
Repeat Steps 5–10 to join the RACF directory using the appropriate RACF objectClass and Base DN.
2.6.5. Configure Logging¶
To log changes to each directory object, you must create a cache for the proxy view created in the previous section. To create the cache and log changes made to the backend directories, complete the following steps:
Navigate to the Sync Monitoring tab. Press the Play button to start the glassfish server.
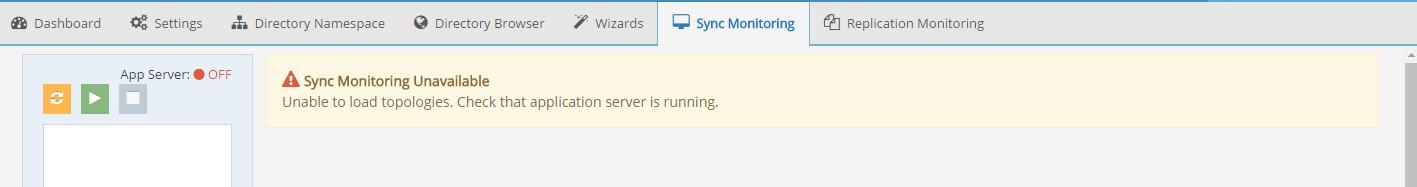
In the Directory Namespace tab, highlight Cache in the left window pane. Select Persistent Cache with Automated Refresh. Click Create Persistent Cache.
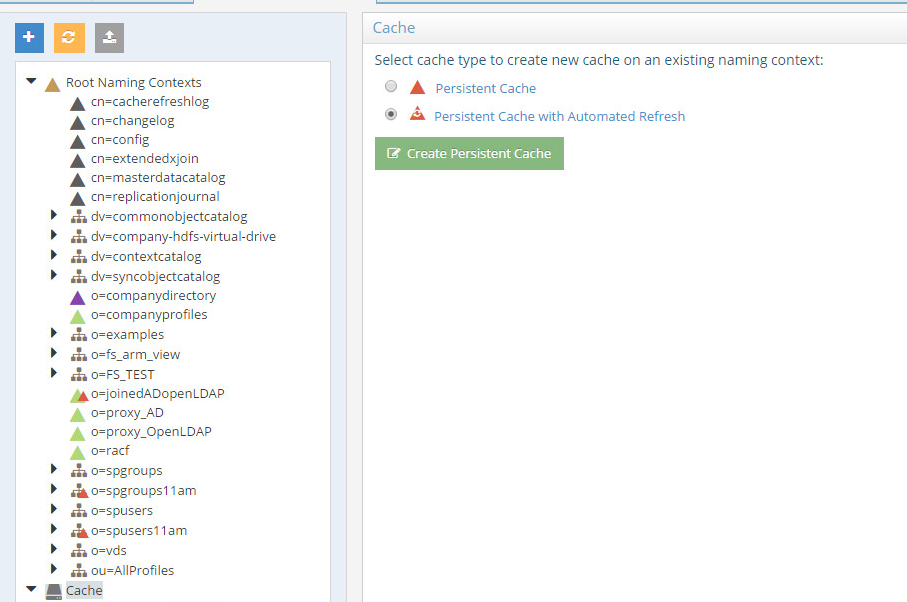
Browse and select the LDAP proxy created in the previous section. Select OK. The VD creates the cache.
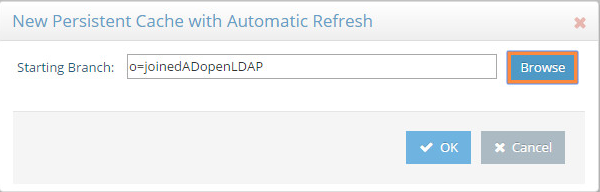
Select the created cache from the lower left window. Click Initialize to make the cache active.
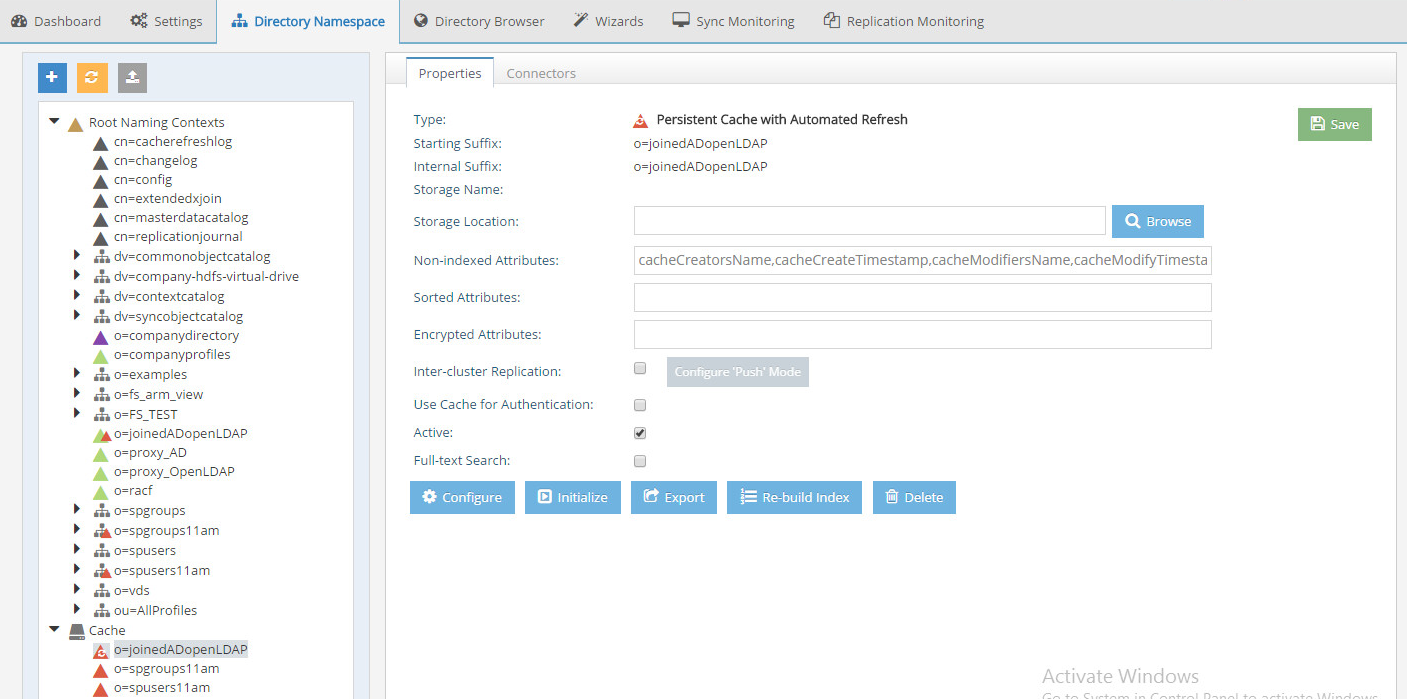
Select Create a new LDIF file from a snapshot of the virtual directory branch. Click OK. This step may take a while depending on the number of accounts in the backend directories.
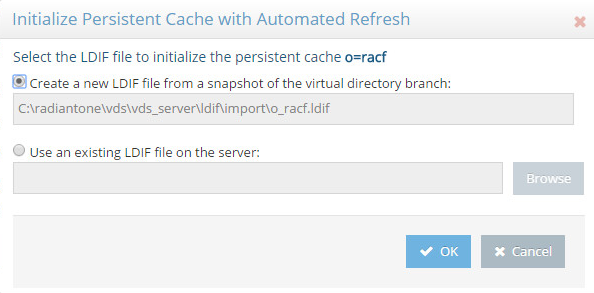
Once complete, Save the settings.
Select the Connectors tab.
There should be a connector for each backend directory and one for the connector itself. Highlight the first connector. Select Configure. Change the connector type to “Capture [Snapshot].” Click OK. Repeat this step for each connector except the “vdsconnector-cacherefresh.”
Back at the Connectors tab, highlight the first connector. Select Settings. Change the log level to the number 4. Click OK. Repeat this step for each connector except the “vdsconnector-cacherefresh.”
If the Status from each connector reads STARTED, you are done with this step. If not, review the logs and check the connections to the backend databases.
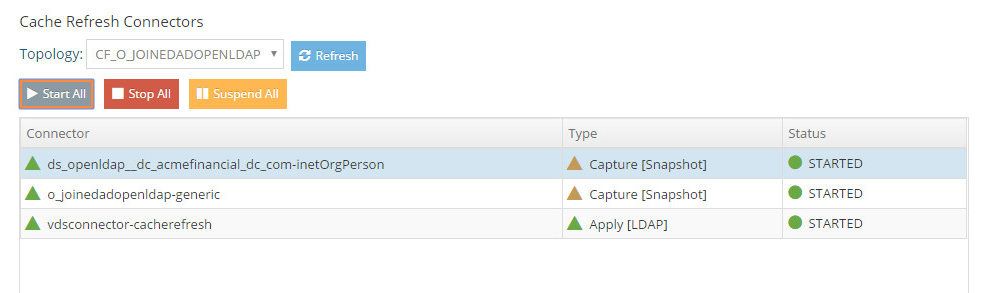
2.6.7. Scripts¶
Two PowerShell scripts are scheduled to run on regular intervals on RadiantOne VDS server. The goal of these scripts is to determine if the virtual directory server (RadiantOne VDS) and the RACF directory server are online or offline. The first script determines if RadiantOne VDS is online or offline and writes the corresponding status message to a local file being monitored by Splunk. The second script, which also runs on the RadiantOne VDS server, determines if the Vanguard RACF directory is reachable and writes corresponding offline or online messages to a local file also being monitored by Splunk.
2.6.8. Script: RadiantOnlineStatus.ps1¶
#This script checks determines if this server is online or offline
#If gateway route exists and VDS server is running, the script will
#output the current time, hostname, status and previous time (last
#time it wrote to output file)
#Check if gateway route exists and if the VDS service is running
if ((Get-Netroute 0.0.0.0/0) -And (Get-Process vdsserver))
{
#Store date in PrevTime variable
$PrevTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyyy"
#Check if prevtime-file.txt exists
if (ls C:\scripts\Radiant\prevtime-file.txt)
{
#Place the contents of prevtime-file.txt in the PrevTime variable
$PrevTime=Get-Content C:\scripts\Radiant\prevtime-file.txt
}
#Place the current date in CurrentTime
$CurrentTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy"
#Overwrite the contents of prevtime-file.txt with the current date
Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy" > C:\scripts\Radiant\prevtime-file.txt
$HostVar = hostname
$Status = 'online'
#Add the contents of the variables CurrentTime, HostVar, Status, PrevTime to Radiant-Status-Output.csv
Add-Content C:\scripts\Radiant\Radiant-Status-Output.csv $CurrentTime','$HostVar','$Status','$PrevTime
}
else
{
$PrevTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyyy"
if (ls C:\scripts\Radiant\prevtime-file.txt)
{
$PrevTime=Get-Content C:\scripts\Radiant\prevtime-file.txt
}
$CurrentTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy"
Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy" > C:\scripts\Radiant\prevtime-file.txt
$HostVar = hostname
$Status = 'offline'
Add-Content C:\scripts\Radiant\Radiant-Status-Output.csv $CurrentTime','$HostVar','$Status','$PrevTime
}
2.6.9. Script: VanguardOnlineStatus.ps1¶
#Script checks if the RACF mainframe is online and outputs status messages to file
#Check if the RACF mainframe is reachable with pings
if (ping -n 3 172.17.212.10 | select-string "Reply from 172.17.212.10")
{
#Store date in PrevTime variable
$PrevTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyyy"
#Check if prevtime-file.txt exists
if (ls C:\scripts\Vanguard\prevtime-file.txt)
{
#Place the contents of prevtime-file.txt in the PrevTime variable
$PrevTime=Get-Content C:\scripts\Vanguard\prevtime-file.txt
}
#Place the current date in CurrentTime
$CurrentTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy"
#Overwrite the contents of prevtime-file.txt with the current date
Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy" > C:\scripts\Vanguard\prevtime-file.txt
$HostVar = "VanguardMainframe.acmefinancial.com"
$Status = 'online'
Add-Content C:\scripts\Vanguard\VanguardServer-Output.csv $CurrentTime','$HostVar','$Status','$PrevTime
}
else
{
$PrevTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyyy"
if (ls C:\scripts\Vanguard\prevtime-file.txt)
{
$PrevTime=Get-Content C:\scripts\Vanguard\prevtime-file.txt
}
$CurrentTime = Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy"
Get-Date -format "ddd MMM dd HH:mm:ss \EST yyy" > C:\scripts\Vanguard\prevtime-file.txt
$HostVar = "VanguardMainframe.acmefinancial.com"
$Status = 'offline'
Add-Content C:\scripts\Vanguard\VanguardServer-Output.csv $CurrentTime','$HostVar','$Status','$PrevTime
}
2.6.10. LDAPS Configuration¶
RadiantOne VDS virtual directory service connects to the Active Directory, OpenLDAP, and RACF backend directory servers and takes snapshots of the directory contents. Configuring LDAPS ensures that this process is encrypted with SSL. To use LDAPS to make these connections, follow these steps:
- Copy the certificates of the backend directories to the RadiantOne VDS virtual directory server.
- Import each certificate into the client trust store by opening the Main Control Panel.
- Click Settings tab > Security section > Client Certificate Trust Store.
- The certificates will be dynamically loaded into the Client Certificate Trust Store.
- Configure the backend connections to use LDAPS by going to the Settings tab.
- Click Server Backend > LDAP Data Sources > Edit LDAP Data Source.
- Check the SSL box and type 636 into the Port text box.
2.8. Splunk¶
Splunk is a Security Information and Event Management system that allows for the collection and parsing of logs and data from multiple systems.
2.8.1. How It’s Used¶
Splunk can receive data from a plethora of different sources. The most reliable option is installing Splunk’s “Universal Forwarder” on each system you want to collect data from. Other options include syslogs, file and directory monitoring, network events, and more. Once data has been collected by Splunk, it can then be parsed and displayed using prebuilt rules or custom criteria.
2.8.2. Installation¶
Note: You will need a Splunk account to download Splunk Enterprise. The account is free and can be set up at https://www.splunk.com/page/sign_up.
Download Splunk Enterprise from https://www.splunk.com/en_us/download/splunk-enterprise.html. Splunk can be installed on Windows, Linux, Solaris, and Mac OS X. Each of these installation instructions can be found at:
2.8.3. Queries¶
Splunk reports, alerts, and dashboards are powered by queries written in the Splunk Search Processing Language (SPL). These queries are used to perform the analytics responsible for capturing events, identifying trends, and detecting anomalies. Once a query is written, it can be saved as a report, an alert, or as a dashboard panel. The following queries were also saved to dashboards to provide a central viewing location for operators, managers, and decision makers.
2.8.4. Query: Detect User Provisioning Accounts Events¶
The following search query detects when a user account is provisioned or when the user account attributes are modified. The provisioning and modification events detected include those that are in compliance with the established workflow and originate from the approved provisioning system, as well as those that violate the workflow. The output of the query shows which events were authorized and which were not.
(index=main sourcetype="wineventlog:security" EventCode=5136 OR EventCode=4720) OR (index=sandbox sourcetype="alertstatictest" OR sourcetype="RadiantSourceTest") OR (index=main sourcetype="openldap-outlog")
| rex "givenName:(?P<FirstName>\w+)"
| rex "sn:(?P<LastName>\w+)"
| rex mode=sed "s/;;/ /g"
| rex "changetype:(?P<RLICHANGETYPE>\w+)"
| rex "employeeNumber:(?P<EmployeeNumber>\w+)"
| rex "changetype:modify (?P<CHANGE>.+)"
| rex "conn=\d+\s\w+\:cn=(?P<LDAP_UID>\w+\S\w+)"
| rex "A user account was (?P<RLICHANGETYPE>\w+)"
| rex "A directory service object was (?P<RLICHANGETYPE>\w+)"
| eval RLICHANGETYPE=if(RLICHANGETYPE=="modified","update",RLICHANGETYPE)
| eval RLICHANGETYPE=if(RLICHANGETYPE=="created","insert", RLICHANGETYPE)
| eval RLICHANGETYPE=if(RLICHANGETYPE=="add","insert",RLICHANGETYPE)
| fields _time host checkStatus checkAuthFields EmployeeNo FirstName LastName ADUserId LDAPUserId RLICHANGETYPE employeeNumber givenName sn uid gidnumber RLICHANGES LDAP_UID LDAP_MSG AD_UID AD_MSG
| rex "\-create\(\):User: (?P<LDAP_UID>\w+\.\w+)"
| rex "\-create\(\):User: (?P<AD_UID>\w+\s)"
| rex "\-create\(\):User: (?P<LDAP_MSG>\w+\.\w+\s\w+\s\w+)"
| rex "\-create\(\):User: (?P<AD_MSG>\w+\s\w+\s\w+)"
| rex "<RLICHANGETYPE>(?P<RLICHANGETYPE>\w+)"
| rex "<RLICHANGES>(?P<RLICHANGES>.+)\<\/RLICHANGES\>"
| rex "employeeNumber: (?P<EmployeeNumber>\w+)"
| rex "sn: (?P<SurName>\w+)"
| rex "givenName: (?P<GivenName>\w+)"
| rex "gidNumber: (?P<GidNumber>\w+)"
| rex "mail: (?P<mail>\S+)"
| rex "departmentNumber: (?P<DeptNumber>\w+)"
| rex "## l: (?P<L>\w+)"
| rex "## o: (?P<O>\w+)"
| rex "## pager: (?P<Pager>\w+)"
| rex "## initials: (?P<Initials>\w+)"
| rex "mobile: (?P<Mobile>\w+)"
| rex "modifiersName: (?P<ModifiersName>\S+\s*\S+)"
| rex "\<givenName\>(?P<GivenName>\S+\s*\S+)\<\/givenName\>"
| rex "\<sn\>(?P<SurName>\S+\s*\S+)\<\/sn\>"
| rex "\<employeeNumber\>(?P<EmployeeNumber>\S+\s*\S+)\<\/employeeNumber\>"
| table _time host checkStatus EmployeeNo FirstName LastName EmployeeNumber GivenName SurName RLICHANGETYPE RLICHANGES checkAuthFields LDAP_UID LDAP_MSG AD_UID AD_MSG ADUserId LDAPUserId
| where (isnotnull(FirstName)) OR (isnotnull(RLICHANGES) OR (isnotnull(LDAP_MSG)) OR (isnotnull(AD_MSG))) OR isnotnull(RLICHANGETYPE)
| eval F_Name=coalesce(FirstName,GivenName)
| eval L_Name=coalesce(LastName,SurName)
| eval EmpNo=coalesce(EmployeeNo,EmployeeNumber)
| eval LDAP_UID=coalesce(LDAP_UID,LDAPUserId)
| eval AD_UID=coalesce(AD_UserId,AD_UID)
| table _time host checkStatus EmpNo F_Name L_Name RLICHANGETYPE RLICHANGES checkAuthFields LDAP_UID AD_UID LDAP_MSG AD_MSG
| eval RLICHANGES=if(RLICHANGETYPE=="insert","New User Record",RLICHANGES)
| eval LDAP_UID=if((isnull(LDAP_UID) AND host=="RadiantOne VDS"),lower(F_Name+"."+L_Name),LDAP_UID)
| eval AD_UID=if(isnull(AD_UID),lower(substr(F_Name,1,1) + substr(L_Name,1)),AD_UID)
| eval RLICHANGES=if(Like(LDAP_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(AD_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(LDAP_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(AD_MSG,"%created%"),"New User Record",RLICHANGES)
| eval UniqueKey=lower(LDAP_UID+"."+AD_UID)
| eval host=if(host=="WIN-CHSUIS3NKVR","AlertEnterprise-WIN",host)
| transaction UniqueKey, RLICHANGES maxspan=120s
| eval host1=if(Like(host,"%RadiantOne VDS%"),"RadiantOne VDS","NULL")
| eval host2=if(Like(host, "%WIN%"),"AlertE","NULL")
| eval Authority=if((host1=="RadiantOne VDS" AND host2=="AlertE"), "Authorized", "Not Legal")
| eval Authority=if((host1=="RadiantOne VDS" AND host2=="NULL"), "Unauthorized", Authority)
| table _time host Authority RLICHANGETYPE RLICHANGES EmpNo F_Name L_Name LDAP_UID AD_UID ADCHANGETYPE
| where isnotnull(EmpNo)
| table _time host Authority RLICHANGETYPE RLICHANGES EmpNo F_Name L_Name LDAP_UID AD_UID
| where Authority !="Not Legal"
| eval CHANGES=if(isnotnull(RLICHANGES),RLICHANGES,RLICHANGES)
| eval CHANGETYPE=if(isnotnull(RLICHANGETYPE),RLICHANGETYPE,RLICHANGETYPE)
| table _time host Authority CHANGETYPE CHANGES EmpNo F_Name L_Name LDAP_UID AD_UID
| where Not Like(CHANGES, "%lastLogonTimestamp%")
2.8.5. Query: Authorized and Unauthorized Provisioning Trend Line Chart¶
The following search query generates a line chart showing the trends for both the authorized and unauthorized provisioning events:
earliest="1/25/2017:00:00:00" latest="2/15/2017:00:00:00" index=sandbox sourcetype="alertstatictest" OR sourcetype="RadiantSourceTest"
| fields _time host checkStatus checkAuthFields EmployeeNo FirstName LastName ADUserId LDAPUserId RLICHANGETYPE employeeNumber givenName sn uid gidnumber RLICHANGES LDAP_UID LDAP_MSG AD_UID AD_MSG
| rex "\-create\(\):User: (?P<LDAP_UID>\w+\.\w+)"
| rex "\-create\(\):User: (?P<AD_UID>\w+\s)"
| rex "\-create\(\):User: (?P<LDAP_MSG>\w+\.\w+\s\w+\s\w+)"
| rex "\-create\(\):User: (?P<AD_MSG>\w+\s\w+\s\w+)"
| rex "<RLICHANGETYPE>(?P<RLICHANGETYPE>\w+)"
| rex "<RLICHANGES>(?P<RLICHANGES>.+)\<\/RLICHANGES\>"
| rex "employeeNumber: (?P<EmployeeNumber>\w+)"
| rex "sn: (?P<SurName>\w+)"
| rex "givenName: (?P<GivenName>\w+)"
| rex "gidNumber: (?P<GidNumber>\w+)"
| rex "mail: (?P<mail>\S+)"
| rex "departmentNumber: (?P<DeptNumber>\w+)"
| rex "## l: (?P<L>\w+)"
| rex "## o: (?P<O>\w+)"
| rex "## pager: (?P<Pager>\w+)"
| rex "## initials: (?P<Initials>\w+)"
| rex "mobile: (?P<Mobile>\w+)"
| rex "modifiersName: (?P<ModifiersName>\S+\s*\S+)"
| rex "\<givenName\>(?P<GivenName>\S+\s*\S+)\<\/givenName\>"
| rex "\<sn\>(?P<SurName>\S+\s*\S+)\<\/sn\>"
| rex "\<employeeNumber\>(?P<EmployeeNumber>\S+\s*\S+)\<\/employeeNumber\>"
| table _time host checkStatus EmployeeNo FirstName LastName EmployeeNumber GivenName SurName RLICHANGETYPE RLICHANGES checkAuthFields LDAP_UID LDAP_MSG AD_UID AD_MSG ADUserId LDAPUserId
| where (isnotnull(FirstName)) OR (isnotnull(RLICHANGES) OR (isnotnull(LDAP_MSG)) OR (isnotnull(AD_MSG)))
| eval F_Name=coalesce(FirstName,GivenName)
| eval L_Name=coalesce(LastName,SurName)
| eval EmpNo=coalesce(EmployeeNo,EmployeeNumber)
| eval LDAP_UID=coalesce(LDAP_UID,LDAPUserId)
| eval AD_UID=coalesce(AD_UserId,AD_UID)
| table _time host checkStatus EmpNo F_Name L_Name RLICHANGETYPE RLICHANGES checkAuthFields LDAP_UID AD_UID LDAP_MSG AD_MSG
| eval RLICHANGES=if(RLICHANGETYPE=="insert","New User Record",RLICHANGES)
| eval LDAP_UID=if((isnull(LDAP_UID) AND host=="RadiantOne VDS"),lower(F_Name+"."+L_Name),LDAP_UID)
| eval AD_UID=if(isnull(AD_UID),lower(substr(F_Name,1,1) + substr(L_Name,1)),AD_UID)
| eval RLICHANGES=if(Like(LDAP_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(AD_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(LDAP_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(AD_MSG,"%created%"),"New User Record",RLICHANGES)
| eval UniqueKey=lower(LDAP_UID+"."+AD_UID)
| eval host=if(host=="WIN-CHSUIS3NKVR","AlertEnterprise-WIN",host)
| transaction UniqueKey, RLICHANGES maxspan=120s
| eval host1=if(Like(host,"%RadiantOne VDS%"),"RadiantOne VDS","NULL")
| eval host2=if(Like(host, "%WIN%"),"AlertE","NULL")
| eval Authority=if((host1=="RadiantOne VDS" AND host2=="AlertE"), "Authorized", "Not Legal")
| eval Authority=if((host1=="RadiantOne VDS" AND host2=="NULL"), "Unauthorized", Authority)
| table _time host Authority RLICHANGETYPE RLICHANGES EmpNo F_Name L_Name LDAP_UID AD_UID
| where isnotnull(EmpNo)
| table _time host Authority RLICHANGETYPE RLICHANGES EmpNo F_Name L_Name LDAP_UID AD_UID
| where Authority !="Not Legal"
| eval CHANGES=if(isnotnull(RLICHANGES),RLICHANGES,RLICHANGES)
| eval CHANGETYPE=if(isnotnull(RLICHANGETYPE),RLICHANGETYPE,RLICHANGETYPE)
| table _time host Authority CHANGETYPE CHANGES EmpNo F_Name L_Name LDAP_UID AD_UID
| timechart span=2d count BY Authority
2.8.6. Query: Combined Provisioning Trend Line Chart¶
The following search query generates a line chart that shows the total authorized and unauthorized provisioning events combined in a single trend line:
index=sandbox sourcetype="alertstatictest" OR sourcetype="RadiantSourceTest"
| fields _time host checkStatus checkAuthFields EmployeeNo FirstName LastName ADUserId LDAPUserId RLICHANGETYPE employeeNumber givenName sn uid gidnumber RLICHANGES LDAP_UID LDAP_MSG AD_UID AD_MSG
| rex "\-create\(\):User: (?P<LDAP_UID>\w+\.\w+)"
| rex "\-create\(\):User: (?P<AD_UID>\w+\s)"
| rex "\-create\(\):User: (?P<LDAP_MSG>\w+\.\w+\s\w+\s\w+)"
| rex "\-create\(\):User: (?P<AD_MSG>\w+\s\w+\s\w+)"
| rex "<RLICHANGETYPE>(?P<RLICHANGETYPE>\w+)"
| rex "<RLICHANGES>(?P<RLICHANGES>.+)\<\/RLICHANGES\>"
| rex "employeeNumber: (?P<EmployeeNumber>\w+)"
| rex "sn: (?P<SurName>\w+)"
| rex "givenName: (?P<GivenName>\w+)"
| rex "gidNumber: (?P<GidNumber>\w+)"
| rex "mail: (?P<mail>\S+)"
| rex "departmentNumber: (?P<DeptNumber>\w+)"
| rex "## l: (?P<L>\w+)"
| rex "## o: (?P<O>\w+)"
| rex "## pager: (?P<Pager>\w+)"
| rex "## initials: (?P<Initials>\w+)"
| rex "mobile: (?P<Mobile>\w+)"
| rex "modifiersName: (?P<ModifiersName>\S+\s*\S+)"
| rex "\<givenName\>(?P<GivenName>\S+\s*\S+)\<\/givenName\>"
| rex "\<sn\>(?P<SurName>\S+\s*\S+)\<\/sn\>"
| rex "\<employeeNumber\>(?P<EmployeeNumber>\S+\s*\S+)\<\/employeeNumber\>"
| table _time host checkStatus EmployeeNo FirstName LastName EmployeeNumber GivenName SurName RLICHANGETYPE RLICHANGES checkAuthFields LDAP_UID LDAP_MSG AD_UID AD_MSG ADUserId LDAPUserId
| where (isnotnull(FirstName)) OR (isnotnull(RLICHANGES) OR (isnotnull(LDAP_MSG)) OR (isnotnull(AD_MSG)))
| eval F_Name=coalesce(FirstName,GivenName)
| eval L_Name=coalesce(LastName,SurName)
| eval EmpNo=coalesce(EmployeeNo,EmployeeNumber)
| eval LDAP_UID=coalesce(LDAP_UID,LDAPUserId)
| eval AD_UID=coalesce(AD_UserId,AD_UID)
| table _time host checkStatus EmpNo F_Name L_Name RLICHANGETYPE RLICHANGES checkAuthFields LDAP_UID AD_UID LDAP_MSG AD_MSG
| eval RLICHANGES=if(RLICHANGETYPE=="insert","New User Record",RLICHANGES)
| eval LDAP_UID=if((isnull(LDAP_UID) AND host=="RadiantOne VDS"),lower(F_Name+"."+L_Name),LDAP_UID)
| eval AD_UID=if(isnull(AD_UID),lower(substr(F_Name,1,1) + substr(L_Name,1)),AD_UID)
| eval RLICHANGES=if(Like(LDAP_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(AD_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(LDAP_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(AD_MSG,"%created%"),"New User Record",RLICHANGES)
| eval UniqueKey=lower(LDAP_UID+"."+AD_UID)
| eval host=if(host=="WIN-CHSUIS3NKVR","AlertEnterprise-WIN",host)
| transaction UniqueKey, RLICHANGES maxspan=120s
| eval host1=if(Like(host,"%RadiantOne VDS%"),"RadiantOne VDS","NULL")
| eval host2=if(Like(host, "%WIN%"),"AlertE","NULL")
| eval Authority=if((host1=="RadiantOne VDS" AND host2=="AlertE"), "Authorized", "Not Legal")
| eval Authority=if((host1=="RadiantOne VDS" AND host2=="NULL"), "Unauthorized", Authority)
| table _time host Authority RLICHANGETYPE RLICHANGES EmpNo F_Name L_Name LDAP_UID AD_UID
| where isnotnull(EmpNo)
| table _time host Authority RLICHANGETYPE RLICHANGES EmpNo F_Name L_Name LDAP_UID AD_UID
| where Authority !="Not Legal"
| eval CHANGES=if(isnotnull(RLICHANGES),RLICHANGES,RLICHANGES)
| eval CHANGETYPE=if(isnotnull(RLICHANGETYPE),RLICHANGETYPE,RLICHANGETYPE)
| table _time host Authority CHANGETYPE CHANGES EmpNo F_Name L_Name LDAP_UID AD_UID
| eval Event=if(isnotnull(Authority),"Provisioning", "Null")
| timechart span=2d count BY Event
2.8.7. Query: Detect modifications to High Value or Privileged Accounts¶
The following search query detects any modification to high-value accounts or privileged accounts, such as managers and system administrators. It detects modifications that violate corporate policy as well as those that are performed in accordance to policy.
(index=main sourcetype="wineventlog:security" EventCode=5136 OR EventCode=4720) OR (index=sandbox sourcetype="alertstatictest" OR sourcetype="RadiantSourceTest") OR (index=main sourcetype="openldap-outlog")
| rex "givenName:(?P<FirstName>\w+)"
| rex "sn:(?P<LastName>\w+)"
| rex mode=sed "s/;;/ /g"
| rex "changetype:(?P<RLICHANGETYPE>\w+)"
| rex "employeeNumber:(?P<EmployeeNumber>\w+)"
| rex "changetype:modify (?P<CHANGE>.+)"
| rex "conn=\d+\s\w+\:cn=(?P<LDAP_UID>\w+\S\w+)"
| rex "A user account was (?P<RLICHANGETYPE>\w+)"
| rex "A directory service object was (?P<RLICHANGETYPE>\w+)"
| eval RLICHANGETYPE=if(RLICHANGETYPE=="modified","update",RLICHANGETYPE)
| eval RLICHANGETYPE=if(RLICHANGETYPE=="created","insert", RLICHANGETYPE)
| eval RLICHANGETYPE=if(RLICHANGETYPE=="add","insert",RLICHANGETYPE)
| fields _time host checkStatus checkAuthFields EmployeeNo FirstName LastName ADUserId LDAPUserId RLICHANGETYPE employeeNumber givenName sn uid gidnumber RLICHANGES LDAP_UID LDAP_MSG AD_UID AD_MSG
| rex "\-create\(\):User: (?P<LDAP_UID>\w+\.\w+)"
| rex "\-create\(\):User: (?P<AD_UID>\w+\s)"
| rex "\-create\(\):User: (?P<LDAP_MSG>\w+\.\w+\s\w+\s\w+)"
| rex "\-create\(\):User: (?P<AD_MSG>\w+\s\w+\s\w+)"
| rex "<RLICHANGETYPE>(?P<RLICHANGETYPE>\w+)"
| rex "<RLICHANGES>(?P<RLICHANGES>.+)\<\/RLICHANGES\>"
| rex "employeeNumber: (?P<EmployeeNumber>\w+)"
| rex "sn: (?P<SurName>\w+)"
| rex "givenName: (?P<GivenName>\w+)"
| rex "gidNumber: (?P<GidNumber>\w+)"
| rex "mail: (?P<mail>\S+)"
| rex "departmentNumber: (?P<DeptNumber>\w+)"
| rex "## l: (?P<L>\w+)"
| rex "## o: (?P<O>\w+)"
| rex "## pager: (?P<Pager>\w+)"
| rex "## initials: (?P<Initials>\w+)"
| rex "mobile: (?P<Mobile>\w+)"
| rex "modifiersName: (?P<ModifiersName>\S+\s*\S+)"
| rex "\<givenName\>(?P<GivenName>\S+\s*\S+)\<\/givenName\>"
| rex "\<sn\>(?P<SurName>\S+\s*\S+)\<\/sn\>"
| rex "\<employeeNumber\>(?P<EmployeeNumber>\S+\s*\S+)\<\/employeeNumber\>"
| table _time host checkStatus EmployeeNo FirstName LastName EmployeeNumber GivenName SurName RLICHANGETYPE RLICHANGES checkAuthFields LDAP_UID LDAP_MSG AD_UID AD_MSG ADUserId LDAPUserId
| where (isnotnull(FirstName)) OR (isnotnull(RLICHANGES) OR (isnotnull(LDAP_MSG)) OR (isnotnull(AD_MSG))) OR isnotnull(RLICHANGETYPE)
| eval F_Name=coalesce(FirstName,GivenName)
| eval L_Name=coalesce(LastName,SurName)
| eval EmpNo=coalesce(EmployeeNo,EmployeeNumber)
| eval LDAP_UID=coalesce(LDAP_UID,LDAPUserId)
| eval AD_UID=coalesce(AD_UserId,AD_UID)
| table _time host checkStatus EmpNo F_Name L_Name RLICHANGETYPE RLICHANGES checkAuthFields LDAP_UID AD_UID LDAP_MSG AD_MSG
| eval RLICHANGES=if(RLICHANGETYPE=="insert","New User Record",RLICHANGES)
| eval LDAP_UID=if((isnull(LDAP_UID) AND host=="RadiantOne VDS"),lower(F_Name+"."+L_Name),LDAP_UID)
| eval AD_UID=if(isnull(AD_UID),lower(substr(F_Name,1,1) + substr(L_Name,1)),AD_UID)
| eval RLICHANGES=if(Like(LDAP_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(AD_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(LDAP_MSG,"%created%"),"New User Record",RLICHANGES)
| eval RLICHANGES=if(Like(AD_MSG,"%created%"),"New User Record",RLICHANGES)
| eval UniqueKey=lower(LDAP_UID+"."+AD_UID)
| eval host=if(host=="WIN-CHSUIS3NKVR","AlertEnterprise-WIN",host)
| transaction UniqueKey, RLICHANGES maxspan=120s
| eval host1=if(Like(host,"%RadiantOne VDS%"),"RadiantOne VDS","NULL")
| eval host2=if(Like(host, "%WIN%"),"AlertE","NULL")
| eval Authority=if((host1=="RadiantOne VDS" AND host2=="AlertE"), "Authorized", "Not Legal")
| eval Authority=if((host1=="RadiantOne VDS" AND host2=="NULL"), "Unauthorized", Authority)
| table _time host Authority RLICHANGETYPE RLICHANGES EmpNo F_Name L_Name LDAP_UID AD_UID ADCHANGETYPE
| where isnotnull(EmpNo)
| table _time host Authority RLICHANGETYPE RLICHANGES EmpNo F_Name L_Name LDAP_UID AD_UID
| where Authority !="Not Legal"
| eval CHANGES=if(isnotnull(RLICHANGES),RLICHANGES,RLICHANGES)
| eval CHANGETYPE=if(isnotnull(RLICHANGETYPE),RLICHANGETYPE,RLICHANGETYPE)
| table _time host Authority CHANGETYPE CHANGES EmpNo F_Name L_Name LDAP_UID AD_UID
| where Not Like(CHANGES, "%lastLogonTimestamp%")
| table _time host Authority CHANGETYPE CHANGES EmpNo F_Name L_Name LDAP_UID AD_UID
| where isnotnull(CHANGETYPE) AND ((Like(CHANGES, "%MNGR%")) OR (Like(CHANGES, "%Manager%") OR Like(CHANGES, "%Administrator%")))
2.8.8. Query: Virtual Directory Server Offline Detection¶
The following search query detects when the virtual directory server goes offline. The virtual directory server is configured to send online status messages to Splunk at regular intervals. This query searches for those messages and declares the virtual directory server offline if the last online message received has exceeded the expected interval.
earliest=-24h sourcetype="radiant-status"
| table _time CurrentTime Hostname Status
| sort 1 -_time
| eval SearchTime_Epoch=now()
| eval CTime_Epoch=strptime(CurrentTime,"%a %b %d %H:%M:%S %Z %Y")
| eval TimeDiff=(SearchTime_Epoch - CTime_Epoch)
| eval Status=if(TimeDiff > 900, "Offline", Status)
| where Status=="offline"
| table CurrentTime Hostname Status
2.8.9. Query: Critical Servers Offline¶
The following search query detects when a directory server goes offline. The query uses the results of multiple data sources to determine when a server is offline and when it is online.
earliest=-12h (index=sandbox sourcetype="radiantsourcetest" ERROR) OR (index=main sourcetype=openldap-status1) OR (index=main sourcetype=AD-Status) OR (sourcetype="Vanguard-Status") OR (sourcetype="Radiant-Status")
| rex "Exception taking snapshot. Entries in snapshot: 0 Error :com.rli.slapd.server.LDAPException: (?P<IPAddress>\d+\.\d+\.\d+\.\d+)"
| rex "ERROR (?P<ConnectionStatus>\w+\s\w+)"
| table _time CurrentTime PrevTime Hostname Status IPAddress ConnectionStatus
| eval CTime=strptime(CurrentTime,"%a %b %d %H:%M:%S %Z %Y")
| eval PTime=strptime(PrevTime,"%a %b %d %H:%M:%S %Z %Y")
| eval TimeDiff=(CTime-PTime)
| eval Hostname=if(IPAddress=="192.168.19.11", "openldap.acmefinancial.com", Hostname)
| eval Hostname=if(IPAddress=="192.168.19.10", "ActiveDirectory.acmefinancial.com", Hostname)
| eval Hostname=if(Hostname=="RadiantOne VDS", "RadiantOne VDS.acmefinancial.com", Hostname)
| eval Hostname=if(Hostname=="ActiveDirectory", "ActiveDirectory.acmefinancial.com", Hostname)
| eval Status=if(ConnectionStatus=="Connection error", "offline", Status)
| where isnotnull(Hostname)
| transaction Hostname Status
| table _time Hostname Status
2.8.10. SSL Forwarding¶
We took advantage Splunk’s built in SSL forwarding capability and configured SSL encryption between forwarders and the indexer. Instructions to enable SSL forwarding can be found at http://docs.splunk.com/Documentation/Splunk/6.5.3/Security/ConfigureSplunkforwardingtousesignedcertificates.
2.9. TDI ConsoleWorks¶
ConsoleWorks is a product that provides a portal for remote access to devices, a logging facility with advanced hashing and pattern matching features, and role-based access control for administrators.
2.9.1. How It’s Used¶
ConsoleWorks provides a portal through which privileged users access directory servers and core systems in the lab infrastructure. There are two primary types of access connectors that are configured. The first is a console connector that is either an SSH or Telnet connection to an internal LAN system. The other is a graphical user interface (GUI) connector that can be either through Remote Desktop Protocol (RDP) or Virtual Network Computing (VNC). In this build, SSH was used for the console connections, whereas RDP was used for the GUI connections.
The ConsoleWorks Server sits on a separate subnet that is connected to the Internet via a virtual private network. It is configured to allow connections initiated from the VPN, but it drops connections initiated from the LAN.
Additionally, ConsoleWorks maintains logs of what systems were accessed, the time of access, and by whom. These logs are formatted and prepared for consumption by the Splunk indexer.
2.9.2. Virtual Machine Configuration¶
ConsoleWorks virtual machine is configured as follows:
- CentOS 7.2.1511
- 1CPU cor
- 8GB of RAM
- 2 NICs
- 100GB of storage.
Network Configuration (LAN)
Network Configuration (WAN)
2.9.3. Firewall Configuration¶
Enter the following commands in sequence to allow traffic to ports 5176 and 22 ports only. The ConsoleWorks web service listens on port 5176.
firewall-cmd – zone=public – add-port=5176/tcpfirewall-cmd – zone=public – add-port=22/tcp
2.9.4. Installation¶
Installation for Windows, Linux, and Solaris systems can be found at http://support.tditechnologies.com/tags/installation-guides
2.9.5. Console Connection Configuration¶
To create a console connection:
- Click on Consoles>Add.
- Type in the name of the Console (for example, OpenLDAPServer).
- Choose the Connector type (for example, SSH on Demand).
- Click Connection Details. Check the Exclusive Connect checkbox.
- Type in the Host IP, Port, Username, and Password fields.
- Click Save.
2.9.6. Graphical Gateway Configuration¶
A Graphical Gateway is required to make an RDP or VNC connection to a server.
To configure a Graphical Gateway, you need to obtain and install the graphical gateway package from TDi Technologies Inc. The following steps describe installing and starting the service once the package is obtained.
rpm -ivh /tmp/consoleworks/ConsoleWorks_gui_gateway-version>.rpm
/opt/gui_gateway/install_local.sh
/opt/ConsoleWorks/bin/cw_start <invocation name> (created during
installation)
service gui_gatewayd start
Install the Graphical gateway:
- On the landing page on your ConsoleWorks server, click GRAPHICAL>Gateways>Add.
- Give it a name, then set Host as Localhost and Port as 5172.
- Check Enabled checkbox and click Save.
- Verify it works by clicking Test in the top-left corner.
2.9.7. Graphical Connection Configuration¶
Configure the Graphical gateway:
- On the landing page of your ConsoleWorks server, click GRAPHICAL>Add.
- Type in the name of the Graphical connection (for example, ADServer).
- Choose a protocol in the Type drop-down list (for example, RDP).
- Enter the name or IP address of the server in the Host field.
- Type in the port number in the Port field. Enter 3389 for RDP.
- Click Save.
2.9.8. Profile Creation¶
- Click USERS>Profiles>Add.
- Type in the name of the profile in the Name field.
- Click Save.
2.9.9. Access Controls¶
Access controls are rules that determine the level of access a user has to a Console or Graphical connection. These rules can be associated with profiles and tags, which in turn can be associated with a user to determine what a user has access to when logged in. In our build, we grouped privileged users based on the servers they needed access to, created profiles that mirrored these groups, linked the users to these profiles, and associated the access rules to the profiles.
Create new access control rules:
- Copy the CONSOLE_CONTROL access control rule and assign it a number below 100. Access control rules with lower numbers have priority over higher numbers.
- Select the newly copied access rule and click Edit.
To create a profile:
- In the Allow or Deny field, Select ALLOW.
- In the component Type, select Console.
- In the Profile Selection area, select the profile of choice from the Simple tab and click the double arrows. Make sure it appears in the Profiles section.
- In the Resource Selection section, select the Console you want users associated with this profile to connect to. Select the OpenLDAP console.
- To set access control rules for Graphical connections: Copy the DEF_GRAPHICAL_DENY and rename as ALLOW_COPY_DEF_GRAPHICAL_1.
- Click Edit.
- To link an access control rule to a profile and a resource, first follow these steps:Edit this rule and change the Allow or Deny field from DENY to ALLOW.
- Change the Description to Default ALLOW Graphical Connection.
- Ensure that the order number is lower than the Default DENY Graphical Connection rule (DEF_GRAPHICAL_DENY).
- Under Profile Selection, click the Simple tab and select “Is one of these Profiles.”
- Select the profile of choice and make sure it appears on the right under Profiles.
- Next, you will need to Select the Graphical Connection of choice such as RADIANTONE VDS.
- Click the double arrow and ensure that it appears on the right.
To add users and link to a profile:
- Click on USERS > Add.
- Type in the username in Name field.
- Enter the password in the Password and Retype Password fields.
- Click on PROFILES > Add.
- Select the profile of choice.
2.9.10. User Auditing¶
An audit trail of ConsoleWorks user activity is captured in a file and forwarded to Splunk for further analysis. The the information includes username, logon timestamp, and the target server to which the user is connecting. The connection reporting script below parses the ConsoleWorks logs and writes the output to a file. The bash connectionreporting script removes duplicate lines. The bashconenctionreporting script is scheduled using cron to run every minute using the following /etc/crontab configuration.
2.9.11. Cron Configuration: /etc/crontab¶
SHELL=/bin/bash
PATH=/sbin:/bin:/usr/sbin:/usr/bin
MAILTO=root
# For details see man 4 crontabs
# Example of job definition:
# .---------------- minute (0 - 59)
# | .------------- hour (0 - 23)
# | | .---------- day of month (1 - 31)
# | | | .------- month (1 - 12) OR jan,feb,mar,apr ...
# | | | | .---- day of week (0 - 6) (Sunday=0 or 7) OR sun,mon,tue,wed,thu,fri,sat
# | | | | |
# * * * * * user-name command to be executed
* * * * * root /etc/cron.daily/bashconnectionreporting
2.9.12. Scripts: connectionreporting¶
#!/usr/bin/python3.5
#Script identifies ConsoleWorks users, connection times and their targets
#import the OS module
import os
#Store the ConsoleWorks log directory in the "directory" variable
directory = "/opt/ConsoleWorks/FSARM/log"
#Change directory to the Log dir
os.chdir(directory)
#Iterate through files in log dir and look for strings shown in the
#IF statements. Matching lines are written to file
for file in os.listdir(directory):
with open(file, 'r') as file_object:
for line in file_object:
if "CONWRKS Audit:: User:" in line:
with open('/var/log/connections.out','a') as outfile_object:
outfile_object.write(line)
if "connecting" in line:
with open('/var/log/connections.out','a') as outfile_object:
outfile_object.write(line)
if "disconnecting" in line:
with open('/var/log/connections.out','a') as outfile_object:
outfile_object.write(line)
2.9.13. Scripts: bashconnectionreporting¶
#!/bin/bash
#Calls python script that reads ConsoleWorks log files and outputs to
#/var/log/connections.out
/etc/cron.daily/connectionreporting
#This line removes duplicate lines from the connections.out file and outputs them
# to connections.log
awk '!seen[$0]++' /var/log/connections.out > /var/log/connections.log
2.10. Network Firewall Configuration¶
pfSense virtual devices were used as firewall routers for each subnet and were configured to restrict traffic as appropriate. The subnets listed below have critical services and resources that need to be accessed from devices external to the LAN. We have made the exact configuration used in each pfSense firewall available in XML format. This can be imported directly into another pfSense device. It is important to note that an IPSEC VPN connection was made to the offsite RACF LDAP directory server. The IPSEC VPN configuration was set up in the firewall for the backbone subnet.
2.10.1. Firewall Configuration for Backbone Subnet¶
<?xml version="1.0"?>
<pfsense>
<version>15.4</version>
<lastchange/>
<theme>pfsense_ng</theme>
<system>
<optimization>normal</optimization>
<hostname>pfsenseVLAN13</hostname>
<domain>acmefinancial.com</domain>
<group>
<name>all</name>
<description>
<![CDATA[All Users]]>
</description>
<scope>system</scope>
<gid>1998</gid>
<member>0</member>
</group>
<group>
<name>admins</name>
<description>
<![CDATA[System Administrators]]>
</description>
<scope>system</scope>
<gid>1999</gid>
<member>0</member>
<priv>page-all</priv>
</group>
<user>
<name>admin</name>
<descr>
<![CDATA[System Administrator]]>
</descr>
<scope>system</scope>
<groupname>admins</groupname>
<password>$1$dSJImFph$GvZ7.1UbuWu.Yb8etC0re.</password>
<uid>0</uid>
<priv>user-shell-access</priv>
</user>
<nextuid>2000</nextuid>
<nextgid>2000</nextgid>
<timezone>America/New_York</timezone>
<time-update-interval/>
<timeservers>10.97.74.8</timeservers>
<webgui>
<protocol>http</protocol>
<loginautocomplete/>
<ssl-certref>5720a0502b277</ssl-certref>
<dashboardcolumns>2</dashboardcolumns>
<webguicss>pfsense.css</webguicss>
</webgui>
<disablesegmentationoffloading/>
<disablelargereceiveoffloading/>
<ipv6allow/>
<powerd_ac_mode>hadp</powerd_ac_mode>
<powerd_battery_mode>hadp</powerd_battery_mode>
<powerd_normal_mode>hadp</powerd_normal_mode>
<bogons>
<interval>monthly</interval>
</bogons>
<language>en_US</language>
<dns1gw>GW_WAN</dns1gw>
<dns2gw>GW_WAN</dns2gw>
<dns3gw>none</dns3gw>
<dns4gw>none</dns4gw>
<maximumstates/>
<aliasesresolveinterval/>
<maximumtableentries/>
<maximumfrags/>
<enablenatreflectionpurenat>yes</enablenatreflectionpurenat>
<enablebinatreflection>yes</enablebinatreflection>
<enablenatreflectionhelper>yes</enablenatreflectionhelper>
<reflectiontimeout/>
<dnsserver>10.97.74.8</dnsserver>
<dnsserver>10.63.255.2</dnsserver>
</system>
<interfaces>
<wan>
<if>em0</if>
<descr>
<![CDATA[WAN]]>
</descr>
<enable/>
<spoofmac/>
<ipaddr>10.33.50.34</ipaddr>
<subnet>28</subnet>
<gateway>GW_WAN</gateway>
<ipaddrv6/>
<subnetv6/>
<gatewayv6/>
</wan>
<lan>
<enable/>
<if>em1</if>
<ipaddr>192.168.13.1</ipaddr>
<subnet>24</subnet>
<ipaddrv6/>
<subnetv6/>
<media/>
<mediaopt/>
<track6-interface>wan</track6-interface>
<track6-prefix-id>0</track6-prefix-id>
<gateway/>
<gatewayv6/>
</lan>
</interfaces>
<staticroutes>
<route>
<network>192.168.14.0/24</network>
<gateway>VLAN2014</gateway>
<descr/>
</route>
<route>
<network>192.168.19.0/24</network>
<gateway>VLAN2019</gateway>
<descr/>
</route>
<route>
<network>192.168.18.0/24</network>
<gateway>VLAN2018</gateway>
<descr/>
</route>
<route>
<network>192.168.15.0/24</network>
<gateway>VLAN2015</gateway>
<descr/>
</route>
<route>
<network>192.168.16.0/24</network>
<gateway>VLAN2016</gateway>
<descr/>
</route>
<route>
<network>192.168.17.0/24</network>
<gateway>VLAN2017</gateway>
<descr/>
</route>
<route>
<network>192.168.20.0/24</network>
<gateway>VLAN2020</gateway>
<descr/>
</route>
<route>
<network>10.33.50.160/28</network>
<gateway>VLAN2066</gateway>
<descr>
<![CDATA[Route to Vendor Net]]>
</descr>
</route>
</staticroutes>
<dhcpd>
<lan>
<enable/>
<range>
<from>192.168.13.100</from>
<to>192.168.13.150</to>
</range>
<failover_peerip/>
<dhcpleaseinlocaltime/>
<defaultleasetime/>
<maxleasetime/>
<netmask/>
<dnsserver>192.168.19.10</dnsserver>
<gateway/>
<domain>acmefinancial.com</domain>
<domainsearchlist>acmefinancial.com</domainsearchlist>
<ddnsdomain/>
<ddnsdomainprimary/>
<ddnsdomainkeyname/>
<ddnsdomainkey/>
<mac_allow/>
<mac_deny/>
<tftp/>
<ldap/>
<nextserver/>
<filename/>
<filename32/>
<filename64/>
<rootpath/>
<numberoptions/>
</lan>
<opt1>
<enable/>
<range>
<from>192.168.14.100</from>
<to>192.168.14.150</to>
</range>
<dhcpleaseinlocaltime/>
</opt1>
<opt2>
<enable/>
<range>
<from>192.168.15.100</from>
<to>192.168.15.150</to>
</range>
<dhcpleaseinlocaltime/>
</opt2>
<opt3>
<enable/>
<range>
<from>192.168.16.100</from>
<to>192.168.16.150</to>
</range>
<dhcpleaseinlocaltime/>
</opt3>
</dhcpd>
<snmpd>
<syslocation/>
<syscontact/>
<rocommunity>public</rocommunity>
</snmpd>
<diag>
<ipv6nat>
<ipaddr/>
</ipv6nat>
</diag>
<bridge/>
<syslog/>
<nat>
<outbound>
<mode>automatic</mode>
</outbound>
<onetoone>
<external>10.33.50.44</external>
<descr>
<![CDATA[mapping to 2020 pfsense firewall ]]>
</descr>
<interface>wan</interface>
<source>
<address>192.168.13.20</address>
</source>
<destination>
<any/>
</destination>
</onetoone>
<onetoone>
<external>10.33.50.42</external>
<descr>
<![CDATA[Mapping to Pfsense firewall]]>
</descr>
<interface>wan</interface>
<source>
<address>192.168.13.17</address>
</source>
<destination>
<any/>
</destination>
</onetoone>
<onetoone>
<external>10.33.50.35</external>
<descr>
<![CDATA[Mapping to Splunk]]>
</descr>
<interface>wan</interface>
<source>
<address>192.168.17.11</address>
</source>
<destination>
<any/>
</destination>
</onetoone>
<onetoone>
<external>10.33.50.41</external>
<descr>
<![CDATA[Mapping to Pfsense firewall]]>
</descr>
<interface>wan</interface>
<source>
<address>192.168.19.11</address>
</source>
<destination>
<any/>
</destination>
</onetoone>
<onetoone>
<external>10.33.50.36</external>
<descr>
<![CDATA[Mapping to Hytrust ESXi Server]]>
</descr>
<interface>wan</interface>
<source>
<address>192.168.20.12</address>
</source>
<destination>
<any/>
</destination>
</onetoone>
<onetoone>
<external>10.33.50.37</external>
<descr>
<![CDATA[NAT Mapping to RadiantOne VDS]]>
</descr>
<interface>wan</interface>
<source>
<address>192.168.14.11</address>
</source>
<destination>
<any/>
</destination>
</onetoone>
<onetoone>
<external>10.33.50.38</external>
<descr>
<![CDATA[NAT Mapping to Hytrust CloudControl VM]]>
</descr>
<interface>wan</interface>
<source>
<address>192.168.20.11</address>
</source>
<destination>
<any/>
</destination>
</onetoone>
<onetoone>
<external>10.33.50.40</external>
<descr>
<![CDATA[Mapping to ActiveDirectory]]>
</descr>
<interface>wan</interface>
<source>
<address>192.168.19.10</address>
</source>
<destination>
<any/>
</destination>
</onetoone>
<onetoone>
<external>10.33.50.43</external>
<descr>
<![CDATA[VIP for ConsoleWorks -- Mapping to Internal Address]]>
</descr>
<interface>wan</interface>
<source>
<address>192.168.17.11</address>
</source>
<destination>
<any/>
</destination>
</onetoone>
<onetoone>
<external>10.33.50.45</external>
<descr>
<![CDATA[VIP for CentOSToAD-- Mapping to Internal Address]]>
</descr>
<interface>wan</interface>
<source>
<address>192.168.19.30</address>
</source>
<destination>
<any/>
</destination>
</onetoone>
<onetoone>
<external>10.33.50.46</external>
<descr>
<![CDATA[AlertEnterprise Enterprise Guardian]]>
</descr>
<interface>wan</interface>
<source>
<address>192.168.17.114</address>
</source>
<destination>
<any/>
</destination>
</onetoone>
<rule>
<source>
<any/>
</source>
<destination>
<network>wanip</network>
<port>1322</port>
</destination>
<protocol>tcp</protocol>
<target>192.168.13.130</target>
<local-port>80</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Mapping to pfsense 192.168.13.130]]>
</descr>
<associated-rule-id>nat_581795efbc2944.51341500</associated-rule-id>
<created>
<time>1477940719</time>
<username>admin@192.168.13.139</username>
</created>
<updated>
<time>1477940861</time>
<username>admin@192.168.13.139</username>
</updated>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.41</address>
<port>80</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.19.11</target>
<local-port>80</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Port forward to openldap; Add /phpldapadmin to address]]>
</descr>
<associated-rule-id>nat_57bf0c96d083f4.07194849</associated-rule-id>
<created>
<time>1472138390</time>
<username>admin@10.97.67.137</username>
</created>
<updated>
<time>1473431620</time>
<username>admin@10.97.67.134</username>
</updated>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.41</address>
<port>22</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.19.11</target>
<local-port>22</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Port forward to openldap; ]]>
</descr>
<associated-rule-id>nat_57f555406f2de3.01889708</associated-rule-id>
<created>
<time>1475695936</time>
<username>admin@10.97.67.145</username>
</created>
<updated>
<time>1475695966</time>
<username>admin@10.97.67.145</username>
</updated>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.35</address>
<port>8000</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.17.10</target>
<local-port>8000</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Splunk port 8000 Web Interface]]>
</descr>
<associated-rule-id>nat_57d825ba865df6.65796295</associated-rule-id>
<created>
<time>1473783226</time>
<username>admin@10.97.67.152</username>
</created>
<updated>
<time>1473785552</time>
<username>admin@10.97.67.152</username>
</updated>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.35</address>
<port>22</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.17.10</target>
<local-port>22</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Splunk SSH ]]>
</descr>
<associated-rule-id>nat_582ef78ed63d23.63868026</associated-rule-id>
<updated>
<time>1479473038</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1479473038</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.42</address>
<port>1314</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.13.14</target>
<local-port>80</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Port Forward to 192.168.13.14 Pf]]>
</descr>
<associated-rule-id>nat_57c01545c247f0.43308393</associated-rule-id>
<updated>
<time>1472206149</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1472206149</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.42</address>
<port>1315</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.13.15</target>
<local-port>80</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Port Forward to 192.168.13.15 Pf]]>
</descr>
<associated-rule-id>nat_57c0163d6e2de9.62906352</associated-rule-id>
<updated>
<time>1472206397</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1472206397</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.42</address>
<port>1316</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.13.16</target>
<local-port>80</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Port Forward to 192.168.13.16 Pf]]>
</descr>
<associated-rule-id>nat_57c01682da98c4.72334719</associated-rule-id>
<updated>
<time>1472206466</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1472206466</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.42</address>
<port>1317</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.13.17</target>
<local-port>80</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Port Forward to 192.168.13.17 Pf]]>
</descr>
<associated-rule-id>nat_57c01787b4e891.75909166</associated-rule-id>
<updated>
<time>1472206727</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1472206727</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.42</address>
<port>1318</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.13.18</target>
<local-port>80</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Port Forward to 192.168.13.18 Pf]]>
</descr>
<associated-rule-id>nat_57c017be3dffa1.16882401</associated-rule-id>
<updated>
<time>1472206782</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1472206782</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.42</address>
<port>1319</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.13.19</target>
<local-port>80</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Port Forward to 192.168.13.19 Pf]]>
</descr>
<associated-rule-id>nat_57c017e1e48d65.86612217</associated-rule-id>
<updated>
<time>1472206817</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1472206817</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.42</address>
<port>1320</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.13.20</target>
<local-port>80</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Port Forward to 192.168.13.20 Pf]]>
</descr>
<associated-rule-id>nat_57c0187fd4a074.12397754</associated-rule-id>
<created>
<time>1472206975</time>
<username>admin@10.97.67.135</username>
</created>
<updated>
<time>1477940348</time>
<username>admin@192.168.13.139</username>
</updated>
</rule>
<rule>
<source>
<any/>
</source>
<destination>
<address>10.33.50.42</address>
<port>2006</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.20.6</target>
<local-port>443</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Port Forward to Hytrust Cloud Control 192.168.20.6]]>
</descr>
<associated-rule-id>nat_585ab274d8bce0.68941358</associated-rule-id>
<updated>
<time>1482338932</time>
<username>admin@10.97.67.139</username>
</updated>
<created>
<time>1482338932</time>
<username>admin@10.97.67.139</username>
</created>
</rule>
<separator/>
</nat>
<filter>
<rule>
<id/>
<tracker>1483547179</tracker>
<type>pass</type>
<interface>enc0</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow IPSEC Traffic in both directions to pass]]>
</descr>
<updated>
<time>1483547179</time>
<username>admin@10.97.67.165</username>
</updated>
<created>
<time>1483547179</time>
<username>admin@10.97.67.165</username>
</created>
</rule>
<rule>
<id/>
<tracker>1481038469</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<address>192.168.14.111</address>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow Radiant (192.168.14.111) to go anywhere -LAN]]>
</descr>
<updated>
<time>1481038469</time>
<username>admin@10.97.67.155</username>
</updated>
<created>
<time>1481038469</time>
<username>admin@10.97.67.155</username>
</created>
</rule>
<rule>
<id/>
<tracker>1481134883</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<address>192.168.13.135</address>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow CA.acmefinancial to go anywhere]]>
</descr>
<updated>
<time>1481134883</time>
<username>admin@10.97.67.146</username>
</updated>
<created>
<time>1481134883</time>
<username>admin@10.97.67.146</username>
</created>
</rule>
<rule>
<id/>
<tracker>1481038517</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<address>192.168.17.100</address>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow Radiant (192.168.17.100) to go anywhere -LAN]]>
</descr>
<updated>
<time>1481038517</time>
<username>admin@10.97.67.155</username>
</updated>
<created>
<time>1481038517</time>
<username>admin@10.97.67.155</username>
</created>
</rule>
<rule>
<id/>
<tracker>1478010422</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1478010422</time>
<username>admin@10.97.66.18</username>
</updated>
<created>
<time>1478010422</time>
<username>admin@10.97.66.18</username>
</created>
</rule>
<rule>
<id/>
<tracker>1480540664</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow all LAN traffic to go to anywhere]]>
</descr>
<updated>
<time>1480540664</time>
<username>admin@10.97.67.140</username>
</updated>
<created>
<time>1480540664</time>
<username>admin@10.97.67.140</username>
</created>
</rule>
<rule>
<id/>
<tracker>1472208251</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<address>192.168.0.0/16</address>
</source>
<destination>
<address>192.168.0.0/16</address>
</destination>
<descr>
<![CDATA[Allow traffic going from local subnet to local subne]]>
</descr>
<updated>
<time>1472208251</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1472208251</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1472216936</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<address>192.168.0.0/16</address>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow traffic going from local subnet to anywhere]]>
</descr>
<updated>
<time>1472216936</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1472216936</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1476720725</tracker>
<type>pass</type>
<interface>enc0</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow All traffic sourced from Tunnel to Anywhere o]]>
</descr>
<updated>
<time>1476720725</time>
<username>admin@10.97.67.137</username>
</updated>
<created>
<time>1476720725</time>
<username>admin@10.97.67.137</username>
</created>
</rule>
<rule>
<id/>
<tracker>1471551236</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow all TCP/UDP Traffic sourced from WAN interface]]>
</descr>
<updated>
<time>1471551236</time>
<username>admin@10.97.67.136</username>
</updated>
<created>
<time>1471551236</time>
<username>admin@10.97.67.136</username>
</created>
</rule>
<rule>
<id/>
<tracker>1470759134</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>(self)</network>
</destination>
<descr>
<![CDATA[Rule to allow connection to firewall -can be tighten]]>
</descr>
<updated>
<time>1470759134</time>
<username>admin@192.168.13.135</username>
</updated>
<created>
<time>1470759134</time>
<username>admin@192.168.13.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1461788221</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1461788221</time>
<username>admin@192.168.1.2</username>
</updated>
<created>
<time>1461788221</time>
<username>admin@192.168.1.2</username>
</created>
</rule>
<rule>
<id/>
<tracker>1465934823</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>icmp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Easy Rule: Passed from Firewall Log View]]>
</descr>
<created>
<time>1465934786</time>
<username>Easy Rule</username>
</created>
<updated>
<time>1465934839</time>
<username>admin@192.168.13.101</username>
</updated>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.19.11</address>
<port>80</port>
</destination>
<descr>
<![CDATA[NAT Port forward to openldap; Add /phpldapadmin to address]]>
</descr>
<associated-rule-id>nat_57bf0c96d083f4.07194849</associated-rule-id>
<tracker>1472138390</tracker>
<created>
<time>1472138390</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.13.14</address>
<port>80</port>
</destination>
<descr>
<![CDATA[NAT Port Forward to 192.168.13.14 Pf]]>
</descr>
<associated-rule-id>nat_57c01545c247f0.43308393</associated-rule-id>
<tracker>1472206149</tracker>
<created>
<time>1472206149</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.13.15</address>
<port>80</port>
</destination>
<descr>
<![CDATA[NAT Port Forward to 192.168.13.15 Pf]]>
</descr>
<associated-rule-id>nat_57c0163d6e2de9.62906352</associated-rule-id>
<tracker>1472206397</tracker>
<created>
<time>1472206397</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.13.16</address>
<port>80</port>
</destination>
<descr>
<![CDATA[NAT Port Forward to 192.168.13.16 Pf]]>
</descr>
<associated-rule-id>nat_57c01682da98c4.72334719</associated-rule-id>
<tracker>1472206466</tracker>
<created>
<time>1472206466</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.13.17</address>
<port>80</port>
</destination>
<descr>
<![CDATA[NAT Port Forward to 192.168.13.17 Pf]]>
</descr>
<associated-rule-id>nat_57c01787b4e891.75909166</associated-rule-id>
<tracker>1472206727</tracker>
<created>
<time>1472206727</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.13.18</address>
<port>80</port>
</destination>
<descr>
<![CDATA[NAT Port Forward to 192.168.13.18 Pf]]>
</descr>
<associated-rule-id>nat_57c017be3dffa1.16882401</associated-rule-id>
<tracker>1472206782</tracker>
<created>
<time>1472206782</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.13.19</address>
<port>80</port>
</destination>
<descr>
<![CDATA[NAT Port Forward to 192.168.13.19 Pf]]>
</descr>
<associated-rule-id>nat_57c017e1e48d65.86612217</associated-rule-id>
<tracker>1472206817</tracker>
<created>
<time>1472206817</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.13.20</address>
<port>80</port>
</destination>
<descr>
<![CDATA[NAT Port Forward to 192.168.13.20 Pf]]>
</descr>
<associated-rule-id>nat_57c0187fd4a074.12397754</associated-rule-id>
<tracker>1472206975</tracker>
<created>
<time>1472206975</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.17.10</address>
<port>8000</port>
</destination>
<descr>
<![CDATA[NAT Splunk port 8000 Web Interface]]>
</descr>
<associated-rule-id>nat_57d825ba865df6.65796295</associated-rule-id>
<tracker>1473783226</tracker>
<created>
<time>1473783226</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.19.11</address>
<port>22</port>
</destination>
<descr>
<![CDATA[NAT Port forward to openldap; ]]>
</descr>
<associated-rule-id>nat_57f555406f2de3.01889708</associated-rule-id>
<tracker>1475695936</tracker>
<created>
<time>1475695936</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp</protocol>
<destination>
<address>192.168.13.130</address>
<port>80</port>
</destination>
<descr>
<![CDATA[NAT Mapping to pfsense 192.168.13.130]]>
</descr>
<associated-rule-id>nat_581795efbc2944.51341500</associated-rule-id>
<tracker>1477940719</tracker>
<created>
<time>1477940719</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.17.10</address>
<port>22</port>
</destination>
<descr>
<![CDATA[NAT Splunk SSH ]]>
</descr>
<associated-rule-id>nat_582ef78ed63d23.63868026</associated-rule-id>
<tracker>1479473038</tracker>
<created>
<time>1479473038</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.20.6</address>
<port>443</port>
</destination>
<descr>
<![CDATA[NAT Port Forward to Hytrust Cloud Control 192.168.20.6]]>
</descr>
<associated-rule-id>nat_585ab274d8bce0.68941358</associated-rule-id>
<tracker>1482338932</tracker>
<created>
<time>1482338932</time>
<username>NAT Port Forward</username>
</created>
</rule>
<rule>
<id/>
<tracker>1480540738</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow all LAN traffic to go to anywhere]]>
</descr>
<updated>
<time>1480540738</time>
<username>admin@10.97.67.140</username>
</updated>
<created>
<time>1480540738</time>
<username>admin@10.97.67.140</username>
</created>
</rule>
<rule>
<id/>
<tracker>1465934857</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>icmp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1465934857</time>
<username>admin@192.168.13.101</username>
</updated>
<created>
<time>1465934857</time>
<username>admin@192.168.13.101</username>
</created>
</rule>
<rule>
<type>pass</type>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Default allow LAN to any rule]]>
</descr>
<interface>lan</interface>
<tracker>0100000101</tracker>
<source>
<network>lan</network>
</source>
<destination>
<any/>
</destination>
</rule>
<rule>
<type>pass</type>
<ipprotocol>inet6</ipprotocol>
<descr>
<![CDATA[Default allow LAN IPv6 to any rule]]>
</descr>
<interface>lan</interface>
<tracker>0100000102</tracker>
<source>
<network>lan</network>
</source>
<destination>
<any/>
</destination>
</rule>
<rule>
<id/>
<tracker>1476720530</tracker>
<type>pass</type>
<interface>enc0</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow All traffic sourced from Tunnel to Anywhere o]]>
</descr>
<created>
<time>1476720530</time>
<username>admin@10.97.67.137</username>
</created>
<updated>
<time>1476720628</time>
<username>admin@10.97.67.137</username>
</updated>
</rule>
<separator>
<lan/>
<wan/>
<floatingrules/>
<enc0/>
</separator>
<bypassstaticroutes>yes</bypassstaticroutes>
</filter>
<shaper/>
<ipsec>
<phase1>
<ikeid>1</ikeid>
<iketype>ikev1</iketype>
<mode>main</mode>
<interface>wan</interface>
<remote-gateway>174.47.13.99</remote-gateway>
<protocol>inet</protocol>
<myid_type>myaddress</myid_type>
<myid_data/>
<peerid_type>peeraddress</peerid_type>
<peerid_data/>
<encryption-algorithm>
<name>aes</name>
<keylen>256</keylen>
</encryption-algorithm>
<hash-algorithm>sha1</hash-algorithm>
<dhgroup>2</dhgroup>
<lifetime>28800</lifetime>
<pre-shared-key>78J%3AkmP*Krr294xYE=v@</pre-shared-key>
<private-key/>
<certref/>
<caref/>
<authentication_method>pre_shared_key</authentication_method>
<descr>
<![CDATA[IPSEC IKEv1 Tunnel to Vanguard's Firewall Public IP address]]>
</descr>
<nat_traversal>force</nat_traversal>
<mobike>off</mobike>
<dpd_delay>10</dpd_delay>
<dpd_maxfail>5</dpd_maxfail>
</phase1>
<client/>
<phase2>
<ikeid>1</ikeid>
<uniqid>5804f45c4f196</uniqid>
<mode>tunnel</mode>
<reqid>1</reqid>
<localid>
<type>network</type>
<address>192.168.19.0</address>
<netbits>24</netbits>
</localid>
<remoteid>
<type>network</type>
<address>172.17.212.0</address>
<netbits>24</netbits>
</remoteid>
<protocol>esp</protocol>
<encryption-algorithm-option>
<name>aes</name>
<keylen>256</keylen>
</encryption-algorithm-option>
<hash-algorithm-option>hmac_sha1</hash-algorithm-option>
<pfsgroup>0</pfsgroup>
<lifetime>3600</lifetime>
<pinghost/>
<descr>
<![CDATA[Phase 2 IPSEC Tunnel to Vanguard]]>
</descr>
</phase2>
<phase2>
<ikeid>1</ikeid>
<uniqid>586d5ecf7f516</uniqid>
<mode>tunnel</mode>
<reqid>2</reqid>
<localid>
<type>network</type>
<address>192.168.17.0</address>
<netbits>24</netbits>
</localid>
<remoteid>
<type>network</type>
<address>172.17.212.0</address>
<netbits>24</netbits>
</remoteid>
<protocol>esp</protocol>
<encryption-algorithm-option>
<name>aes</name>
<keylen>256</keylen>
</encryption-algorithm-option>
<hash-algorithm-option>hmac_sha1</hash-algorithm-option>
<pfsgroup>0</pfsgroup>
<lifetime>3600</lifetime>
<pinghost/>
<descr>
<![CDATA[Phase 2 IPSEC Tunnel to Vanguard]]>
</descr>
</phase2>
<phase2>
<ikeid>1</ikeid>
<uniqid>586d5eeb02957</uniqid>
<mode>tunnel</mode>
<reqid>3</reqid>
<localid>
<type>network</type>
<address>192.168.13.0</address>
<netbits>24</netbits>
</localid>
<remoteid>
<type>network</type>
<address>172.17.212.0</address>
<netbits>24</netbits>
</remoteid>
<protocol>esp</protocol>
<encryption-algorithm-option>
<name>aes</name>
<keylen>256</keylen>
</encryption-algorithm-option>
<hash-algorithm-option>hmac_sha1</hash-algorithm-option>
<pfsgroup>0</pfsgroup>
<lifetime>3600</lifetime>
<pinghost/>
<descr>
<![CDATA[Phase 2 IPSEC Tunnel to Vanguard]]>
</descr>
</phase2>
<phase2>
<ikeid>1</ikeid>
<uniqid>586d5f54943b4</uniqid>
<mode>tunnel</mode>
<reqid>4</reqid>
<localid>
<type>network</type>
<address>192.168.14.0</address>
<netbits>24</netbits>
</localid>
<remoteid>
<type>network</type>
<address>172.17.212.0</address>
<netbits>24</netbits>
</remoteid>
<protocol>esp</protocol>
<encryption-algorithm-option>
<name>aes</name>
<keylen>256</keylen>
</encryption-algorithm-option>
<hash-algorithm-option>hmac_sha1</hash-algorithm-option>
<pfsgroup>0</pfsgroup>
<lifetime>3600</lifetime>
<pinghost/>
<descr>
<![CDATA[Phase 2 IPSEC Tunnel to Vanguard]]>
</descr>
</phase2>
</ipsec>
<aliases/>
<proxyarp/>
<cron>
<item>
<minute>1,31</minute>
<hour>0-5</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 adjkerntz -a</command>
</item>
<item>
<minute>1</minute>
<hour>3</hour>
<mday>1</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.update_bogons.sh</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 sshlockout</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 webConfiguratorlockout</command>
</item>
<item>
<minute>1</minute>
<hour>1</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.dyndns.update</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 virusprot</command>
</item>
<item>
<minute>30</minute>
<hour>12</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.update_urltables</command>
</item>
</cron>
<wol/>
<rrd>
<enable/>
</rrd>
<load_balancer>
<monitor_type>
<name>ICMP</name>
<type>icmp</type>
<descr>
<![CDATA[ICMP]]>
</descr>
<options/>
</monitor_type>
<monitor_type>
<name>TCP</name>
<type>tcp</type>
<descr>
<![CDATA[Generic TCP]]>
</descr>
<options/>
</monitor_type>
<monitor_type>
<name>HTTP</name>
<type>http</type>
<descr>
<![CDATA[Generic HTTP]]>
</descr>
<options>
<path>/</path>
<host/>
<code>200</code>
</options>
</monitor_type>
<monitor_type>
<name>HTTPS</name>
<type>https</type>
<descr>
<![CDATA[Generic HTTPS]]>
</descr>
<options>
<path>/</path>
<host/>
<code>200</code>
</options>
</monitor_type>
<monitor_type>
<name>SMTP</name>
<type>send</type>
<descr>
<![CDATA[Generic SMTP]]>
</descr>
<options>
<send/>
<expect>220 *</expect>
</options>
</monitor_type>
</load_balancer>
<widgets>
<sequence>system_information:col1:open,gateways:col1:open,interfaces:col2:open</sequence>
</widgets>
<openvpn/>
<dnshaper/>
<unbound>
<enable/>
<dnssec/>
<active_interface/>
<outgoing_interface/>
<custom_options/>
<hideidentity/>
<hideversion/>
<dnssecstripped/>
</unbound>
<dhcpdv6>
<lan>
<range>
<from>::1000</from>
<to>::2000</to>
</range>
<ramode>assist</ramode>
<rapriority>medium</rapriority>
</lan>
</dhcpdv6>
<cert>
<refid>5720a0502b277</refid>
<descr>
<![CDATA[webConfigurator default (5720a0502b277)]]>
</descr>
<type>server</type>
<crt>LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUZiVENDQkZXZ0F3SUJBZ0lCQURBTkJna3Foa2lHOXcwQkFRc0ZBRENCdERFTE1Ba0dBMVVFQmhNQ1ZWTXgKRGpBTUJnTlZCQWdUQlZOMFlYUmxNUkV3RHdZRFZRUUhFd2hNYjJOaGJHbDBlVEU0TURZR0ExVUVDaE12Y0daVApaVzV6WlNCM1pXSkRiMjVtYVdkMWNtRjBiM0lnVTJWc1ppMVRhV2R1WldRZ1EyVnlkR2xtYVdOaGRHVXhLREFtCkJna3Foa2lHOXcwQkNRRVdHV0ZrYldsdVFIQm1VMlZ1YzJVdWJHOWpZV3hrYjIxaGFXNHhIakFjQmdOVkJBTVQKRlhCbVUyVnVjMlV0TlRjeU1HRXdOVEF5WWpJM056QWVGdzB4TmpBME1qY3hNVEU1TkRSYUZ3MHlNVEV3TVRneApNVEU1TkRSYU1JRzBNUXN3Q1FZRFZRUUdFd0pWVXpFT01Bd0dBMVVFQ0JNRlUzUmhkR1V4RVRBUEJnTlZCQWNUCkNFeHZZMkZzYVhSNU1UZ3dOZ1lEVlFRS0V5OXdabE5sYm5ObElIZGxZa052Ym1acFozVnlZWFJ2Y2lCVFpXeG0KTFZOcFoyNWxaQ0JEWlhKMGFXWnBZMkYwWlRFb01DWUdDU3FHU0liM0RRRUpBUllaWVdSdGFXNUFjR1pUWlc1egpaUzVzYjJOaGJHUnZiV0ZwYmpFZU1Cd0dBMVVFQXhNVmNHWlRaVzV6WlMwMU56SXdZVEExTURKaU1qYzNNSUlCCklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUF0L085aDlnT2R5R20yTnQ4R3dpUmw1bDAKVmZ2NGJsQ2NWcGJNYXFMUE1aVzNMdGhDODBHU0dhZnJENWdqcTRwZkNNMHlzbEFPaVlZK1hDYjdNa2o0dmtTMgpmbzl4emNyaDUrNVlaYlBHeXR1a2lsZWR4bjFWeFl6SllzYXZKdnlKb1lRMCtNTkx0dkFjYnRhTUFoZjh1ZkRFClhrclNVQ0N5YTFrbEYxNWJGZmcyUGE0eGRvMk9PNUJ5RzBrV0NKU2o4K1R1WnVkUFRJTkx3QUZnd1E5K1BQZkwKVTQxMFBVb3FFbWEwdzU4Q1RZKzZhZEFiUEhjWGc5SFA0NFQybFNIQ2M1cUp5UTdlK3IyaFZ0N29ENloxQmdCUApyeXd1SEZwd3J1LytYWExieEcrcDdwYXI0aHR0UFRDcml1NmFqQVVTNmpvN05kOElQNWpzZ1kzR0h2ZjhzUUlECkFRQUJvNElCaGpDQ0FZSXdDUVlEVlIwVEJBSXdBREFSQmdsZ2hrZ0JodmhDQVFFRUJBTUNCa0F3TXdZSllJWkkKQVliNFFnRU5CQ1lXSkU5d1pXNVRVMHdnUjJWdVpYSmhkR1ZrSUZObGNuWmxjaUJEWlhKMGFXWnBZMkYwWlRBZApCZ05WSFE0RUZnUVU3K1lLRmNpOFFVSGhTZ0xEdjhFQ3NjQ0p3QUl3Z2VFR0ExVWRJd1NCMlRDQjFvQVU3K1lLCkZjaThRVUhoU2dMRHY4RUNzY0NKd0FLaGdicWtnYmN3Z2JReEN6QUpCZ05WQkFZVEFsVlRNUTR3REFZRFZRUUkKRXdWVGRHRjBaVEVSTUE4R0ExVUVCeE1JVEc5allXeHBkSGt4T0RBMkJnTlZCQW9UTDNCbVUyVnVjMlVnZDJWaQpRMjl1Wm1sbmRYSmhkRzl5SUZObGJHWXRVMmxuYm1Wa0lFTmxjblJwWm1sallYUmxNU2d3SmdZSktvWklodmNOCkFRa0JGaGxoWkcxcGJrQndabE5sYm5ObExteHZZMkZzWkc5dFlXbHVNUjR3SEFZRFZRUURFeFZ3WmxObGJuTmwKTFRVM01qQmhNRFV3TW1JeU56ZUNBUUF3SFFZRFZSMGxCQll3RkFZSUt3WUJCUVVIQXdFR0NDc0dBUVVGQ0FJQwpNQXNHQTFVZER3UUVBd0lGb0RBTkJna3Foa2lHOXcwQkFRc0ZBQU9DQVFFQXJxZFpQdXd2MVZuUC82NmJDWFJ5CkVmaW1LRWlPcmtNaTB5M09PWGtzWEs1cEM2dTd6Ukl3WjEvRjYyRUp3ODlUOWx4Y01ZelZOTm5Idlg0bXFPRUcKUWJhRU42NEkxOHFud3ZmS2JrREZvRThMR1hSdzBkMnAyTGVmYTd4YTIvSGNHc0xHTktPbkJxb3N4ejUrQ1B3ZwpWeVRaTS9wV3p3aDdQRGc4bGdrcVc3dStlb01DNDJIbVJkOURCTmlzdFJ4RVlNMkFLQkFsZG1LYStvRUY1VUwwCm43aXpvNlZ4dHJWMTJvTTdySllRQ05kY00xZkVSeUwvb3ZkUnVpa0F5Wm1VVnFUL1dDZGo3dDdIVG9ob0RFYzEKSklkOVpPSmR2QmZLVU1sUWlELyswSVpTalFXRDczWkdsaEhTK2tOeWc1aDJhUjUwYjh3Wm9zQnNjSUZDa0pFbgp0UT09Ci0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K</crt>
<prv>LS0tLS1CRUdJTiBQUklWQVRFIEtFWS0tLS0tCk1JSUV2Z0lCQURBTkJna3Foa2lHOXcwQkFRRUZBQVNDQktnd2dnU2tBZ0VBQW9JQkFRQzM4NzJIMkE1M0lhYlkKMjN3YkNKR1htWFJWKy9odVVKeFdsc3hxb3M4eGxiY3UyRUx6UVpJWnArc1BtQ09yaWw4SXpUS3lVQTZKaGo1YwpKdnN5U1BpK1JMWitqM0hOeXVIbjdsaGxzOGJLMjZTS1Y1M0dmVlhGak1saXhxOG0vSW1oaERUNHcwdTI4Qnh1CjFvd0NGL3k1OE1SZVN0SlFJTEpyV1NVWFhsc1YrRFk5cmpGMmpZNDdrSEliU1JZSWxLUHo1TzVtNTA5TWcwdkEKQVdEQkQzNDg5OHRUalhROVNpb1NaclREbndKTmo3cHAwQnM4ZHhlRDBjL2poUGFWSWNKem1vbkpEdDc2dmFGVwozdWdQcG5VR0FFK3ZMQzRjV25DdTcvNWRjdHZFYjZudWxxdmlHMjA5TUt1SzdwcU1CUkxxT2pzMTN3Zy9tT3lCCmpjWWU5L3l4QWdNQkFBRUNnZ0VCQUpRRFpxU3duMnNTUTh0SVNBTUVrUW0zcXhrb3BzdzB4cWNScmFlOEd4VmQKejBpOU1KbkZVQWFleTQvL3JldndhZW1PR3RYSmZ2ai9jSnY3cmJIWGIzYkJtVW9hcDhxY0RjdnVSMmlHRUZYWQpCL3hjNVpINTlaTUFabWE1VWVQLzNjcDlzNVhhcHNpclNXV1I4cFFZc3Z6Mmt6ci8zMXdrQXd4SGJZWHhJVDk1CjNLRmk4VTZUM1hnU1c2eFowZHp1ZnlPUzAvbXlmNU5YLzVoRklPNmFDc0xlUjZ4N1RZa2FDQU9FYlViT29qUXkKc09XeWphbEtTUWZ3WEdzdVM0bXdyR2hMZ0NRYlB2MnE5V0Nia0VMNEZUZmRzRlZXcHBRNGlZVWtwNzhMY1FPMgpsSGR5cTJxTmJsNDIwa3h5M2FnZlF2YTVqYUgyRm5LdkExR2YxY05hcGRVQ2dZRUE0NzNMUWoxcExLSmRZN2JxCmtMU3NVT0ZhTUZlZG1xU2ttbzh3QjlpMXhzbElLQUd0M3U4dTdMZlZtU2lybnMwVVBTMHRVUDRyQXMzVFJocEgKU2Z4VXVsbGVGaktjZk9xRE11TTBCOGttbFJnUFRmVHVPaGNwMGVkamQwK1E5Y2VlY25kaFp3UEl6TUc3TWRTSApKOG5yU2t5TFdMdWUxUVJNZHNhbmNBRDhVYThDZ1lFQXpzYjYzbzRBSHlYNjZkcEJ6TGlzYzZxS2d2ZG4xazhVCm02N3RuK2M3NkVhSEtZTlk0RjdhS0dFSk1yeU0yQTJTelAzdm03Rmk4eGRtblgrSXd5cUx5T1VwSnZXQ012TVIKRDFpNWVFTVVoZVo2OUpOK0I3SmZ2RjYrK2tHa1NHOGxaN0VLY21Uc1kzRVJxOURsSk94Nk1ROFEwMDNsTHVtQQpJZm1DWlpRSUQ1OENnWUJjamFOdk5obnFJOG9rWGhBUjR2c3NtNGpWb0tYU1ZScjRIVHo5MDFwOGdReXNCWkt0CnlUS2V6VThuUVZvTjNYWmVMbC8rVEcwYVpKOTZHKy9nNTRWZmZqWTRlelVScHhUT3QzdEx0cm5SV2NmT2ZMM2MKS2RHN0ZuaGI0cUFjNHBWSUc3QWY5Mi9CbHZJR25FS1pMdnhLWTdVMXlIb1NRLzczUG1DSnFqemd6UUtCZ1FDZgpJQjE3RzRnWWNGL3hpdGJNTnVudmNUUjZxTzR0ekZtdG5TYWN3WlFtb2UvdUVIaGE0bU84WTBCeTNRcitVU1BCCndVR2RiUnNhdTgxcU12VUtURG1hZGsvKy9Ud2UvVk1Kbmx2TW9zS3VjTG42Y1c2eGVhR1hFc3FoUjlhbkwzRjMKcEpUSGg4Y3FsNTdqdkRRN0FBamdyQmxrb3pOVnNMZThiWWpkcHRlMVBRS0JnQ0xDR0R1RXNBYUxwZlRtOG44bgoyQ1h1NE52K1l3a1RlczduWjRoM3ZRODI1ZkQxbGVzVjBYdDJ1cVJqeFEvSDgxMHRGd1p3cC9uSVdycnRCZlZLClUzSThhYnpnUUtwOEwrZjVadTAxY1pZVk5TU0FIUFRHYm5jb1IzbGVPYjNLeUVXQjdsZFBHQWpOS3UwNkd5TEkKakh5TDhadEFBRXVBZ1FUOVFOVGJkQWJrCi0tLS0tRU5EIFBSSVZBVEUgS0VZLS0tLS0K</prv>
</cert>
<revision>
<time>1493217875</time>
<description>
<![CDATA[admin@10.97.67.148: /firewall_nat_1to1_edit.php made unknown change]]>
</description>
<username>admin@10.97.67.148</username>
</revision>
<gateways>
<gateway_item>
<interface>wan</interface>
<gateway>10.33.50.33</gateway>
<name>GW_WAN</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<interval/>
<descr>
<![CDATA[Interface wan Gateway]]>
</descr>
<defaultgw/>
</gateway_item>
<gateway_item>
<interface>lan</interface>
<gateway>192.168.13.14</gateway>
<name>VLAN2014</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr/>
</gateway_item>
<gateway_item>
<interface>lan</interface>
<gateway>192.168.13.19</gateway>
<name>VLAN2019</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[VLAN2019]]>
</descr>
</gateway_item>
<gateway_item>
<interface>lan</interface>
<gateway>192.168.13.18</gateway>
<name>VLAN2018</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[VLAN2018]]>
</descr>
</gateway_item>
<gateway_item>
<interface>lan</interface>
<gateway>192.168.13.15</gateway>
<name>VLAN2015</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr/>
</gateway_item>
<gateway_item>
<interface>lan</interface>
<gateway>192.168.13.16</gateway>
<name>VLAN2016</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr/>
</gateway_item>
<gateway_item>
<interface>lan</interface>
<gateway>192.168.13.17</gateway>
<name>VLAN2017</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr/>
</gateway_item>
<gateway_item>
<interface>lan</interface>
<gateway>192.168.13.20</gateway>
<name>VLAN2020</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr/>
</gateway_item>
<gateway_item>
<interface>lan</interface>
<gateway>192.168.13.10</gateway>
<name>VLAN2066</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Gateway to Vendor Net]]>
</descr>
</gateway_item>
</gateways>
<ppps/>
<dyndnses/>
<virtualip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>576b23658af3d</uniqid>
<descr>
<![CDATA[Virtual IP for Splunk]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.35</subnet>
</vip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>5773d4c39ae54</uniqid>
<descr>
<![CDATA[Virtual IP for RadiantOne VDS]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.37</subnet>
</vip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>57a8ce7868f78</uniqid>
<descr>
<![CDATA[Virtual IP for Hytrust ESXi Server]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.36</subnet>
</vip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>57aa0a09a4d09</uniqid>
<descr>
<![CDATA[VIP for Hytrust CloudControl VM]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.38</subnet>
</vip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>57b615eac1f16</uniqid>
<descr>
<![CDATA[VIP for VCenter Server]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.39</subnet>
</vip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>57bd089e9ab62</uniqid>
<descr>
<![CDATA[VIP for ActiveDirectory]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.40</subnet>
</vip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>57bf0bbc594c5</uniqid>
<descr>
<![CDATA[VIP for OpenLDAP]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.41</subnet>
</vip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>57bf97481ae8c</uniqid>
<descr>
<![CDATA[VIP for Internal Pfsense Firewalls]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.42</subnet>
</vip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>581788c622d42</uniqid>
<descr>
<![CDATA[VIP for ConsoleWorks -- Mapping to Internal Address]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.43</subnet>
</vip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>58179833f127e</uniqid>
<descr>
<![CDATA[Testing ]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.44</subnet>
</vip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>58e410a9241f1</uniqid>
<descr>
<![CDATA[Mapping to CentOSToAD VM (test machine)]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.45</subnet>
</vip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>5900b1ef3b079</uniqid>
<descr>
<![CDATA[AlertEnterprise Enterprise Guardian]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>10.33.50.46</subnet>
</vip>
</virtualip>
</pfSense>
2.10.2. Firewall Configuration for Common Services Subnet¶
<?xml version="1.0"?>
<pfSense>
<version>15.4</version>
<lastchange/>
<theme>pfSense_ng</theme>
<system>
<optimization>normal</optimization>
<hostname>FS-ARM</hostname>
<domain>FS-ARM.gov</domain>
<group>
<name>all</name>
<description>
<![CDATA[All Users]]>
</description>
<scope>system</scope>
<gid>1998</gid>
<member>0</member>
</group>
<group>
<name>admins</name>
<description>
<![CDATA[System Administrators]]>
</description>
<scope>system</scope>
<gid>1999</gid>
<member>0</member>
<priv>page-all</priv>
</group>
<user>
<name>admin</name>
<descr>
<![CDATA[System Administrator]]>
</descr>
<scope>system</scope>
<groupname>admins</groupname>
<password>$1$dSJImFph$GvZ7.1UbuWu.Yb8etC0re.</password>
<uid>0</uid>
<priv>user-shell-access</priv>
</user>
<nextuid>2000</nextuid>
<nextgid>2000</nextgid>
<timezone>America/New_York</timezone>
<time-update-interval/>
<timeservers>10.97.74.8</timeservers>
<webgui>
<protocol>http</protocol>
<loginautocomplete/>
<ssl-certref>5720a0502b277</ssl-certref>
<dashboardcolumns>2</dashboardcolumns>
<port/>
<max_procs>2</max_procs>
<nohttpreferercheck/>
</webgui>
<disablenatreflection>yes</disablenatreflection>
<disablesegmentationoffloading/>
<disablelargereceiveoffloading/>
<ipv6allow/>
<powerd_ac_mode>hadp</powerd_ac_mode>
<powerd_battery_mode>hadp</powerd_battery_mode>
<powerd_normal_mode>hadp</powerd_normal_mode>
<bogons>
<interval>monthly</interval>
</bogons>
<language>en_US</language>
<dns1gw>GW_WAN</dns1gw>
<dns2gw>GW_WAN</dns2gw>
<dns3gw>none</dns3gw>
<dns4gw>none</dns4gw>
<dnsserver>10.97.74.8</dnsserver>
<dnsserver>10.63.255.2</dnsserver>
<maximumstates/>
<aliasesresolveinterval/>
<maximumtableentries/>
<maximumfrags/>
<reflectiontimeout/>
<serialspeed>115200</serialspeed>
<primaryconsole>serial</primaryconsole>
</system>
<interfaces>
<wan>
<if>em0</if>
<descr>
<![CDATA[WAN]]>
</descr>
<enable/>
<spoofmac/>
<ipaddr>192.168.13.19</ipaddr>
<subnet>24</subnet>
<gateway>GW_WAN_2</gateway>
<ipaddrv6/>
<subnetv6/>
<gatewayv6/>
</wan>
<lan>
<enable/>
<if>em1</if>
<ipaddr>192.168.19.1</ipaddr>
<subnet>24</subnet>
<ipaddrv6/>
<subnetv6/>
<media/>
<mediaopt/>
<track6-interface>wan</track6-interface>
<track6-prefix-id>0</track6-prefix-id>
<gateway/>
<gatewayv6/>
</lan>
</interfaces>
<staticroutes>
<route>
<network>192.168.17.0/24</network>
<gateway>GW_VLAN17</gateway>
<descr>
<![CDATA[Route to VLAN 17]]>
</descr>
</route>
</staticroutes>
<dhcpd>
<lan>
<enable/>
<range>
<from>192.168.19.100</from>
<to>192.168.19.150</to>
</range>
</lan>
<opt1>
<enable/>
<range>
<from>192.168.14.100</from>
<to>192.168.14.150</to>
</range>
</opt1>
<opt2>
<enable/>
<range>
<from>192.168.15.100</from>
<to>192.168.15.150</to>
</range>
</opt2>
<opt3>
<enable/>
<range>
<from>192.168.16.100</from>
<to>192.168.16.150</to>
</range>
</opt3>
</dhcpd>
<snmpd>
<syslocation/>
<syscontact/>
<rocommunity>public</rocommunity>
</snmpd>
<diag>
<ipv6nat>
<ipaddr/>
</ipv6nat>
</diag>
<bridge/>
<syslog/>
<nat>
<outbound>
<mode>disabled</mode>
</outbound>
</nat>
<filter>
<rule>
<id/>
<tracker>1493319263</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
</destination>
<descr>
<![CDATA[Allow Any to LAN net]]>
</descr>
<updated>
<time>1493319263</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493319263</time>
<username>admin@10.97.67.143</username>
</created>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1481038226</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<address>192.168.14.111</address>
</source>
<destination>
<any/>
</destination>
<disabled/>
<descr>
<![CDATA[Allow Radiant (192.168.14.111) in -WAN]]>
</descr>
<created>
<time>1481038226</time>
<username>admin@10.97.67.155</username>
</created>
<updated>
<time>1493311659</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1481038269</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>389</port>
</destination>
<descr>
<![CDATA[Allow LDAP traffic to AD and OpenLDAP]]>
</descr>
<created>
<time>1481038269</time>
<username>admin@10.97.67.155</username>
</created>
<updated>
<time>1493319675</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1493314739</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
<port>636</port>
</destination>
<descr>
<![CDATA[Allow Connection to LDAPS on AD and OpenLDAP]]>
</descr>
<created>
<time>1493314739</time>
<username>admin@10.97.67.143</username>
</created>
<updated>
<time>1493319543</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1472179541</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<disabled/>
<descr>
<![CDATA[Testing to see if there will be communication betwee]]>
</descr>
<created>
<time>1472179541</time>
<username>admin@192.168.13.135</username>
</created>
<updated>
<time>1493311684</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1493327079</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>icmp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
</destination>
<descr>
<![CDATA[Allow ICMP for troubleshooting]]>
</descr>
<updated>
<time>1493327079</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493327079</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493327306</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os></os>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
<port>53</port>
</destination>
<descr>
<![CDATA[Allow DNS Requests to AD]]>
</descr>
<updated>
<time>1493327306</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493327306</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493312171</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>389</port>
</destination>
<descr>
<![CDATA[Allow LDAP traffic to LAN nodes]]>
</descr>
<updated>
<time>1493312171</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493312171</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493313314</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>53</port>
</destination>
<descr>
<![CDATA[Allow DNS traffic to LAN nodes]]>
</descr>
<updated>
<time>1493313314</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493313314</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493312231</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>636</port>
</destination>
<descr>
<![CDATA[Allow LDAPs traffic to LAN nodes]]>
</descr>
<updated>
<time>1493312231</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493312231</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493311864</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>22</port>
</destination>
<descr>
<![CDATA[Allow SSH traffic to LAN nodes ]]>
</descr>
<updated>
<time>1493311864</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493311864</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493311502</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<network>lan</network>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow all LAN traffic to go to anywhere --Applied to]]>
</descr>
<updated>
<time>1493311502</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493311502</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493311408</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>wanip</network>
<port>80</port>
</destination>
<descr>
<![CDATA[Allow to Port 80 on Firewall WAN]]>
</descr>
<updated>
<time>1493311408</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493311408</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493312279</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>wanip</network>
<port>443</port>
</destination>
<descr>
<![CDATA[Allow to Port 443 on Firewall WAN]]>
</descr>
<updated>
<time>1493312279</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493312279</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493311302</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>3389</port>
</destination>
<descr>
<![CDATA[Allow RDP to LAN nodes]]>
</descr>
<updated>
<time>1493311302</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493311302</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1469127156</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<disabled/>
<descr/>
<created>
<time>1469127156</time>
<username>admin@192.168.13.132</username>
</created>
<updated>
<time>1493311628</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1480964347</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<address>192.168.14.111</address>
</source>
<destination>
<any/>
</destination>
<disabled/>
<descr>
<![CDATA[Allow Radiant (192.168.14.111) to Get Subnet 19 with]]>
</descr>
<created>
<time>1480964347</time>
<username>admin@10.97.67.144</username>
</created>
<updated>
<time>1493311596</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1480964466</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<address>192.168.17.100</address>
</source>
<destination>
<any/>
</destination>
<disabled/>
<descr>
<![CDATA[Allow Radiant (192.168.17.100) to Get Subnet 19 from]]>
</descr>
<created>
<time>1480964466</time>
<username>admin@10.97.67.144</username>
</created>
<updated>
<time>1493311572</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1465935224</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>icmp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1465935224</time>
<username>admin@192.168.18.100</username>
</updated>
<created>
<time>1465935224</time>
<username>admin@192.168.18.100</username>
</created>
</rule>
<rule>
<id/>
<tracker>1469127171</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<disabled/>
<descr/>
<created>
<time>1469127171</time>
<username>admin@192.168.13.132</username>
</created>
<updated>
<time>1493322054</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1465935241</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>icmp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1465935241</time>
<username>admin@192.168.18.100</username>
</updated>
<created>
<time>1465935241</time>
<username>admin@192.168.18.100</username>
</created>
</rule>
<rule>
<type>pass</type>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Default allow LAN to any rule]]>
</descr>
<interface>lan</interface>
<tracker>0100000101</tracker>
<source>
<network>lan</network>
</source>
<destination>
<any/>
</destination>
</rule>
<rule>
<type>pass</type>
<ipprotocol>inet6</ipprotocol>
<descr>
<![CDATA[Default allow LAN IPv6 to any rule]]>
</descr>
<interface>lan</interface>
<tracker>0100000102</tracker>
<source>
<network>lan</network>
</source>
<destination>
<any/>
</destination>
</rule>
<separator>
<wan/>
<lan/>
<floatingrules/>
</separator>
<bypassstaticroutes>yes</bypassstaticroutes>
</filter>
<shaper></shaper>
<ipsec/>
<aliases/>
<proxyarp/>
<cron>
<item>
<minute>1,31</minute>
<hour>0-5</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 adjkerntz -a</command>
</item>
<item>
<minute>1</minute>
<hour>3</hour>
<mday>1</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.update_bogons.sh</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 sshlockout</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 webConfiguratorlockout</command>
</item>
<item>
<minute>1</minute>
<hour>1</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.dyndns.update</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 virusprot</command>
</item>
<item>
<minute>30</minute>
<hour>12</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.update_urltables</command>
</item>
</cron>
<wol/>
<rrd>
<enable/>
</rrd>
<load_balancer>
<monitor_type>
<name>ICMP</name>
<type>icmp</type>
<descr>
<![CDATA[ICMP]]>
</descr>
<options/>
</monitor_type>
<monitor_type>
<name>TCP</name>
<type>tcp</type>
<descr>
<![CDATA[Generic TCP]]>
</descr>
<options/>
</monitor_type>
<monitor_type>
<name>HTTP</name>
<type>http</type>
<descr>
<![CDATA[Generic HTTP]]>
</descr>
<options>
<path>/</path>
<host/>
<code>200</code>
</options>
</monitor_type>
<monitor_type>
<name>HTTPS</name>
<type>https</type>
<descr>
<![CDATA[Generic HTTPS]]>
</descr>
<options>
<path>/</path>
<host/>
<code>200</code>
</options>
</monitor_type>
<monitor_type>
<name>SMTP</name>
<type>send</type>
<descr>
<![CDATA[Generic SMTP]]>
</descr>
<options>
<send/>
<expect>220 *</expect>
</options>
</monitor_type>
</load_balancer>
<widgets>
<sequence>system_information:col1:open,gateways:col1:open,interfaces:col2:open</sequence>
</widgets>
<openvpn/>
<dnshaper></dnshaper>
<unbound>
<enable/>
<dnssec/>
<active_interface/>
<outgoing_interface/>
<custom_options/>
<hideidentity/>
<hideversion/>
<dnssecstripped/>
</unbound>
<dhcpdv6>
<lan>
<range>
<from>::1000</from>
<to>::2000</to>
</range>
<ramode>assist</ramode>
<rapriority>medium</rapriority>
</lan>
</dhcpdv6>
<cert>
<refid>5720a0502b277</refid>
<descr>
<![CDATA[webConfigurator default (5720a0502b277)]]>
</descr>
<type>server</type>
<crt>LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUZiVENDQkZXZ0F3SUJBZ0lCQURBTkJna3Foa2lHOXcwQkFRc0ZBRENCdERFTE1Ba0dBMVVFQmhNQ1ZWTXgKRGpBTUJnTlZCQWdUQlZOMFlYUmxNUkV3RHdZRFZRUUhFd2hNYjJOaGJHbDBlVEU0TURZR0ExVUVDaE12Y0daVApaVzV6WlNCM1pXSkRiMjVtYVdkMWNtRjBiM0lnVTJWc1ppMVRhV2R1WldRZ1EyVnlkR2xtYVdOaGRHVXhLREFtCkJna3Foa2lHOXcwQkNRRVdHV0ZrYldsdVFIQm1VMlZ1YzJVdWJHOWpZV3hrYjIxaGFXNHhIakFjQmdOVkJBTVQKRlhCbVUyVnVjMlV0TlRjeU1HRXdOVEF5WWpJM056QWVGdzB4TmpBME1qY3hNVEU1TkRSYUZ3MHlNVEV3TVRneApNVEU1TkRSYU1JRzBNUXN3Q1FZRFZRUUdFd0pWVXpFT01Bd0dBMVVFQ0JNRlUzUmhkR1V4RVRBUEJnTlZCQWNUCkNFeHZZMkZzYVhSNU1UZ3dOZ1lEVlFRS0V5OXdabE5sYm5ObElIZGxZa052Ym1acFozVnlZWFJ2Y2lCVFpXeG0KTFZOcFoyNWxaQ0JEWlhKMGFXWnBZMkYwWlRFb01DWUdDU3FHU0liM0RRRUpBUllaWVdSdGFXNUFjR1pUWlc1egpaUzVzYjJOaGJHUnZiV0ZwYmpFZU1Cd0dBMVVFQXhNVmNHWlRaVzV6WlMwMU56SXdZVEExTURKaU1qYzNNSUlCCklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUF0L085aDlnT2R5R20yTnQ4R3dpUmw1bDAKVmZ2NGJsQ2NWcGJNYXFMUE1aVzNMdGhDODBHU0dhZnJENWdqcTRwZkNNMHlzbEFPaVlZK1hDYjdNa2o0dmtTMgpmbzl4emNyaDUrNVlaYlBHeXR1a2lsZWR4bjFWeFl6SllzYXZKdnlKb1lRMCtNTkx0dkFjYnRhTUFoZjh1ZkRFClhrclNVQ0N5YTFrbEYxNWJGZmcyUGE0eGRvMk9PNUJ5RzBrV0NKU2o4K1R1WnVkUFRJTkx3QUZnd1E5K1BQZkwKVTQxMFBVb3FFbWEwdzU4Q1RZKzZhZEFiUEhjWGc5SFA0NFQybFNIQ2M1cUp5UTdlK3IyaFZ0N29ENloxQmdCUApyeXd1SEZwd3J1LytYWExieEcrcDdwYXI0aHR0UFRDcml1NmFqQVVTNmpvN05kOElQNWpzZ1kzR0h2ZjhzUUlECkFRQUJvNElCaGpDQ0FZSXdDUVlEVlIwVEJBSXdBREFSQmdsZ2hrZ0JodmhDQVFFRUJBTUNCa0F3TXdZSllJWkkKQVliNFFnRU5CQ1lXSkU5d1pXNVRVMHdnUjJWdVpYSmhkR1ZrSUZObGNuWmxjaUJEWlhKMGFXWnBZMkYwWlRBZApCZ05WSFE0RUZnUVU3K1lLRmNpOFFVSGhTZ0xEdjhFQ3NjQ0p3QUl3Z2VFR0ExVWRJd1NCMlRDQjFvQVU3K1lLCkZjaThRVUhoU2dMRHY4RUNzY0NKd0FLaGdicWtnYmN3Z2JReEN6QUpCZ05WQkFZVEFsVlRNUTR3REFZRFZRUUkKRXdWVGRHRjBaVEVSTUE4R0ExVUVCeE1JVEc5allXeHBkSGt4T0RBMkJnTlZCQW9UTDNCbVUyVnVjMlVnZDJWaQpRMjl1Wm1sbmRYSmhkRzl5SUZObGJHWXRVMmxuYm1Wa0lFTmxjblJwWm1sallYUmxNU2d3SmdZSktvWklodmNOCkFRa0JGaGxoWkcxcGJrQndabE5sYm5ObExteHZZMkZzWkc5dFlXbHVNUjR3SEFZRFZRUURFeFZ3WmxObGJuTmwKTFRVM01qQmhNRFV3TW1JeU56ZUNBUUF3SFFZRFZSMGxCQll3RkFZSUt3WUJCUVVIQXdFR0NDc0dBUVVGQ0FJQwpNQXNHQTFVZER3UUVBd0lGb0RBTkJna3Foa2lHOXcwQkFRc0ZBQU9DQVFFQXJxZFpQdXd2MVZuUC82NmJDWFJ5CkVmaW1LRWlPcmtNaTB5M09PWGtzWEs1cEM2dTd6Ukl3WjEvRjYyRUp3ODlUOWx4Y01ZelZOTm5Idlg0bXFPRUcKUWJhRU42NEkxOHFud3ZmS2JrREZvRThMR1hSdzBkMnAyTGVmYTd4YTIvSGNHc0xHTktPbkJxb3N4ejUrQ1B3ZwpWeVRaTS9wV3p3aDdQRGc4bGdrcVc3dStlb01DNDJIbVJkOURCTmlzdFJ4RVlNMkFLQkFsZG1LYStvRUY1VUwwCm43aXpvNlZ4dHJWMTJvTTdySllRQ05kY00xZkVSeUwvb3ZkUnVpa0F5Wm1VVnFUL1dDZGo3dDdIVG9ob0RFYzEKSklkOVpPSmR2QmZLVU1sUWlELyswSVpTalFXRDczWkdsaEhTK2tOeWc1aDJhUjUwYjh3Wm9zQnNjSUZDa0pFbgp0UT09Ci0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K</crt>
<prv>LS0tLS1CRUdJTiBQUklWQVRFIEtFWS0tLS0tCk1JSUV2Z0lCQURBTkJna3Foa2lHOXcwQkFRRUZBQVNDQktnd2dnU2tBZ0VBQW9JQkFRQzM4NzJIMkE1M0lhYlkKMjN3YkNKR1htWFJWKy9odVVKeFdsc3hxb3M4eGxiY3UyRUx6UVpJWnArc1BtQ09yaWw4SXpUS3lVQTZKaGo1YwpKdnN5U1BpK1JMWitqM0hOeXVIbjdsaGxzOGJLMjZTS1Y1M0dmVlhGak1saXhxOG0vSW1oaERUNHcwdTI4Qnh1CjFvd0NGL3k1OE1SZVN0SlFJTEpyV1NVWFhsc1YrRFk5cmpGMmpZNDdrSEliU1JZSWxLUHo1TzVtNTA5TWcwdkEKQVdEQkQzNDg5OHRUalhROVNpb1NaclREbndKTmo3cHAwQnM4ZHhlRDBjL2poUGFWSWNKem1vbkpEdDc2dmFGVwozdWdQcG5VR0FFK3ZMQzRjV25DdTcvNWRjdHZFYjZudWxxdmlHMjA5TUt1SzdwcU1CUkxxT2pzMTN3Zy9tT3lCCmpjWWU5L3l4QWdNQkFBRUNnZ0VCQUpRRFpxU3duMnNTUTh0SVNBTUVrUW0zcXhrb3BzdzB4cWNScmFlOEd4VmQKejBpOU1KbkZVQWFleTQvL3JldndhZW1PR3RYSmZ2ai9jSnY3cmJIWGIzYkJtVW9hcDhxY0RjdnVSMmlHRUZYWQpCL3hjNVpINTlaTUFabWE1VWVQLzNjcDlzNVhhcHNpclNXV1I4cFFZc3Z6Mmt6ci8zMXdrQXd4SGJZWHhJVDk1CjNLRmk4VTZUM1hnU1c2eFowZHp1ZnlPUzAvbXlmNU5YLzVoRklPNmFDc0xlUjZ4N1RZa2FDQU9FYlViT29qUXkKc09XeWphbEtTUWZ3WEdzdVM0bXdyR2hMZ0NRYlB2MnE5V0Nia0VMNEZUZmRzRlZXcHBRNGlZVWtwNzhMY1FPMgpsSGR5cTJxTmJsNDIwa3h5M2FnZlF2YTVqYUgyRm5LdkExR2YxY05hcGRVQ2dZRUE0NzNMUWoxcExLSmRZN2JxCmtMU3NVT0ZhTUZlZG1xU2ttbzh3QjlpMXhzbElLQUd0M3U4dTdMZlZtU2lybnMwVVBTMHRVUDRyQXMzVFJocEgKU2Z4VXVsbGVGaktjZk9xRE11TTBCOGttbFJnUFRmVHVPaGNwMGVkamQwK1E5Y2VlY25kaFp3UEl6TUc3TWRTSApKOG5yU2t5TFdMdWUxUVJNZHNhbmNBRDhVYThDZ1lFQXpzYjYzbzRBSHlYNjZkcEJ6TGlzYzZxS2d2ZG4xazhVCm02N3RuK2M3NkVhSEtZTlk0RjdhS0dFSk1yeU0yQTJTelAzdm03Rmk4eGRtblgrSXd5cUx5T1VwSnZXQ012TVIKRDFpNWVFTVVoZVo2OUpOK0I3SmZ2RjYrK2tHa1NHOGxaN0VLY21Uc1kzRVJxOURsSk94Nk1ROFEwMDNsTHVtQQpJZm1DWlpRSUQ1OENnWUJjamFOdk5obnFJOG9rWGhBUjR2c3NtNGpWb0tYU1ZScjRIVHo5MDFwOGdReXNCWkt0CnlUS2V6VThuUVZvTjNYWmVMbC8rVEcwYVpKOTZHKy9nNTRWZmZqWTRlelVScHhUT3QzdEx0cm5SV2NmT2ZMM2MKS2RHN0ZuaGI0cUFjNHBWSUc3QWY5Mi9CbHZJR25FS1pMdnhLWTdVMXlIb1NRLzczUG1DSnFqemd6UUtCZ1FDZgpJQjE3RzRnWWNGL3hpdGJNTnVudmNUUjZxTzR0ekZtdG5TYWN3WlFtb2UvdUVIaGE0bU84WTBCeTNRcitVU1BCCndVR2RiUnNhdTgxcU12VUtURG1hZGsvKy9Ud2UvVk1Kbmx2TW9zS3VjTG42Y1c2eGVhR1hFc3FoUjlhbkwzRjMKcEpUSGg4Y3FsNTdqdkRRN0FBamdyQmxrb3pOVnNMZThiWWpkcHRlMVBRS0JnQ0xDR0R1RXNBYUxwZlRtOG44bgoyQ1h1NE52K1l3a1RlczduWjRoM3ZRODI1ZkQxbGVzVjBYdDJ1cVJqeFEvSDgxMHRGd1p3cC9uSVdycnRCZlZLClUzSThhYnpnUUtwOEwrZjVadTAxY1pZVk5TU0FIUFRHYm5jb1IzbGVPYjNLeUVXQjdsZFBHQWpOS3UwNkd5TEkKakh5TDhadEFBRXVBZ1FUOVFOVGJkQWJrCi0tLS0tRU5EIFBSSVZBVEUgS0VZLS0tLS0K</prv>
</cert>
<revision>
<time>1493327306</time>
<description>
<![CDATA[admin@10.97.67.143: /firewall_rules_edit.php made unknown change]]>
</description>
<username>admin@10.97.67.143</username>
</revision>
<gateways>
<gateway_item>
<interface>wan</interface>
<gateway>192.168.13.1</gateway>
<name>GW_WAN_2</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<interval/>
<descr>
<![CDATA[Interface wan Gateway]]>
</descr>
</gateway_item>
<gateway_item>
<interface>wan</interface>
<gateway>192.168.13.17</gateway>
<name>GW_VLAN17</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Gateway to VLAN 17]]>
</descr>
</gateway_item>
</gateways>
<ppps/>
<dyndnses/>
</pfSense>
2.10.3. Firewall Configuration for ID-ARM Subnet¶
<?xml version="1.0"?>
<pfSense>
<version>15.4</version>
<lastchange/>
<theme>pfSense_ng</theme>
<system>
<optimization>normal</optimization>
<hostname>FS-ARM</hostname>
<domain>FS-ARM.gov</domain>
<group>
<name>all</name>
<description>
<![CDATA[All Users]]>
</description>
<scope>system</scope>
<gid>1998</gid>
<member>0</member>
</group>
<group>
<name>admins</name>
<description>
<![CDATA[System Administrators]]>
</description>
<scope>system</scope>
<gid>1999</gid>
<member>0</member>
<priv>page-all</priv>
</group>
<user>
<name>admin</name>
<descr>
<![CDATA[System Administrator]]>
</descr>
<scope>system</scope>
<groupname>admins</groupname>
<password>$1$dSJImFph$GvZ7.1UbuWu.Yb8etC0re.</password>
<uid>0</uid>
<priv>user-shell-access</priv>
</user>
<nextuid>2000</nextuid>
<nextgid>2000</nextgid>
<timezone>America/New_York</timezone>
<time-update-interval/>
<timeservers>10.97.74.8</timeservers>
<webgui>
<protocol>http</protocol>
<loginautocomplete/>
<ssl-certref>5720a0502b277</ssl-certref>
<dashboardcolumns>2</dashboardcolumns>
<port/>
<max_procs>2</max_procs>
<nohttpreferercheck/>
</webgui>
<disablenatreflection>yes</disablenatreflection>
<disablesegmentationoffloading/>
<disablelargereceiveoffloading/>
<ipv6allow/>
<powerd_ac_mode>hadp</powerd_ac_mode>
<powerd_battery_mode>hadp</powerd_battery_mode>
<powerd_normal_mode>hadp</powerd_normal_mode>
<bogons>
<interval>monthly</interval>
</bogons>
<language>en_US</language>
<dns1gw>GW_WAN</dns1gw>
<dns2gw>GW_WAN</dns2gw>
<dns3gw>none</dns3gw>
<dns4gw>none</dns4gw>
<dnsserver>10.97.74.8</dnsserver>
<dnsserver>10.63.255.2</dnsserver>
<serialspeed>115200</serialspeed>
<primaryconsole>serial</primaryconsole>
</system>
<interfaces>
<wan>
<if>em0</if>
<descr>
<![CDATA[WAN]]>
</descr>
<enable/>
<spoofmac/>
<ipaddr>192.168.13.14</ipaddr>
<subnet>24</subnet>
<gateway>GW_WAN</gateway>
</wan>
<lan>
<enable/>
<if>em1</if>
<ipaddr>192.168.14.1</ipaddr>
<subnet>24</subnet>
<ipaddrv6/>
<subnetv6/>
<media/>
<mediaopt/>
<track6-interface>wan</track6-interface>
<track6-prefix-id>0</track6-prefix-id>
<gateway/>
<gatewayv6/>
</lan>
</interfaces>
<staticroutes>
<route>
<network>192.168.17.0/24</network>
<gateway>GW_VLAN17</gateway>
<descr>
<![CDATA[Route to VLAN 2017]]>
</descr>
</route>
<route>
<network>192.168.16.0/24</network>
<gateway>GW_VLAN16</gateway>
<descr>
<![CDATA[Route to VLAN 2016]]>
</descr>
</route>
<route>
<network>192.168.15.0/24</network>
<gateway>GW_VLAN15</gateway>
<descr>
<![CDATA[Route to VLAN 2015]]>
</descr>
</route>
<route>
<network>192.168.18.0/24</network>
<gateway>GW_VLAN18</gateway>
<descr>
<![CDATA[Route to VLAN 2018]]>
</descr>
</route>
<route>
<network>192.168.19.0/24</network>
<gateway>GW_VLAN19</gateway>
<descr>
<![CDATA[Route to VLAN 2019]]>
</descr>
</route>
</staticroutes>
<dhcpd>
<lan>
<enable/>
<range>
<from>192.168.14.100</from>
<to>192.168.14.150</to>
</range>
</lan>
<opt1>
<enable/>
<range>
<from>192.168.14.100</from>
<to>192.168.14.150</to>
</range>
</opt1>
<opt2>
<enable/>
<range>
<from>192.168.15.100</from>
<to>192.168.15.150</to>
</range>
</opt2>
<opt3>
<enable/>
<range>
<from>192.168.16.100</from>
<to>192.168.16.150</to>
</range>
</opt3>
</dhcpd>
<snmpd>
<syslocation/>
<syscontact/>
<rocommunity>public</rocommunity>
</snmpd>
<diag>
<ipv6nat>
<ipaddr/>
</ipv6nat>
</diag>
<bridge/>
<syslog/>
<nat>
<outbound>
<mode>disabled</mode>
</outbound>
</nat>
<filter>
<rule>
<id/>
<tracker>1481037990</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>3389</port>
</destination>
<descr>
<![CDATA[Allow RDP to LAN nodes]]>
</descr>
<created>
<time>1481037990</time>
<username>admin@10.97.67.155</username>
</created>
<updated>
<time>1493324042</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1481038086</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>2389</port>
</destination>
<descr>
<![CDATA[Allow Connection to Radiant Port 2389]]>
</descr>
<created>
<time>1481038086</time>
<username>admin@10.97.67.155</username>
</created>
<updated>
<time>1493324258</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1493650861</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>389</port>
</destination>
<descr>
<![CDATA[Allow Connection to Port 389 in LAN]]>
</descr>
<updated>
<time>1493650861</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1493650861</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493650905</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os></os>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>636</port>
</destination>
<descr>
<![CDATA[Allow Connection to Port 636 in LAN]]>
</descr>
<updated>
<time>1493650905</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1493650905</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493328157</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>8089</port>
</destination>
<descr>
<![CDATA[Allow Connection to Radiant Port 8089]]>
</descr>
<updated>
<time>1493328157</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493328157</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493328202</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>8090</port>
</destination>
<descr>
<![CDATA[Allow Connection to Radiant Port 8090]]>
</descr>
<updated>
<time>1493328202</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493328202</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493327695</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>8443</port>
</destination>
<descr>
<![CDATA[Allow Connection to Nextlabs port 8443]]>
</descr>
<updated>
<time>1493327695</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493327695</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493327739</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>443</port>
</destination>
<descr>
<![CDATA[Allow Connection to Nextlabs port 443]]>
</descr>
<updated>
<time>1493327739</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493327739</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493327782</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
<port>9233</port>
</destination>
<descr>
<![CDATA[Allow Connection to Nextlabs port 9233]]>
</descr>
<created>
<time>1493327782</time>
<username>admin@10.97.67.143</username>
</created>
<updated>
<time>1493327896</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1493327859</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
<port>19888</port>
</destination>
<descr>
<![CDATA[Allow Connection to Nextlabs port 19888]]>
</descr>
<updated>
<time>1493327859</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493327859</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493325919</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<network>lan</network>
</source>
<destination>
<any/>
<port>53</port>
</destination>
<descr>
<![CDATA[Allow DNS port 53 going out]]>
</descr>
<created>
<time>1493325919</time>
<username>admin@10.97.67.143</username>
</created>
<updated>
<time>1493326213</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1493328002</tracker>
<type>pass</type>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
<port>2000</port>
</destination>
<descr>
<![CDATA[Allow Connection to Nextlabs port 2000]]>
</descr>
<updated>
<time>1493328002</time>
<username>admin@10.97.67.143</username>
</updated>
<created>
<time>1493328002</time>
<username>admin@10.97.67.143</username>
</created>
</rule>
<rule>
<id/>
<tracker>1481037313</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<address>192.168.14.111</address>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow Radiant (192.168.14.111) to get out with any p]]>
</descr>
<created>
<time>1481037313</time>
<username>admin@10.97.67.155</username>
</created>
<updated>
<time>1481037359</time>
<username>admin@10.97.67.155</username>
</updated>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1480537443</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow Everything]]>
</descr>
<updated>
<time>1480537443</time>
<username>admin@192.168.13.139</username>
</updated>
<created>
<time>1480537443</time>
<username>admin@192.168.13.139</username>
</created>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1466105351</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1466105351</time>
<username>admin@192.168.13.101</username>
</updated>
<created>
<time>1466105351</time>
<username>admin@192.168.13.101</username>
</created>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1465934980</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>icmp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1465934980</time>
<username>admin@192.168.14.100</username>
</updated>
<created>
<time>1465934980</time>
<username>admin@192.168.14.100</username>
</created>
</rule>
<rule>
<id/>
<tracker>1461788221</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>wanip</network>
<port>80</port>
</destination>
<descr>
<![CDATA[Allow to Port 80 on Firewall WAN]]>
</descr>
<created>
<time>1461788221</time>
<username>admin@192.168.1.2</username>
</created>
<updated>
<time>1493323649</time>
<username>admin@10.97.67.143</username>
</updated>
</rule>
<rule>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Easy Rule: Passed from Firewall Log View]]>
</descr>
<protocol>udp</protocol>
<source>
<address>192.168.13.101</address>
</source>
<destination>
<address>192.168.13.102</address>
<port>137</port>
</destination>
<created>
<time>1466105470</time>
<username>Easy Rule</username>
</created>
</rule>
<rule>
<id/>
<tracker>1480537570</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[All Everything from LAN Interface]]>
</descr>
<updated>
<time>1480537570</time>
<username>admin@192.168.13.139</username>
</updated>
<created>
<time>1480537570</time>
<username>admin@192.168.13.139</username>
</created>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1466105363</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1466105363</time>
<username>admin@192.168.13.101</username>
</updated>
<created>
<time>1466105363</time>
<username>admin@192.168.13.101</username>
</created>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1465934995</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>icmp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1465934995</time>
<username>admin@192.168.14.100</username>
</updated>
<created>
<time>1465934995</time>
<username>admin@192.168.14.100</username>
</created>
</rule>
<rule>
<id/>
<tracker>1465915373</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow Any Any]]>
</descr>
<updated>
<time>1465915373</time>
<username>admin@192.168.14.100</username>
</updated>
<created>
<time>1465915373</time>
<username>admin@192.168.14.100</username>
</created>
<disabled/>
</rule>
<rule>
<type>pass</type>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Default allow LAN to any rule]]>
</descr>
<interface>lan</interface>
<tracker>0100000101</tracker>
<source>
<network>lan</network>
</source>
<destination>
<any/>
</destination>
</rule>
<rule>
<type>pass</type>
<ipprotocol>inet6</ipprotocol>
<descr>
<![CDATA[Default allow LAN IPv6 to any rule]]>
</descr>
<interface>lan</interface>
<tracker>0100000102</tracker>
<source>
<network>lan</network>
</source>
<destination>
<any/>
</destination>
</rule>
<separator>
<wan/>
<lan/>
<floatingrules/>
</separator>
</filter>
<shaper></shaper>
<ipsec/>
<aliases/>
<proxyarp/>
<cron>
<item>
<minute>1,31</minute>
<hour>0-5</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 adjkerntz -a</command>
</item>
<item>
<minute>1</minute>
<hour>3</hour>
<mday>1</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.update_bogons.sh</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 sshlockout</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 webConfiguratorlockout</command>
</item>
<item>
<minute>1</minute>
<hour>1</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.dyndns.update</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 virusprot</command>
</item>
<item>
<minute>30</minute>
<hour>12</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.update_urltables</command>
</item>
</cron>
<wol/>
<rrd>
<enable/>
</rrd>
<load_balancer>
<monitor_type>
<name>ICMP</name>
<type>icmp</type>
<descr>
<![CDATA[ICMP]]>
</descr>
<options/>
</monitor_type>
<monitor_type>
<name>TCP</name>
<type>tcp</type>
<descr>
<![CDATA[Generic TCP]]>
</descr>
<options/>
</monitor_type>
<monitor_type>
<name>HTTP</name>
<type>http</type>
<descr>
<![CDATA[Generic HTTP]]>
</descr>
<options>
<path>/</path>
<host/>
<code>200</code>
</options>
</monitor_type>
<monitor_type>
<name>HTTPS</name>
<type>https</type>
<descr>
<![CDATA[Generic HTTPS]]>
</descr>
<options>
<path>/</path>
<host/>
<code>200</code>
</options>
</monitor_type>
<monitor_type>
<name>SMTP</name>
<type>send</type>
<descr>
<![CDATA[Generic SMTP]]>
</descr>
<options>
<send/>
<expect>220 *</expect>
</options>
</monitor_type>
</load_balancer>
<widgets>
<sequence>system_information:col1:open,gateways:col1:open,interfaces:col2:open</sequence>
</widgets>
<openvpn/>
<dnshaper></dnshaper>
<unbound>
<enable/>
<dnssec/>
<active_interface/>
<outgoing_interface/>
<custom_options/>
<hideidentity/>
<hideversion/>
<dnssecstripped/>
</unbound>
<dhcpdv6>
<lan>
<range>
<from>::1000</from>
<to>::2000</to>
</range>
<ramode>assist</ramode>
<rapriority>medium</rapriority>
</lan>
</dhcpdv6>
<cert>
<refid>5720a0502b277</refid>
<descr>
<![CDATA[webConfigurator default (5720a0502b277)]]>
</descr>
<type>server</type>
<crt>LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUZiVENDQkZXZ0F3SUJBZ0lCQURBTkJna3Foa2lHOXcwQkFRc0ZBRENCdERFTE1Ba0dBMVVFQmhNQ1ZWTXgKRGpBTUJnTlZCQWdUQlZOMFlYUmxNUkV3RHdZRFZRUUhFd2hNYjJOaGJHbDBlVEU0TURZR0ExVUVDaE12Y0daVApaVzV6WlNCM1pXSkRiMjVtYVdkMWNtRjBiM0lnVTJWc1ppMVRhV2R1WldRZ1EyVnlkR2xtYVdOaGRHVXhLREFtCkJna3Foa2lHOXcwQkNRRVdHV0ZrYldsdVFIQm1VMlZ1YzJVdWJHOWpZV3hrYjIxaGFXNHhIakFjQmdOVkJBTVQKRlhCbVUyVnVjMlV0TlRjeU1HRXdOVEF5WWpJM056QWVGdzB4TmpBME1qY3hNVEU1TkRSYUZ3MHlNVEV3TVRneApNVEU1TkRSYU1JRzBNUXN3Q1FZRFZRUUdFd0pWVXpFT01Bd0dBMVVFQ0JNRlUzUmhkR1V4RVRBUEJnTlZCQWNUCkNFeHZZMkZzYVhSNU1UZ3dOZ1lEVlFRS0V5OXdabE5sYm5ObElIZGxZa052Ym1acFozVnlZWFJ2Y2lCVFpXeG0KTFZOcFoyNWxaQ0JEWlhKMGFXWnBZMkYwWlRFb01DWUdDU3FHU0liM0RRRUpBUllaWVdSdGFXNUFjR1pUWlc1egpaUzVzYjJOaGJHUnZiV0ZwYmpFZU1Cd0dBMVVFQXhNVmNHWlRaVzV6WlMwMU56SXdZVEExTURKaU1qYzNNSUlCCklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUF0L085aDlnT2R5R20yTnQ4R3dpUmw1bDAKVmZ2NGJsQ2NWcGJNYXFMUE1aVzNMdGhDODBHU0dhZnJENWdqcTRwZkNNMHlzbEFPaVlZK1hDYjdNa2o0dmtTMgpmbzl4emNyaDUrNVlaYlBHeXR1a2lsZWR4bjFWeFl6SllzYXZKdnlKb1lRMCtNTkx0dkFjYnRhTUFoZjh1ZkRFClhrclNVQ0N5YTFrbEYxNWJGZmcyUGE0eGRvMk9PNUJ5RzBrV0NKU2o4K1R1WnVkUFRJTkx3QUZnd1E5K1BQZkwKVTQxMFBVb3FFbWEwdzU4Q1RZKzZhZEFiUEhjWGc5SFA0NFQybFNIQ2M1cUp5UTdlK3IyaFZ0N29ENloxQmdCUApyeXd1SEZwd3J1LytYWExieEcrcDdwYXI0aHR0UFRDcml1NmFqQVVTNmpvN05kOElQNWpzZ1kzR0h2ZjhzUUlECkFRQUJvNElCaGpDQ0FZSXdDUVlEVlIwVEJBSXdBREFSQmdsZ2hrZ0JodmhDQVFFRUJBTUNCa0F3TXdZSllJWkkKQVliNFFnRU5CQ1lXSkU5d1pXNVRVMHdnUjJWdVpYSmhkR1ZrSUZObGNuWmxjaUJEWlhKMGFXWnBZMkYwWlRBZApCZ05WSFE0RUZnUVU3K1lLRmNpOFFVSGhTZ0xEdjhFQ3NjQ0p3QUl3Z2VFR0ExVWRJd1NCMlRDQjFvQVU3K1lLCkZjaThRVUhoU2dMRHY4RUNzY0NKd0FLaGdicWtnYmN3Z2JReEN6QUpCZ05WQkFZVEFsVlRNUTR3REFZRFZRUUkKRXdWVGRHRjBaVEVSTUE4R0ExVUVCeE1JVEc5allXeHBkSGt4T0RBMkJnTlZCQW9UTDNCbVUyVnVjMlVnZDJWaQpRMjl1Wm1sbmRYSmhkRzl5SUZObGJHWXRVMmxuYm1Wa0lFTmxjblJwWm1sallYUmxNU2d3SmdZSktvWklodmNOCkFRa0JGaGxoWkcxcGJrQndabE5sYm5ObExteHZZMkZzWkc5dFlXbHVNUjR3SEFZRFZRUURFeFZ3WmxObGJuTmwKTFRVM01qQmhNRFV3TW1JeU56ZUNBUUF3SFFZRFZSMGxCQll3RkFZSUt3WUJCUVVIQXdFR0NDc0dBUVVGQ0FJQwpNQXNHQTFVZER3UUVBd0lGb0RBTkJna3Foa2lHOXcwQkFRc0ZBQU9DQVFFQXJxZFpQdXd2MVZuUC82NmJDWFJ5CkVmaW1LRWlPcmtNaTB5M09PWGtzWEs1cEM2dTd6Ukl3WjEvRjYyRUp3ODlUOWx4Y01ZelZOTm5Idlg0bXFPRUcKUWJhRU42NEkxOHFud3ZmS2JrREZvRThMR1hSdzBkMnAyTGVmYTd4YTIvSGNHc0xHTktPbkJxb3N4ejUrQ1B3ZwpWeVRaTS9wV3p3aDdQRGc4bGdrcVc3dStlb01DNDJIbVJkOURCTmlzdFJ4RVlNMkFLQkFsZG1LYStvRUY1VUwwCm43aXpvNlZ4dHJWMTJvTTdySllRQ05kY00xZkVSeUwvb3ZkUnVpa0F5Wm1VVnFUL1dDZGo3dDdIVG9ob0RFYzEKSklkOVpPSmR2QmZLVU1sUWlELyswSVpTalFXRDczWkdsaEhTK2tOeWc1aDJhUjUwYjh3Wm9zQnNjSUZDa0pFbgp0UT09Ci0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K</crt>
<prv>LS0tLS1CRUdJTiBQUklWQVRFIEtFWS0tLS0tCk1JSUV2Z0lCQURBTkJna3Foa2lHOXcwQkFRRUZBQVNDQktnd2dnU2tBZ0VBQW9JQkFRQzM4NzJIMkE1M0lhYlkKMjN3YkNKR1htWFJWKy9odVVKeFdsc3hxb3M4eGxiY3UyRUx6UVpJWnArc1BtQ09yaWw4SXpUS3lVQTZKaGo1YwpKdnN5U1BpK1JMWitqM0hOeXVIbjdsaGxzOGJLMjZTS1Y1M0dmVlhGak1saXhxOG0vSW1oaERUNHcwdTI4Qnh1CjFvd0NGL3k1OE1SZVN0SlFJTEpyV1NVWFhsc1YrRFk5cmpGMmpZNDdrSEliU1JZSWxLUHo1TzVtNTA5TWcwdkEKQVdEQkQzNDg5OHRUalhROVNpb1NaclREbndKTmo3cHAwQnM4ZHhlRDBjL2poUGFWSWNKem1vbkpEdDc2dmFGVwozdWdQcG5VR0FFK3ZMQzRjV25DdTcvNWRjdHZFYjZudWxxdmlHMjA5TUt1SzdwcU1CUkxxT2pzMTN3Zy9tT3lCCmpjWWU5L3l4QWdNQkFBRUNnZ0VCQUpRRFpxU3duMnNTUTh0SVNBTUVrUW0zcXhrb3BzdzB4cWNScmFlOEd4VmQKejBpOU1KbkZVQWFleTQvL3JldndhZW1PR3RYSmZ2ai9jSnY3cmJIWGIzYkJtVW9hcDhxY0RjdnVSMmlHRUZYWQpCL3hjNVpINTlaTUFabWE1VWVQLzNjcDlzNVhhcHNpclNXV1I4cFFZc3Z6Mmt6ci8zMXdrQXd4SGJZWHhJVDk1CjNLRmk4VTZUM1hnU1c2eFowZHp1ZnlPUzAvbXlmNU5YLzVoRklPNmFDc0xlUjZ4N1RZa2FDQU9FYlViT29qUXkKc09XeWphbEtTUWZ3WEdzdVM0bXdyR2hMZ0NRYlB2MnE5V0Nia0VMNEZUZmRzRlZXcHBRNGlZVWtwNzhMY1FPMgpsSGR5cTJxTmJsNDIwa3h5M2FnZlF2YTVqYUgyRm5LdkExR2YxY05hcGRVQ2dZRUE0NzNMUWoxcExLSmRZN2JxCmtMU3NVT0ZhTUZlZG1xU2ttbzh3QjlpMXhzbElLQUd0M3U4dTdMZlZtU2lybnMwVVBTMHRVUDRyQXMzVFJocEgKU2Z4VXVsbGVGaktjZk9xRE11TTBCOGttbFJnUFRmVHVPaGNwMGVkamQwK1E5Y2VlY25kaFp3UEl6TUc3TWRTSApKOG5yU2t5TFdMdWUxUVJNZHNhbmNBRDhVYThDZ1lFQXpzYjYzbzRBSHlYNjZkcEJ6TGlzYzZxS2d2ZG4xazhVCm02N3RuK2M3NkVhSEtZTlk0RjdhS0dFSk1yeU0yQTJTelAzdm03Rmk4eGRtblgrSXd5cUx5T1VwSnZXQ012TVIKRDFpNWVFTVVoZVo2OUpOK0I3SmZ2RjYrK2tHa1NHOGxaN0VLY21Uc1kzRVJxOURsSk94Nk1ROFEwMDNsTHVtQQpJZm1DWlpRSUQ1OENnWUJjamFOdk5obnFJOG9rWGhBUjR2c3NtNGpWb0tYU1ZScjRIVHo5MDFwOGdReXNCWkt0CnlUS2V6VThuUVZvTjNYWmVMbC8rVEcwYVpKOTZHKy9nNTRWZmZqWTRlelVScHhUT3QzdEx0cm5SV2NmT2ZMM2MKS2RHN0ZuaGI0cUFjNHBWSUc3QWY5Mi9CbHZJR25FS1pMdnhLWTdVMXlIb1NRLzczUG1DSnFqemd6UUtCZ1FDZgpJQjE3RzRnWWNGL3hpdGJNTnVudmNUUjZxTzR0ekZtdG5TYWN3WlFtb2UvdUVIaGE0bU84WTBCeTNRcitVU1BCCndVR2RiUnNhdTgxcU12VUtURG1hZGsvKy9Ud2UvVk1Kbmx2TW9zS3VjTG42Y1c2eGVhR1hFc3FoUjlhbkwzRjMKcEpUSGg4Y3FsNTdqdkRRN0FBamdyQmxrb3pOVnNMZThiWWpkcHRlMVBRS0JnQ0xDR0R1RXNBYUxwZlRtOG44bgoyQ1h1NE52K1l3a1RlczduWjRoM3ZRODI1ZkQxbGVzVjBYdDJ1cVJqeFEvSDgxMHRGd1p3cC9uSVdycnRCZlZLClUzSThhYnpnUUtwOEwrZjVadTAxY1pZVk5TU0FIUFRHYm5jb1IzbGVPYjNLeUVXQjdsZFBHQWpOS3UwNkd5TEkKakh5TDhadEFBRXVBZ1FUOVFOVGJkQWJrCi0tLS0tRU5EIFBSSVZBVEUgS0VZLS0tLS0K</prv>
</cert>
<revision>
<time>1493650905</time>
<description>
<![CDATA[admin@10.97.67.135: /firewall_rules_edit.php made unknown change]]>
</description>
<username>admin@10.97.67.135</username>
</revision>
<gateways>
<gateway_item>
<interface>lan</interface>
<gateway>dynamic</gateway>
<name>WAN_DHCP</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Interface WAN_DHCP Gateway]]>
</descr>
</gateway_item>
<gateway_item>
<interface>lan</interface>
<gateway>dynamic</gateway>
<name>WAN_DHCP</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Interface WAN_DHCP Gateway]]>
</descr>
</gateway_item>
<gateway_item>
<interface>lan</interface>
<gateway>dynamic</gateway>
<name>WAN_DHCP6</name>
<weight>1</weight>
<ipprotocol>inet6</ipprotocol>
<descr>
<![CDATA[Interface WAN_DHCP6 Gateway]]>
</descr>
<defaultgw/>
</gateway_item>
<gateway_item>
<interface>wan</interface>
<gateway>192.168.13.1</gateway>
<name>GW_WAN</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<interval/>
<descr>
<![CDATA[Interface wan Gateway]]>
</descr>
<defaultgw/>
</gateway_item>
<gateway_item>
<interface>wan</interface>
<gateway>192.168.13.17</gateway>
<name>GW_VLAN17</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Gateway to VLAN 17]]>
</descr>
</gateway_item>
<gateway_item>
<interface>wan</interface>
<gateway>192.168.13.16</gateway>
<name>GW_VLAN16</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Gateway to VLAN 16]]>
</descr>
</gateway_item>
<gateway_item>
<interface>wan</interface>
<gateway>192.168.13.15</gateway>
<name>GW_VLAN15</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Gateway to VLAN 15]]>
</descr>
</gateway_item>
<gateway_item>
<interface>wan</interface>
<gateway>192.168.13.18</gateway>
<name>GW_VLAN18</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Gateway to VLAN 18]]>
</descr>
</gateway_item>
<gateway_item>
<interface>wan</interface>
<gateway>192.168.13.19</gateway>
<name>GW_VLAN19</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Gateway to VLAN 19]]>
</descr>
</gateway_item>
</gateways>
<ppps/>
<dyndnses/>
</pfSense>
2.10.4. Firewall Configuration for Private Cloud Subnet¶
<?xml version="1.0"?>
<pfSense>
<version>15.4</version>
<lastchange/>
<theme>pfSense_ng</theme>
<system>
<optimization>normal</optimization>
<hostname>FS-ARM</hostname>
<domain>FS-ARM.gov</domain>
<group>
<name>all</name>
<description>
<![CDATA[All Users]]>
</description>
<scope>system</scope>
<gid>1998</gid>
<member>0</member>
</group>
<group>
<name>admins</name>
<description>
<![CDATA[System Administrators]]>
</description>
<scope>system</scope>
<gid>1999</gid>
<member>0</member>
<priv>page-all</priv>
</group>
<user>
<name>admin</name>
<descr>
<![CDATA[System Administrator]]>
</descr>
<scope>system</scope>
<groupname>admins</groupname>
<password>$1$dSJImFph$GvZ7.1UbuWu.Yb8etC0re.</password>
<uid>0</uid>
<priv>user-shell-access</priv>
</user>
<nextuid>2000</nextuid>
<nextgid>2000</nextgid>
<timezone>America/New_York</timezone>
<time-update-interval/>
<timeservers>10.97.74.8</timeservers>
<webgui>
<protocol>http</protocol>
<loginautocomplete/>
<ssl-certref>5720a0502b277</ssl-certref>
<dashboardcolumns>2</dashboardcolumns>
<port/>
<max_procs>2</max_procs>
<nohttpreferercheck/>
</webgui>
<disablesegmentationoffloading/>
<disablelargereceiveoffloading/>
<ipv6allow/>
<powerd_ac_mode>hadp</powerd_ac_mode>
<powerd_battery_mode>hadp</powerd_battery_mode>
<powerd_normal_mode>hadp</powerd_normal_mode>
<bogons>
<interval>monthly</interval>
</bogons>
<language>en_US</language>
<dns1gw>GW_WAN</dns1gw>
<dns2gw>GW_WAN</dns2gw>
<dns3gw>none</dns3gw>
<dns4gw>none</dns4gw>
<dnsserver>10.97.74.8</dnsserver>
<dnsserver>10.63.255.2</dnsserver>
<maximumstates/>
<aliasesresolveinterval/>
<maximumtableentries/>
<maximumfrags/>
<enablenatreflectionpurenat>yes</enablenatreflectionpurenat>
<enablebinatreflection>yes</enablebinatreflection>
<enablenatreflectionhelper>yes</enablenatreflectionhelper>
<reflectiontimeout/>
<serialspeed>115200</serialspeed>
<primaryconsole>serial</primaryconsole>
</system>
<interfaces>
<wan>
<if>em0</if>
<descr>
<![CDATA[WAN]]>
</descr>
<enable/>
<spoofmac/>
<ipaddr>192.168.13.20</ipaddr>
<subnet>24</subnet>
<gateway>GW_WAN_2</gateway>
<ipaddrv6/>
<subnetv6/>
<gatewayv6/>
</wan>
<lan>
<enable/>
<if>em1</if>
<ipaddr>192.168.20.1</ipaddr>
<subnet>24</subnet>
<ipaddrv6/>
<subnetv6/>
<media/>
<mediaopt/>
<track6-interface>wan</track6-interface>
<track6-prefix-id>0</track6-prefix-id>
<gateway/>
<gatewayv6/>
</lan>
</interfaces>
<staticroutes/>
<dhcpd>
<lan>
<enable/>
<range>
<from>192.168.20.100</from>
<to>192.168.20.150</to>
</range>
</lan>
<opt1>
<enable/>
<range>
<from>192.168.14.100</from>
<to>192.168.14.150</to>
</range>
</opt1>
<opt2>
<enable/>
<range>
<from>192.168.15.100</from>
<to>192.168.15.150</to>
</range>
</opt2>
<opt3>
<enable/>
<range>
<from>192.168.16.100</from>
<to>192.168.16.150</to>
</range>
</opt3>
</dhcpd>
<snmpd>
<syslocation/>
<syscontact/>
<rocommunity>public</rocommunity>
</snmpd>
<diag>
<ipv6nat>
<ipaddr/>
</ipv6nat>
</diag>
<bridge/>
<syslog/>
<nat>
<outbound>
<mode>automatic</mode>
</outbound>
</nat>
<filter>
<rule>
<id/>
<tracker>1493654453</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>443</port>
</destination>
<descr>
<![CDATA[Allow HTTPS connection to LAN server]]>
</descr>
<updated>
<time>1493654453</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1493654453</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493654529</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>80</port>
</destination>
<descr>
<![CDATA[Allow HTTP connection to LAN server]]>
</descr>
<updated>
<time>1493654529</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1493654529</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493654337</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>3389</port>
</destination>
<descr>
<![CDATA[Allow RDP Connection to LAN servers]]>
</descr>
<created>
<time>1493654337</time>
<username>admin@10.97.67.135</username>
</created>
<updated>
<time>1493654474</time>
<username>admin@10.97.67.135</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1469131237</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>wanip</network>
<port>80</port>
</destination>
<descr>
<![CDATA[Allow Port 80 on WAN ]]>
</descr>
<created>
<time>1469131237</time>
<username>admin@192.168.20.103</username>
</created>
<updated>
<time>1493654100</time>
<username>admin@10.97.67.135</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1465935224</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>icmp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1465935224</time>
<username>admin@192.168.18.100</username>
</updated>
<created>
<time>1465935224</time>
<username>admin@192.168.18.100</username>
</created>
</rule>
<rule>
<id/>
<tracker>1461788221</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>wanip</network>
<port>443</port>
</destination>
<descr>
<![CDATA[Allow Port 443 on WAN]]>
</descr>
<created>
<time>1461788221</time>
<username>admin@192.168.1.2</username>
</created>
<updated>
<time>1493654159</time>
<username>admin@10.97.67.135</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1468437174</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1468437174</time>
<username>admin@192.168.20.100</username>
</updated>
<created>
<time>1468437174</time>
<username>admin@192.168.20.100</username>
</created>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1465935241</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>icmp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1465935241</time>
<username>admin@192.168.18.100</username>
</updated>
<created>
<time>1465935241</time>
<username>admin@192.168.18.100</username>
</created>
</rule>
<rule>
<type>pass</type>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Default allow LAN to any rule]]>
</descr>
<interface>lan</interface>
<tracker>0100000101</tracker>
<source>
<network>lan</network>
</source>
<destination>
<any/>
</destination>
</rule>
<rule>
<type>pass</type>
<ipprotocol>inet6</ipprotocol>
<descr>
<![CDATA[Default allow LAN IPv6 to any rule]]>
</descr>
<interface>lan</interface>
<tracker>0100000102</tracker>
<source>
<network>lan</network>
</source>
<destination>
<any/>
</destination>
</rule>
<separator>
<wan/>
<lan/>
<floatingrules/>
</separator>
</filter>
<shaper></shaper>
<ipsec/>
<aliases/>
<proxyarp/>
<cron>
<item>
<minute>1,31</minute>
<hour>0-5</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 adjkerntz -a</command>
</item>
<item>
<minute>1</minute>
<hour>3</hour>
<mday>1</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.update_bogons.sh</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 sshlockout</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 webConfiguratorlockout</command>
</item>
<item>
<minute>1</minute>
<hour>1</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.dyndns.update</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 virusprot</command>
</item>
<item>
<minute>30</minute>
<hour>12</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.update_urltables</command>
</item>
</cron>
<wol/>
<rrd>
<enable/>
</rrd>
<load_balancer>
<monitor_type>
<name>ICMP</name>
<type>icmp</type>
<descr>
<![CDATA[ICMP]]>
</descr>
<options/>
</monitor_type>
<monitor_type>
<name>TCP</name>
<type>tcp</type>
<descr>
<![CDATA[Generic TCP]]>
</descr>
<options/>
</monitor_type>
<monitor_type>
<name>HTTP</name>
<type>http</type>
<descr>
<![CDATA[Generic HTTP]]>
</descr>
<options>
<path>/</path>
<host/>
<code>200</code>
</options>
</monitor_type>
<monitor_type>
<name>HTTPS</name>
<type>https</type>
<descr>
<![CDATA[Generic HTTPS]]>
</descr>
<options>
<path>/</path>
<host/>
<code>200</code>
</options>
</monitor_type>
<monitor_type>
<name>SMTP</name>
<type>send</type>
<descr>
<![CDATA[Generic SMTP]]>
</descr>
<options>
<send/>
<expect>220 *</expect>
</options>
</monitor_type>
</load_balancer>
<widgets>
<sequence>system_information:col1:open,gateways:col1:open,interfaces:col2:open</sequence>
</widgets>
<openvpn/>
<dnshaper></dnshaper>
<unbound>
<dnssec/>
<active_interface>all</active_interface>
<outgoing_interface>all</outgoing_interface>
<custom_options/>
<hideidentity/>
<hideversion/>
<dnssecstripped/>
<domainoverrides>
<domain>acmefinancial.com</domain>
<ip>192.168.19.10</ip>
<descr>
<![CDATA[Active Directory]]>
</descr>
</domainoverrides>
<port/>
<system_domain_local_zone_type>transparent</system_domain_local_zone_type>
<enable/>
</unbound>
<dhcpdv6>
<lan>
<range>
<from>::1000</from>
<to>::2000</to>
</range>
<ramode>assist</ramode>
<rapriority>medium</rapriority>
</lan>
</dhcpdv6>
<cert>
<refid>5720a0502b277</refid>
<descr>
<![CDATA[webConfigurator default (5720a0502b277)]]>
</descr>
<type>server</type>
<crt>LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUZiVENDQkZXZ0F3SUJBZ0lCQURBTkJna3Foa2lHOXcwQkFRc0ZBRENCdERFTE1Ba0dBMVVFQmhNQ1ZWTXgKRGpBTUJnTlZCQWdUQlZOMFlYUmxNUkV3RHdZRFZRUUhFd2hNYjJOaGJHbDBlVEU0TURZR0ExVUVDaE12Y0daVApaVzV6WlNCM1pXSkRiMjVtYVdkMWNtRjBiM0lnVTJWc1ppMVRhV2R1WldRZ1EyVnlkR2xtYVdOaGRHVXhLREFtCkJna3Foa2lHOXcwQkNRRVdHV0ZrYldsdVFIQm1VMlZ1YzJVdWJHOWpZV3hrYjIxaGFXNHhIakFjQmdOVkJBTVQKRlhCbVUyVnVjMlV0TlRjeU1HRXdOVEF5WWpJM056QWVGdzB4TmpBME1qY3hNVEU1TkRSYUZ3MHlNVEV3TVRneApNVEU1TkRSYU1JRzBNUXN3Q1FZRFZRUUdFd0pWVXpFT01Bd0dBMVVFQ0JNRlUzUmhkR1V4RVRBUEJnTlZCQWNUCkNFeHZZMkZzYVhSNU1UZ3dOZ1lEVlFRS0V5OXdabE5sYm5ObElIZGxZa052Ym1acFozVnlZWFJ2Y2lCVFpXeG0KTFZOcFoyNWxaQ0JEWlhKMGFXWnBZMkYwWlRFb01DWUdDU3FHU0liM0RRRUpBUllaWVdSdGFXNUFjR1pUWlc1egpaUzVzYjJOaGJHUnZiV0ZwYmpFZU1Cd0dBMVVFQXhNVmNHWlRaVzV6WlMwMU56SXdZVEExTURKaU1qYzNNSUlCCklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUF0L085aDlnT2R5R20yTnQ4R3dpUmw1bDAKVmZ2NGJsQ2NWcGJNYXFMUE1aVzNMdGhDODBHU0dhZnJENWdqcTRwZkNNMHlzbEFPaVlZK1hDYjdNa2o0dmtTMgpmbzl4emNyaDUrNVlaYlBHeXR1a2lsZWR4bjFWeFl6SllzYXZKdnlKb1lRMCtNTkx0dkFjYnRhTUFoZjh1ZkRFClhrclNVQ0N5YTFrbEYxNWJGZmcyUGE0eGRvMk9PNUJ5RzBrV0NKU2o4K1R1WnVkUFRJTkx3QUZnd1E5K1BQZkwKVTQxMFBVb3FFbWEwdzU4Q1RZKzZhZEFiUEhjWGc5SFA0NFQybFNIQ2M1cUp5UTdlK3IyaFZ0N29ENloxQmdCUApyeXd1SEZwd3J1LytYWExieEcrcDdwYXI0aHR0UFRDcml1NmFqQVVTNmpvN05kOElQNWpzZ1kzR0h2ZjhzUUlECkFRQUJvNElCaGpDQ0FZSXdDUVlEVlIwVEJBSXdBREFSQmdsZ2hrZ0JodmhDQVFFRUJBTUNCa0F3TXdZSllJWkkKQVliNFFnRU5CQ1lXSkU5d1pXNVRVMHdnUjJWdVpYSmhkR1ZrSUZObGNuWmxjaUJEWlhKMGFXWnBZMkYwWlRBZApCZ05WSFE0RUZnUVU3K1lLRmNpOFFVSGhTZ0xEdjhFQ3NjQ0p3QUl3Z2VFR0ExVWRJd1NCMlRDQjFvQVU3K1lLCkZjaThRVUhoU2dMRHY4RUNzY0NKd0FLaGdicWtnYmN3Z2JReEN6QUpCZ05WQkFZVEFsVlRNUTR3REFZRFZRUUkKRXdWVGRHRjBaVEVSTUE4R0ExVUVCeE1JVEc5allXeHBkSGt4T0RBMkJnTlZCQW9UTDNCbVUyVnVjMlVnZDJWaQpRMjl1Wm1sbmRYSmhkRzl5SUZObGJHWXRVMmxuYm1Wa0lFTmxjblJwWm1sallYUmxNU2d3SmdZSktvWklodmNOCkFRa0JGaGxoWkcxcGJrQndabE5sYm5ObExteHZZMkZzWkc5dFlXbHVNUjR3SEFZRFZRUURFeFZ3WmxObGJuTmwKTFRVM01qQmhNRFV3TW1JeU56ZUNBUUF3SFFZRFZSMGxCQll3RkFZSUt3WUJCUVVIQXdFR0NDc0dBUVVGQ0FJQwpNQXNHQTFVZER3UUVBd0lGb0RBTkJna3Foa2lHOXcwQkFRc0ZBQU9DQVFFQXJxZFpQdXd2MVZuUC82NmJDWFJ5CkVmaW1LRWlPcmtNaTB5M09PWGtzWEs1cEM2dTd6Ukl3WjEvRjYyRUp3ODlUOWx4Y01ZelZOTm5Idlg0bXFPRUcKUWJhRU42NEkxOHFud3ZmS2JrREZvRThMR1hSdzBkMnAyTGVmYTd4YTIvSGNHc0xHTktPbkJxb3N4ejUrQ1B3ZwpWeVRaTS9wV3p3aDdQRGc4bGdrcVc3dStlb01DNDJIbVJkOURCTmlzdFJ4RVlNMkFLQkFsZG1LYStvRUY1VUwwCm43aXpvNlZ4dHJWMTJvTTdySllRQ05kY00xZkVSeUwvb3ZkUnVpa0F5Wm1VVnFUL1dDZGo3dDdIVG9ob0RFYzEKSklkOVpPSmR2QmZLVU1sUWlELyswSVpTalFXRDczWkdsaEhTK2tOeWc1aDJhUjUwYjh3Wm9zQnNjSUZDa0pFbgp0UT09Ci0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K</crt>
<prv>LS0tLS1CRUdJTiBQUklWQVRFIEtFWS0tLS0tCk1JSUV2Z0lCQURBTkJna3Foa2lHOXcwQkFRRUZBQVNDQktnd2dnU2tBZ0VBQW9JQkFRQzM4NzJIMkE1M0lhYlkKMjN3YkNKR1htWFJWKy9odVVKeFdsc3hxb3M4eGxiY3UyRUx6UVpJWnArc1BtQ09yaWw4SXpUS3lVQTZKaGo1YwpKdnN5U1BpK1JMWitqM0hOeXVIbjdsaGxzOGJLMjZTS1Y1M0dmVlhGak1saXhxOG0vSW1oaERUNHcwdTI4Qnh1CjFvd0NGL3k1OE1SZVN0SlFJTEpyV1NVWFhsc1YrRFk5cmpGMmpZNDdrSEliU1JZSWxLUHo1TzVtNTA5TWcwdkEKQVdEQkQzNDg5OHRUalhROVNpb1NaclREbndKTmo3cHAwQnM4ZHhlRDBjL2poUGFWSWNKem1vbkpEdDc2dmFGVwozdWdQcG5VR0FFK3ZMQzRjV25DdTcvNWRjdHZFYjZudWxxdmlHMjA5TUt1SzdwcU1CUkxxT2pzMTN3Zy9tT3lCCmpjWWU5L3l4QWdNQkFBRUNnZ0VCQUpRRFpxU3duMnNTUTh0SVNBTUVrUW0zcXhrb3BzdzB4cWNScmFlOEd4VmQKejBpOU1KbkZVQWFleTQvL3JldndhZW1PR3RYSmZ2ai9jSnY3cmJIWGIzYkJtVW9hcDhxY0RjdnVSMmlHRUZYWQpCL3hjNVpINTlaTUFabWE1VWVQLzNjcDlzNVhhcHNpclNXV1I4cFFZc3Z6Mmt6ci8zMXdrQXd4SGJZWHhJVDk1CjNLRmk4VTZUM1hnU1c2eFowZHp1ZnlPUzAvbXlmNU5YLzVoRklPNmFDc0xlUjZ4N1RZa2FDQU9FYlViT29qUXkKc09XeWphbEtTUWZ3WEdzdVM0bXdyR2hMZ0NRYlB2MnE5V0Nia0VMNEZUZmRzRlZXcHBRNGlZVWtwNzhMY1FPMgpsSGR5cTJxTmJsNDIwa3h5M2FnZlF2YTVqYUgyRm5LdkExR2YxY05hcGRVQ2dZRUE0NzNMUWoxcExLSmRZN2JxCmtMU3NVT0ZhTUZlZG1xU2ttbzh3QjlpMXhzbElLQUd0M3U4dTdMZlZtU2lybnMwVVBTMHRVUDRyQXMzVFJocEgKU2Z4VXVsbGVGaktjZk9xRE11TTBCOGttbFJnUFRmVHVPaGNwMGVkamQwK1E5Y2VlY25kaFp3UEl6TUc3TWRTSApKOG5yU2t5TFdMdWUxUVJNZHNhbmNBRDhVYThDZ1lFQXpzYjYzbzRBSHlYNjZkcEJ6TGlzYzZxS2d2ZG4xazhVCm02N3RuK2M3NkVhSEtZTlk0RjdhS0dFSk1yeU0yQTJTelAzdm03Rmk4eGRtblgrSXd5cUx5T1VwSnZXQ012TVIKRDFpNWVFTVVoZVo2OUpOK0I3SmZ2RjYrK2tHa1NHOGxaN0VLY21Uc1kzRVJxOURsSk94Nk1ROFEwMDNsTHVtQQpJZm1DWlpRSUQ1OENnWUJjamFOdk5obnFJOG9rWGhBUjR2c3NtNGpWb0tYU1ZScjRIVHo5MDFwOGdReXNCWkt0CnlUS2V6VThuUVZvTjNYWmVMbC8rVEcwYVpKOTZHKy9nNTRWZmZqWTRlelVScHhUT3QzdEx0cm5SV2NmT2ZMM2MKS2RHN0ZuaGI0cUFjNHBWSUc3QWY5Mi9CbHZJR25FS1pMdnhLWTdVMXlIb1NRLzczUG1DSnFqemd6UUtCZ1FDZgpJQjE3RzRnWWNGL3hpdGJNTnVudmNUUjZxTzR0ekZtdG5TYWN3WlFtb2UvdUVIaGE0bU84WTBCeTNRcitVU1BCCndVR2RiUnNhdTgxcU12VUtURG1hZGsvKy9Ud2UvVk1Kbmx2TW9zS3VjTG42Y1c2eGVhR1hFc3FoUjlhbkwzRjMKcEpUSGg4Y3FsNTdqdkRRN0FBamdyQmxrb3pOVnNMZThiWWpkcHRlMVBRS0JnQ0xDR0R1RXNBYUxwZlRtOG44bgoyQ1h1NE52K1l3a1RlczduWjRoM3ZRODI1ZkQxbGVzVjBYdDJ1cVJqeFEvSDgxMHRGd1p3cC9uSVdycnRCZlZLClUzSThhYnpnUUtwOEwrZjVadTAxY1pZVk5TU0FIUFRHYm5jb1IzbGVPYjNLeUVXQjdsZFBHQWpOS3UwNkd5TEkKakh5TDhadEFBRXVBZ1FUOVFOVGJkQWJrCi0tLS0tRU5EIFBSSVZBVEUgS0VZLS0tLS0K</prv>
</cert>
<revision>
<time>1493654529</time>
<description>
<![CDATA[admin@10.97.67.135: /firewall_rules_edit.php made unknown change]]>
</description>
<username>admin@10.97.67.135</username>
</revision>
<gateways>
<gateway_item>
<interface>wan</interface>
<gateway>192.168.13.1</gateway>
<name>GW_WAN_2</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<interval/>
<descr>
<![CDATA[Interface wan Gateway]]>
</descr>
</gateway_item>
</gateways>
<ppps/>
<dyndnses/>
<dnsmasq>
<enable/>
<custom_options/>
<port>53</port>
<interface/>
<hosts>
<host>activedirectory</host>
<domain>acmefinancial.com</domain>
<ip>192.168.19.10</ip>
<descr/>
<aliases/>
</hosts>
</dnsmasq>
</pfSense>
2.10.5. Firewall Configuration for the Management and Monitoring Subnet¶
<?xml version="1.0"?>
<pfSense>
<version>15.4</version>
<lastchange/>
<theme>pfSense_ng</theme>
<system>
<optimization>normal</optimization>
<hostname>FS-ARM</hostname>
<domain>FS-ARM.gov</domain>
<group>
<name>all</name>
<description>
<![CDATA[All Users]]>
</description>
<scope>system</scope>
<gid>1998</gid>
<member>0</member>
</group>
<group>
<name>admins</name>
<description>
<![CDATA[System Administrators]]>
</description>
<scope>system</scope>
<gid>1999</gid>
<member>0</member>
<priv>page-all</priv>
</group>
<user>
<name>admin</name>
<descr>
<![CDATA[System Administrator]]>
</descr>
<scope>system</scope>
<groupname>admins</groupname>
<password>$1$dSJImFph$GvZ7.1UbuWu.Yb8etC0re.</password>
<uid>0</uid>
<priv>user-shell-access</priv>
</user>
<nextuid>2000</nextuid>
<nextgid>2000</nextgid>
<timezone>America/New_York</timezone>
<time-update-interval/>
<timeservers>10.97.74.8</timeservers>
<webgui>
<protocol>http</protocol>
<loginautocomplete/>
<ssl-certref>5720a0502b277</ssl-certref>
<dashboardcolumns>2</dashboardcolumns>
<port/>
<max_procs>2</max_procs>
<nohttpreferercheck/>
</webgui>
<disablenatreflection>yes</disablenatreflection>
<disablesegmentationoffloading/>
<disablelargereceiveoffloading/>
<ipv6allow/>
<powerd_ac_mode>hadp</powerd_ac_mode>
<powerd_battery_mode>hadp</powerd_battery_mode>
<powerd_normal_mode>hadp</powerd_normal_mode>
<bogons>
<interval>monthly</interval>
</bogons>
<language>en_US</language>
<dns1gw>GW_WAN</dns1gw>
<dns2gw>GW_WAN</dns2gw>
<dns3gw>none</dns3gw>
<dns4gw>none</dns4gw>
<dnsserver>10.97.74.8</dnsserver>
<dnsserver>10.63.255.2</dnsserver>
<serialspeed>115200</serialspeed>
<primaryconsole>serial</primaryconsole>
<maximumstates/>
<aliasesresolveinterval/>
<maximumtableentries/>
<maximumfrags/>
<reflectiontimeout/>
</system>
<interfaces>
<wan>
<if>em0</if>
<descr>
<![CDATA[WAN]]>
</descr>
<enable/>
<spoofmac/>
<ipaddr>192.168.13.17</ipaddr>
<subnet>24</subnet>
<gateway>GW_WAN_2</gateway>
<ipaddrv6/>
<subnetv6/>
<gatewayv6/>
</wan>
<lan>
<enable/>
<if>em1</if>
<ipaddr>192.168.17.1</ipaddr>
<subnet>24</subnet>
<ipaddrv6/>
<subnetv6/>
<media/>
<mediaopt/>
<track6-interface>wan</track6-interface>
<track6-prefix-id>0</track6-prefix-id>
<gateway/>
<gatewayv6/>
</lan>
</interfaces>
<staticroutes>
<route>
<network>192.168.19.0/24</network>
<gateway>GW_VLAN19</gateway>
<descr>
<![CDATA[Route to VLAN 2019]]>
</descr>
</route>
</staticroutes>
<dhcpd>
<lan>
<enable/>
<range>
<from>192.168.17.100</from>
<to>192.168.17.150</to>
</range>
</lan>
<opt1>
<enable/>
<range>
<from>192.168.14.100</from>
<to>192.168.14.150</to>
</range>
</opt1>
<opt2>
<enable/>
<range>
<from>192.168.15.100</from>
<to>192.168.15.150</to>
</range>
</opt2>
<opt3>
<enable/>
<range>
<from>192.168.16.100</from>
<to>192.168.16.150</to>
</range>
</opt3>
</dhcpd>
<snmpd>
<syslocation/>
<syscontact/>
<rocommunity>public</rocommunity>
</snmpd>
<diag>
<ipv6nat>
<ipaddr/>
</ipv6nat>
</diag>
<bridge/>
<syslog/>
<nat>
<outbound>
<mode>disabled</mode>
</outbound>
<rule>
<source>
<any/>
</source>
<destination>
<address>192.168.13.171</address>
<port>5176</port>
</destination>
<protocol>tcp/udp</protocol>
<target>192.168.17.11</target>
<local-port>5176</local-port>
<interface>wan</interface>
<descr>
<![CDATA[Mapping to ConsoleWorks]]>
</descr>
<associated-rule-id>nat_57bf06b1aa4c21.26556306</associated-rule-id>
<natreflection>purenat</natreflection>
<created>
<time>1472136881</time>
<username>admin@192.168.13.135</username>
</created>
<updated>
<time>1472137126</time>
<username>admin@192.168.13.135</username>
</updated>
</rule>
<separator/>
</nat>
<filter>
<rule>
<id/>
<tracker>1493655499</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os></os>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>514</port>
</destination>
<descr>
<![CDATA[Allow Connection to syslog in LAN]]>
</descr>
<updated>
<time>1493655499</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1493655499</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493649494</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>1433-1434</port>
</destination>
<descr>
<![CDATA[Allow Connection to Sharepoint database-1433 and 143]]>
</descr>
<created>
<time>1493649494</time>
<username>admin@10.97.67.135</username>
</created>
<updated>
<time>1493649550</time>
<username>admin@10.97.67.135</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1493649686</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>3389</port>
</destination>
<descr>
<![CDATA[Allow Connection to RDP in LAN]]>
</descr>
<updated>
<time>1493649686</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1493649686</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493649754</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>389</port>
</destination>
<descr>
<![CDATA[Allow LDAP Connection to LAN]]>
</descr>
<created>
<time>1493649754</time>
<username>admin@10.97.67.135</username>
</created>
<updated>
<time>1493650257</time>
<username>admin@10.97.67.135</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1493650231</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>2389</port>
</destination>
<descr>
<![CDATA[Allow Alternate LDAP Connection to Radiant ]]>
</descr>
<updated>
<time>1493650231</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1493650231</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493649801</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>636</port>
</destination>
<descr>
<![CDATA[Allow LDAPS Connection to LAN]]>
</descr>
<created>
<time>1493649801</time>
<username>admin@10.97.67.135</username>
</created>
<updated>
<time>1493650283</time>
<username>admin@10.97.67.135</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1493649895</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>8000</port>
</destination>
<descr>
<![CDATA[Allow Connection to Port 8000 -Splunk Web]]>
</descr>
<created>
<time>1493649895</time>
<username>admin@10.97.67.135</username>
</created>
<updated>
<time>1493649933</time>
<username>admin@10.97.67.135</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1493650131</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>8089</port>
</destination>
<descr>
<![CDATA[Allow Connection to Port 8089 -Splunk management por]]>
</descr>
<updated>
<time>1493650131</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1493650131</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1493650643</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>lan</network>
<port>9997</port>
</destination>
<descr>
<![CDATA[Allow Connection to Port 9997 -Splunk Forwarding]]>
</descr>
<updated>
<time>1493650643</time>
<username>admin@10.97.67.135</username>
</updated>
<created>
<time>1493650643</time>
<username>admin@10.97.67.135</username>
</created>
</rule>
<rule>
<id/>
<tracker>1481037634</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<address>192.168.17.100</address>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow Radiant (192.168.17.100) to outside -LAN]]>
</descr>
<created>
<time>1481037634</time>
<username>admin@10.97.67.155</username>
</created>
<updated>
<time>1481037861</time>
<username>admin@10.97.67.155</username>
</updated>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1481037754</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<source>
<address>192.168.17.100</address>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Allow Radiant (192.168.17.100) to outside - WAN]]>
</descr>
<created>
<time>1481037754</time>
<username>admin@10.97.67.155</username>
</created>
<updated>
<time>1481037814</time>
<username>admin@10.97.67.155</username>
</updated>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1472179706</tracker>
<type>pass</type>
<interface>wan,lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<direction>any</direction>
<quick>yes</quick>
<floating>yes</floating>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr>
<![CDATA[Test for comms between 2017 and 2019]]>
</descr>
<updated>
<time>1472179706</time>
<username>admin@10.97.67.137</username>
</updated>
<created>
<time>1472179706</time>
<username>admin@10.97.67.137</username>
</created>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1469130242</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<network>wanip</network>
<port>80</port>
</destination>
<descr>
<![CDATA[Allow to Port 80 on Firewall WAN]]>
</descr>
<created>
<time>1469130242</time>
<username>admin@192.168.17.103</username>
</created>
<updated>
<time>1493649052</time>
<username>admin@10.97.67.135</username>
</updated>
</rule>
<rule>
<id/>
<tracker>1465935549</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>icmp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1465935549</time>
<username>admin@192.168.17.100</username>
</updated>
<created>
<time>1465935549</time>
<username>admin@192.168.17.100</username>
</created>
</rule>
<rule>
<id/>
<tracker>1461788221</tracker>
<type>pass</type>
<interface>wan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp</protocol>
<source>
<any/>
</source>
<destination>
<network>wanip</network>
<port>443</port>
</destination>
<descr>
<![CDATA[Allow to Port 443 on Firewall WAN]]>
</descr>
<created>
<time>1461788221</time>
<username>admin@192.168.1.2</username>
</created>
<updated>
<time>1493649121</time>
<username>admin@10.97.67.135</username>
</updated>
</rule>
<rule>
<source>
<any/>
</source>
<interface>wan</interface>
<protocol>tcp/udp</protocol>
<destination>
<address>192.168.17.11</address>
<port>5176</port>
</destination>
<descr>
<![CDATA[NAT Mapping to ConsoleWorks]]>
</descr>
<associated-rule-id>nat_57bf06b1aa4c21.26556306</associated-rule-id>
<tracker>1472136881</tracker>
<created>
<time>1472136881</time>
<username>NAT Port Forward</username>
</created>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1469130278</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>tcp/udp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
<port>22</port>
</destination>
<descr>
<![CDATA[Test to port 22]]>
</descr>
<created>
<time>1469130278</time>
<username>admin@192.168.17.103</username>
</created>
<updated>
<time>1472170372</time>
<username>admin@192.168.13.135</username>
</updated>
<disabled/>
</rule>
<rule>
<id/>
<tracker>1465935564</tracker>
<type>pass</type>
<interface>lan</interface>
<ipprotocol>inet</ipprotocol>
<tag/>
<tagged/>
<max/>
<max-src-nodes/>
<max-src-conn/>
<max-src-states/>
<statetimeout/>
<statetype>keep state</statetype>
<os/>
<protocol>icmp</protocol>
<source>
<any/>
</source>
<destination>
<any/>
</destination>
<descr/>
<updated>
<time>1465935564</time>
<username>admin@192.168.17.100</username>
</updated>
<created>
<time>1465935564</time>
<username>admin@192.168.17.100</username>
</created>
</rule>
<rule>
<type>pass</type>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Default allow LAN to any rule]]>
</descr>
<interface>lan</interface>
<tracker>0100000101</tracker>
<source>
<network>lan</network>
</source>
<destination>
<any/>
</destination>
</rule>
<rule>
<type>pass</type>
<ipprotocol>inet6</ipprotocol>
<descr>
<![CDATA[Default allow LAN IPv6 to any rule]]>
</descr>
<interface>lan</interface>
<tracker>0100000102</tracker>
<source>
<network>lan</network>
</source>
<destination>
<any/>
</destination>
</rule>
<separator>
<wan/>
<lan/>
<floatingrules/>
</separator>
<bypassstaticroutes>yes</bypassstaticroutes>
</filter>
<shaper></shaper>
<ipsec/>
<aliases/>
<proxyarp/>
<cron>
<item>
<minute>1,31</minute>
<hour>0-5</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 adjkerntz -a</command>
</item>
<item>
<minute>1</minute>
<hour>3</hour>
<mday>1</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.update_bogons.sh</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 sshlockout</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 webConfiguratorlockout</command>
</item>
<item>
<minute>1</minute>
<hour>1</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.dyndns.update</command>
</item>
<item>
<minute>*/60</minute>
<hour>*</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 virusprot</command>
</item>
<item>
<minute>30</minute>
<hour>12</hour>
<mday>*</mday>
<month>*</month>
<wday>*</wday>
<who>root</who>
<command>/usr/bin/nice -n20 /etc/rc.update_urltables</command>
</item>
</cron>
<wol/>
<rrd>
<enable/>
<category>left=system-processor&right=&resolution=300&timePeriod=-1d&startDate=&endDate=&startTime=0&endTime=0&graphtype=line&invert=true</category>
</rrd>
<load_balancer>
<monitor_type>
<name>ICMP</name>
<type>icmp</type>
<descr>
<![CDATA[ICMP]]>
</descr>
<options/>
</monitor_type>
<monitor_type>
<name>TCP</name>
<type>tcp</type>
<descr>
<![CDATA[Generic TCP]]>
</descr>
<options/>
</monitor_type>
<monitor_type>
<name>HTTP</name>
<type>http</type>
<descr>
<![CDATA[Generic HTTP]]>
</descr>
<options>
<path>/</path>
<host/>
<code>200</code>
</options>
</monitor_type>
<monitor_type>
<name>HTTPS</name>
<type>https</type>
<descr>
<![CDATA[Generic HTTPS]]>
</descr>
<options>
<path>/</path>
<host/>
<code>200</code>
</options>
</monitor_type>
<monitor_type>
<name>SMTP</name>
<type>send</type>
<descr>
<![CDATA[Generic SMTP]]>
</descr>
<options>
<send/>
<expect>220 *</expect>
</options>
</monitor_type>
</load_balancer>
<widgets>
<sequence>system_information:col1:open,gateways:col1:open,interfaces:col2:open</sequence>
</widgets>
<openvpn/>
<dnshaper></dnshaper>
<unbound>
<enable/>
<dnssec/>
<active_interface/>
<outgoing_interface/>
<custom_options/>
<hideidentity/>
<hideversion/>
<dnssecstripped/>
</unbound>
<dhcpdv6>
<lan>
<range>
<from>::1000</from>
<to>::2000</to>
</range>
<ramode>assist</ramode>
<rapriority>medium</rapriority>
</lan>
</dhcpdv6>
<cert>
<refid>5720a0502b277</refid>
<descr>
<![CDATA[webConfigurator default (5720a0502b277)]]>
</descr>
<type>server</type>
<crt>LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUZiVENDQkZXZ0F3SUJBZ0lCQURBTkJna3Foa2lHOXcwQkFRc0ZBRENCdERFTE1Ba0dBMVVFQmhNQ1ZWTXgKRGpBTUJnTlZCQWdUQlZOMFlYUmxNUkV3RHdZRFZRUUhFd2hNYjJOaGJHbDBlVEU0TURZR0ExVUVDaE12Y0daVApaVzV6WlNCM1pXSkRiMjVtYVdkMWNtRjBiM0lnVTJWc1ppMVRhV2R1WldRZ1EyVnlkR2xtYVdOaGRHVXhLREFtCkJna3Foa2lHOXcwQkNRRVdHV0ZrYldsdVFIQm1VMlZ1YzJVdWJHOWpZV3hrYjIxaGFXNHhIakFjQmdOVkJBTVQKRlhCbVUyVnVjMlV0TlRjeU1HRXdOVEF5WWpJM056QWVGdzB4TmpBME1qY3hNVEU1TkRSYUZ3MHlNVEV3TVRneApNVEU1TkRSYU1JRzBNUXN3Q1FZRFZRUUdFd0pWVXpFT01Bd0dBMVVFQ0JNRlUzUmhkR1V4RVRBUEJnTlZCQWNUCkNFeHZZMkZzYVhSNU1UZ3dOZ1lEVlFRS0V5OXdabE5sYm5ObElIZGxZa052Ym1acFozVnlZWFJ2Y2lCVFpXeG0KTFZOcFoyNWxaQ0JEWlhKMGFXWnBZMkYwWlRFb01DWUdDU3FHU0liM0RRRUpBUllaWVdSdGFXNUFjR1pUWlc1egpaUzVzYjJOaGJHUnZiV0ZwYmpFZU1Cd0dBMVVFQXhNVmNHWlRaVzV6WlMwMU56SXdZVEExTURKaU1qYzNNSUlCCklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUF0L085aDlnT2R5R20yTnQ4R3dpUmw1bDAKVmZ2NGJsQ2NWcGJNYXFMUE1aVzNMdGhDODBHU0dhZnJENWdqcTRwZkNNMHlzbEFPaVlZK1hDYjdNa2o0dmtTMgpmbzl4emNyaDUrNVlaYlBHeXR1a2lsZWR4bjFWeFl6SllzYXZKdnlKb1lRMCtNTkx0dkFjYnRhTUFoZjh1ZkRFClhrclNVQ0N5YTFrbEYxNWJGZmcyUGE0eGRvMk9PNUJ5RzBrV0NKU2o4K1R1WnVkUFRJTkx3QUZnd1E5K1BQZkwKVTQxMFBVb3FFbWEwdzU4Q1RZKzZhZEFiUEhjWGc5SFA0NFQybFNIQ2M1cUp5UTdlK3IyaFZ0N29ENloxQmdCUApyeXd1SEZwd3J1LytYWExieEcrcDdwYXI0aHR0UFRDcml1NmFqQVVTNmpvN05kOElQNWpzZ1kzR0h2ZjhzUUlECkFRQUJvNElCaGpDQ0FZSXdDUVlEVlIwVEJBSXdBREFSQmdsZ2hrZ0JodmhDQVFFRUJBTUNCa0F3TXdZSllJWkkKQVliNFFnRU5CQ1lXSkU5d1pXNVRVMHdnUjJWdVpYSmhkR1ZrSUZObGNuWmxjaUJEWlhKMGFXWnBZMkYwWlRBZApCZ05WSFE0RUZnUVU3K1lLRmNpOFFVSGhTZ0xEdjhFQ3NjQ0p3QUl3Z2VFR0ExVWRJd1NCMlRDQjFvQVU3K1lLCkZjaThRVUhoU2dMRHY4RUNzY0NKd0FLaGdicWtnYmN3Z2JReEN6QUpCZ05WQkFZVEFsVlRNUTR3REFZRFZRUUkKRXdWVGRHRjBaVEVSTUE4R0ExVUVCeE1JVEc5allXeHBkSGt4T0RBMkJnTlZCQW9UTDNCbVUyVnVjMlVnZDJWaQpRMjl1Wm1sbmRYSmhkRzl5SUZObGJHWXRVMmxuYm1Wa0lFTmxjblJwWm1sallYUmxNU2d3SmdZSktvWklodmNOCkFRa0JGaGxoWkcxcGJrQndabE5sYm5ObExteHZZMkZzWkc5dFlXbHVNUjR3SEFZRFZRUURFeFZ3WmxObGJuTmwKTFRVM01qQmhNRFV3TW1JeU56ZUNBUUF3SFFZRFZSMGxCQll3RkFZSUt3WUJCUVVIQXdFR0NDc0dBUVVGQ0FJQwpNQXNHQTFVZER3UUVBd0lGb0RBTkJna3Foa2lHOXcwQkFRc0ZBQU9DQVFFQXJxZFpQdXd2MVZuUC82NmJDWFJ5CkVmaW1LRWlPcmtNaTB5M09PWGtzWEs1cEM2dTd6Ukl3WjEvRjYyRUp3ODlUOWx4Y01ZelZOTm5Idlg0bXFPRUcKUWJhRU42NEkxOHFud3ZmS2JrREZvRThMR1hSdzBkMnAyTGVmYTd4YTIvSGNHc0xHTktPbkJxb3N4ejUrQ1B3ZwpWeVRaTS9wV3p3aDdQRGc4bGdrcVc3dStlb01DNDJIbVJkOURCTmlzdFJ4RVlNMkFLQkFsZG1LYStvRUY1VUwwCm43aXpvNlZ4dHJWMTJvTTdySllRQ05kY00xZkVSeUwvb3ZkUnVpa0F5Wm1VVnFUL1dDZGo3dDdIVG9ob0RFYzEKSklkOVpPSmR2QmZLVU1sUWlELyswSVpTalFXRDczWkdsaEhTK2tOeWc1aDJhUjUwYjh3Wm9zQnNjSUZDa0pFbgp0UT09Ci0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K</crt>
<prv>LS0tLS1CRUdJTiBQUklWQVRFIEtFWS0tLS0tCk1JSUV2Z0lCQURBTkJna3Foa2lHOXcwQkFRRUZBQVNDQktnd2dnU2tBZ0VBQW9JQkFRQzM4NzJIMkE1M0lhYlkKMjN3YkNKR1htWFJWKy9odVVKeFdsc3hxb3M4eGxiY3UyRUx6UVpJWnArc1BtQ09yaWw4SXpUS3lVQTZKaGo1YwpKdnN5U1BpK1JMWitqM0hOeXVIbjdsaGxzOGJLMjZTS1Y1M0dmVlhGak1saXhxOG0vSW1oaERUNHcwdTI4Qnh1CjFvd0NGL3k1OE1SZVN0SlFJTEpyV1NVWFhsc1YrRFk5cmpGMmpZNDdrSEliU1JZSWxLUHo1TzVtNTA5TWcwdkEKQVdEQkQzNDg5OHRUalhROVNpb1NaclREbndKTmo3cHAwQnM4ZHhlRDBjL2poUGFWSWNKem1vbkpEdDc2dmFGVwozdWdQcG5VR0FFK3ZMQzRjV25DdTcvNWRjdHZFYjZudWxxdmlHMjA5TUt1SzdwcU1CUkxxT2pzMTN3Zy9tT3lCCmpjWWU5L3l4QWdNQkFBRUNnZ0VCQUpRRFpxU3duMnNTUTh0SVNBTUVrUW0zcXhrb3BzdzB4cWNScmFlOEd4VmQKejBpOU1KbkZVQWFleTQvL3JldndhZW1PR3RYSmZ2ai9jSnY3cmJIWGIzYkJtVW9hcDhxY0RjdnVSMmlHRUZYWQpCL3hjNVpINTlaTUFabWE1VWVQLzNjcDlzNVhhcHNpclNXV1I4cFFZc3Z6Mmt6ci8zMXdrQXd4SGJZWHhJVDk1CjNLRmk4VTZUM1hnU1c2eFowZHp1ZnlPUzAvbXlmNU5YLzVoRklPNmFDc0xlUjZ4N1RZa2FDQU9FYlViT29qUXkKc09XeWphbEtTUWZ3WEdzdVM0bXdyR2hMZ0NRYlB2MnE5V0Nia0VMNEZUZmRzRlZXcHBRNGlZVWtwNzhMY1FPMgpsSGR5cTJxTmJsNDIwa3h5M2FnZlF2YTVqYUgyRm5LdkExR2YxY05hcGRVQ2dZRUE0NzNMUWoxcExLSmRZN2JxCmtMU3NVT0ZhTUZlZG1xU2ttbzh3QjlpMXhzbElLQUd0M3U4dTdMZlZtU2lybnMwVVBTMHRVUDRyQXMzVFJocEgKU2Z4VXVsbGVGaktjZk9xRE11TTBCOGttbFJnUFRmVHVPaGNwMGVkamQwK1E5Y2VlY25kaFp3UEl6TUc3TWRTSApKOG5yU2t5TFdMdWUxUVJNZHNhbmNBRDhVYThDZ1lFQXpzYjYzbzRBSHlYNjZkcEJ6TGlzYzZxS2d2ZG4xazhVCm02N3RuK2M3NkVhSEtZTlk0RjdhS0dFSk1yeU0yQTJTelAzdm03Rmk4eGRtblgrSXd5cUx5T1VwSnZXQ012TVIKRDFpNWVFTVVoZVo2OUpOK0I3SmZ2RjYrK2tHa1NHOGxaN0VLY21Uc1kzRVJxOURsSk94Nk1ROFEwMDNsTHVtQQpJZm1DWlpRSUQ1OENnWUJjamFOdk5obnFJOG9rWGhBUjR2c3NtNGpWb0tYU1ZScjRIVHo5MDFwOGdReXNCWkt0CnlUS2V6VThuUVZvTjNYWmVMbC8rVEcwYVpKOTZHKy9nNTRWZmZqWTRlelVScHhUT3QzdEx0cm5SV2NmT2ZMM2MKS2RHN0ZuaGI0cUFjNHBWSUc3QWY5Mi9CbHZJR25FS1pMdnhLWTdVMXlIb1NRLzczUG1DSnFqemd6UUtCZ1FDZgpJQjE3RzRnWWNGL3hpdGJNTnVudmNUUjZxTzR0ekZtdG5TYWN3WlFtb2UvdUVIaGE0bU84WTBCeTNRcitVU1BCCndVR2RiUnNhdTgxcU12VUtURG1hZGsvKy9Ud2UvVk1Kbmx2TW9zS3VjTG42Y1c2eGVhR1hFc3FoUjlhbkwzRjMKcEpUSGg4Y3FsNTdqdkRRN0FBamdyQmxrb3pOVnNMZThiWWpkcHRlMVBRS0JnQ0xDR0R1RXNBYUxwZlRtOG44bgoyQ1h1NE52K1l3a1RlczduWjRoM3ZRODI1ZkQxbGVzVjBYdDJ1cVJqeFEvSDgxMHRGd1p3cC9uSVdycnRCZlZLClUzSThhYnpnUUtwOEwrZjVadTAxY1pZVk5TU0FIUFRHYm5jb1IzbGVPYjNLeUVXQjdsZFBHQWpOS3UwNkd5TEkKakh5TDhadEFBRXVBZ1FUOVFOVGJkQWJrCi0tLS0tRU5EIFBSSVZBVEUgS0VZLS0tLS0K</prv>
</cert>
<revision>
<time>1493655499</time>
<description>
<![CDATA[admin@10.97.67.135: /firewall_rules_edit.php made unknown change]]>
</description>
<username>admin@10.97.67.135</username>
</revision>
<gateways>
<gateway_item>
<interface>wan</interface>
<gateway>192.168.13.1</gateway>
<name>GW_WAN_2</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<interval/>
<descr>
<![CDATA[Interface wan Gateway]]>
</descr>
</gateway_item>
<gateway_item>
<interface>wan</interface>
<gateway>192.168.13.19</gateway>
<name>GW_VLAN19</name>
<weight>1</weight>
<ipprotocol>inet</ipprotocol>
<descr>
<![CDATA[Gateway to VLAN 19]]>
</descr>
</gateway_item>
</gateways>
<ppps/>
<dyndnses/>
<virtualip>
<vip>
<mode>ipalias</mode>
<interface>wan</interface>
<uniqid>57bf05ffdcc3c</uniqid>
<descr>
<![CDATA[VIP mapping to ConsoleWorks]]>
</descr>
<type>single</type>
<subnet_bits>32</subnet_bits>
<subnet>192.168.13.171</subnet>
</vip>
</virtualip>
</pfSense>
Appendix A List of Acronyms
AD Active Directory
ARM Access Rights Management
CA Certificate Authority
CSF Cybersecurity Framework
FBA Forms Based Authentication
GPO Government Printing Office, Group Policy Object (depending on context)
GUI Graphical User Interface
HTCC HyTrust CloudControl
IdAM Identity and Access Management
IT Information Technology
LDAP Lightweight Directory Access Protocol
LDAPS Lightweight Directory Access Protocol (Secure)
NCCoE National Cybersecurity Center of Excellence
NIST National Institute of Standards and Technology
PEP Policy Enforcement Point
RMF Risk Management Framework
SA Situational Awareness
SCM Security Compliance Manager
SIEM Security Information and Event Management
RDP Remote Desktop Protocol
VD Virtual Directory
VDS Virtual Directory System
VM Virtual Machine
VNC Virtual Network Computing
VPN Virtual Private Network